Patents
Literature
2954 results about "Pattern perception" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
Haptic perception is the process of recognizing objects through touch. It involves a combination of somatosensory perception of patterns on the skin surface (e.g., edges, curvature, and texture) and proprioception of hand position and conformation.
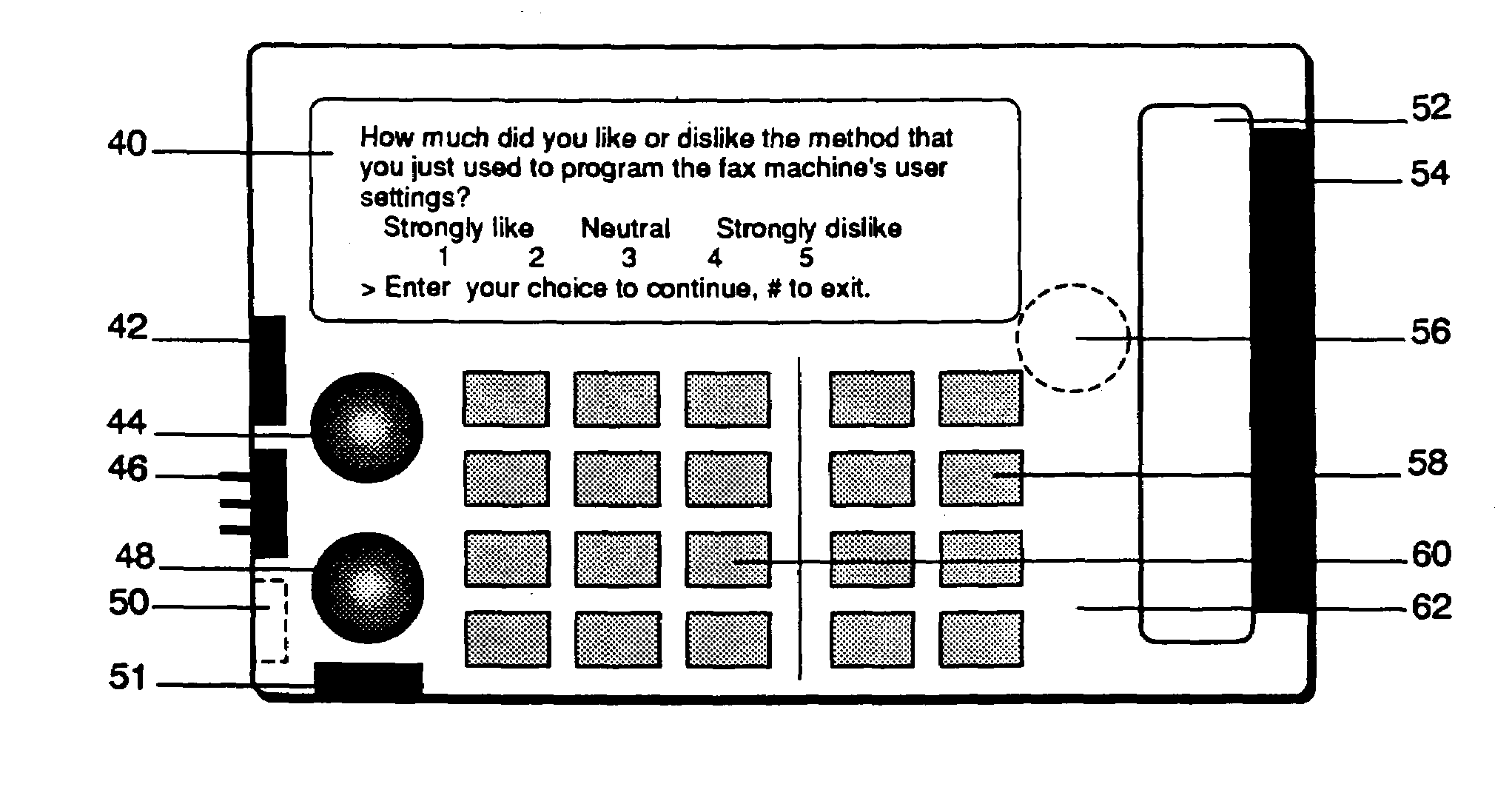
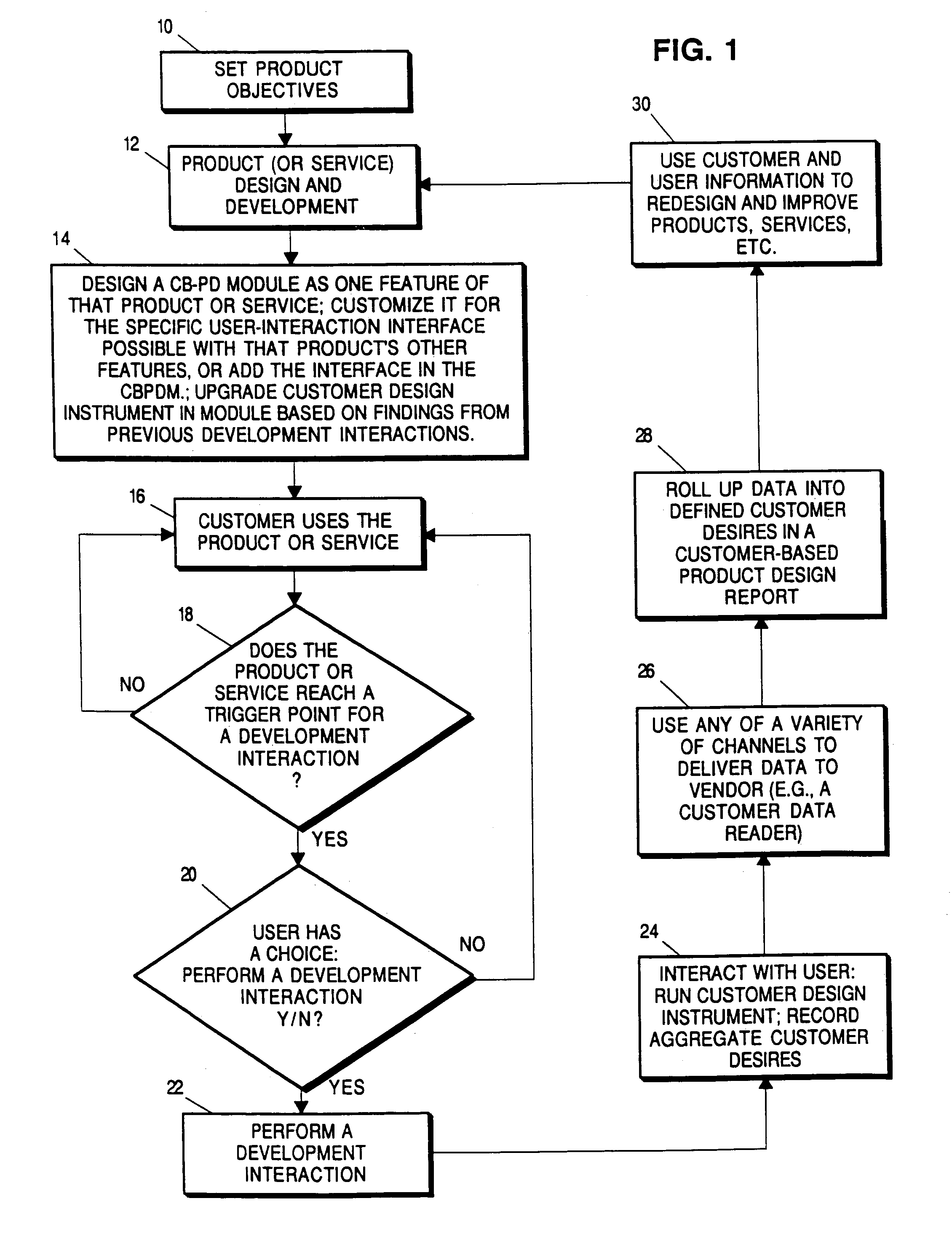
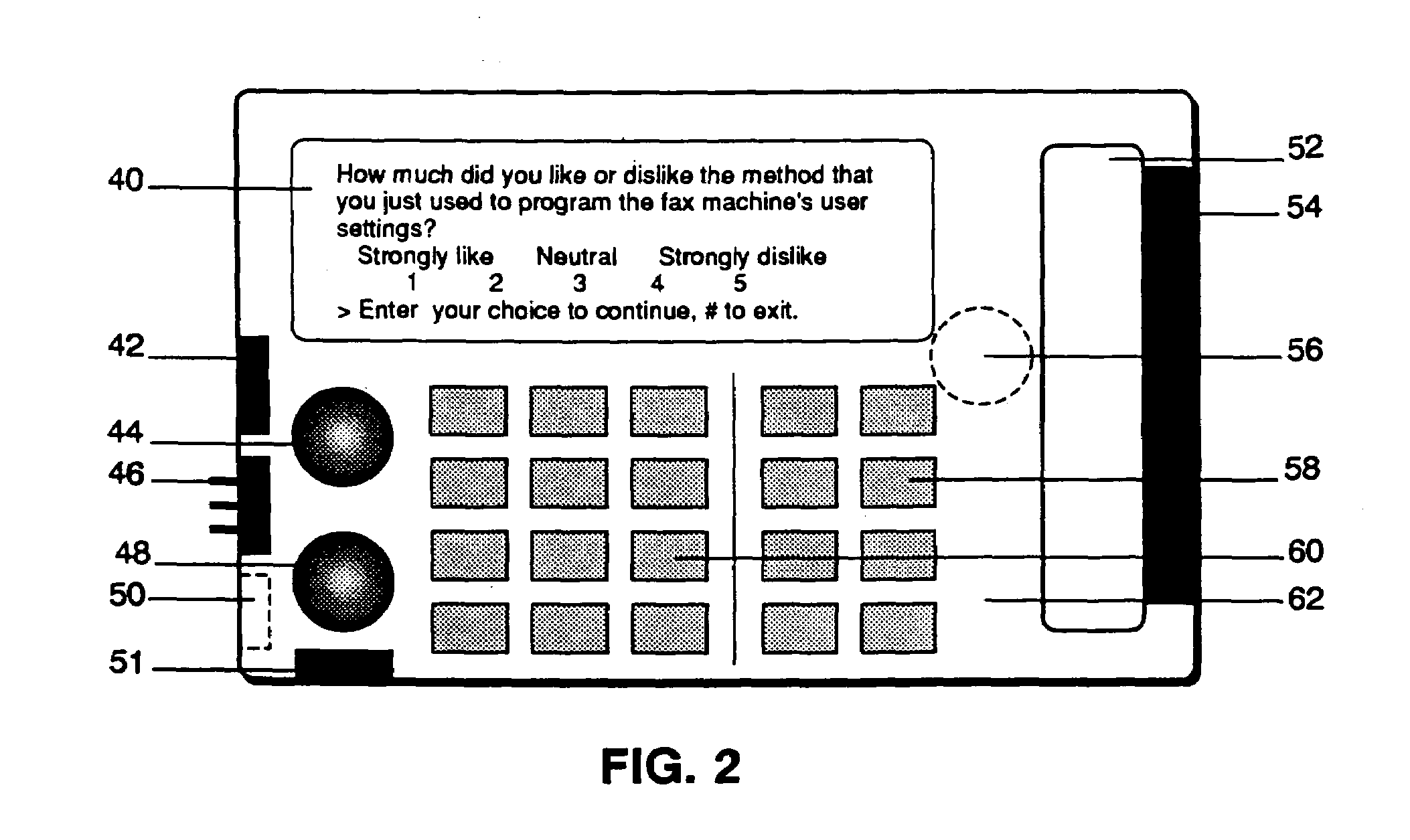
Methods and systems for gathering information from units of a commodity across a network
InactiveUS7222078B2Improve recognitionImprove market shareMarket predictionsPattern perceptionUser interface
In an exemplary system, information is received at a central location from different units of a commodity. The information is generated from two-way local interactions between users of the different units of the commodity and a user interface in the different units of the commodity. The interactions elicit from respective users their perceptions of the commodity.
Owner:LODSYS GRP
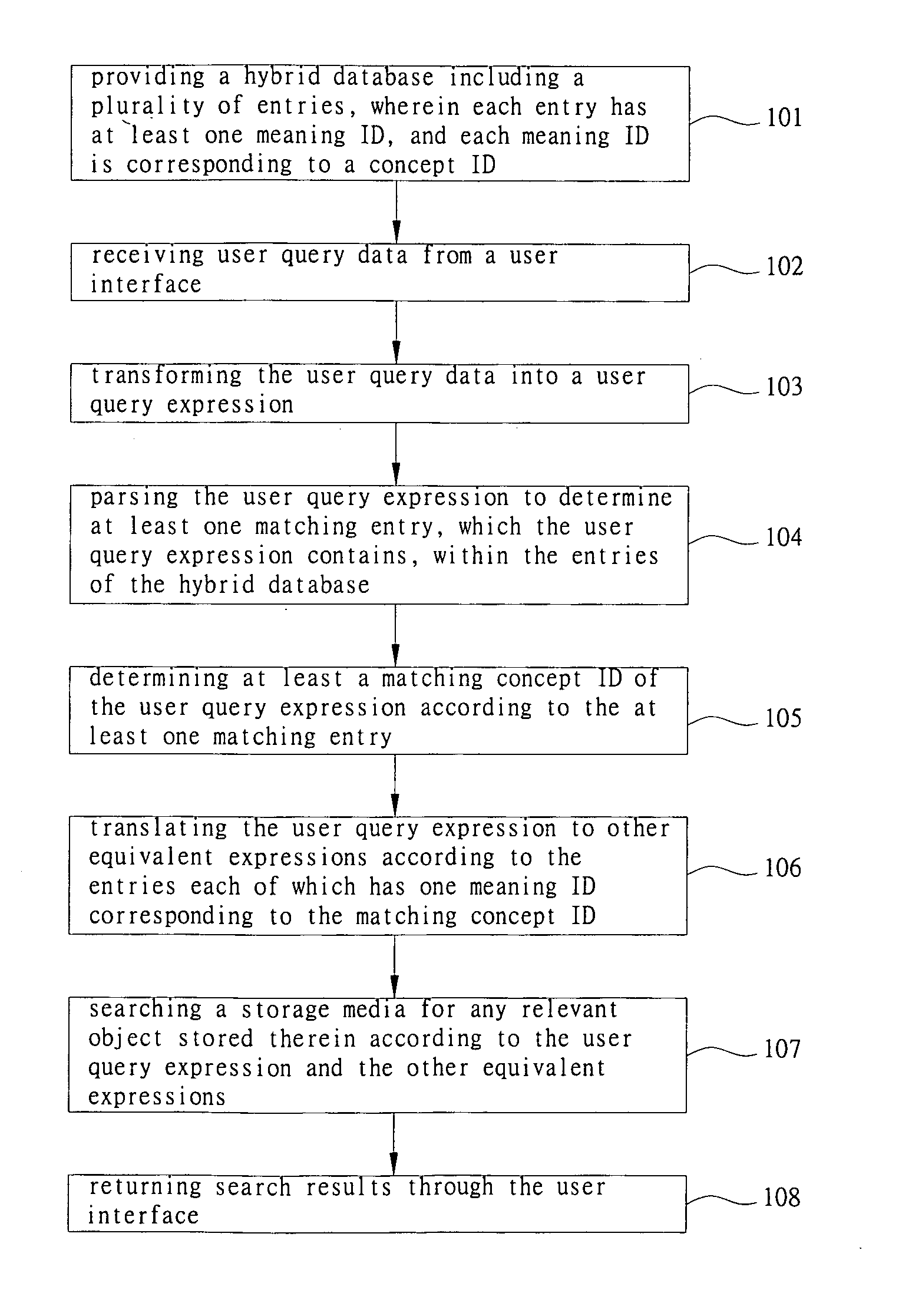
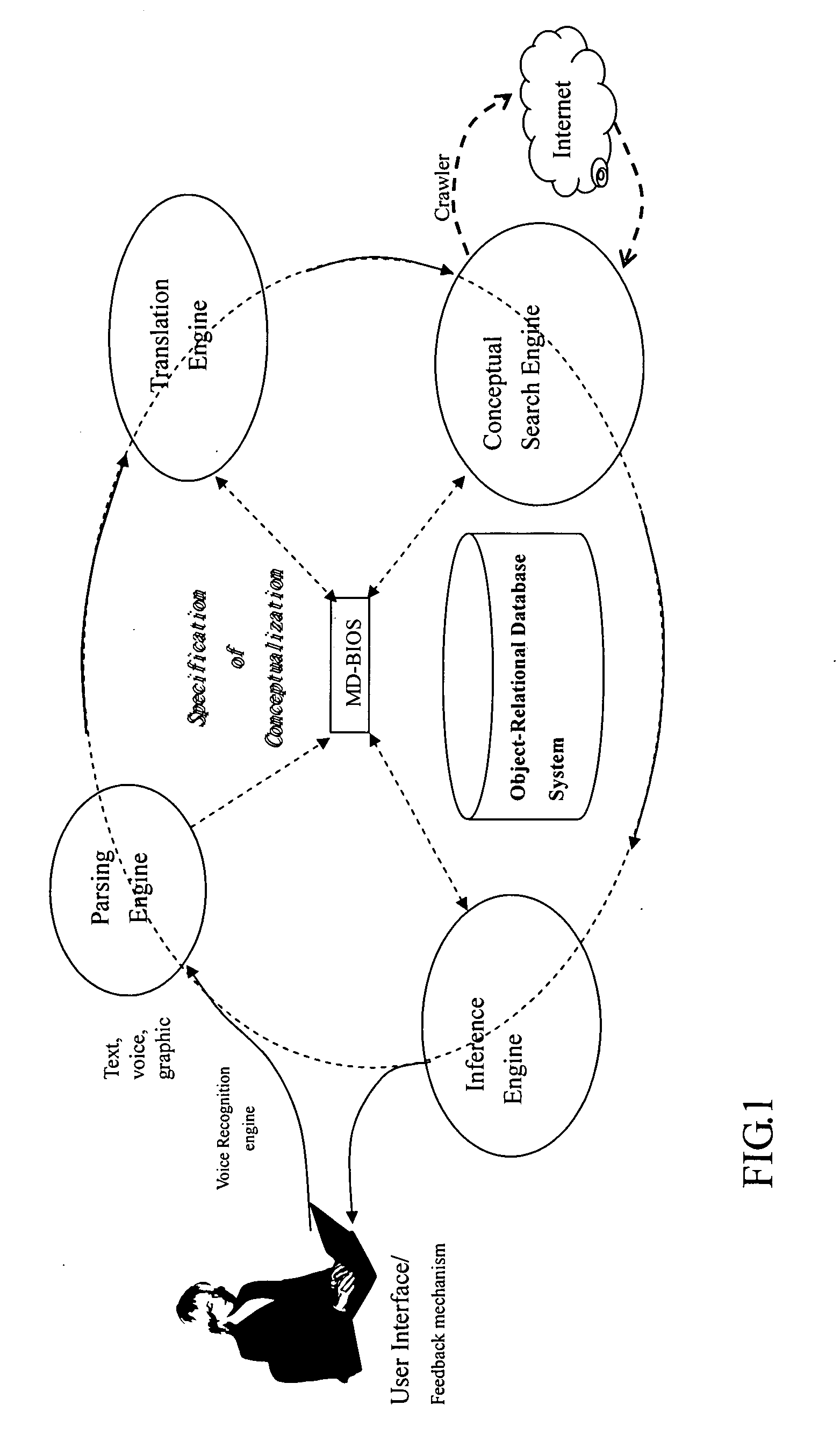
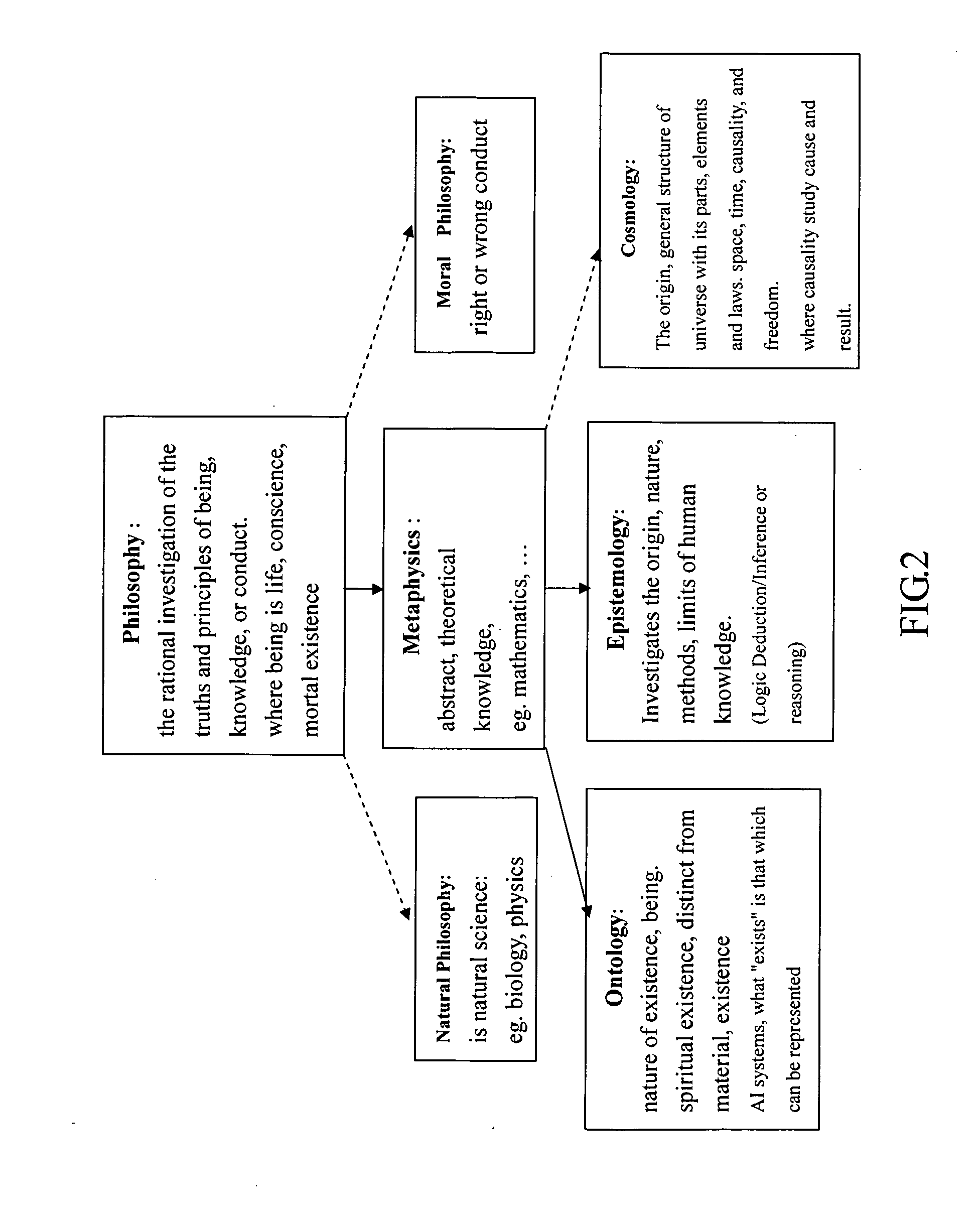
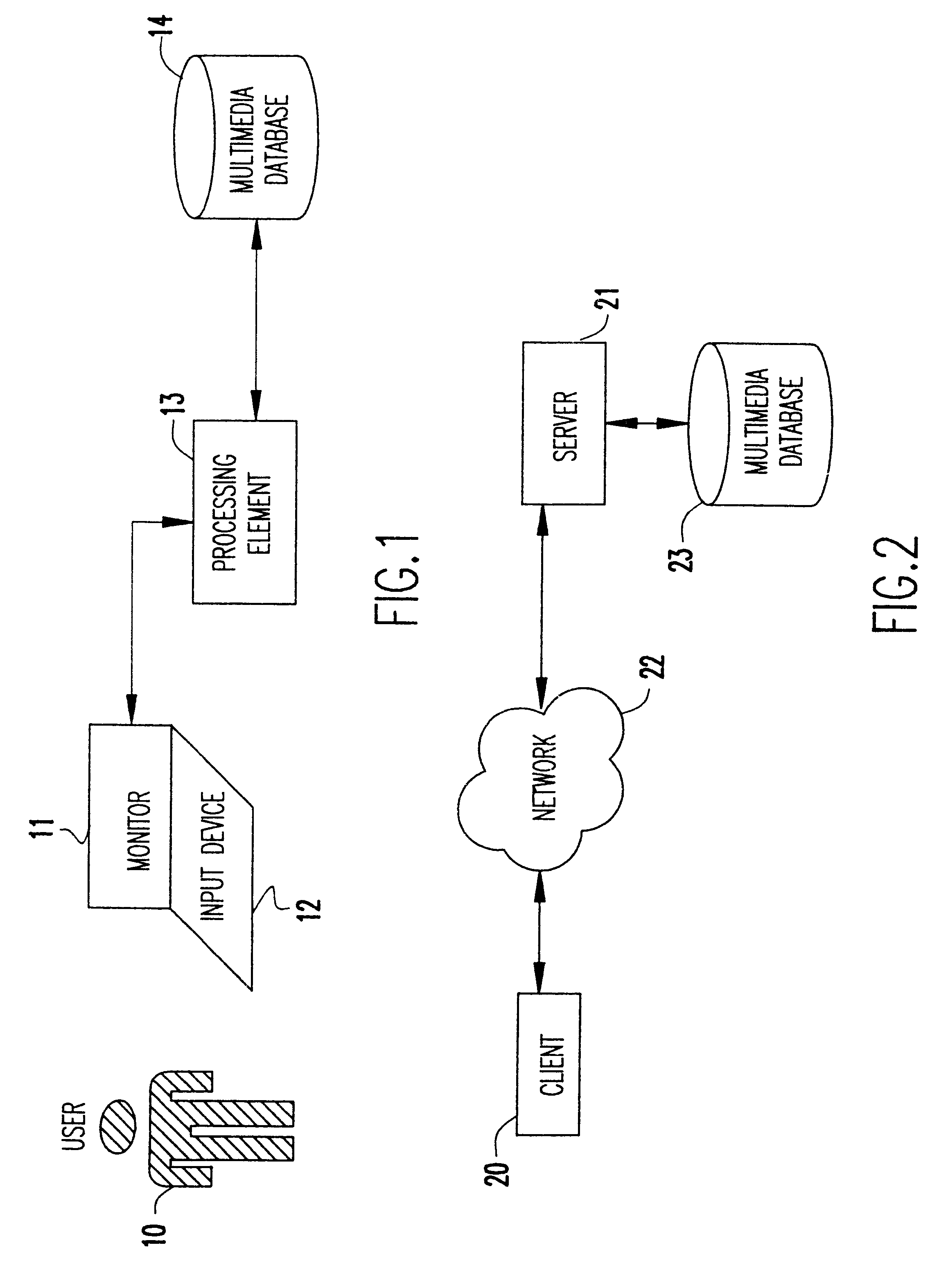
Multimedia conceptual search system and associated search method
InactiveUS20070130112A1High returnLess sensitive to lighting conditionMultimedia data indexingSpecial data processing applicationsPattern perceptionWeb crawler
The current disclosure uses the disciplines of Ontology and Epistemology to implement a context / content-based “multimedia conceptual search and planning”, in which the formation of conceptualization is supported by embedding multimedia sensation and perception into a hybrid database. The disclosed system comprises: 1) A hybrid database model to host concept setup. 2) A graphic user interface to let user freely issue searching request in text and graphic mode. 3) A parsing engine conducting the best match between user query and dictionaries, analyzing queried images, detecting and presenting shape and chroma, extracting features / texture of an object. (4) A translation engine built for search engine and inference engine in text and graphic mode. 5) A search engine using partitioned, parallel, hashed indexes from web crawler result, conducting search in formal / natural language in text and graphic mode. 6) A logic interference engine working in text and graphic mode, and 7) A learning / feedback interface.
