Application file verification method and system
A technology for application programs and files, which is applied in the field of application program file security, and can solve problems such as difficulty in entering mobile terminals, long activation codes or registration codes, and easy piracy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] The present invention will be described in detail below in conjunction with the accompanying drawings and embodiments.
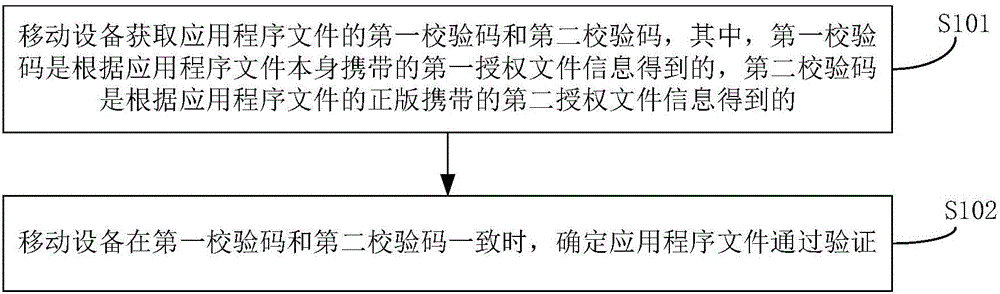
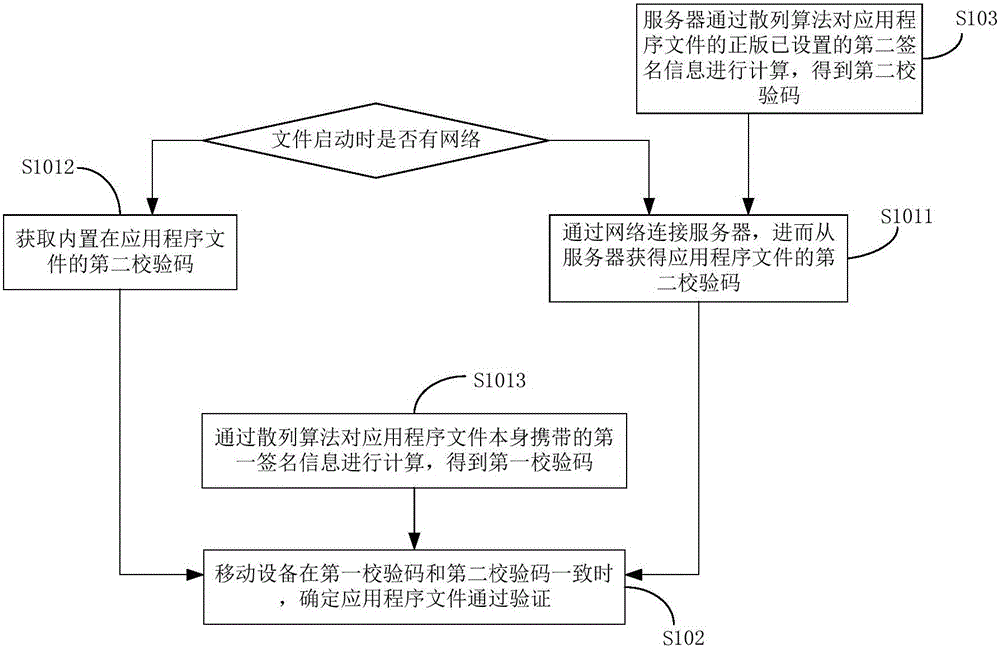
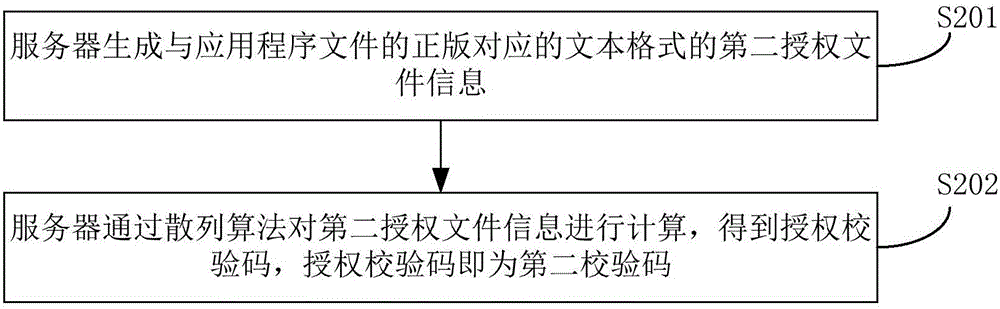
[0030] refer to figure 1 , figure 1 It is a flowchart of an embodiment of the method for verifying application program files in the present invention, including:
[0031] Step S101: The mobile device obtains the first verification code and the second verification code of the application program file, wherein the first verification code is obtained according to the first authorization file information carried by the application program file itself, and the second verification code It is obtained according to the second authorization file information carried by the genuine version of the application program file, and the second authorization file information carried by the genuine version of the application program file is the authorization file information corresponding to the genuine version of the application program file. The acquisition of the fi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More