Social worker attack knowledge representation and excavation method based on SOEKS
A technology of knowledge representation and knowledge, applied in the field of cyberspace security, can solve problems such as inability to form computers, inability to share knowledge, and inconsistencies in forms
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0067] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0068] The application principle of the present invention will be described in detail below in conjunction with the accompanying drawings.
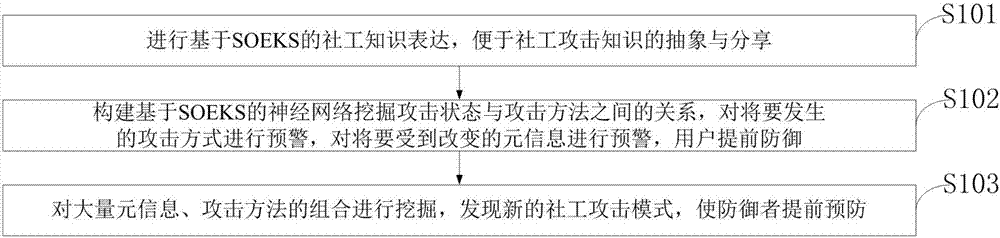
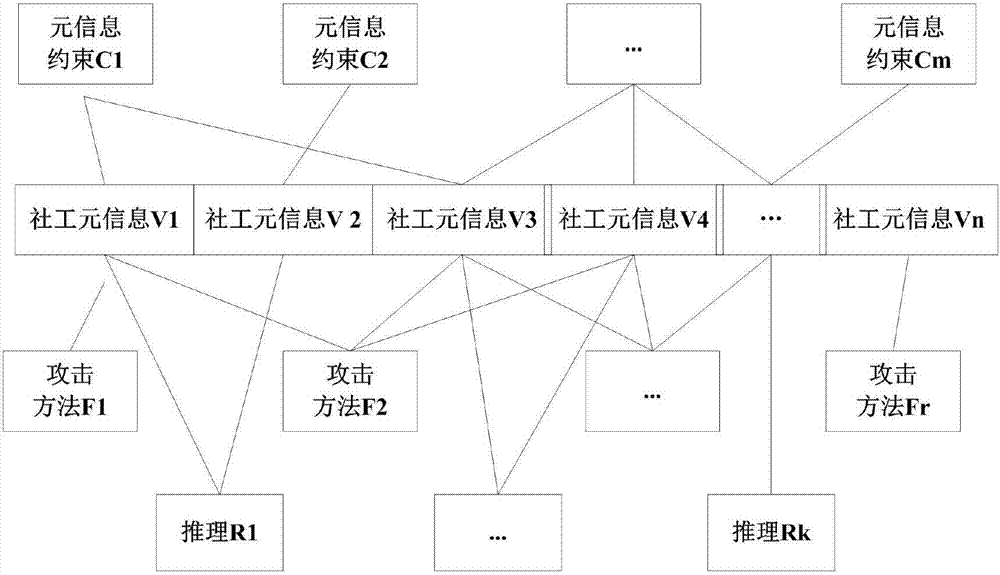
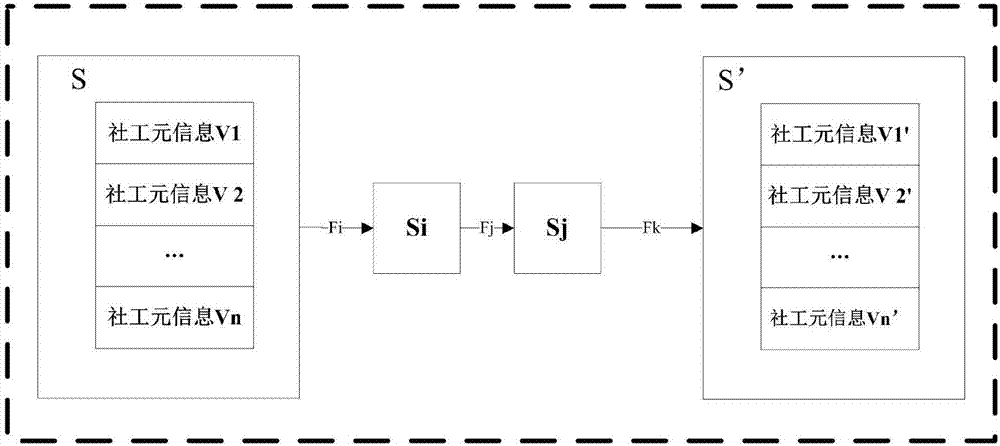
[0069] Such as figure 1 As shown, the SOEKS-based social engineering attack knowledge representation and mining method provided by the embodiment of the present invention includes:
[0070] S101: Perform SOEKS-based social engineering knowledge expression to facilitate the abstraction and sharing of social engineering attack knowledge;
[0071] S102: Construct a neural network based on SOEKS to mine the relationship between the attack state and the attack method, provide early warnin...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More