Owner:INTELLIGENTEK CORP
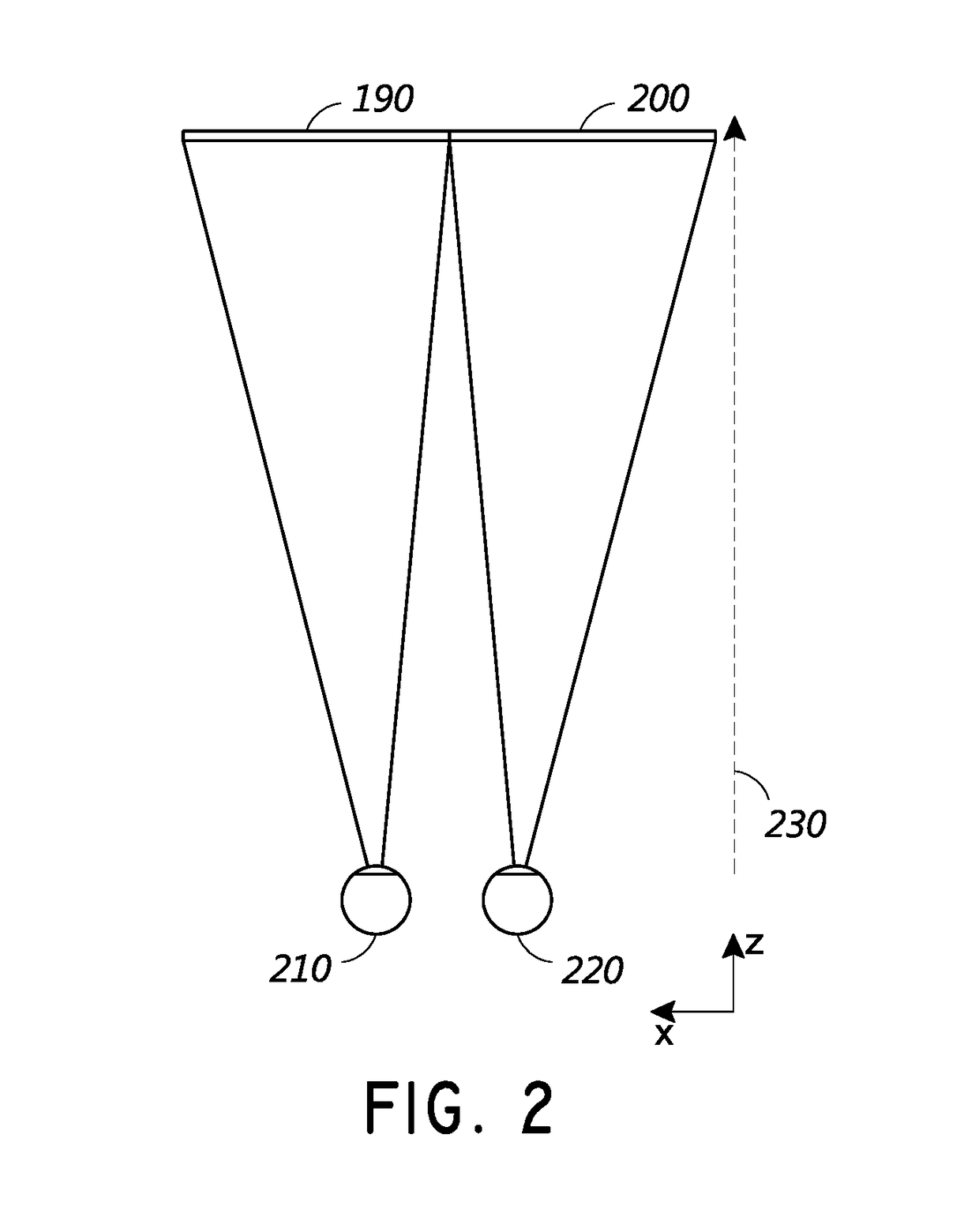
Augmented reality display system for evaluation and modification of neurological conditions, including visual processing and perception conditions
ActiveUS20170365101A1Increase alertnessImprove plasticityMedical automated diagnosisMental therapiesWavefrontPattern perception
In some embodiments, a display system comprising a head-mountable, augmented reality display is configured to perform a neurological analysis and to provide a perception aid based on an environmental trigger associated with the neurological condition. Performing the neurological analysis may include determining a reaction to a stimulus by receiving data from the one or more inwardly-directed sensors; and identifying a neurological condition associated with the reaction. In some embodiments, the perception aid may include a reminder, an alert, or virtual content that changes a property, e.g. a color, of a real object. The augmented reality display may be configured to display virtual content by outputting light with variable wavefront divergence, and to provide an accommodation-vergence mismatch of less than 0.5 diopters, including less than 0.25 diopters.
Owner:MAGIC LEAP
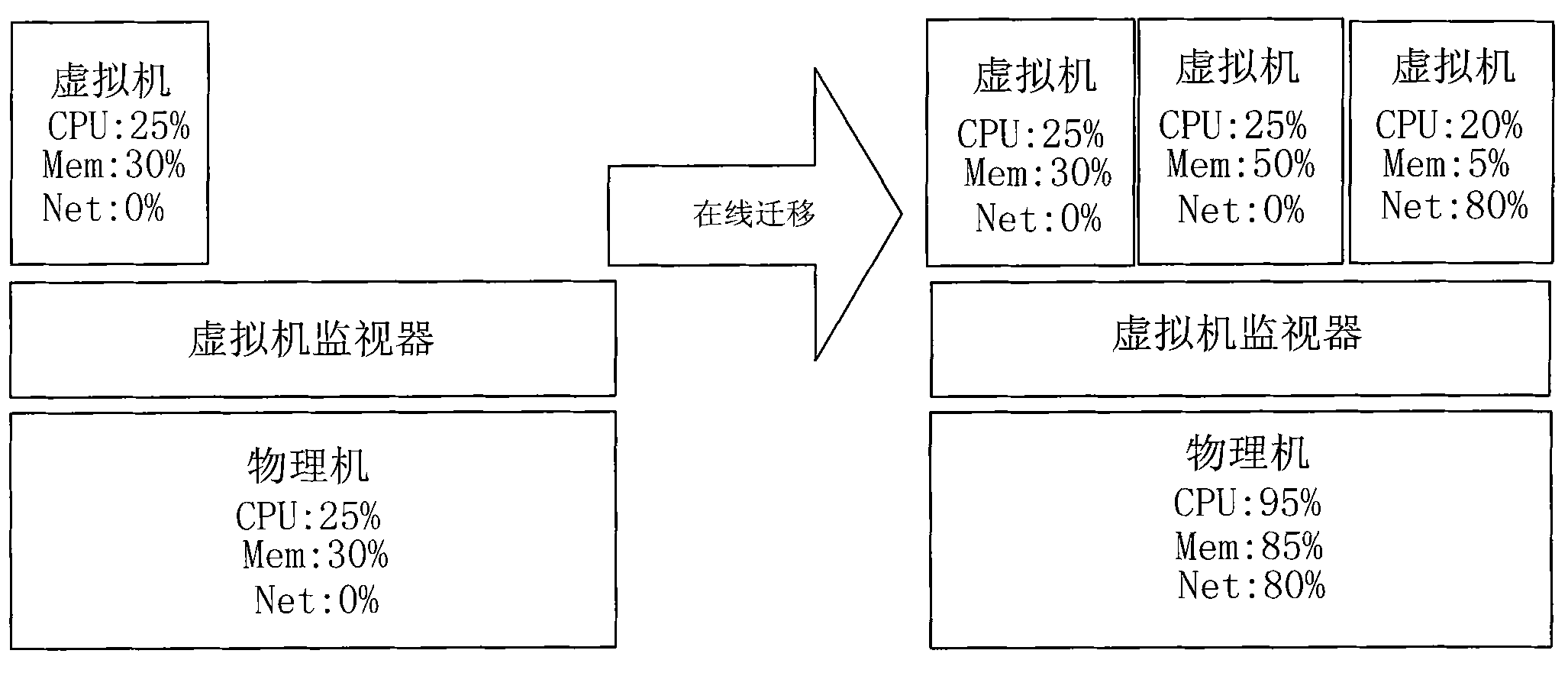
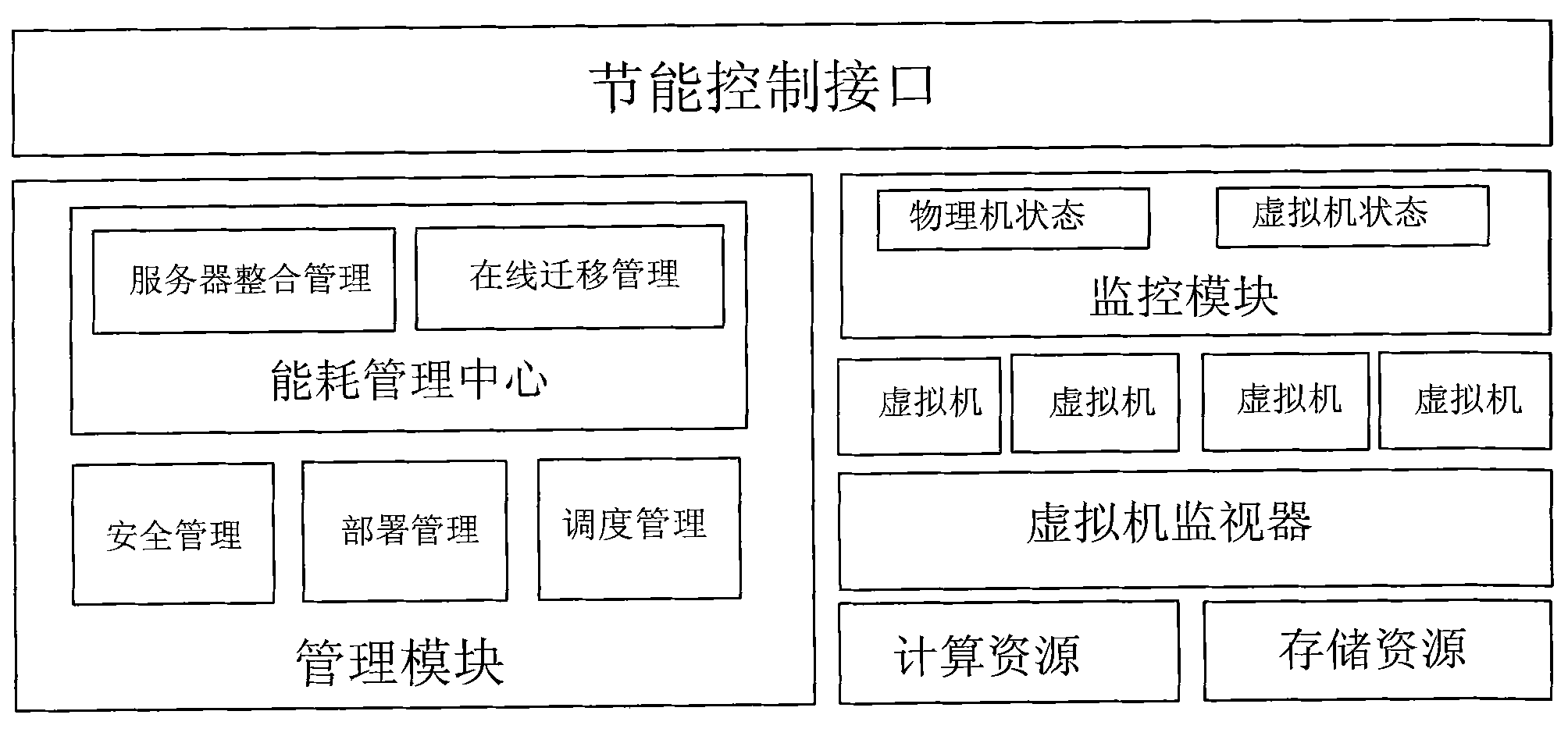
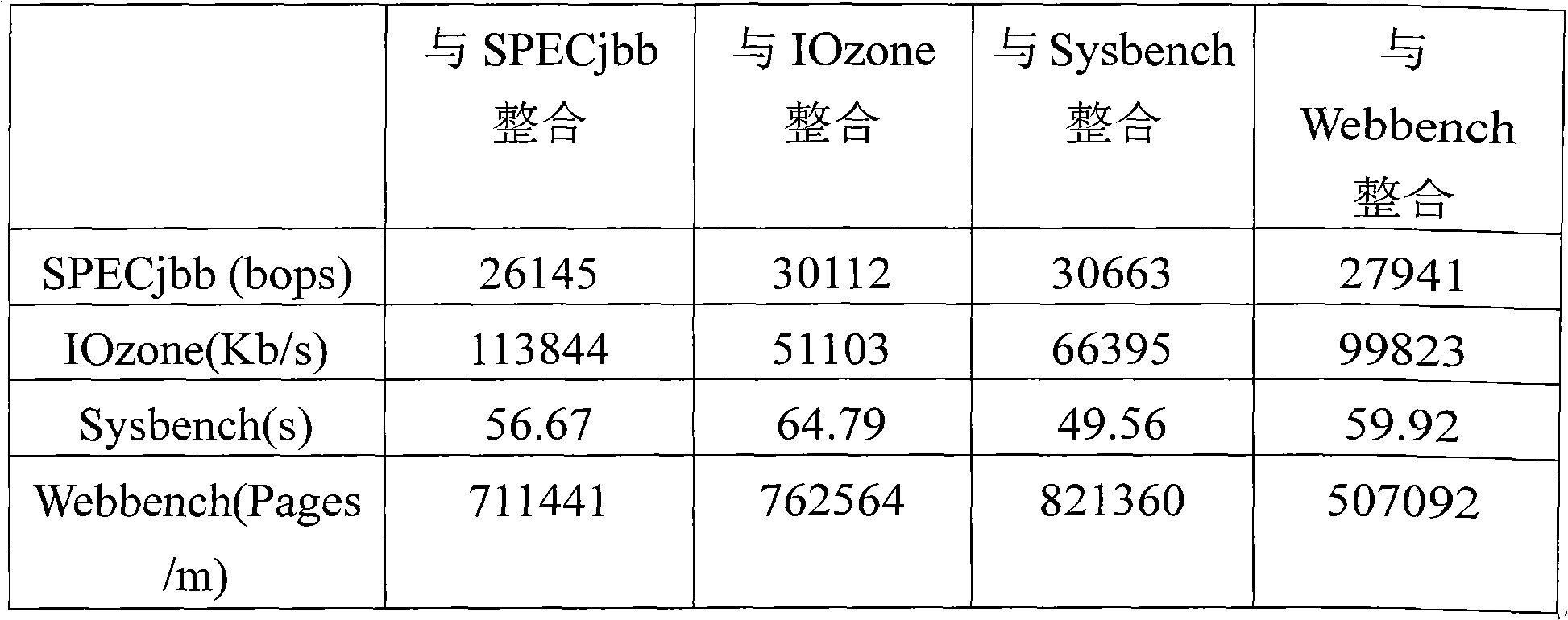
Energy-saving method of cloud data center based on virtual machine migration and load perception integration
ActiveCN102096461AGood technical effectAutomatic Dynamic ReintegrationEnergy efficient ICTMultiprogramming arrangementsVirtualizationComputer architecture
The invention relates to a system level virtualization technology and an energy-saving technology in the field of the structure of a computer system, and discloses an energy-saving method of a cloud data center based on virtual machine migration and load perception integration. The method comprises the steps: dynamically completing the migration and the reintegration of the load of a virtual machine in the cloud data center by monitoring the resource utilization rate of a physical machine and the virtual machine and the resource use condition of current each physical server under the uniform coordination and control of an optimized integration strategy management module of the load perception and an on-line migration control module of the virtual machine, and tuning off the physical servers which run without the load, so that the total use ratio of the server resource is improved, and the aim of energy saving is achieved. The energy-saving method of the cloud data center based on the virtual machine on-line migration and the load perception integration technology is effectively realized, the amount of the physical servers which are actually demanded by the cloud data center is reduced, and the green energy saving is realized.
