Network security evaluation method based on node weight
A technology of network security assessment and node rights, applied in data exchange networks, digital transmission systems, electrical components, etc., to achieve the effect of easy promotion and simple assessment methods
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
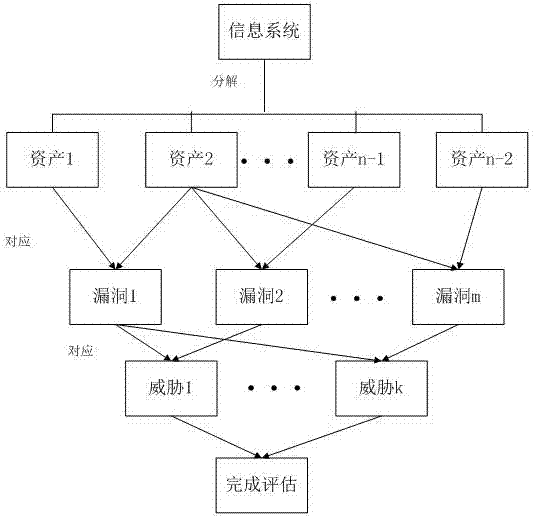
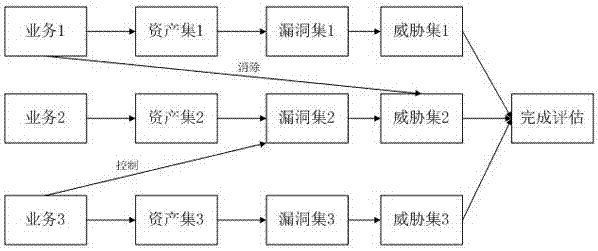
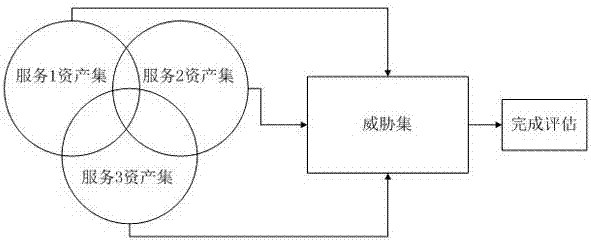
Method used
Image
Examples
Embodiment Construction
[0033] The present invention will be described in further detail below in conjunction with the accompanying drawings and specific embodiments.
[0034] see Figure 4 , in order to verify the correctness of the above method for the risk management and risk assessment of information systems, the following will analyze through an example, the example first builds a simple experimental network, the composition of the network is as follows Figure 4 shown. There are 5 workstations in the network, 1 Web server, and 1 mail server. These devices are connected to a switch, which is connected to a router, and the router is connected to the campus network.
[0035] 1. Asset risk analysis, the specific method is:
[0036] First, look for vulnerabilities, create a list of multiple vulnerabilities of an asset according to the vulnerability source, vulnerability code and risk level; there are 9 nodes in the network, and the asset information table of the corresponding node in this embodime...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More