A network security authentication method
An authentication method and network security technology, applied in the field of computer software security authentication, can solve the problems that users are difficult to grasp, there is no monitoring scheme, and users cannot really grasp the running status of the KDC server, and achieve the effect of effective monitoring and high security level.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0027] The present invention will be described in detail below in conjunction with the implementations shown in the drawings, but it should be noted that these implementations are not limitations of the present invention, and those of ordinary skill in the art based on the functions, methods, or structural changes made by these implementations Equivalent transformations or substitutions all fall within the protection scope of the present invention.
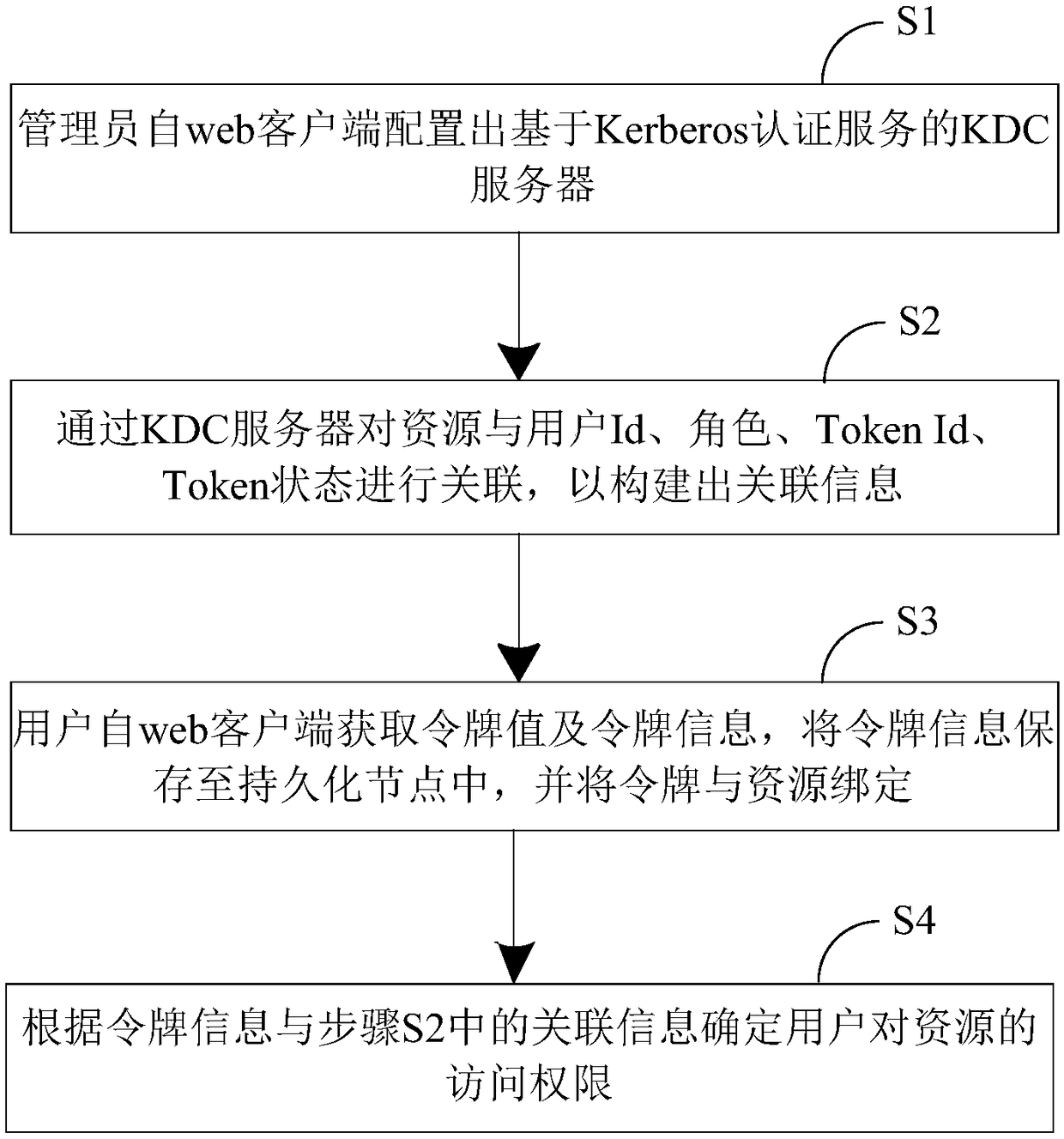
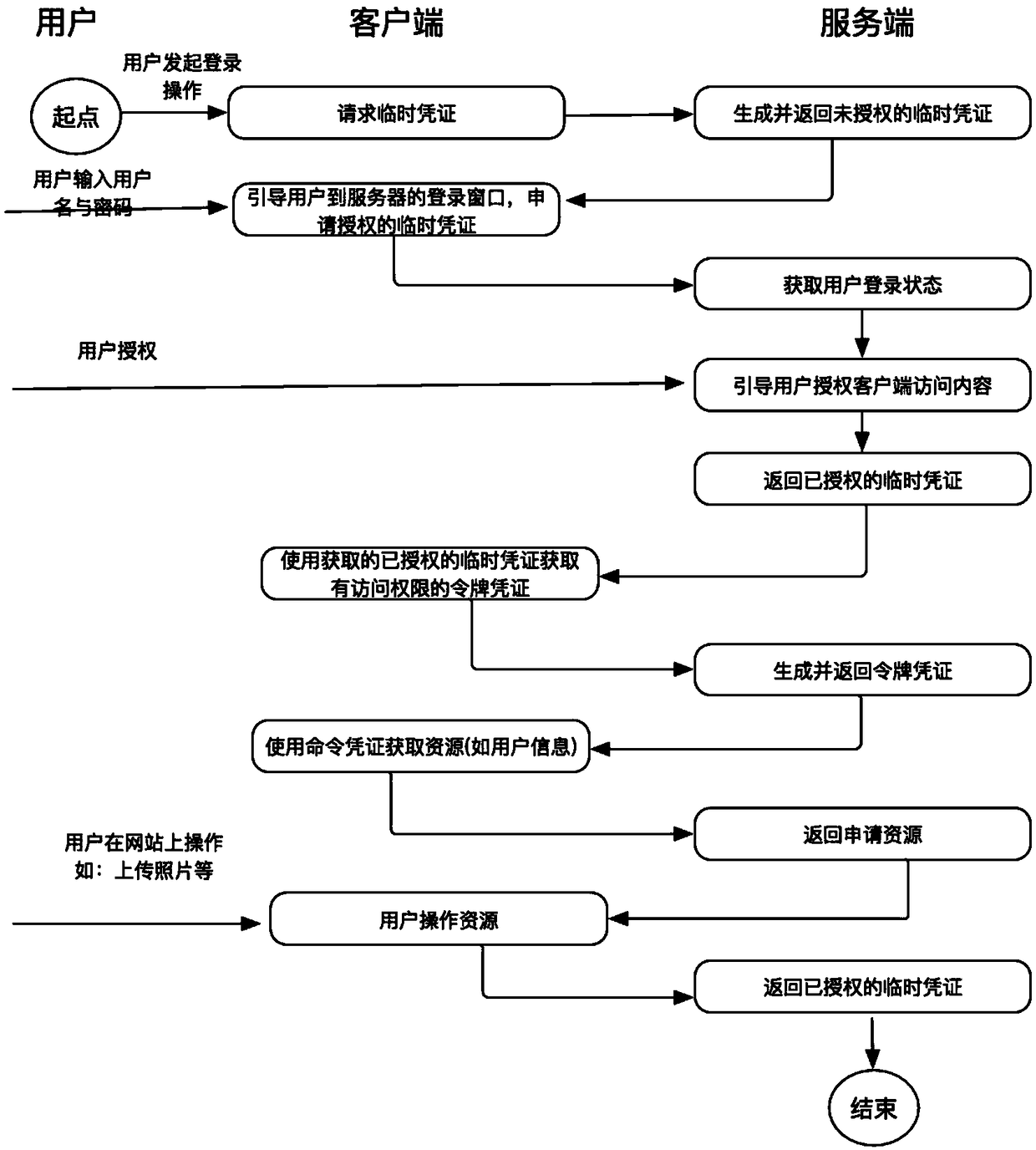
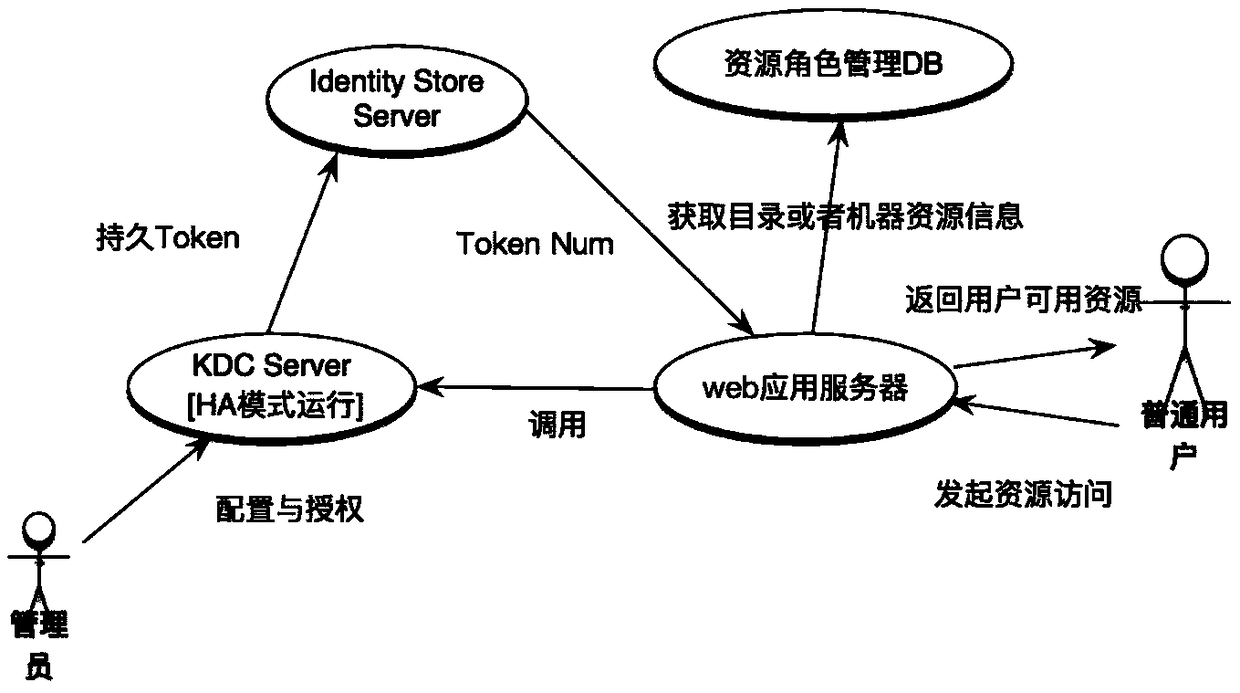
[0028] Please refer to Figure 1 to Figure 7 An embodiment of a network security authentication method of the present invention is shown. In the present embodiment, a kind of network security authentication method, it is based on Apache Kerby security authentication framework, and this network security authentication method comprises the following steps:
[0029] First, step S1 is executed, and the administrator configures the KDC server based on the Kerberos authentication service from the web client.
[0030] Based on the esta...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More