Owner:ZHEJIANG UNIV
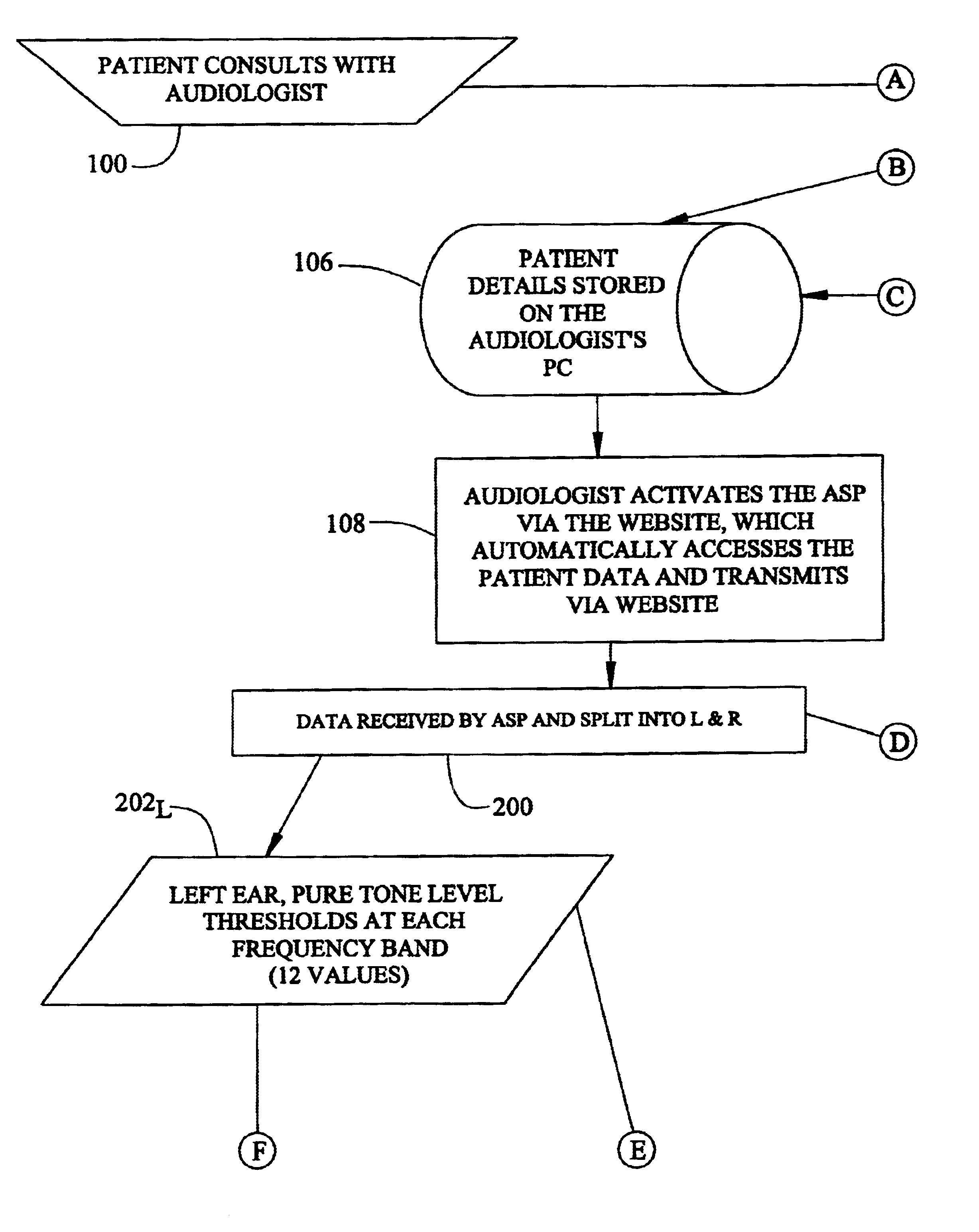
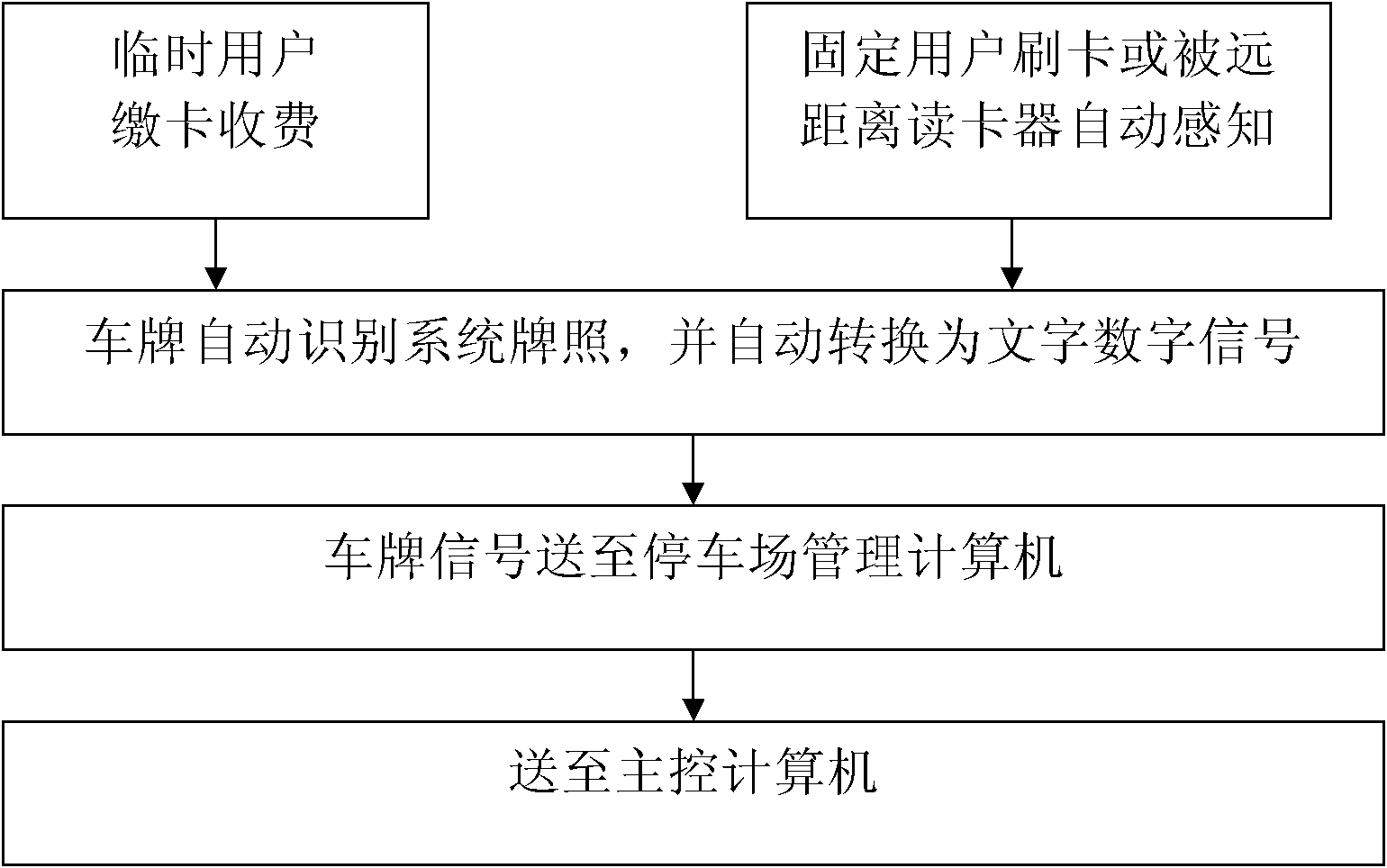
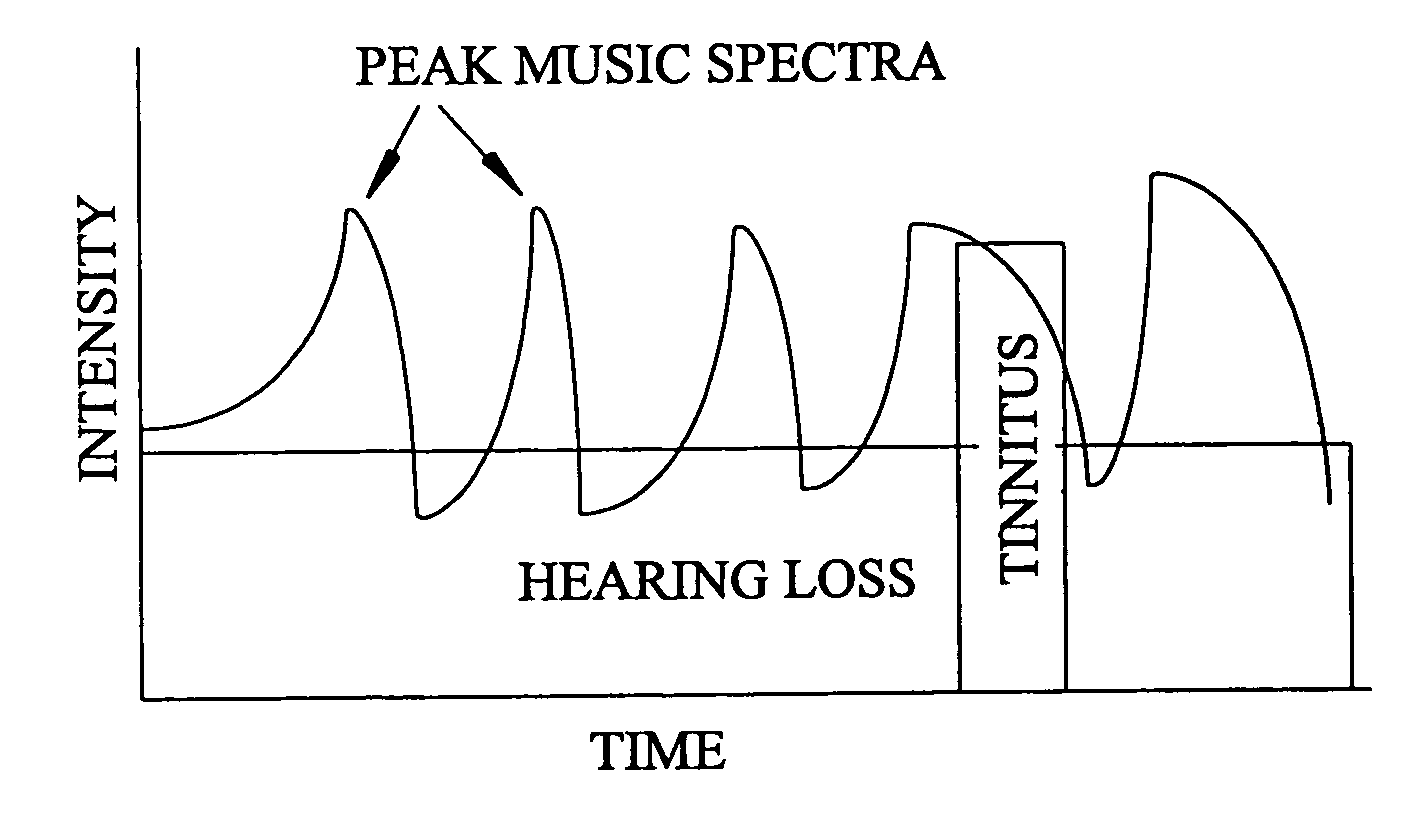
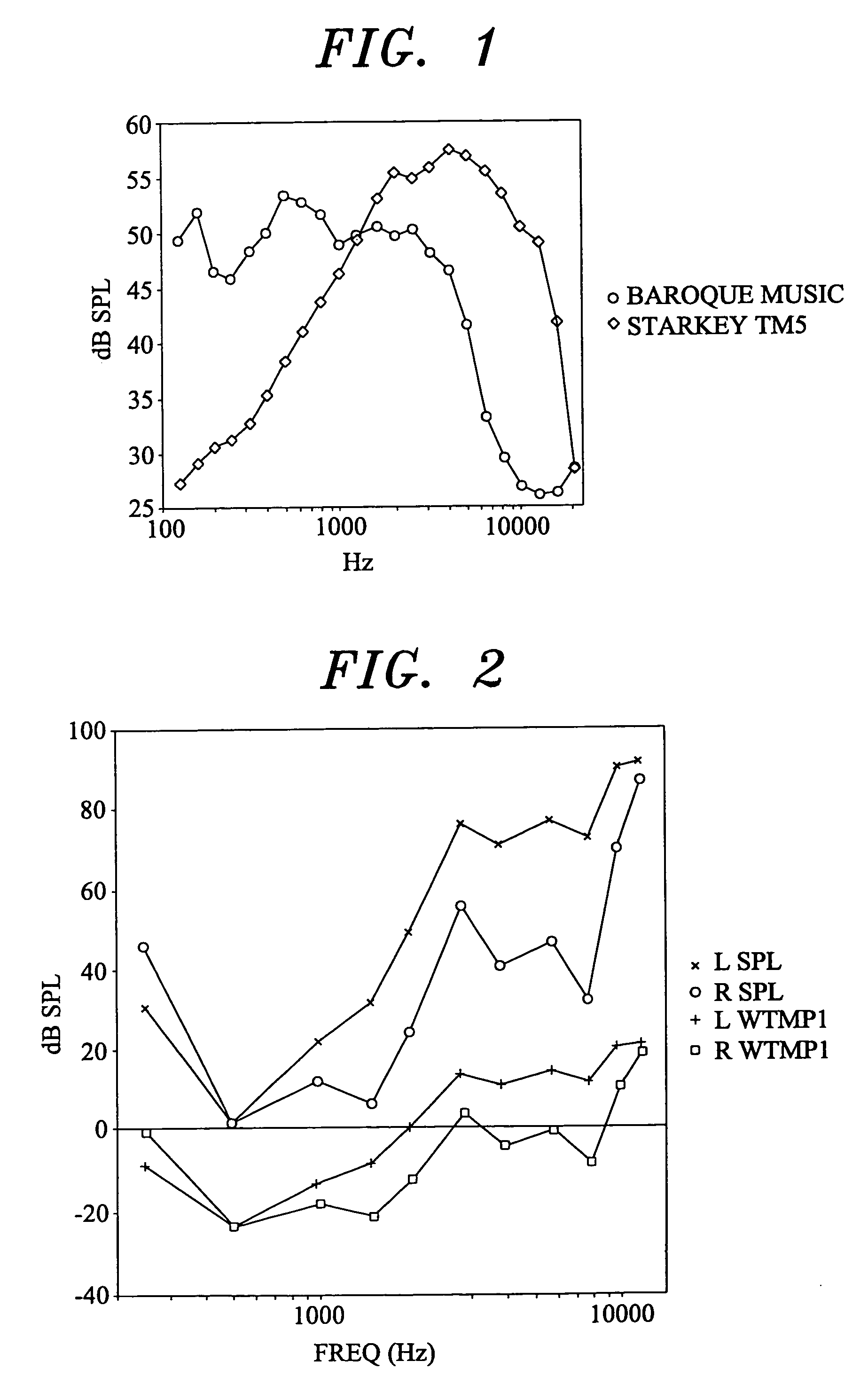
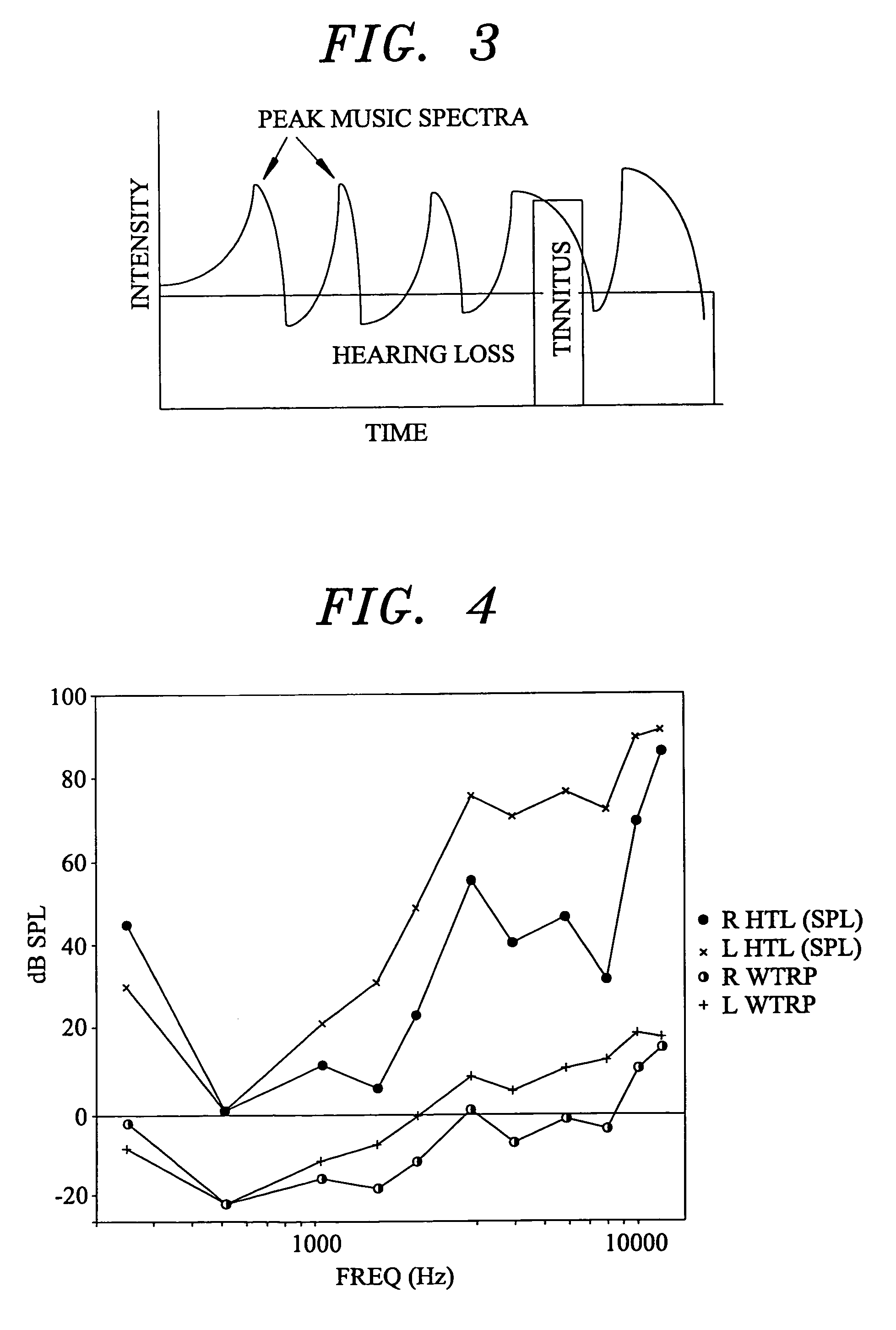
Tinnitus rehabilitation device and method
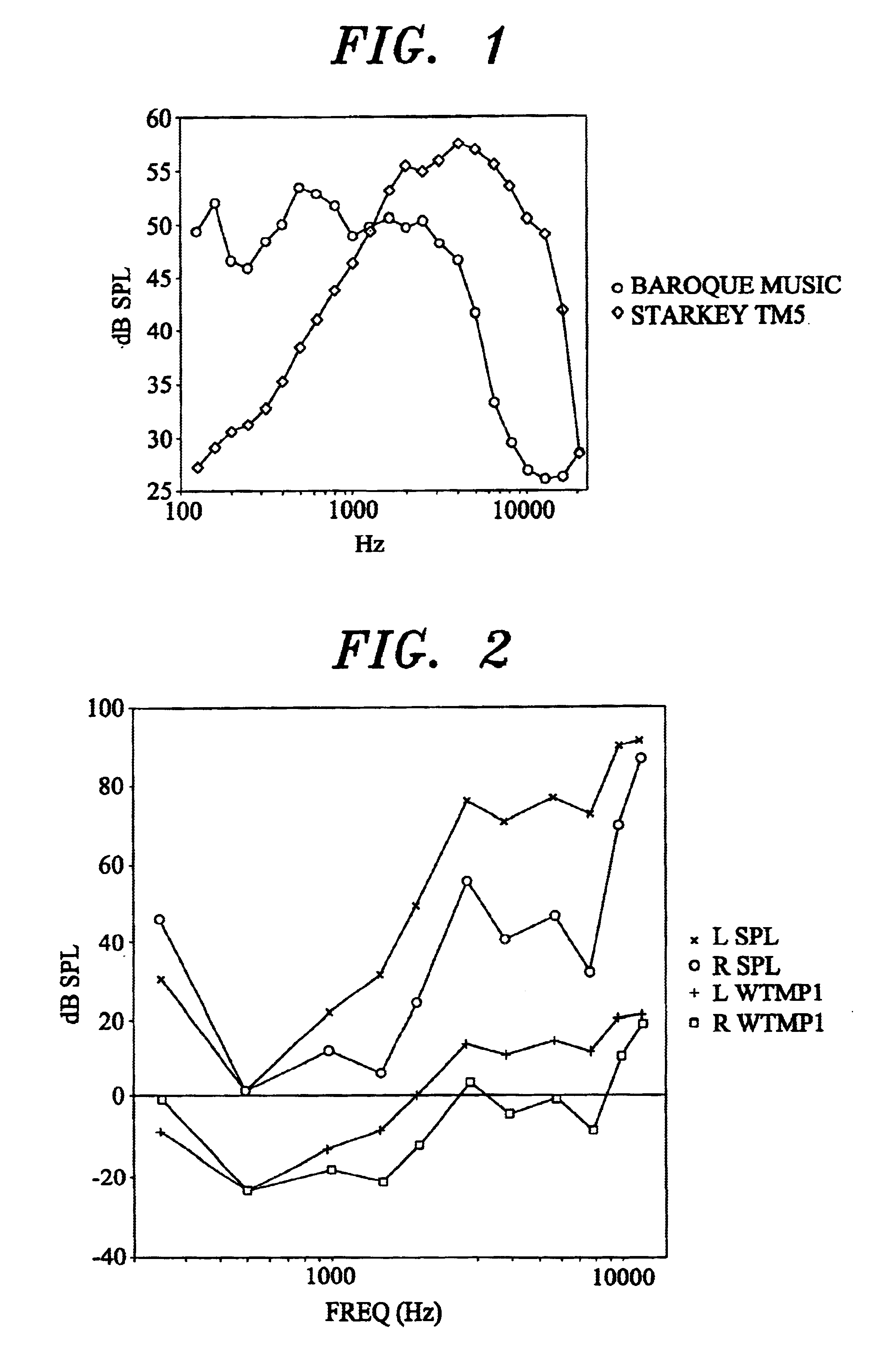
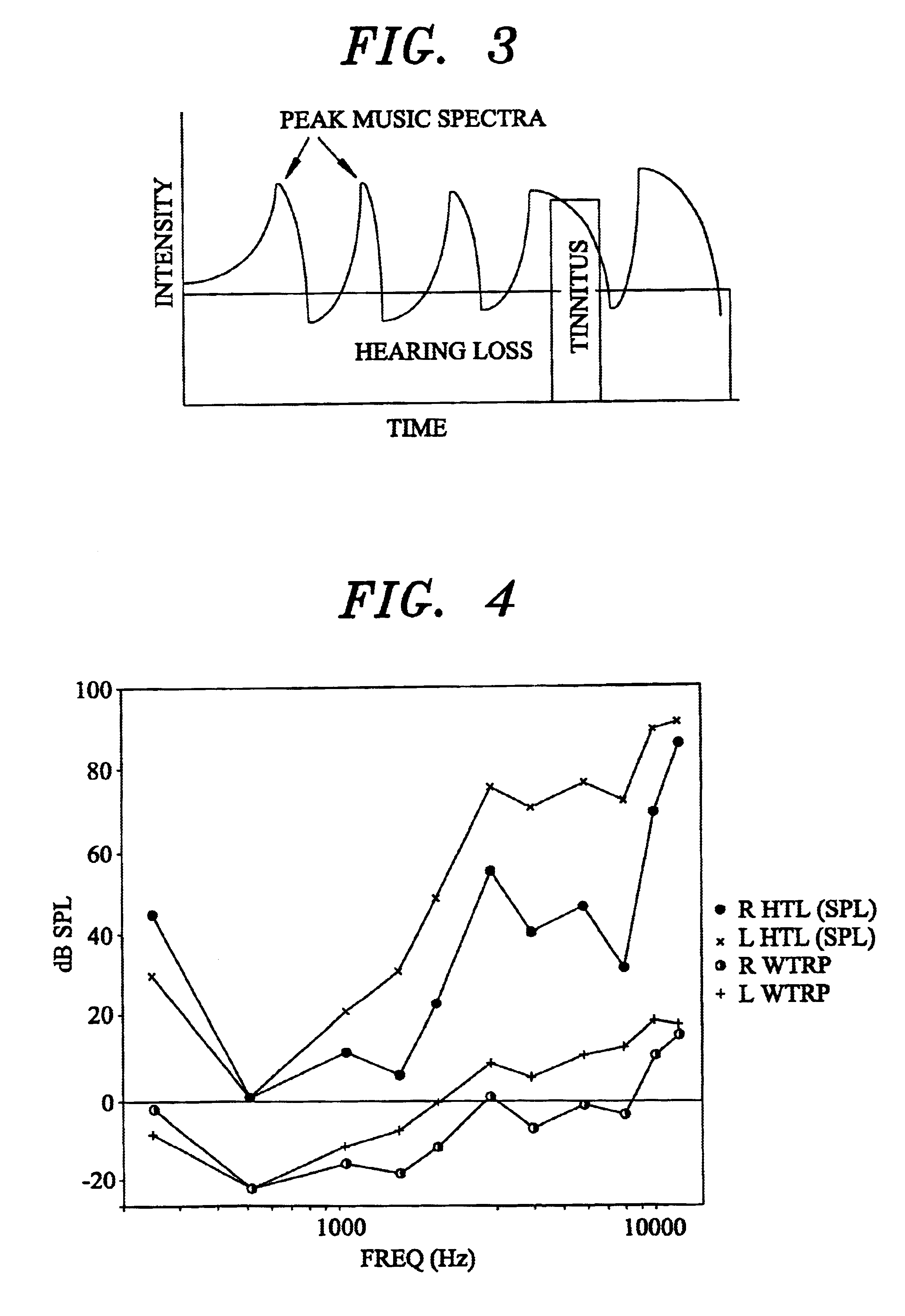
InactiveUS6682472B1Technique is effectiveEar treatmentElectric tinnitus maskersFrequency spectrumHabituation
A tinnitus method and device for providing relief to a person suffering from the disturbing effects of tinnitus is described. The method can be implemented entirely in software to spectrally modify an audio signal in accordance with a predetermined masking algorithm which modifies the intensity of the audio signal at selected frequencies. A predetermined masking algorithm is described which provides intermittent masking of the tinnitus wherein, at a comfortable listening level, during peaks of the audio signal the tinnitus is completely obscured, whereas during troughs the perception of the tinnitus occasionally emerges. In practice it has been found that such intermittent masking provides an immediate sense of relief, control and relaxation for the person, whilst enabling sufficient perception of the tinnitus for habituation and long term treatment to occur. Advantageously the predetermined masking algorithm is specifically tailored to the audiometric configuration of the person. For example, the masking algorithm may be partly tailored to the hearing loss characteristic of the person. A tinnitus rehabilitation device used in conjunction with a personal sound reproducing system is also described.
Owner:NEUROMONICS
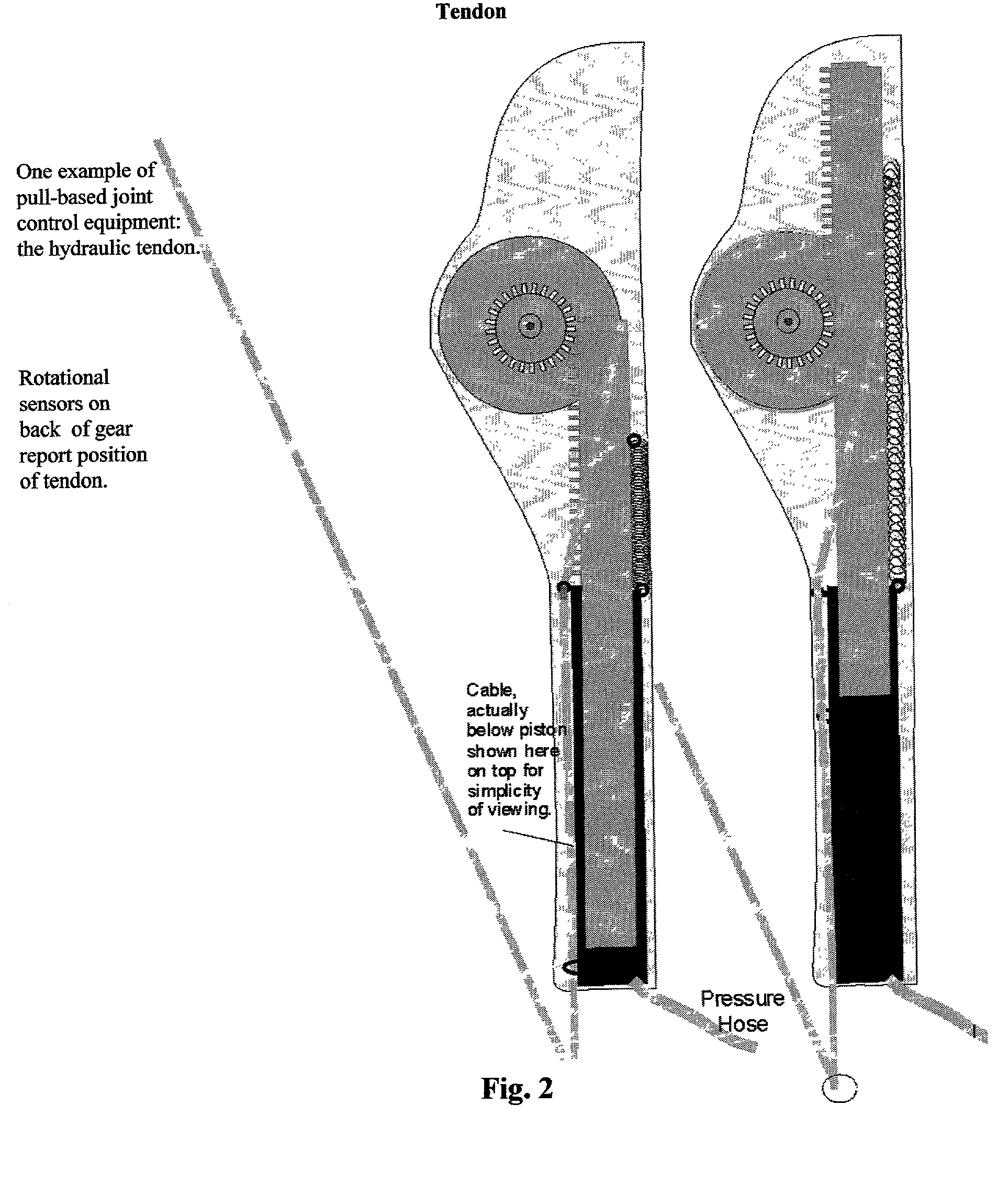
Natural robot control
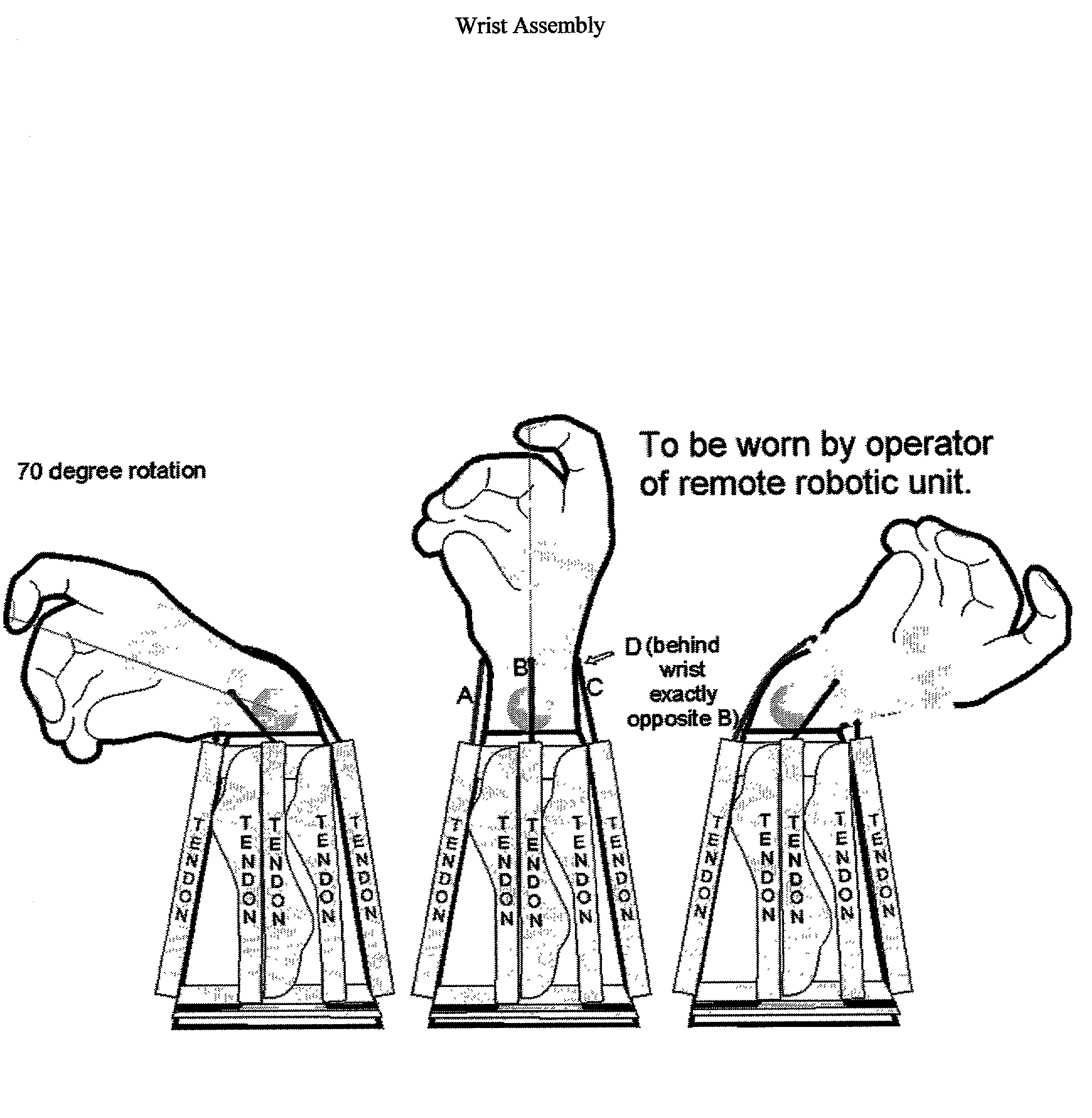
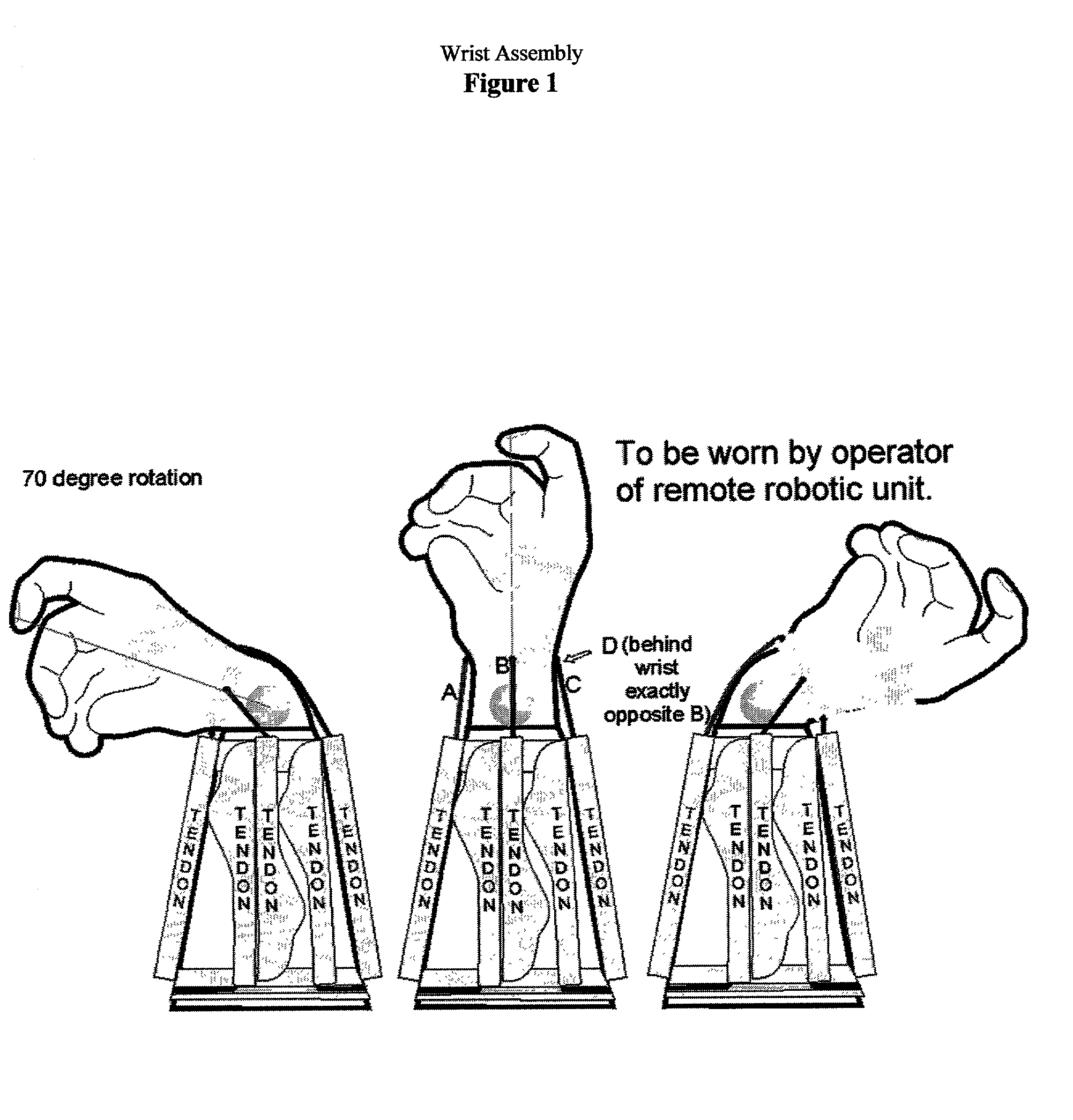
InactiveUS20030030397A1High dexterityAccurate pressureInput/output for user-computer interactionProgramme-controlled manipulatorVirtual worldEngineering
An apparatus and process for controlling a remote robot responsive to the integrated sensory perceptions, natural body movements, inertia and gravitation of an operator / user who is himself responding to a three dimensional virtual world of visual and sensory conditions responsive to the environment at the remote site where the robot is operating. The user requires no training, special commands or devices to direct the robot because the user has the perception of actually being at the remote location, handling remote objects he sees and feels in his hands, walking, climbing, viewing and feeling the remote world.
