An access control method for data sources
An access control and data source technology, applied in electrical digital data processing, instruments, memory systems, etc., to solve problems such as unaffordable cost increases
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0049] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below with reference to the accompanying drawings and examples.
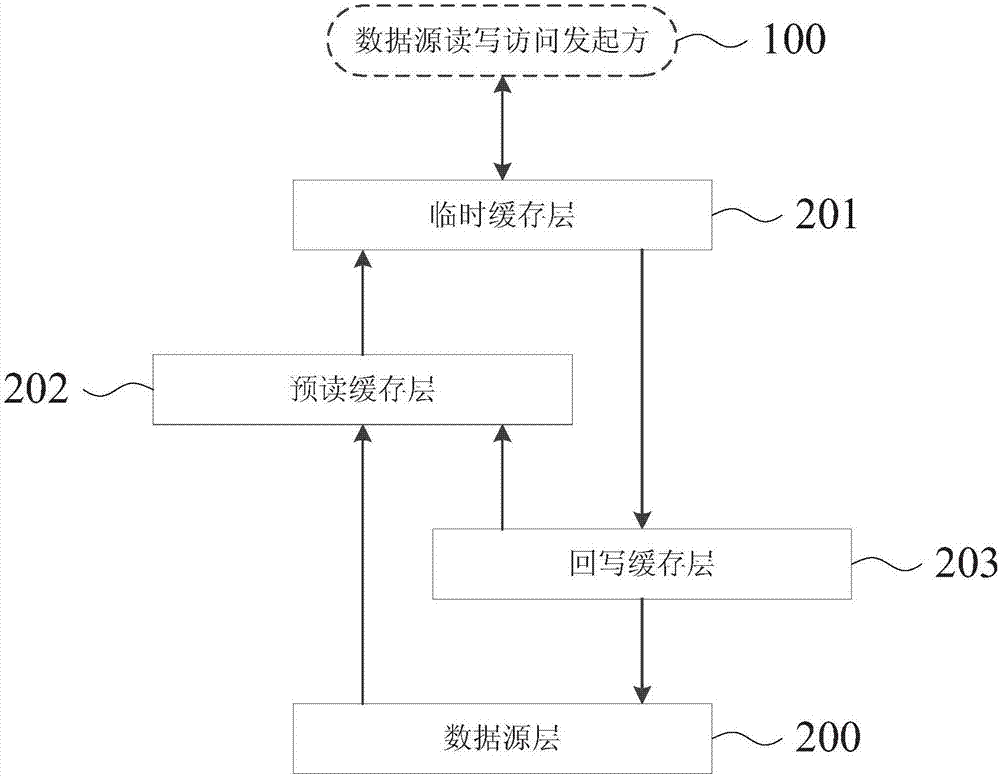
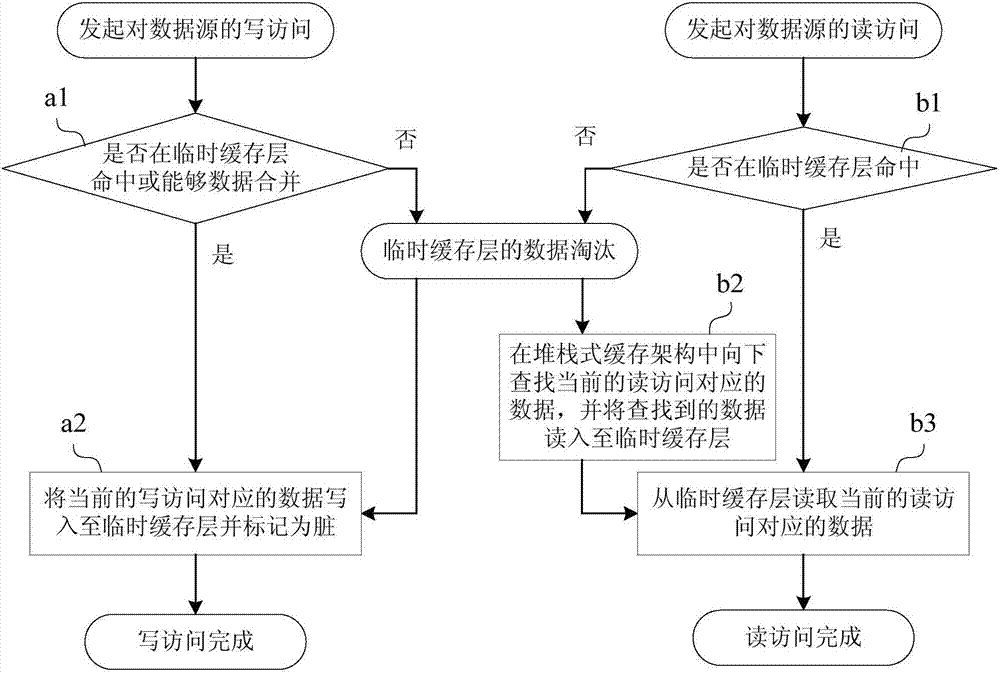
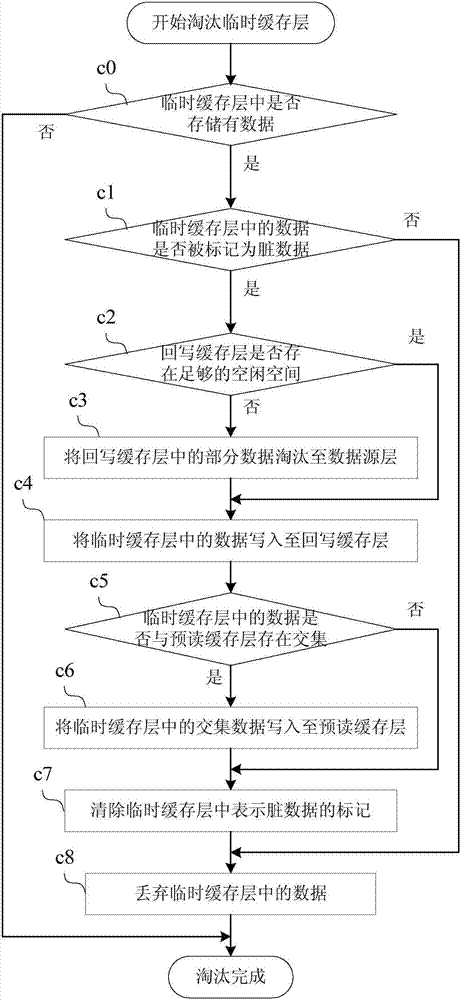
[0050] Please see first figure 1, in this embodiment, a stacked cache architecture is provided, the stacked cache architecture includes a temporary cache layer 101 , a read-ahead cache layer 102 , a write-back cache layer 103 , and a data source layer 200 . The stack cache architecture provided by this embodiment can be regarded as a data source by the data source read and write access initiator 100 as a whole, that is, the temporary cache layer 101, the read-ahead cache layer 102, the write-back cache layer 103, and the data source Layers 200 can all be considered part of a data source.
[0051] Although the temporary cache layer 101, the read-ahead cache layer 102, the write-back cache layer 103, and the data source layer 200 are all part of the data...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More