Owner:SIMMONS JOHN CASTLE
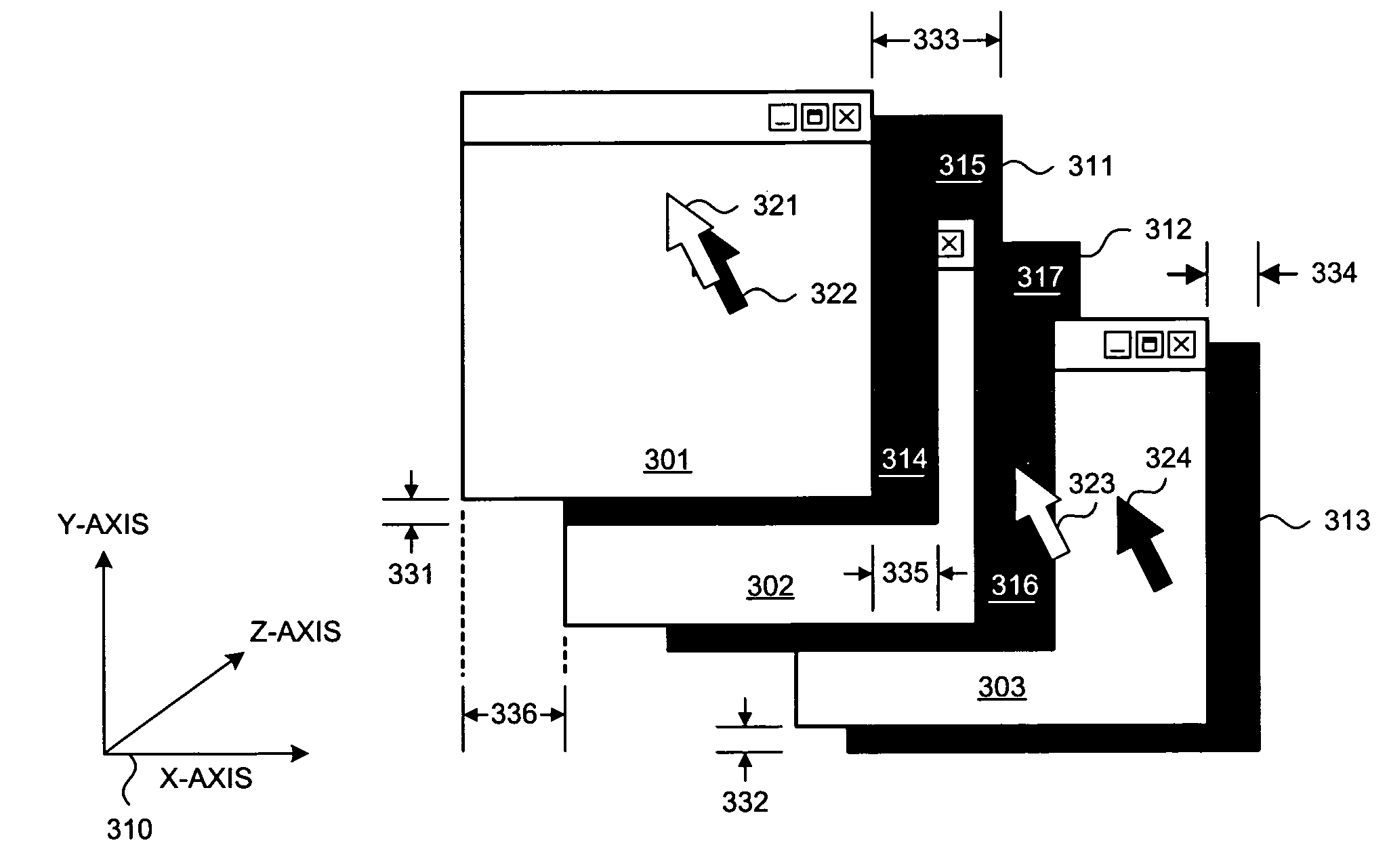
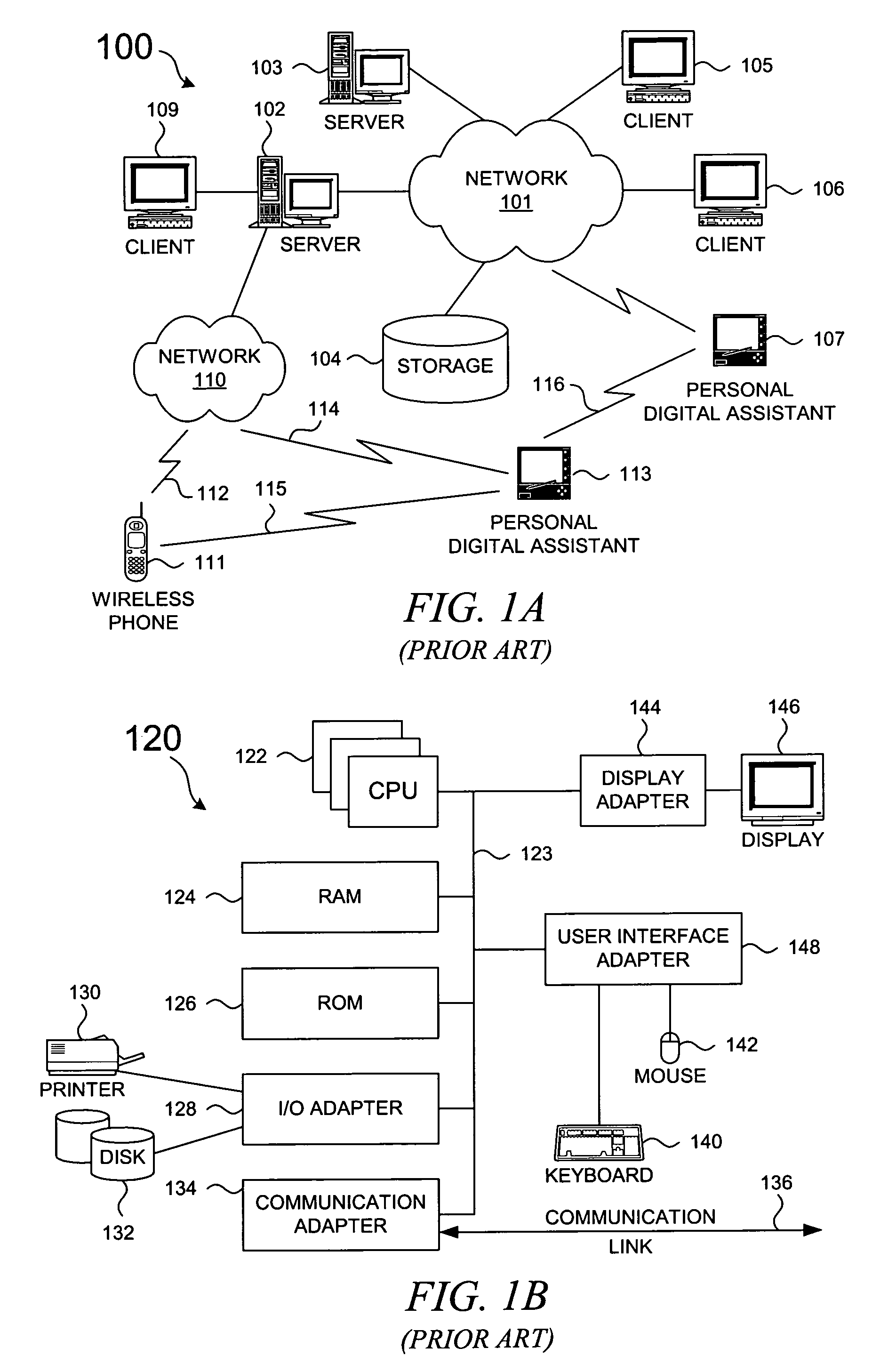
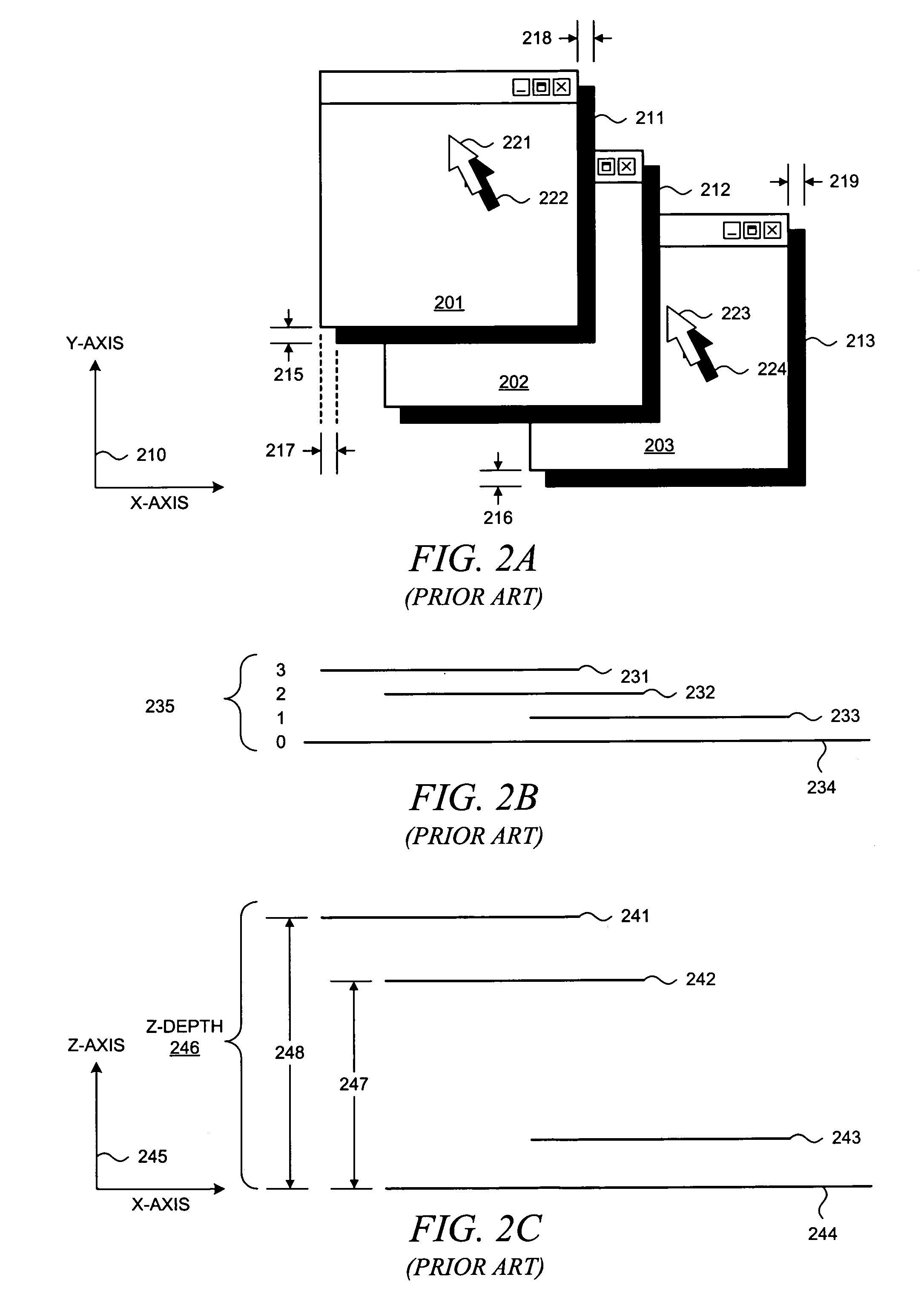
Method and system for producing dynamically determined drop shadows in a three-dimensional graphical user interface
InactiveUS7439975B2Cathode-ray tube indicatorsInput/output processes for data processingGraphicsGraphical user interface
A methodology for generating a drop shadow effect for objects in a graphical user interface is presented. A first object in a presentation space occludes the illumination from a simulated light source, and a dynamically determined drop shadow from the first object may partially occlude a second object. A portion of a drop shadow from the first object is shown on the second object; the portion of the drop shadow from the first object is displaced from the first object in direct proportion to a z-depth difference between the first object and the second object. Hence, a drop shadow can be generated in a computationally inexpensive manner, and the dynamically determined drop shadow enhances the perception of depth within the presentation space by a user.
Owner:ACTIVISION PUBLISHING
Whiteness perception compositions
InactiveUS7686892B2Inorganic/elemental detergent compounding agentsOrganic detergent compounding agentsPattern perceptionOrganic chemistry
The present invention relates to cleaning and / or treatment compositions comprising a dye conjugate, and processes of making and using such compositions. Such compositions can provide benefits such as an increase in the whiteness or blackness perception of a situs that is cleaned or treated with such compositions.
Owner:PROCTER & GAMBLE CO
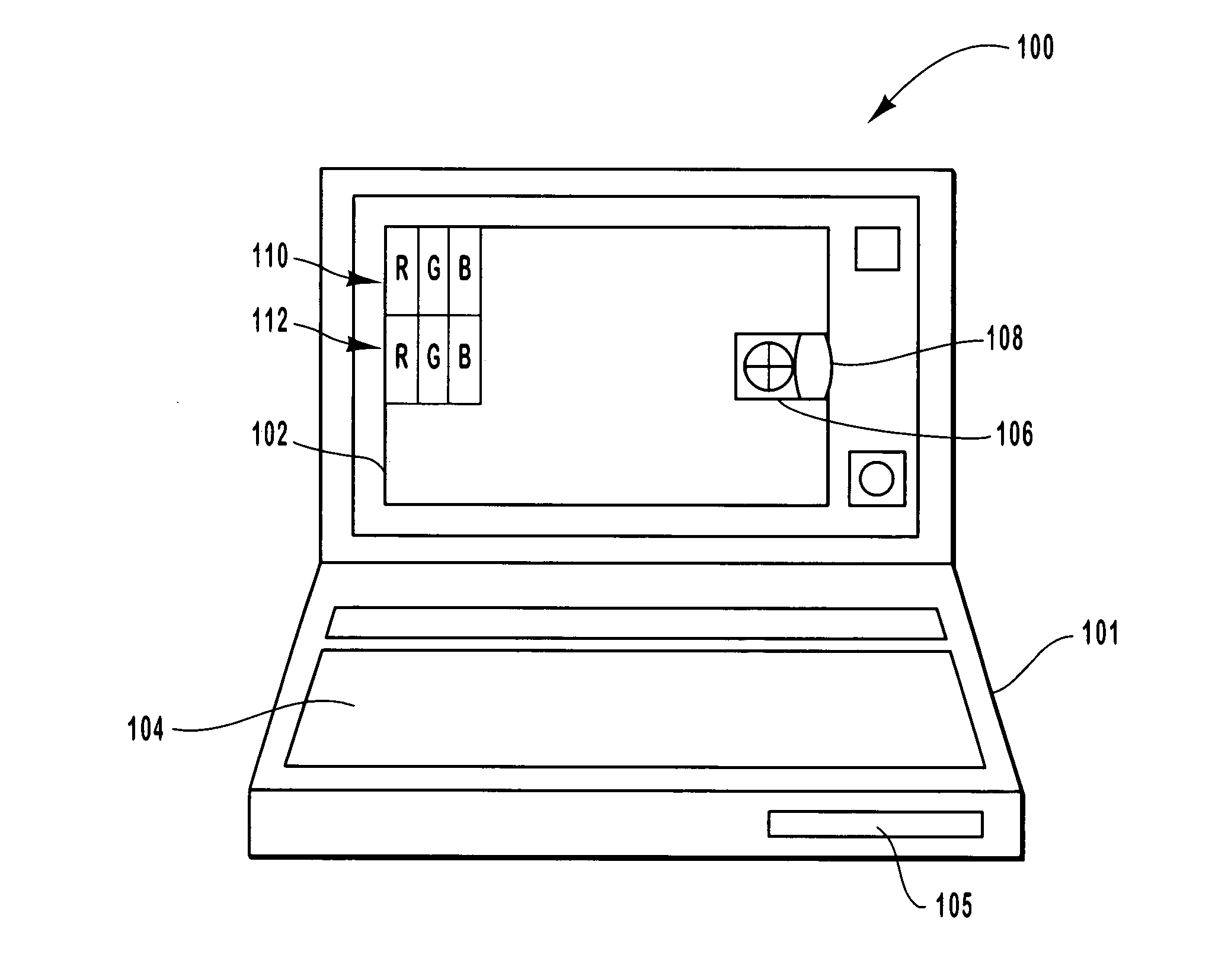
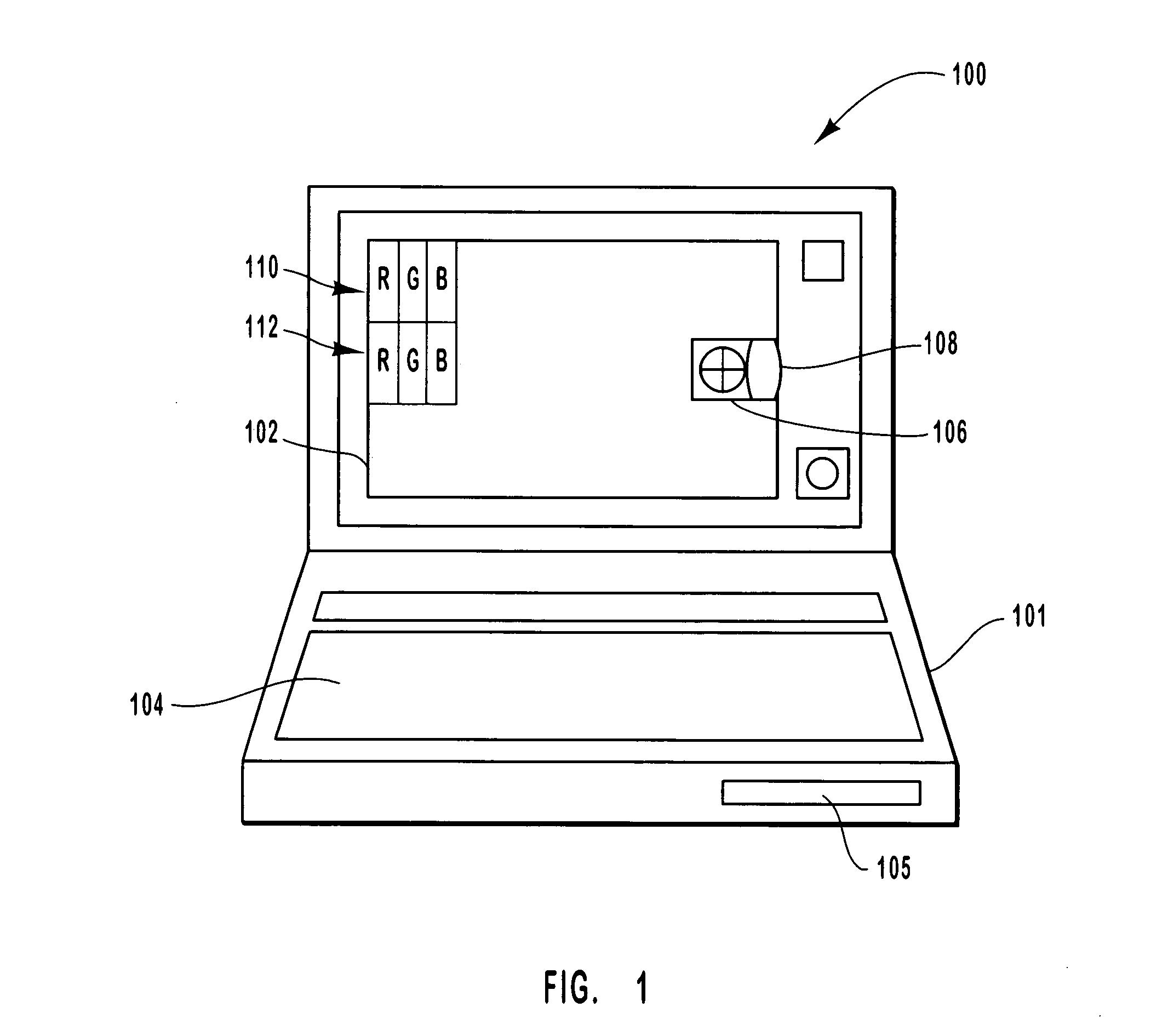
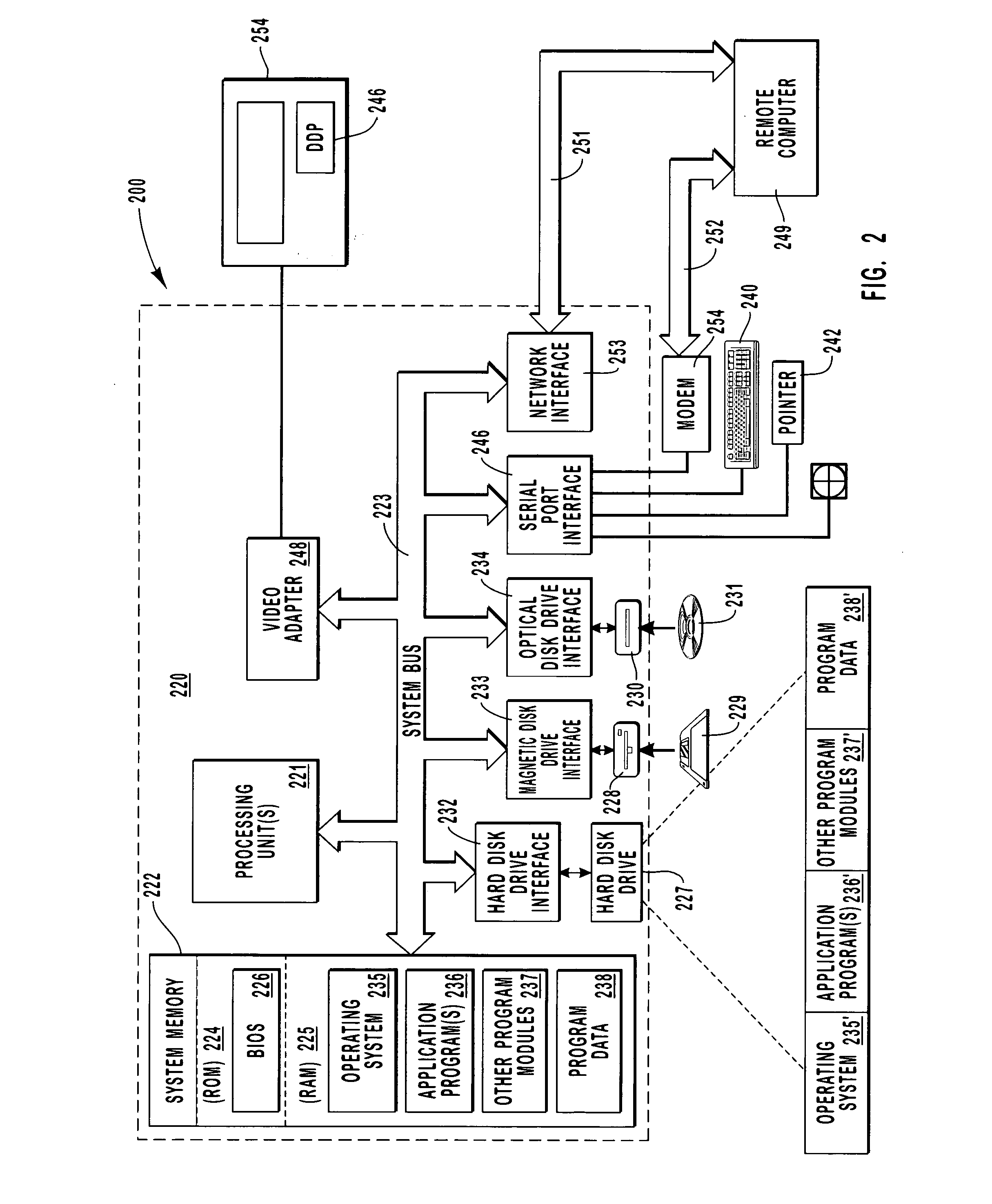
Quality of displayed images with user preference information
InactiveUS20040008208A1Improve perceived qualityImprove image qualityCathode-ray tube indicatorsHousing of computer displaysImaging qualityDisplay device
The present invention relates to methods and apparatus for increasing the perceived quality of displayed images. This is achieved in a variety of ways including the use of a plurality of device specific display characteristics when preparing images for display. It is also achieved through the monitoring of display device and / or ambient light conditions, e.g., on a periodic basis, and using the obtained information when controlling display output. Another approach to improving the perceived quality of displayed images involves the use of information relating to a specific user's ability to perceive image characteristics such as color. By customizing display output to an individual user's own physical perception capabilities and / or viewing characteristics it is possible to enhance the image quality perceived by the individual viewer as compared to embodiments which do not take into consideration individual user characteristics.
Owner:MICROSOFT TECH LICENSING LLC
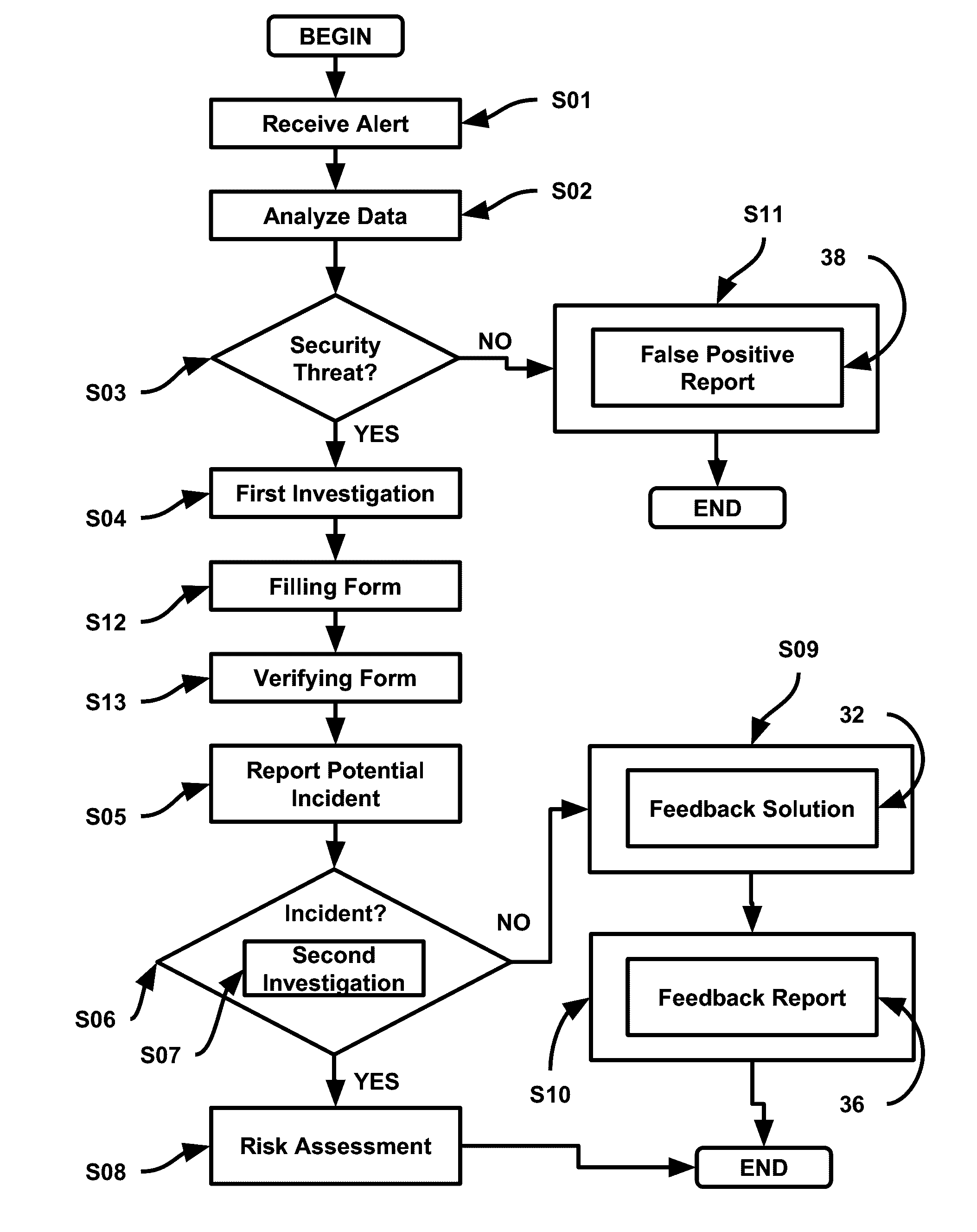
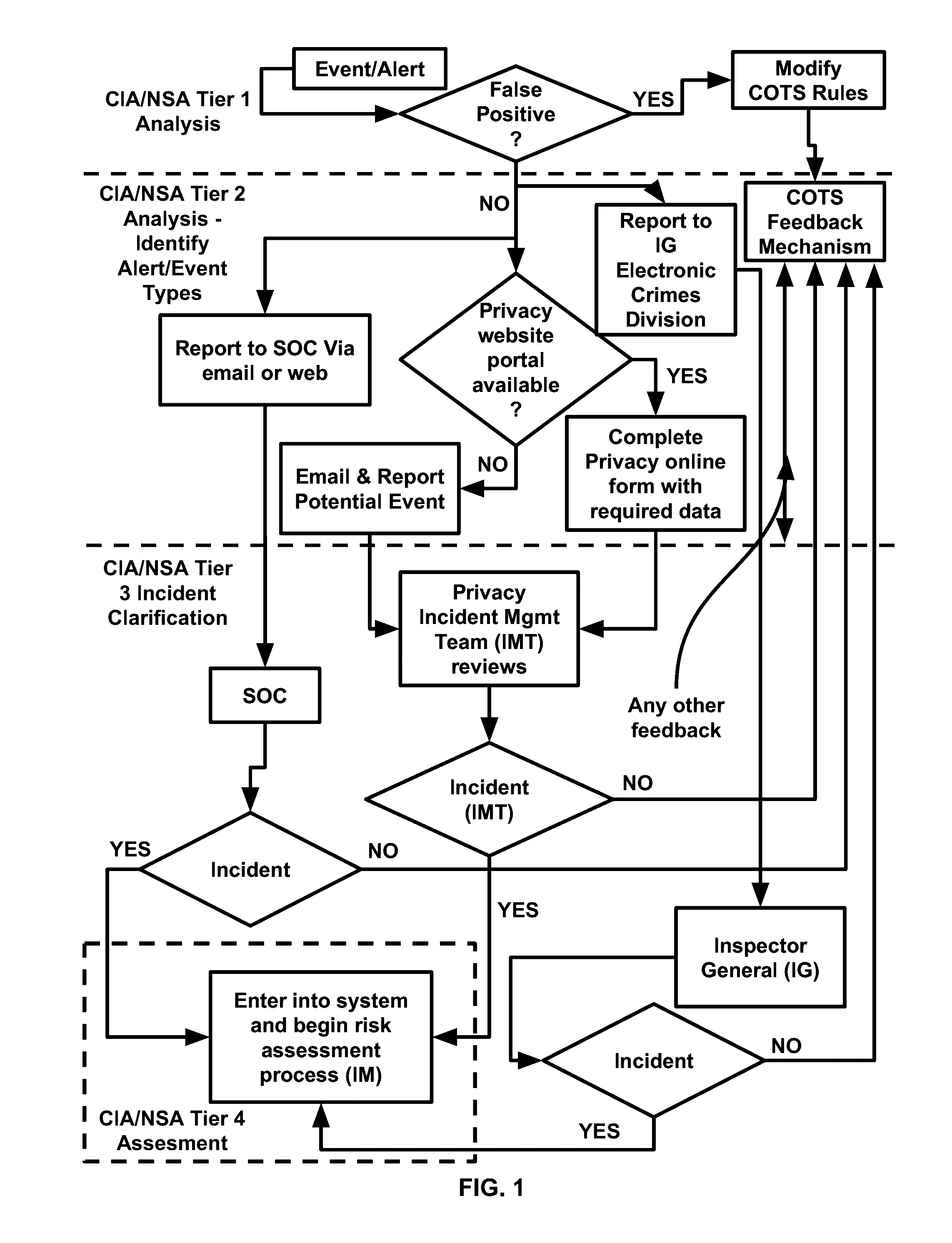
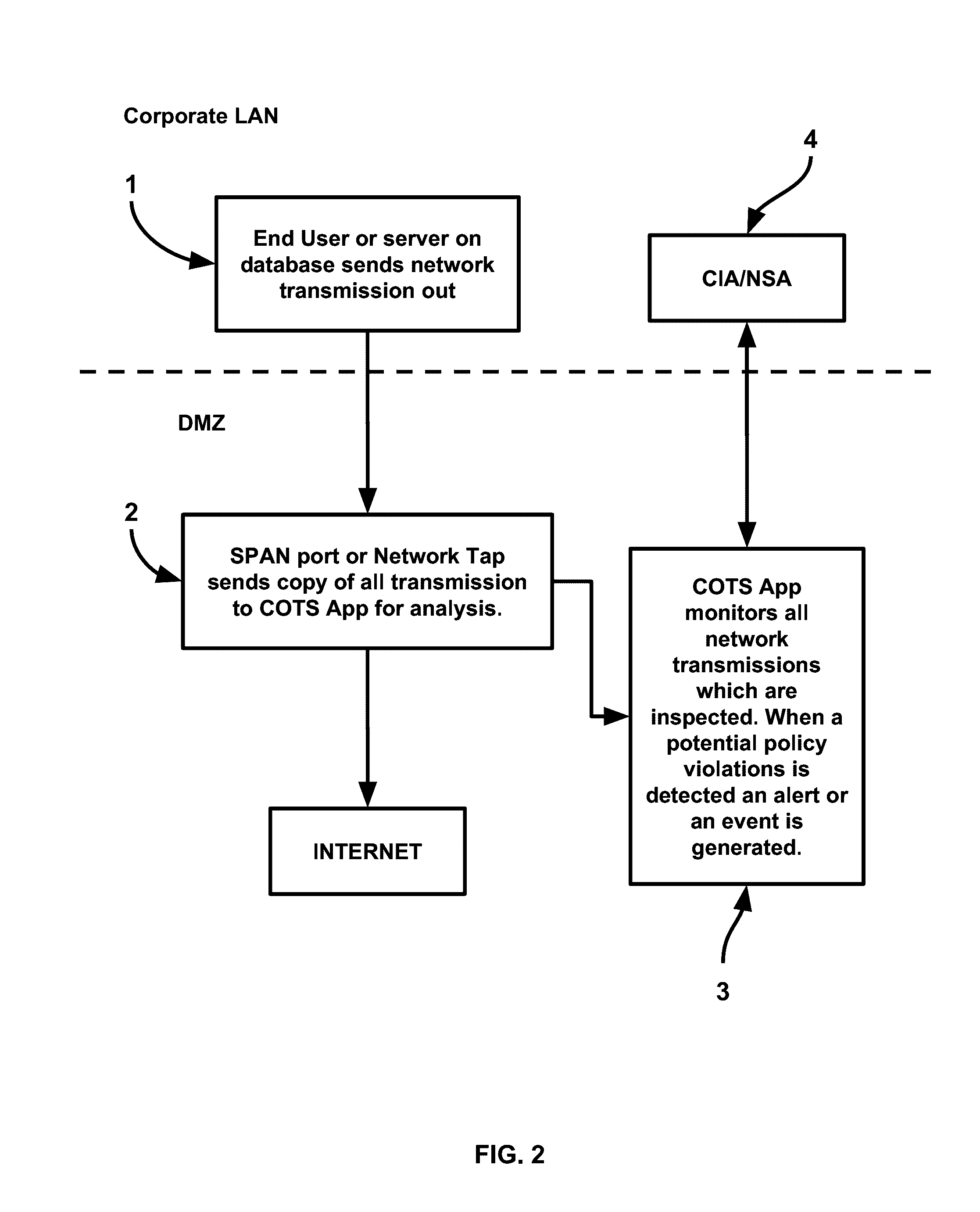
Method and device for managing security in a computer network
InactiveUS20160330219A1Speed up iterationShorten the timeNavigation instrumentsKnowledge representationInteraction systemsInformation type
Method and device for managing security in a computer network include algorithms of iterative intelligence growth, iterative evolution, and evolution pathways; sub-algorithms of information type identifier, conspiracy detection, media scanner, privilege isolation analysis, user risk management and foreign entities management; and modules of security behavior, creativity, artificial threat, automated growth guidance, response / generic parser, security review module and monitoring interaction system. Applications include malware predictive tracking, clandestine machine intelligence retribution through covert operations in cyberspace, logically inferred zero-database a-priori realtime defense, critical infrastructure protection & retribution through cloud & tiered information security, and critical thinking memory & perception.
Owner:HASAN SYED KAMRAN
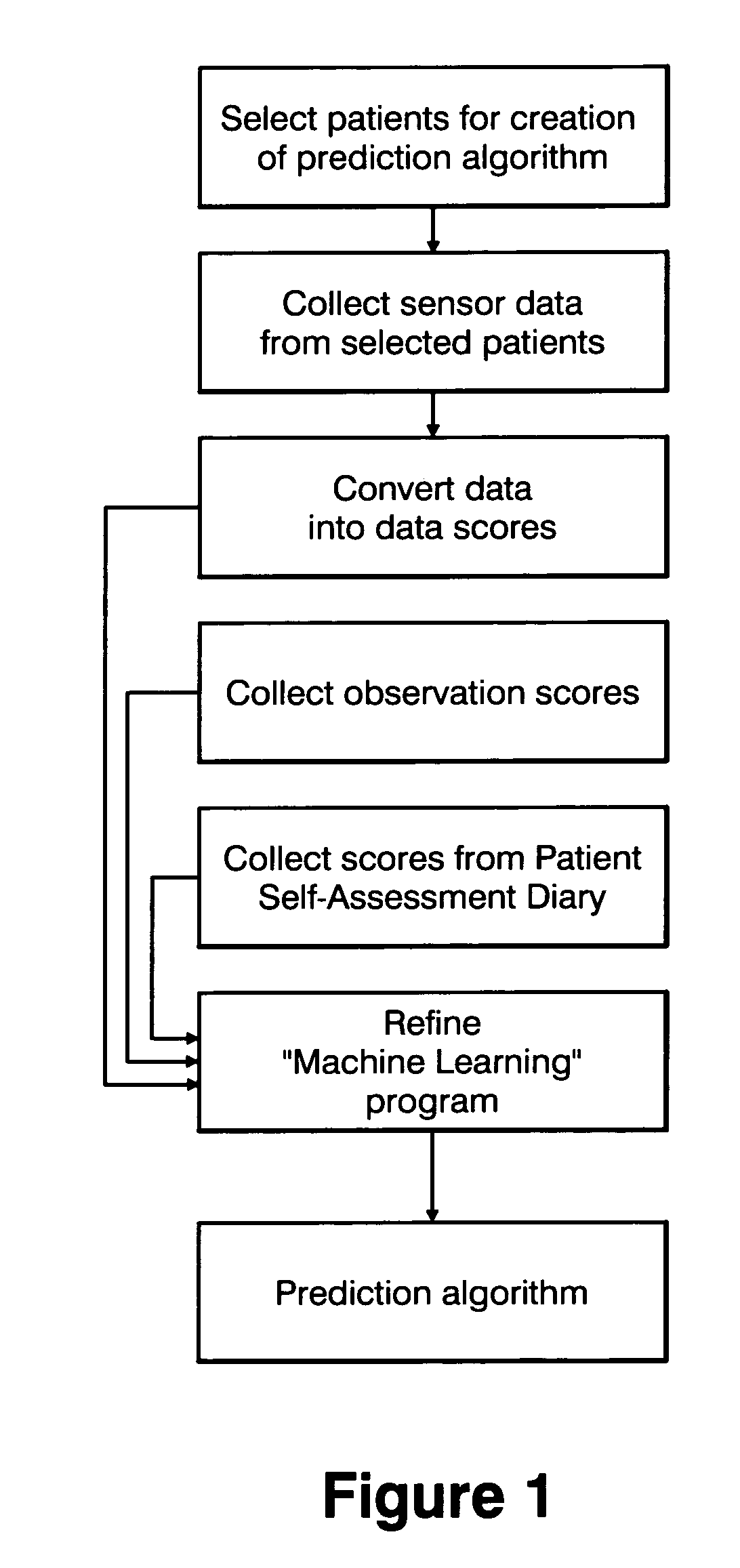
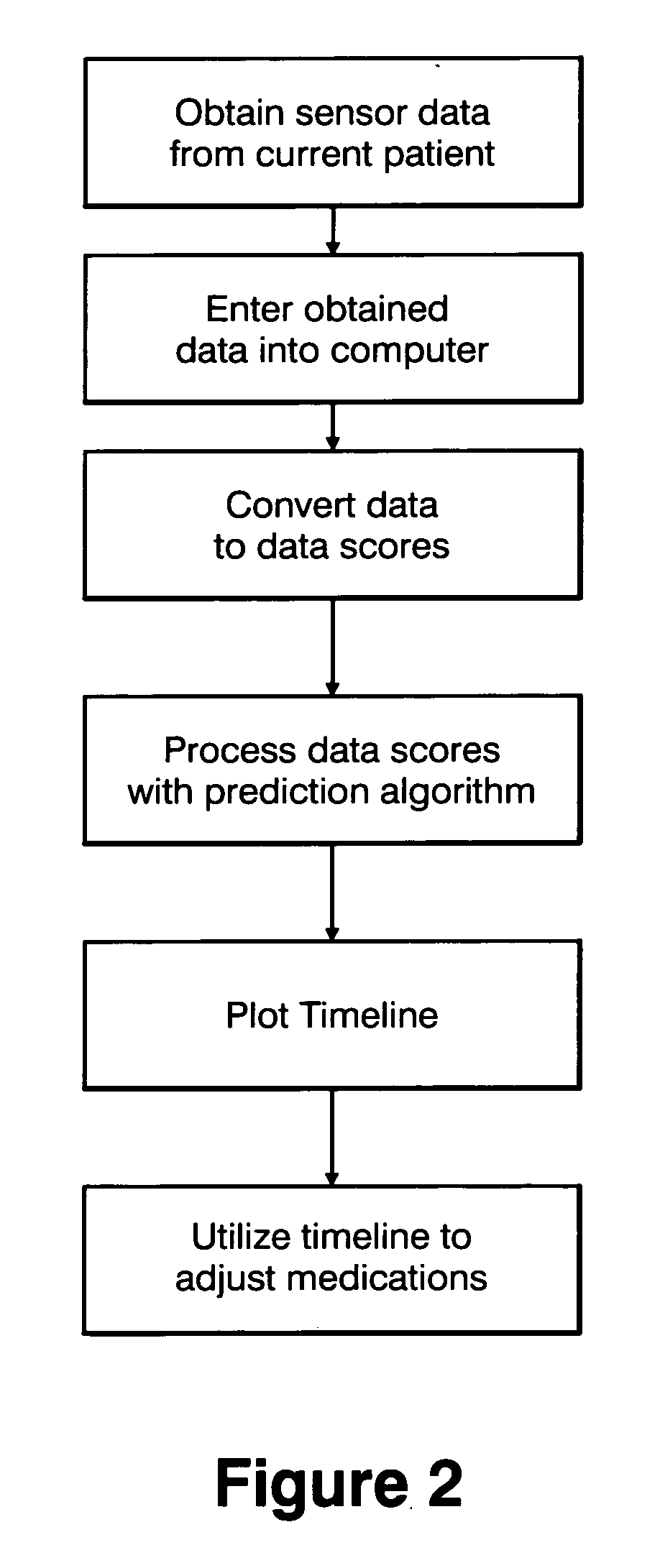
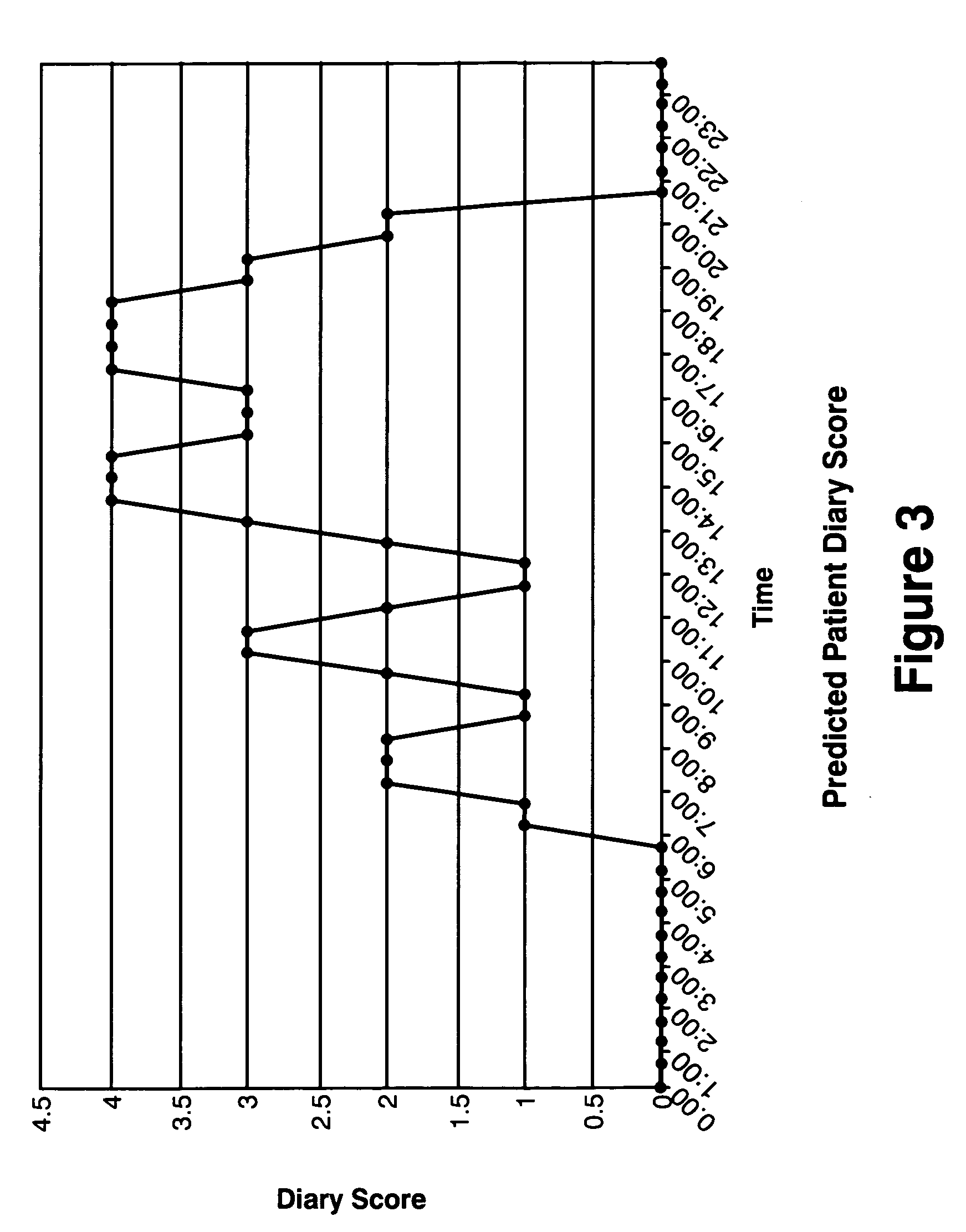
Method and apparatus for classification of movement states in Parkinson's disease
InactiveUS20050234309A1Easy to predictInertial sensorsMedical automated diagnosisAccelerometerClinical psychology
For Parkinson's patients to function at their best, their medications need to be optimally adjusted to the diurnal variation of symptoms. For this to occur, it is important for the managing clinician to have an accurate picture of how the patient's bradykinesia / hypokinesia and dyskinesia and the patient's perception of movement state fluctuate throughout the normal daily activities. The present invention uses wearable accelerometers coupled with computer implemented learning and statistical analysis techniques in order to classify the movement states of Parkinson's patients and to provide a timeline of how the patients fluctuate throughout the day.
Owner:PARK KINESIS INSTR
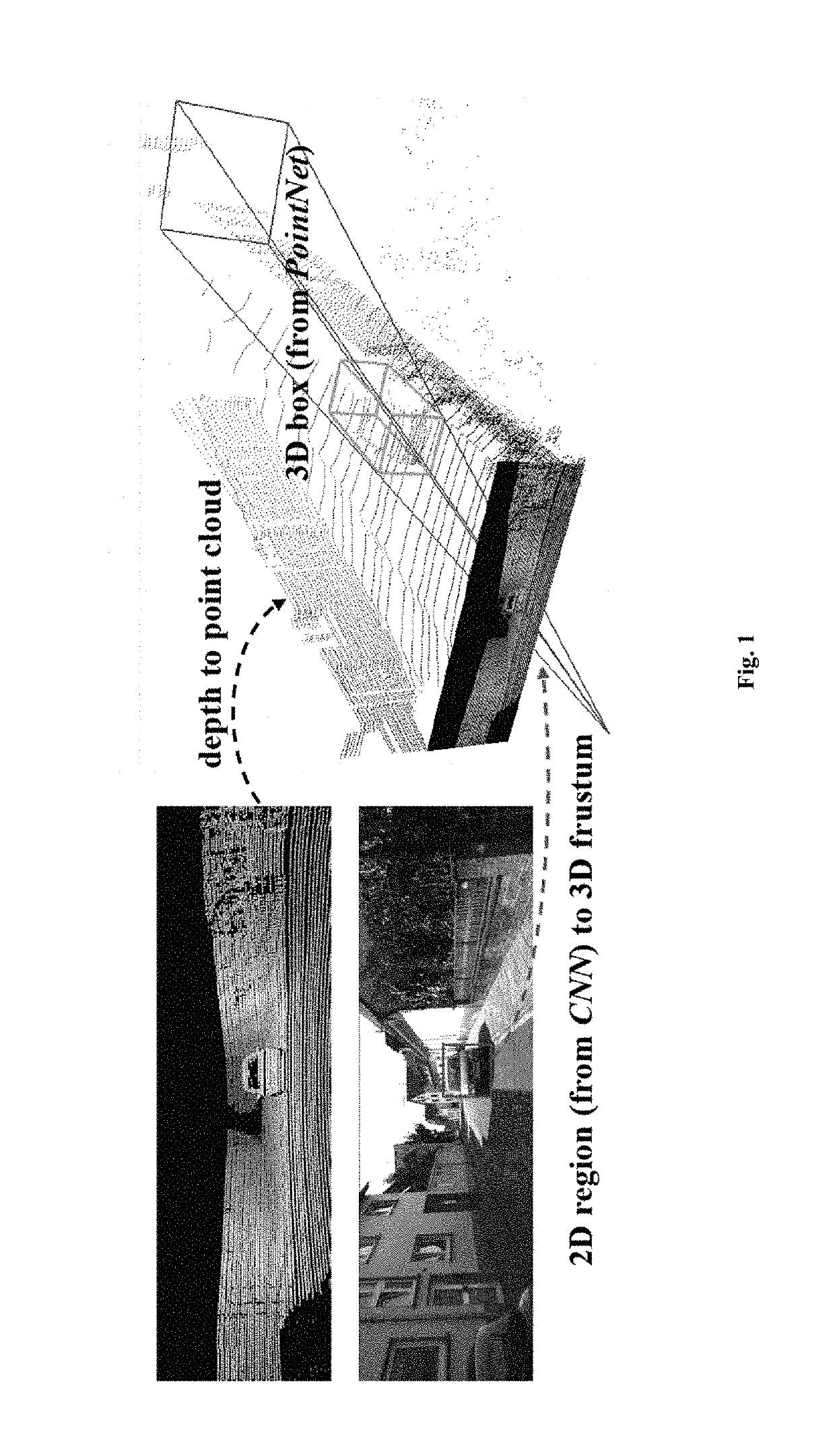
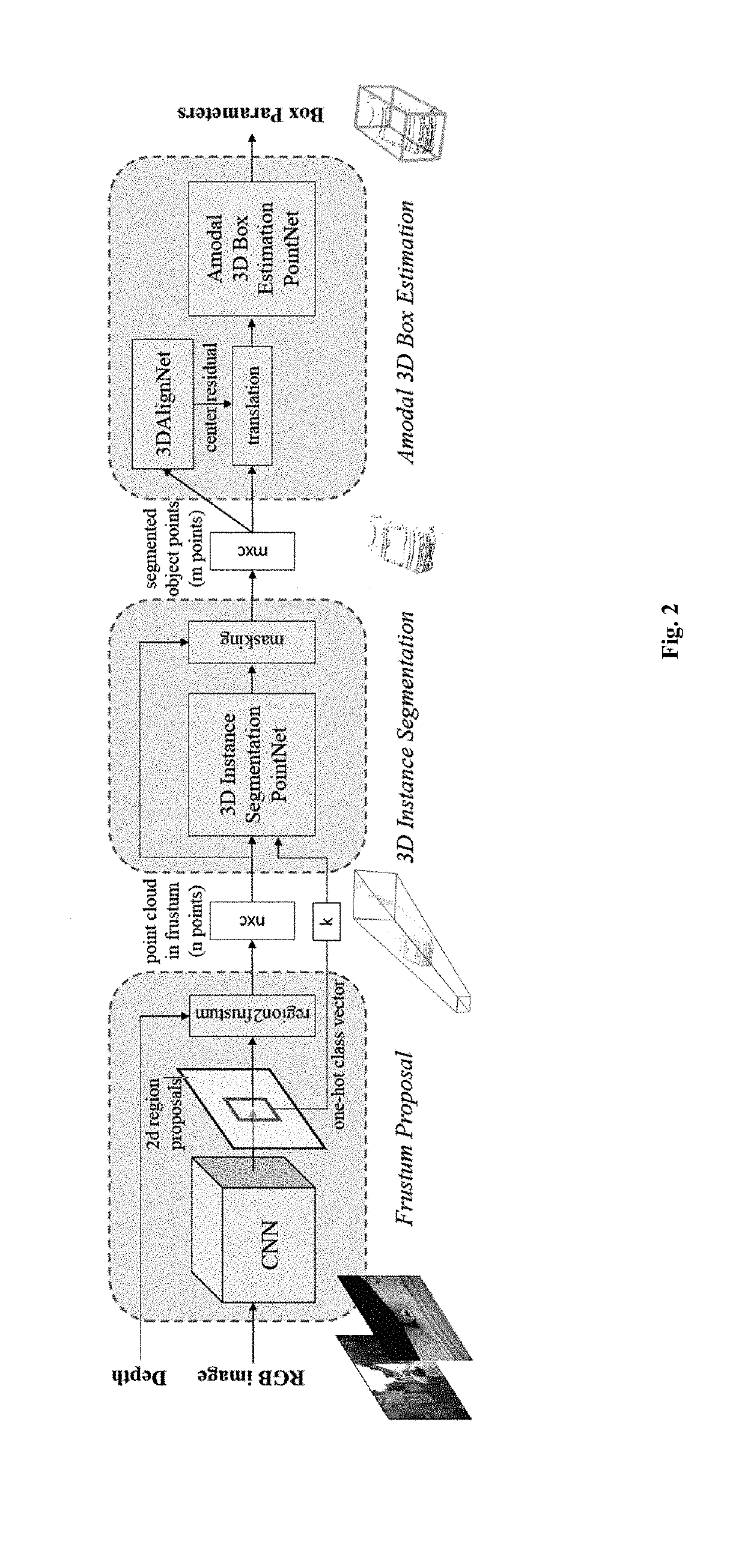
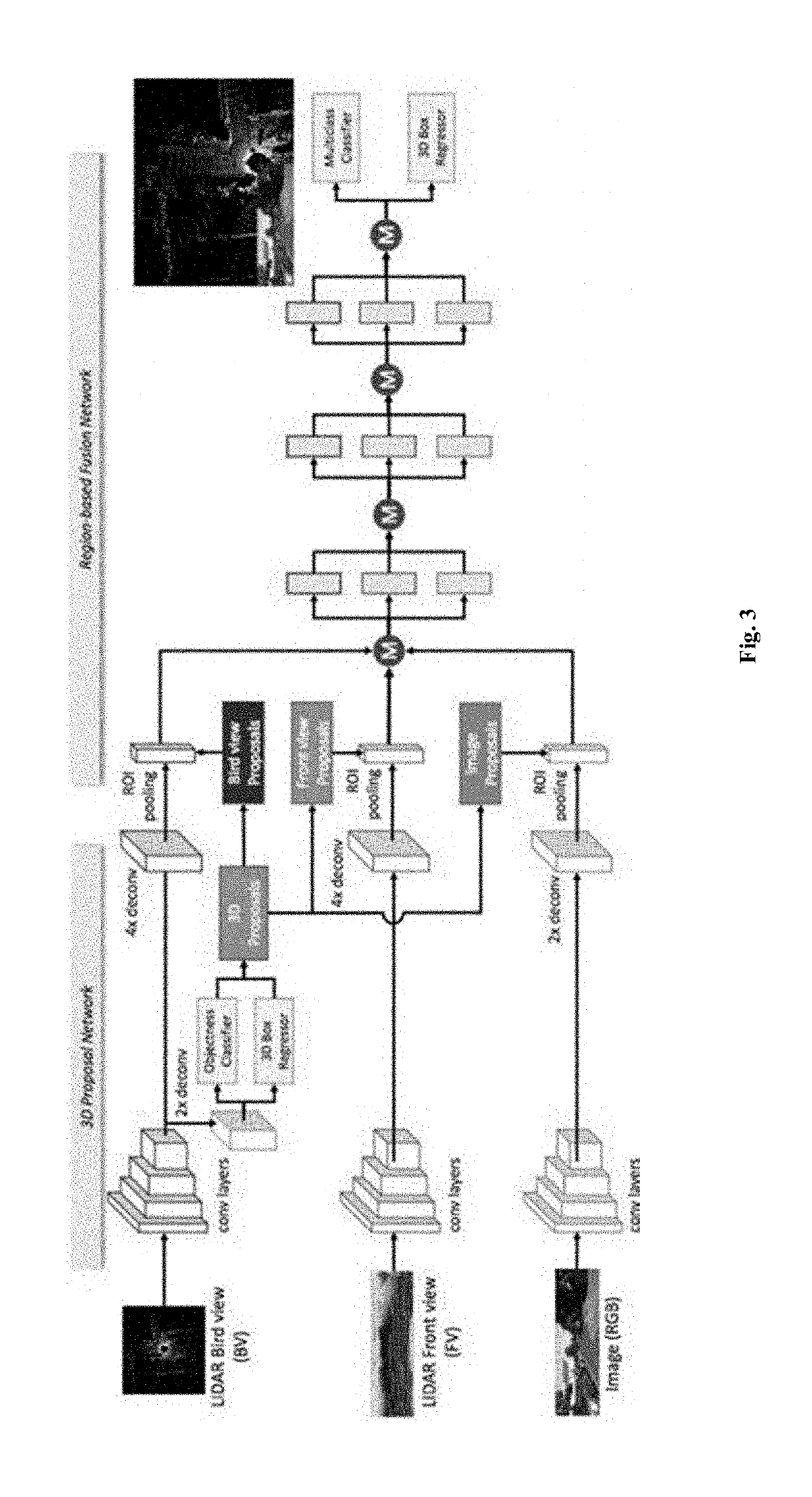
Three-dimensional object detection for autonomous robotic systems using image proposals
Provided herein are methods and systems for implementing three-dimensional perception in an autonomous robotic system comprising an end-to-end neural network architecture that directly consumes large-scale raw sparse point cloud data and performs such tasks as object localization, boundary estimation, object classification, and segmentation of individual shapes or fused complete point cloud shapes.
Owner:NURO INC
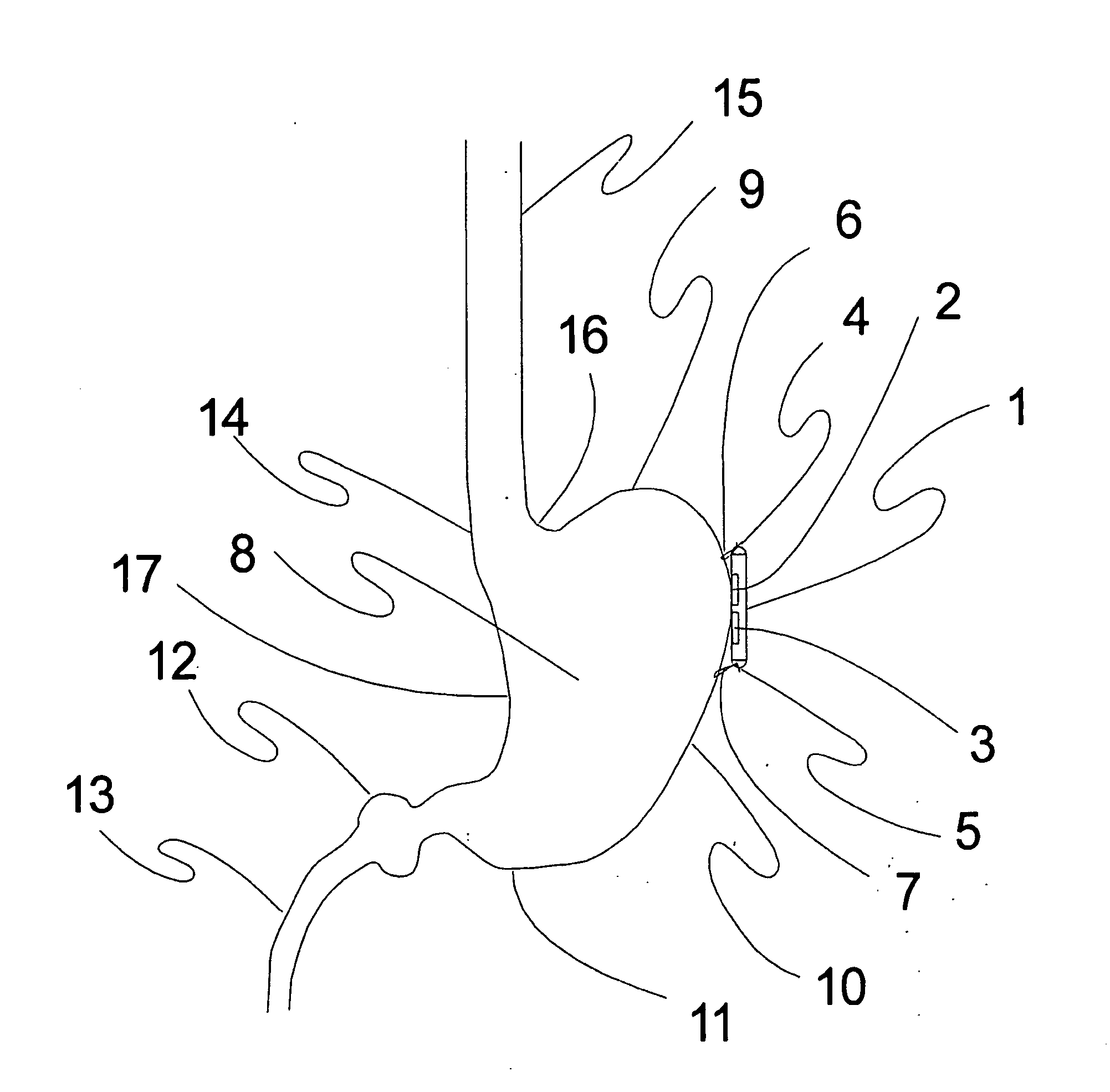
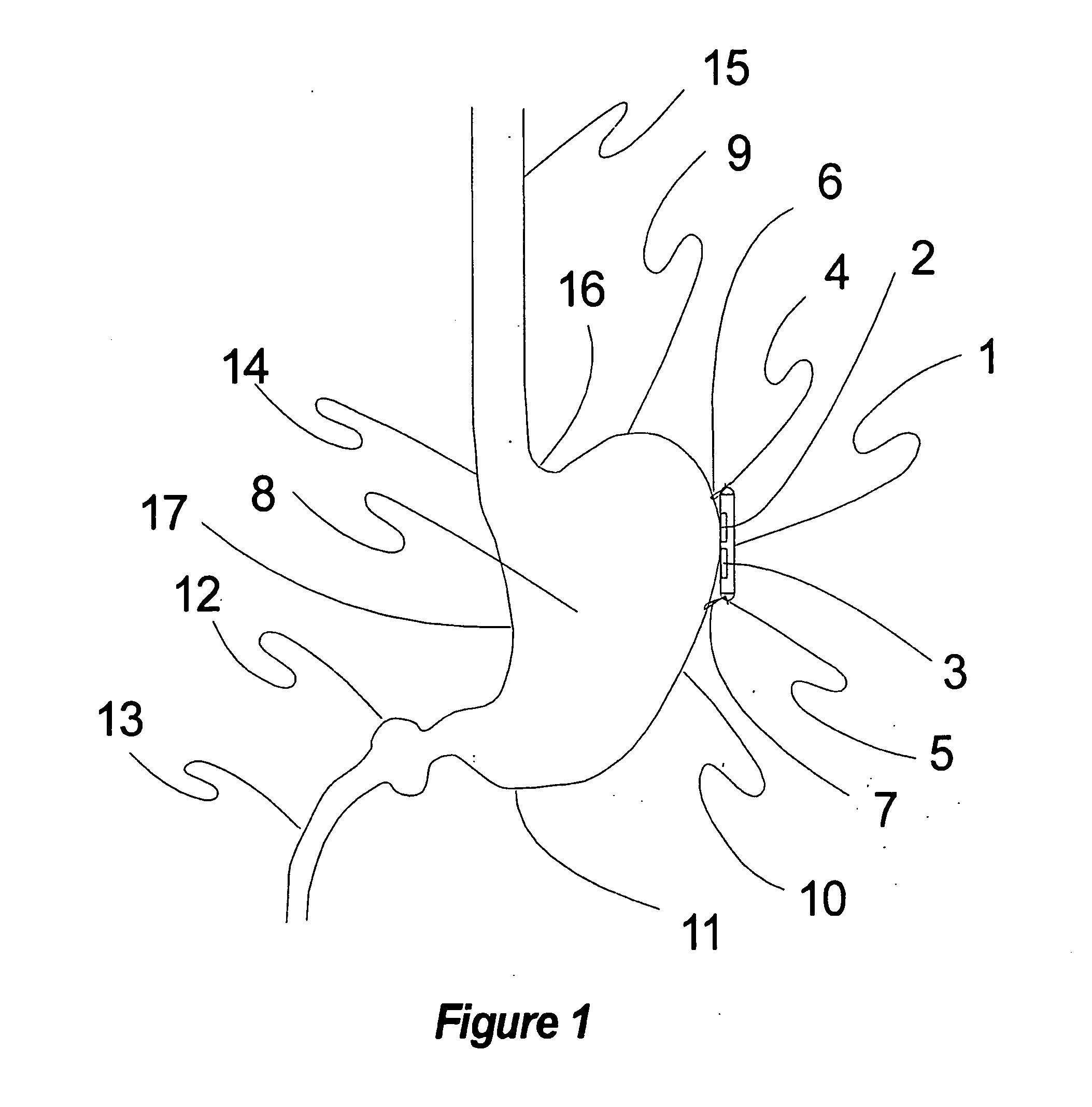
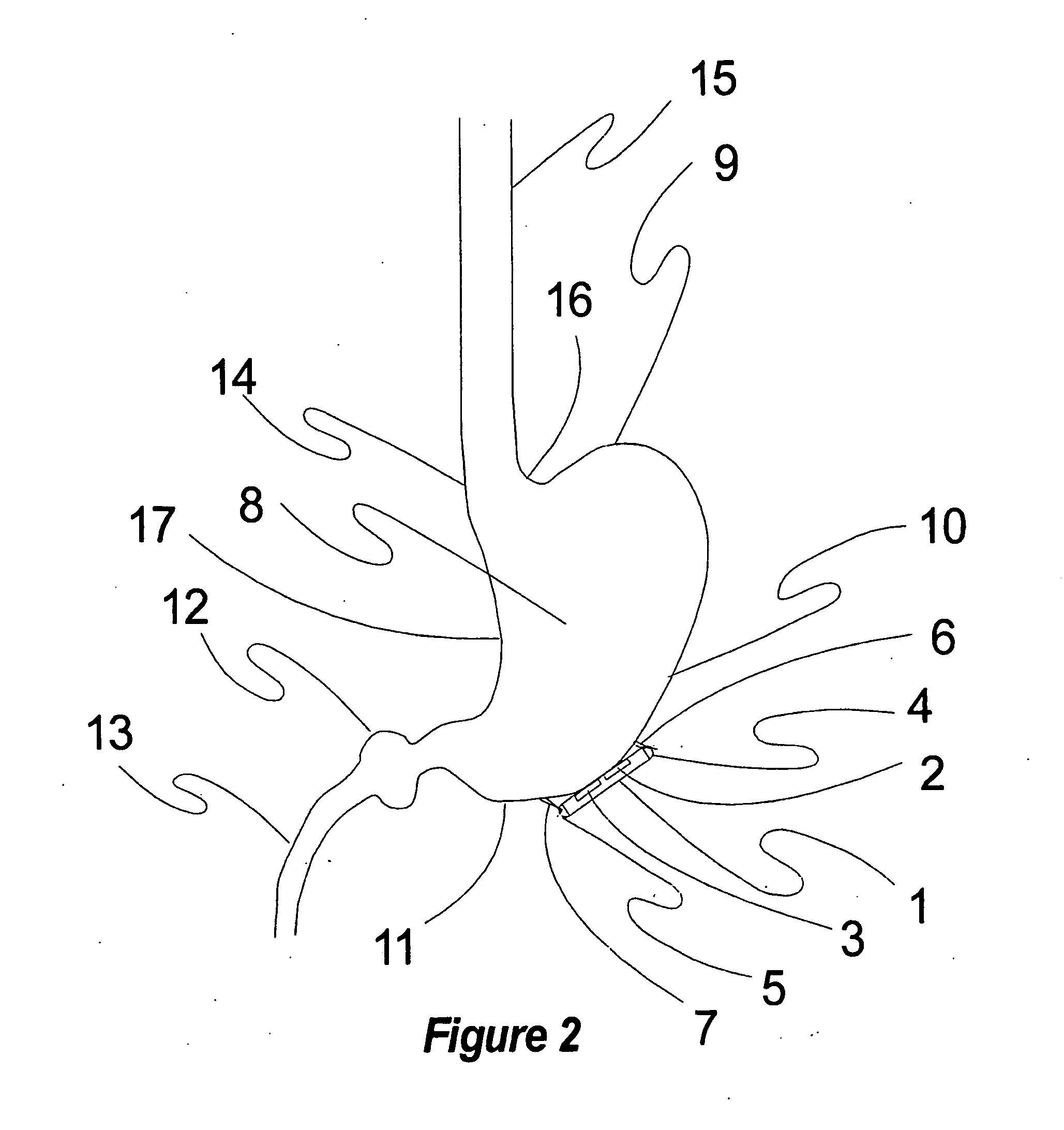
Method, apparatus, surgical technique, and stimulation parameters for autonomic neuromodulation for the treatment of obesity
InactiveUS20070162085A1Reduce or prevent conditionReducing and preventing symptomSpinal electrodesHead electrodesSplanchnic nervesAfferent Neurons
The present invention teaches a method and apparatus for physiological modulation, including neural and gastrointestinal modulation, for the purposes of treating several disorders, including obesity, depression, epilepsy, and diabetes. This includes chronically implanted neural and neuromuscular modulators, used to modulate the afferent neurons of the sympathetic nervous system to induce satiety. Furthermore, this includes neuromuscular stimulation of the stomach to effect baseline and intermittent smooth muscle contraction to increase gastric intraluminal pressure, which induces satiety, and stimulate sympathetic afferent fibers, including those in the sympathetic trunk, splanchnic nerves, and greater curvature of the stomach, to augment the perception of satiety.
Owner:DILORENZO BIOMEDICAL
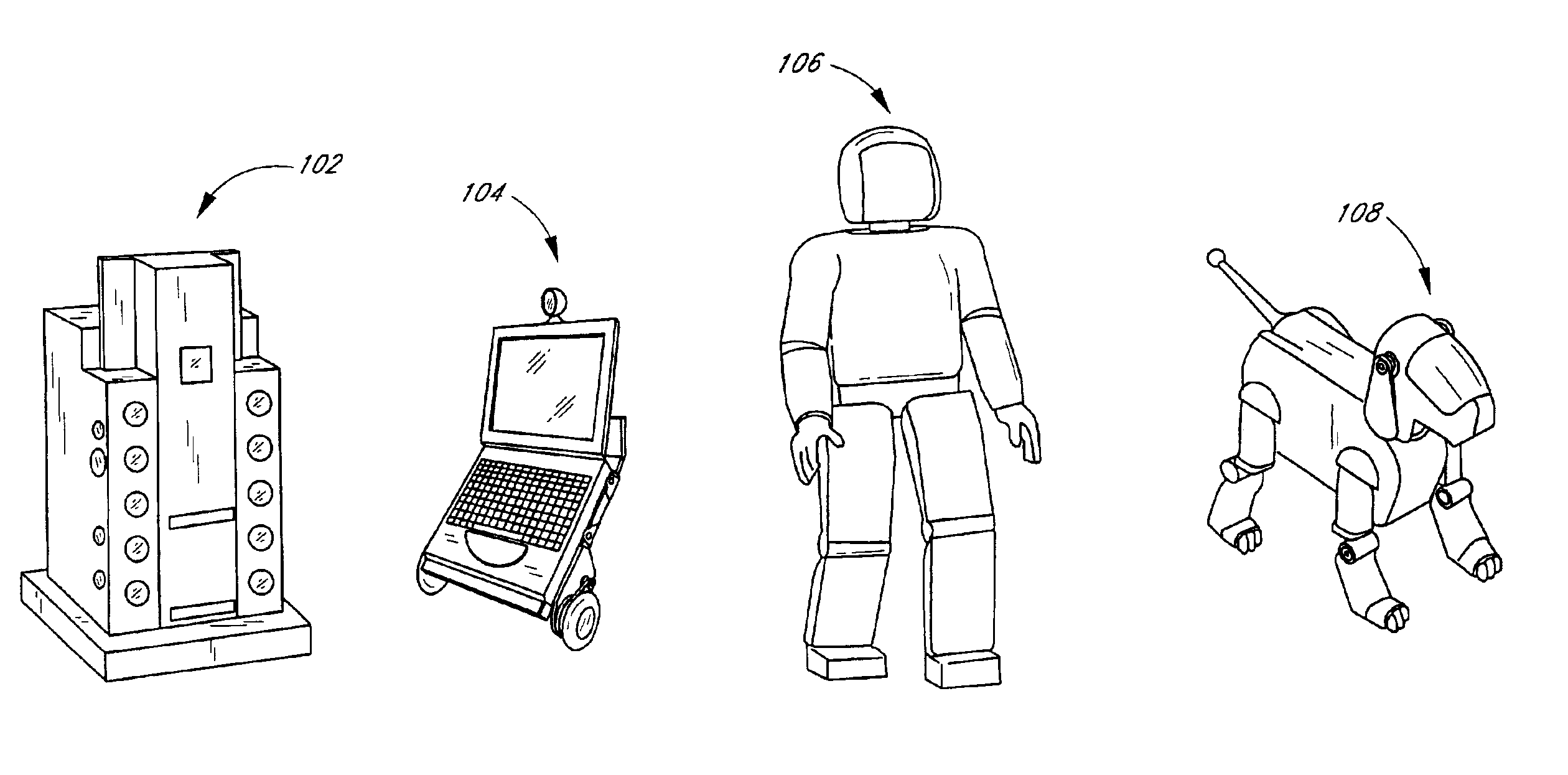
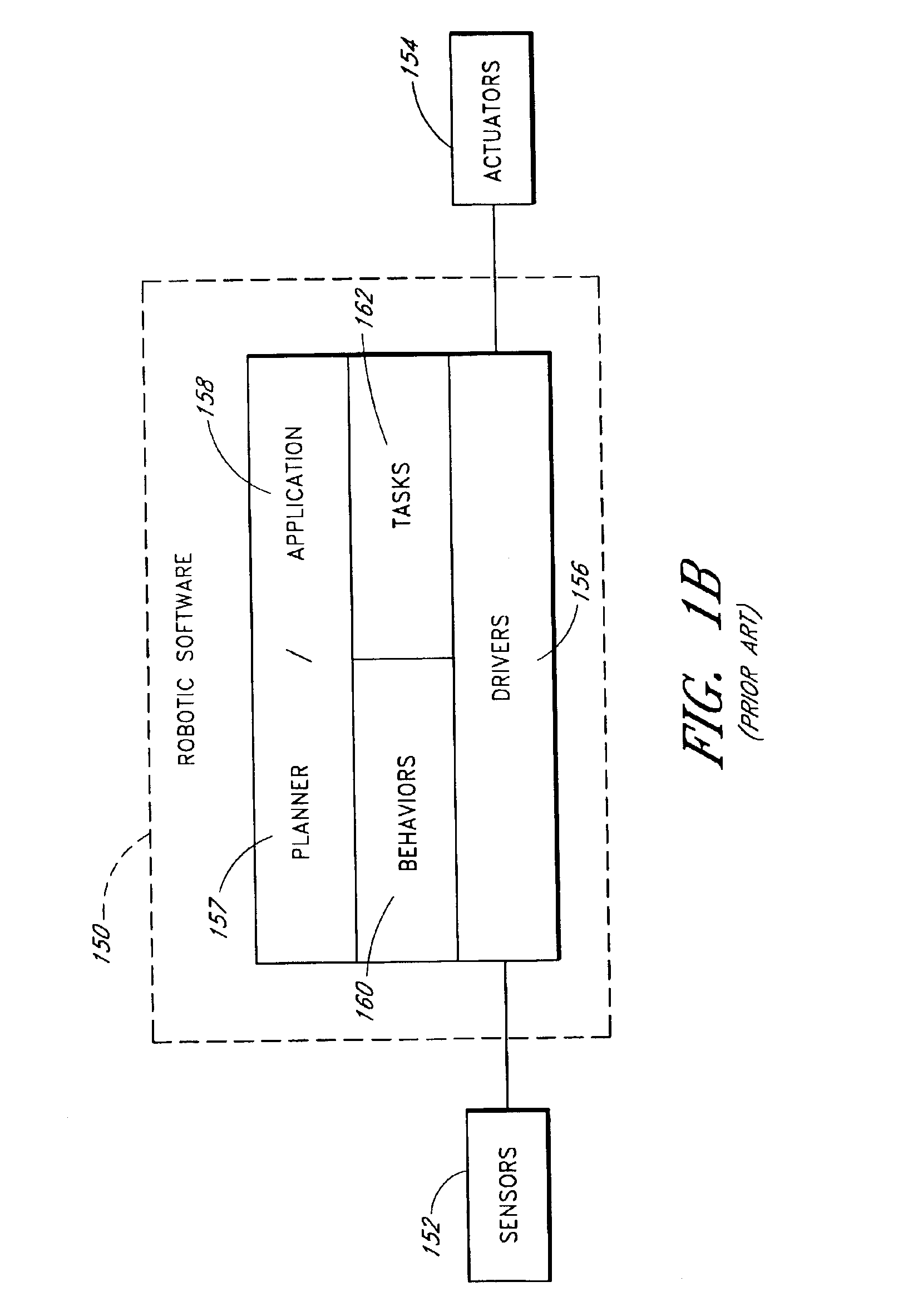
Hardware abstraction layer for a robot
InactiveUS6889118B2Reduced portabilityEfficiently permittingProgramme-controlled manipulatorAutonomous decision making processAbstraction layerOperational system
Owner:IROBOT CORP
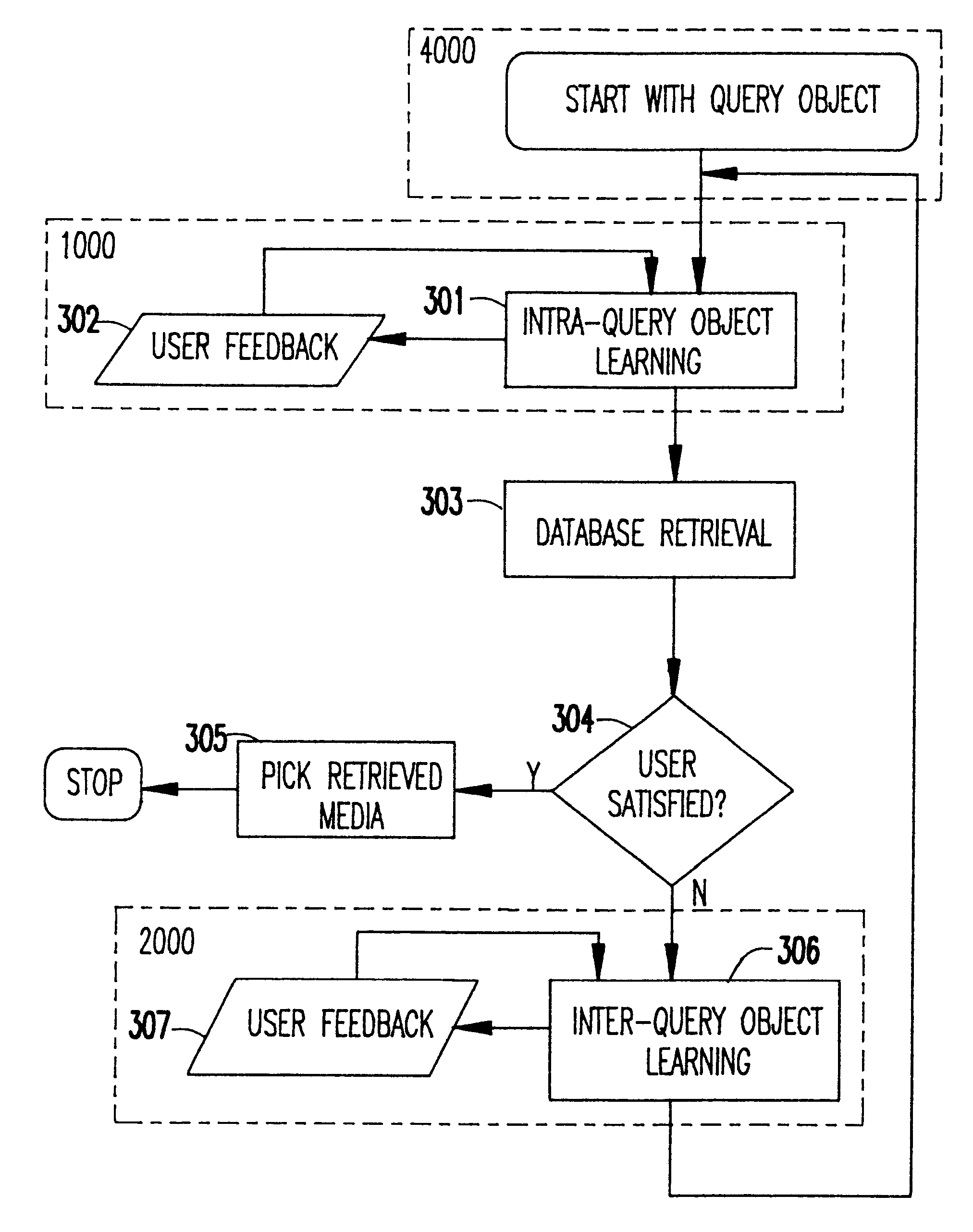
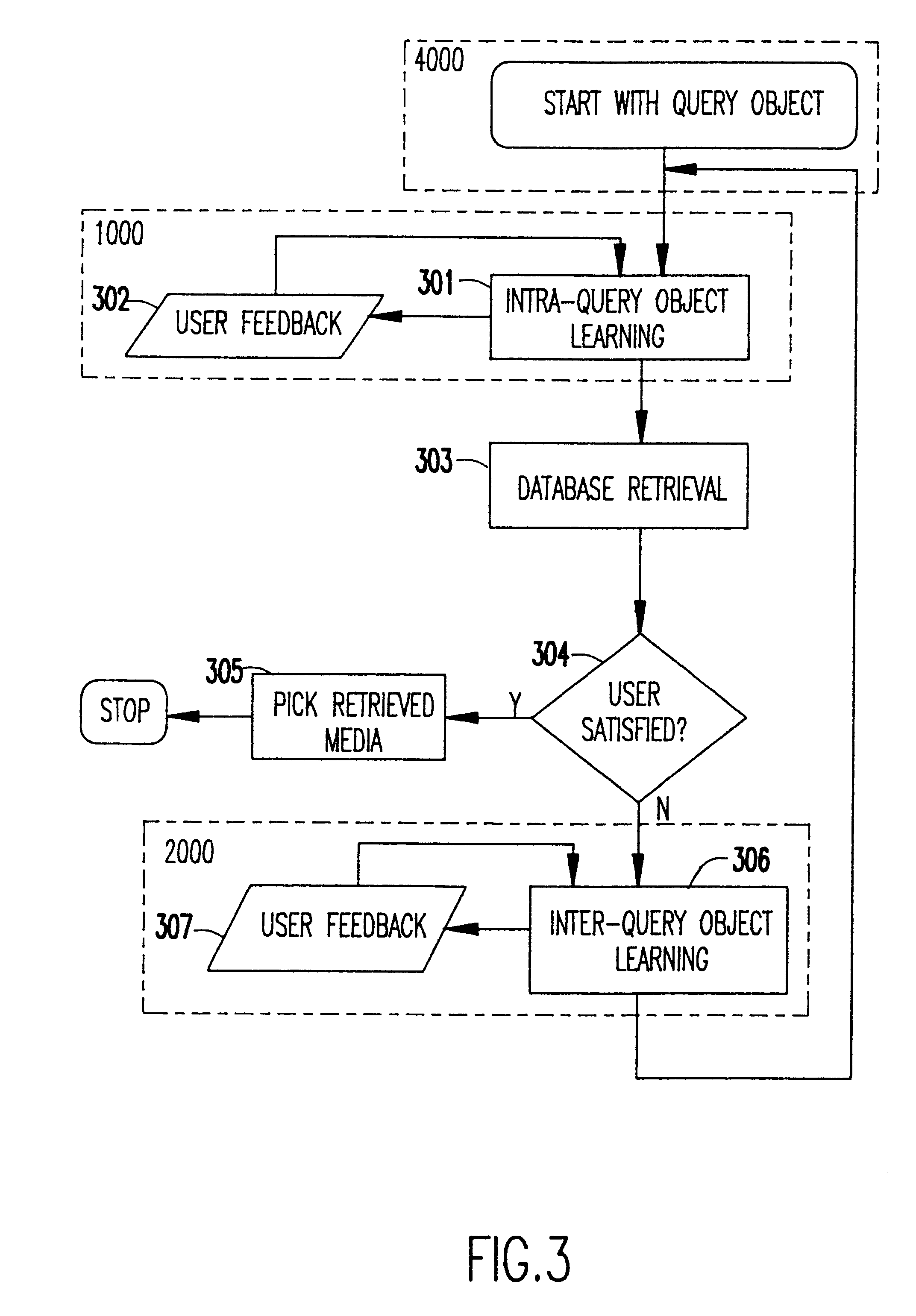
Interactive framework for understanding user's perception of multimedia data
InactiveUS6408293B1Improve approximationReducing being retrievedData processing applicationsDigital data information retrievalPattern perceptionVideo sequence
A methodology of highly interactive intra-object relevance feedback is used to retrieve multimedia data from a database. The query object could consist of one or more images, images derived from video, a video sequence, or an audio clip. The query is adjusted using the information fed-back by the user about the relevance of previously extracted part(s) from the object itself, such that the adjusted query is a better approximation to the user's perception. The information fed-back by the user during intra-query modification is used for intra-object learning of the user's perception. The refined query is subsequently used for inter-object relevance feedback where data is retrieved from the database based on parameters learnt by intra-query object feedback mechanism, and the user provides feedback by ranking the retrieved objects in order of their relevance to him or her. In the system according to the invention, inter-object learning of user's perception is expedited by utilizing the learnt parameters in the intra-object relevance feedback. Furthermore, the methodology of the invention allows for building refined queries based on part(s) or sub-sequence(s) of the query object rather than the entire object itself, thereby reducing the number of irrelevant objects, retrieved from the database. The methodology allows synthesis and modification of the input query object itself in the event a query object is not directly available, and, also to learn the user's perception.
Owner:PHONENICIA INNOVATIONS LLC SUBSIDIARY OF PENDRELL TECH +1
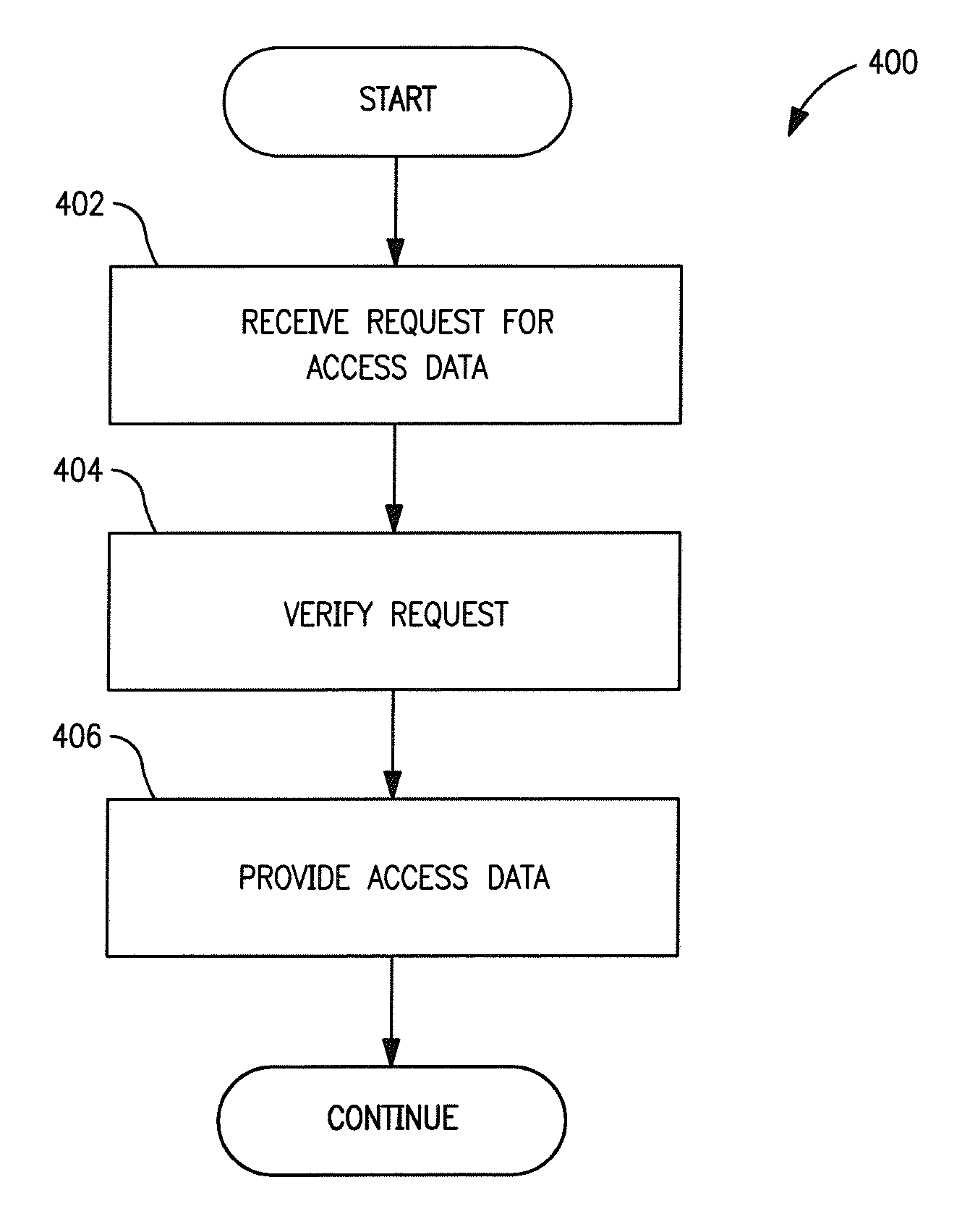
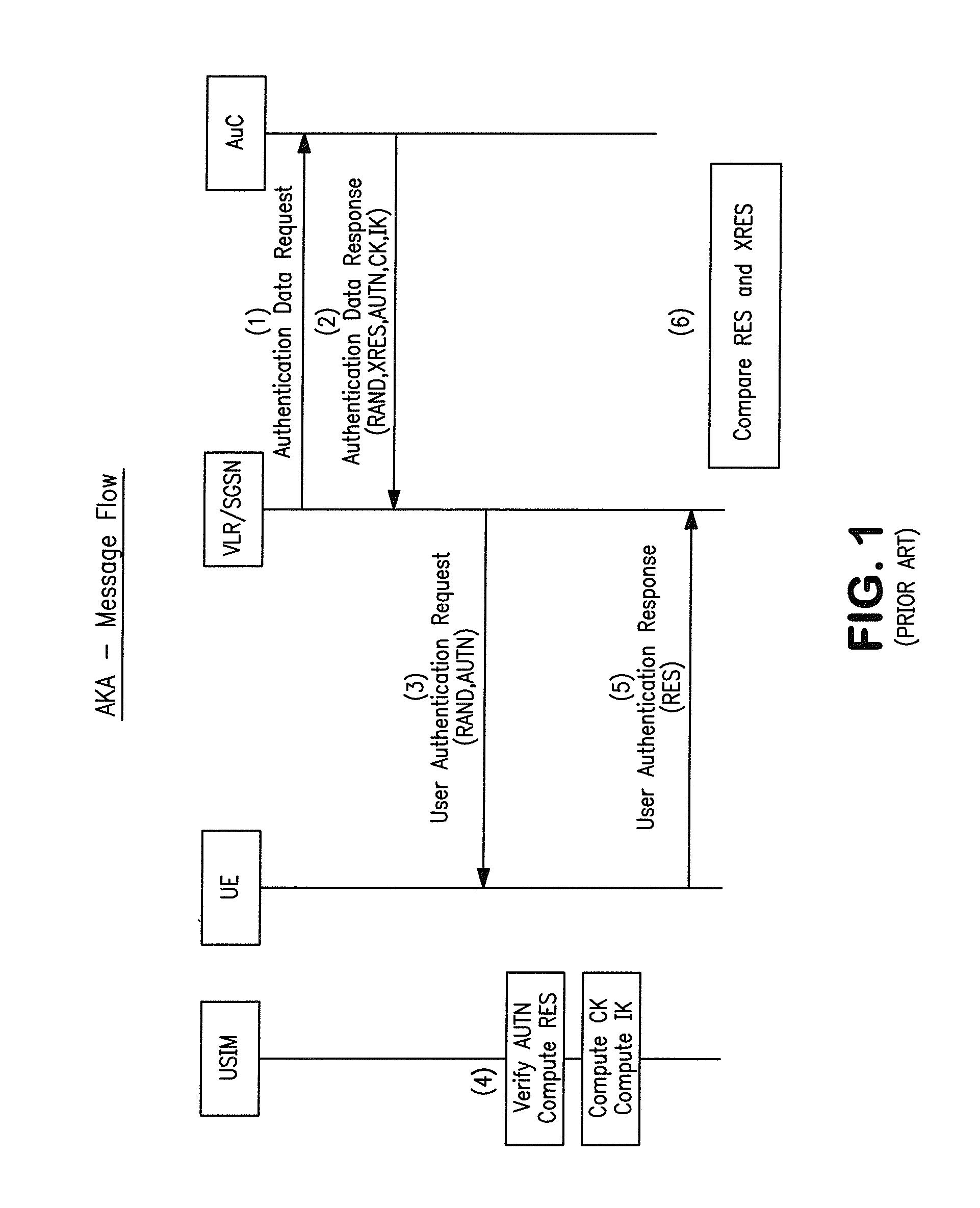
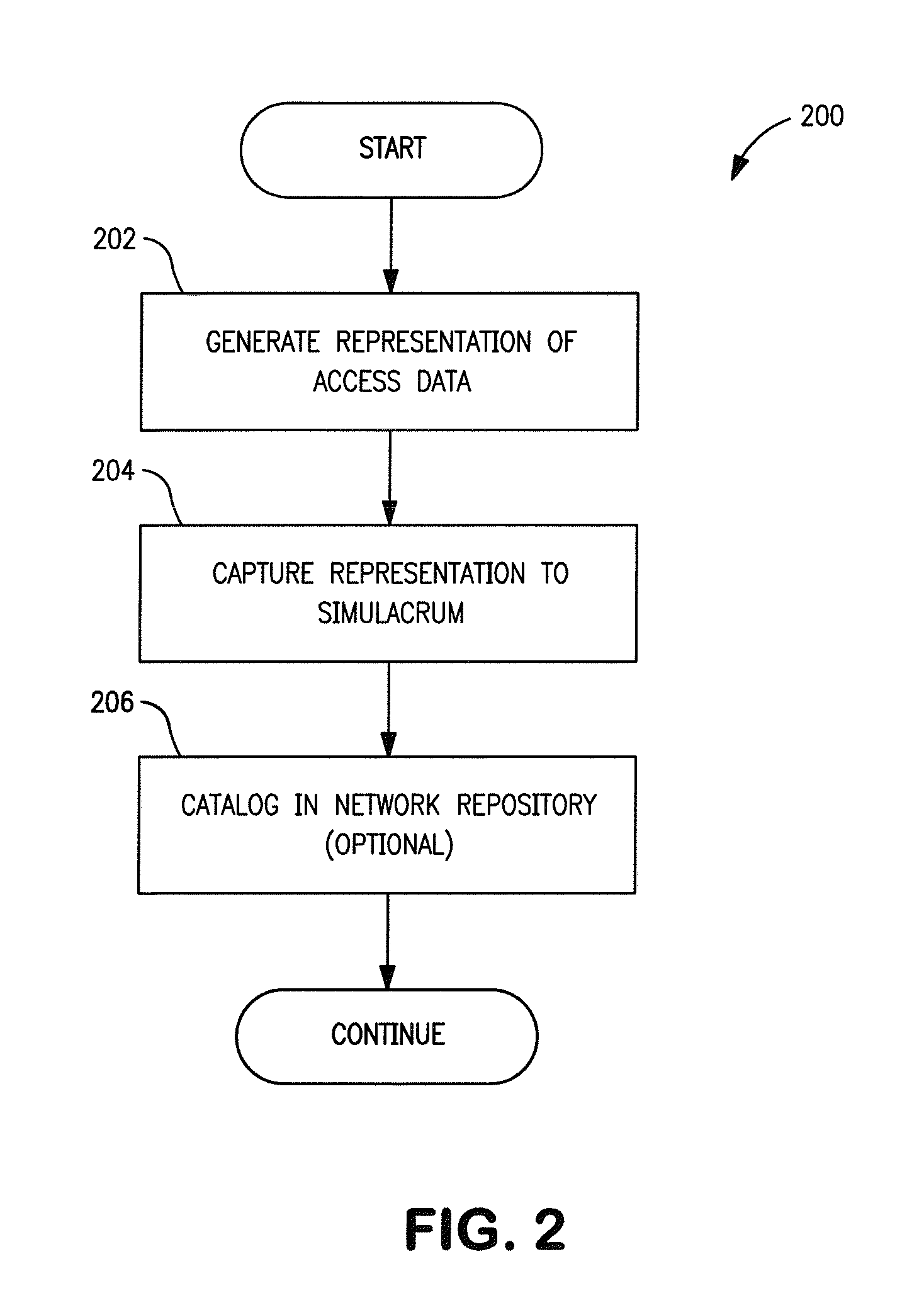
Simulacrum of physical security device and methods
ActiveUS20120117635A1Service provisioningDigital data processing detailsSoftware emulationPhysical security
A simulacrum security device and methods. In one embodiment, a simulacrum or likeness of a physical security device is provided for use in conjunction with a software emulation of the security device. In one implementation, a “faux SIM card” is provided that does not contain Subscriber Identification Module (SIM) information itself, but instead enables a user to download Electronic SIM (eSIM) information (e.g., from a network or eSIM server) which is loaded into a software emulation of a Universal Integrated Circuit Card (UICC) device. The faux card is printed with an activation code, scan pattern, or other activation or access information. The subscriber purchases the faux card, and enters the activation code into a device; the entered activation code enables the device to log onto a network, and download the appropriate eSIM data. Delivery of eSIM information as enabled by the faux card addresses deficiencies in existing SIM distribution schemes, provides users with an enhanced perception of security, and further addresses various legal requirements.
Owner:APPLE INC
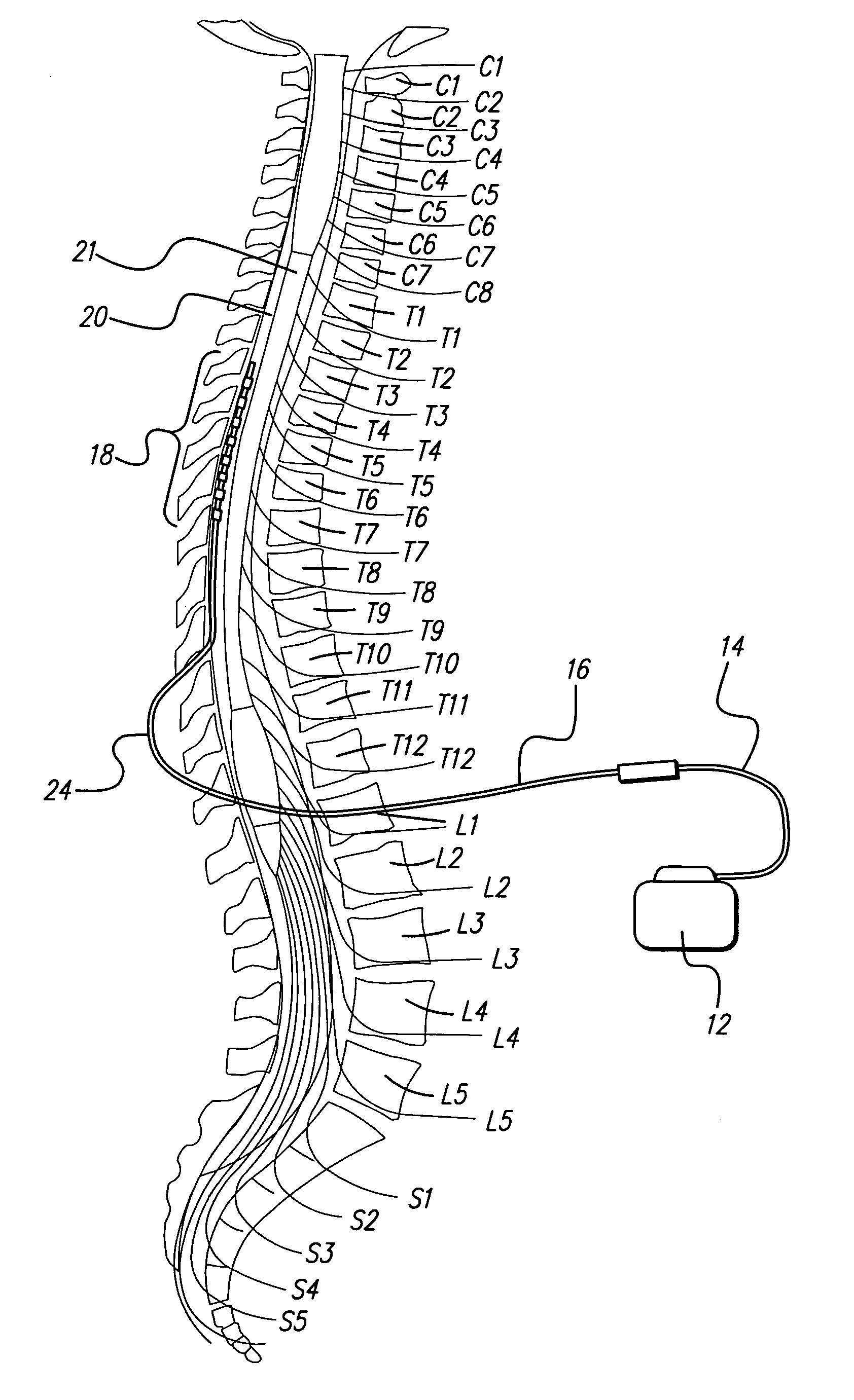
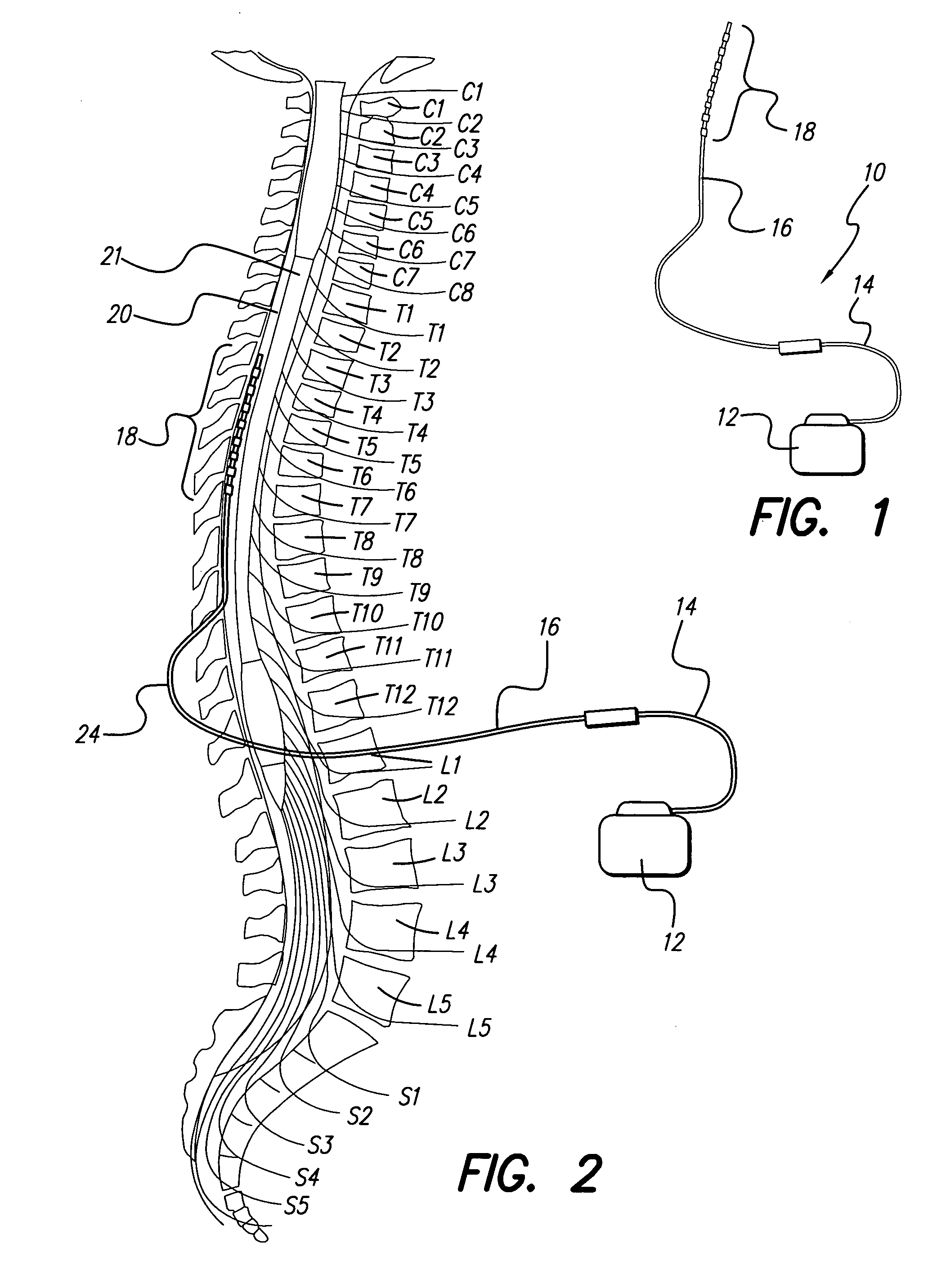
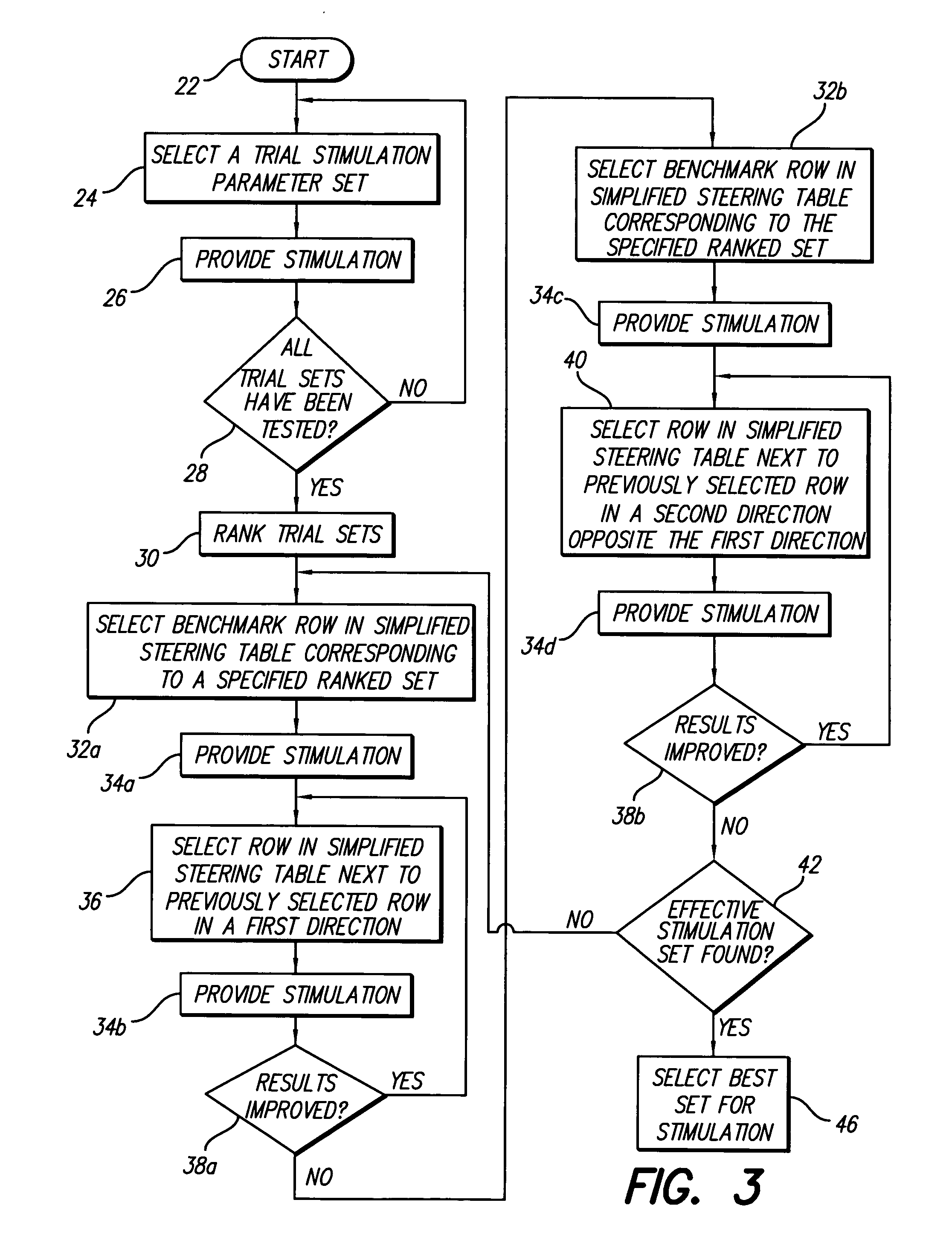
Method for optimizing search for spinal cord stimulation parameter settings
InactiveUS20050209655A1Improve search efficiencyConstant level of paresthesiaSpinal electrodesSurgeryVolumetric Mass DensityPattern perception
Methods for selecting stimulation parameter sets guide a clinician towards an effective set(s) of stimulation parameters. The clinician first evaluates the effectiveness of a small number of trial stimulation parameters sets from a Measurement Table comprising for example, four stimulation parameter sets, measuring the perception threshold and maximum threshold levels. The maximum comfortable step size and desired field shift resolution are determined, and are used along with the measured threshold levels to determine an appropriate step size to use in the current steering process. In order to maintain paresthesia at a relatively constant level during the steering process, a Superposition Equalization (SEQ) algorithm is used to compensate for the physical characteristics of the lead array, i.e., electrode separation and size. A multiplier is determined and a modifying function is used to apply this multiplier to the electrode energy output during transition to maintain a relatively constant current density.
Owner:BOSTON SCI NEUROMODULATION CORP
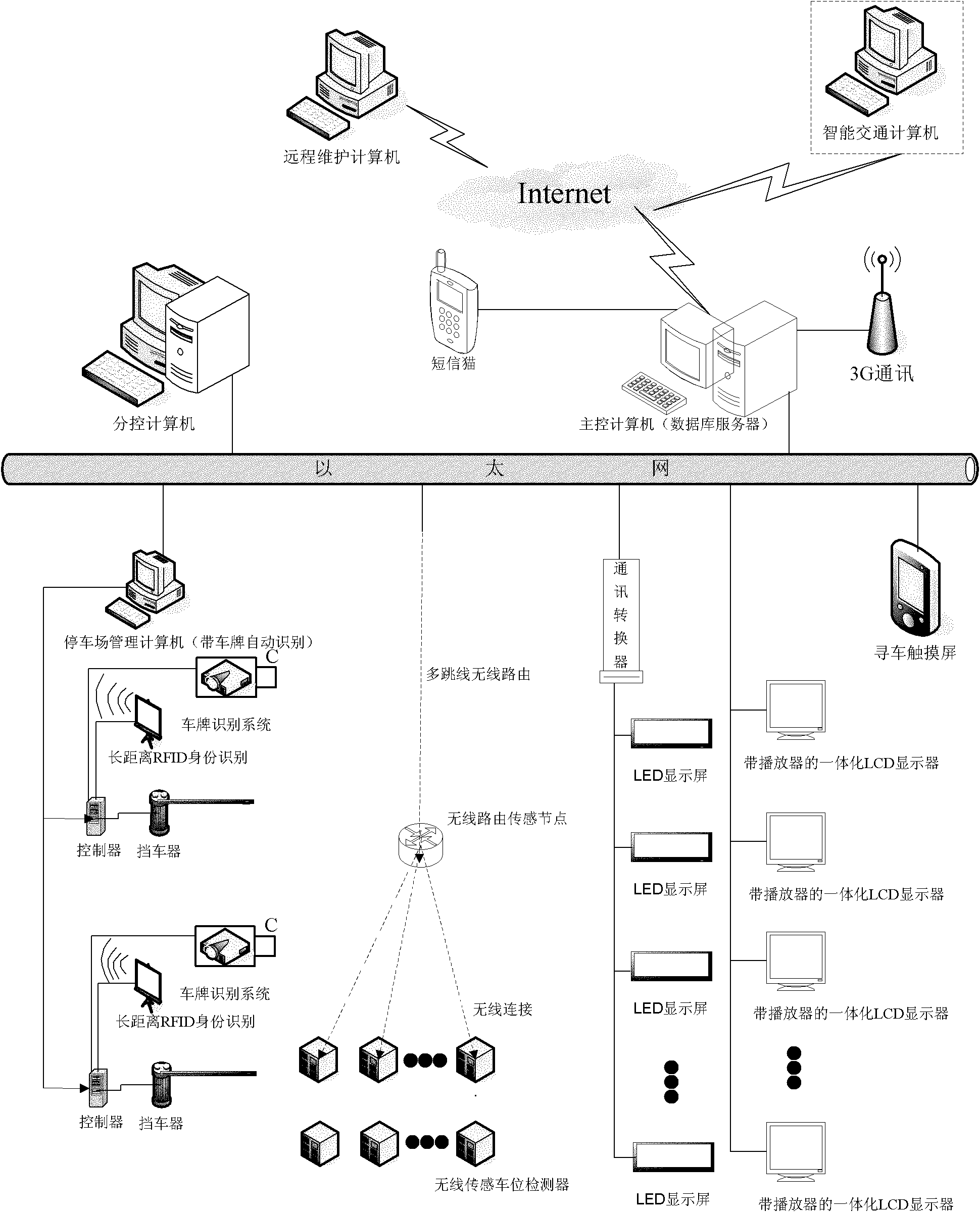
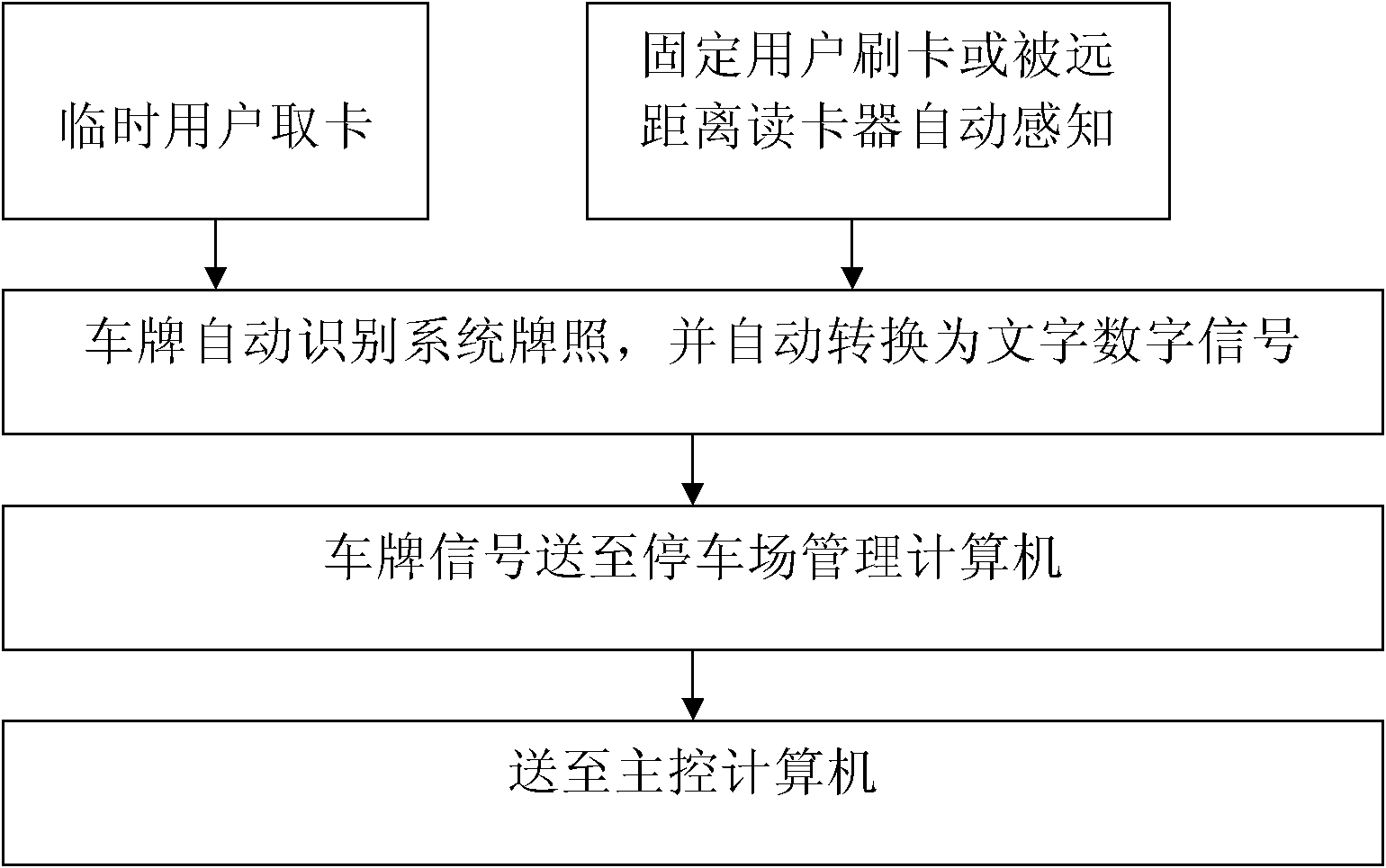
Parking navigation and finding system based on object networking wireless sensing and video perception
ActiveCN101937619AAccurate parking navigationCar owners find parking spaces efficientlyIndication of parksing free spacesCo-operative working arrangementsDisplay deviceThird generation
The invention provides a parking navigation and finding system based on object networking wireless sensing and video perception, comprising a main control computer. The main control computer is connected with a plurality of park control systems with number plate automatic identification and a plurality of integrated LCD displays with players and wireless stall sensors through a network; the wireless stall sensor is installed at each stall; the park control system comprises a number plate identification system, an RFID (Radio Frequency Identification Device) reader-writer and a matched radio frequency identification electronic tag; and the LCD display comprises a navigation screen at the garage entrance and the LCD display arranged on a client forwarding path. The parking navigation and finding system has the advantages of actively informing a related internal part or a common platform of characteristic vehicle information and having a remote maintenance system transmitted through 3G and is a typical object networking perception system. The parking navigation is precise through an object networking wireless perception technique and a number plate identification technique, a vehicle owner finds a stall efficiently and the identity identification is in advance.
Owner:江苏瑞孚特物联网科技有限公司
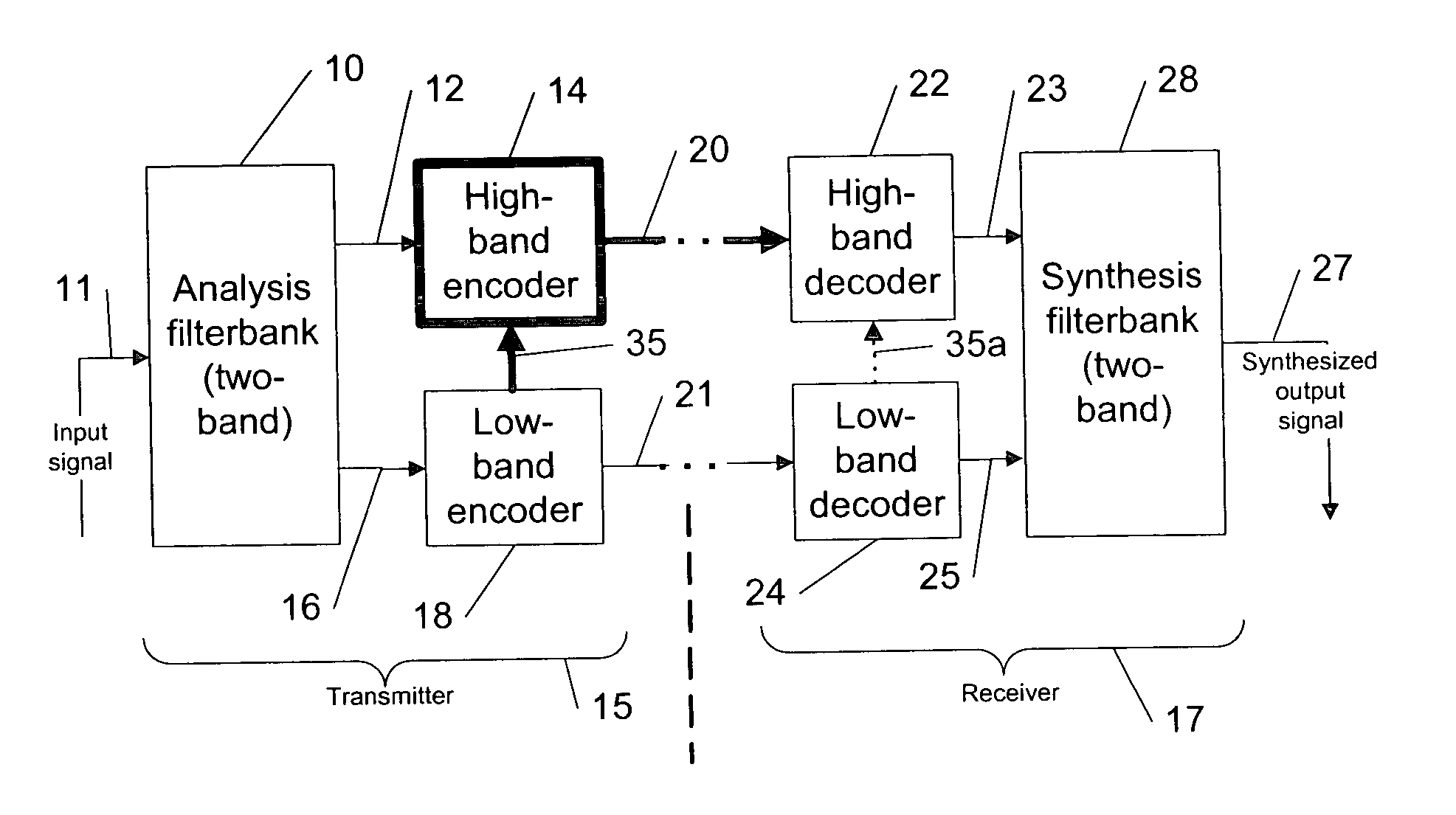
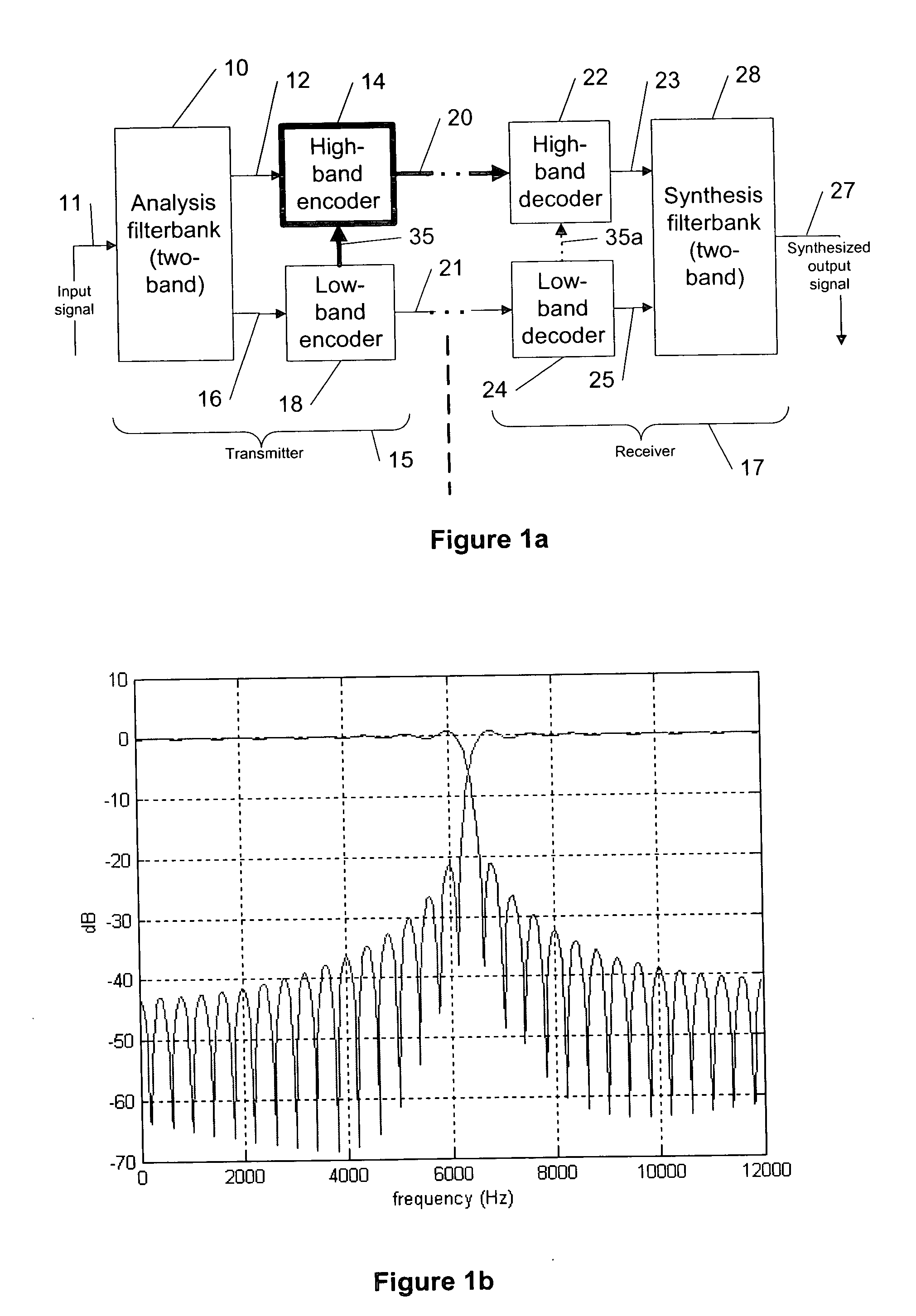
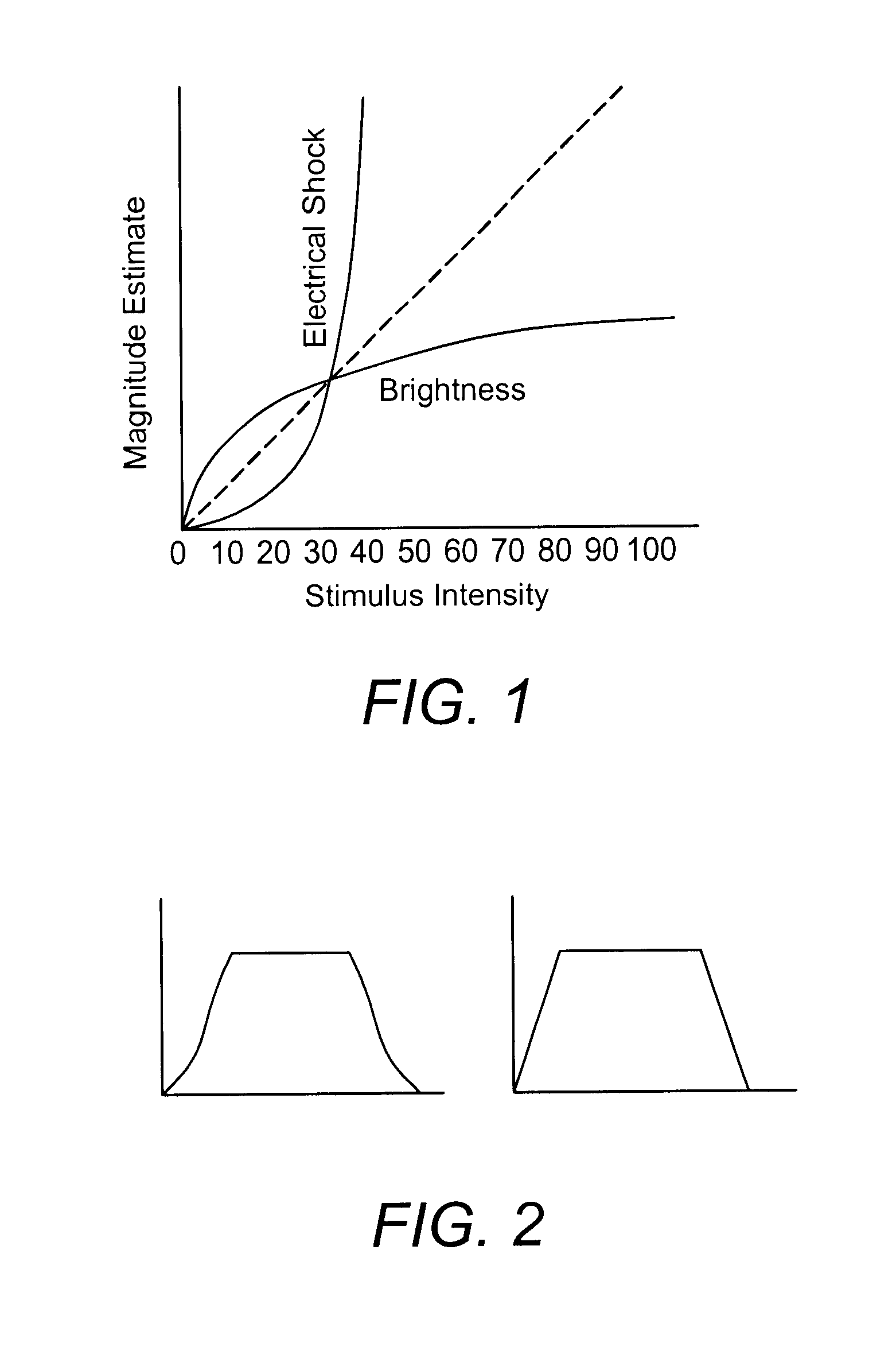
Tinnitus rehabilitation device and method
InactiveUS20040131200A1Technique is effectiveElectric tinnitus maskersEar treatmentFrequency spectrumHabituation
A tinnitus method and device for providing relief to a person suffering from the disturbing effects of tinnitus is described. The method can be implemented entirely in software to spectrally modify an audio signal in accordance with a predetermined masking algorithm which modifies the intensity of the audio signal at selected frequencies. A predetermined masking algorithm is described which provides intermittent masking of the tinnitus wherein, at a comfortable listening level, during peaks of the audio signal the tinnitus is completely obscured, whereas during troughs the perception of the tinnitus occasionally emerges. In practice it has been found that such intermittent masking provides an immediate sense of relief, control and relaxation for the person, whilst enabling sufficient perception of the tinnitus for habituation and long term treatment to occur. Advantageously the predetermined masking algorithm is specifically tailored to the audiometric configuration of the person. For example, the masking algorithm may be partly tailored to the hearing loss characteristic of the person. A tinnitus rehabilitation device used in conjunction with a personal sound reproducing system is also described.
Owner:NEUROMONICS
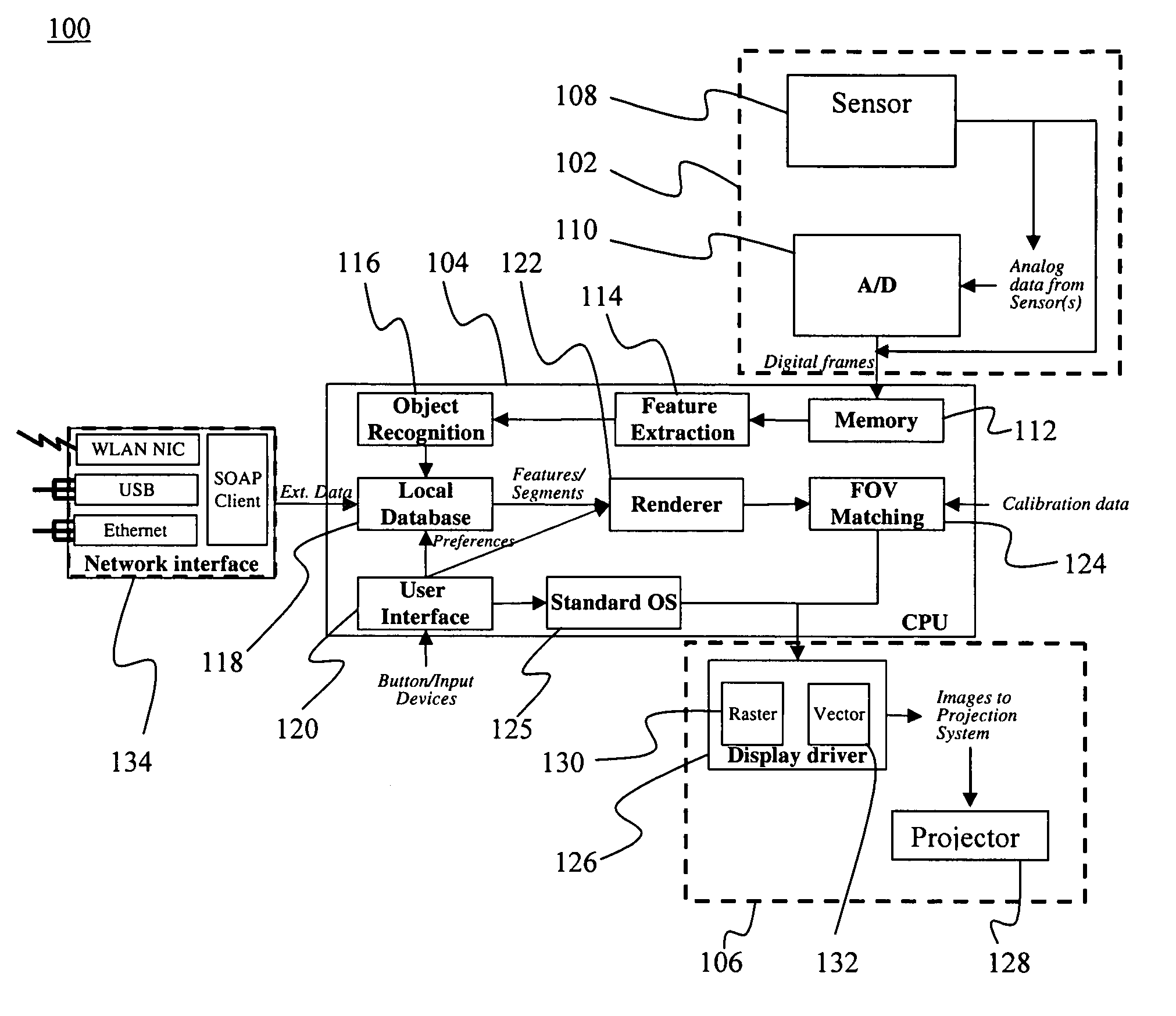
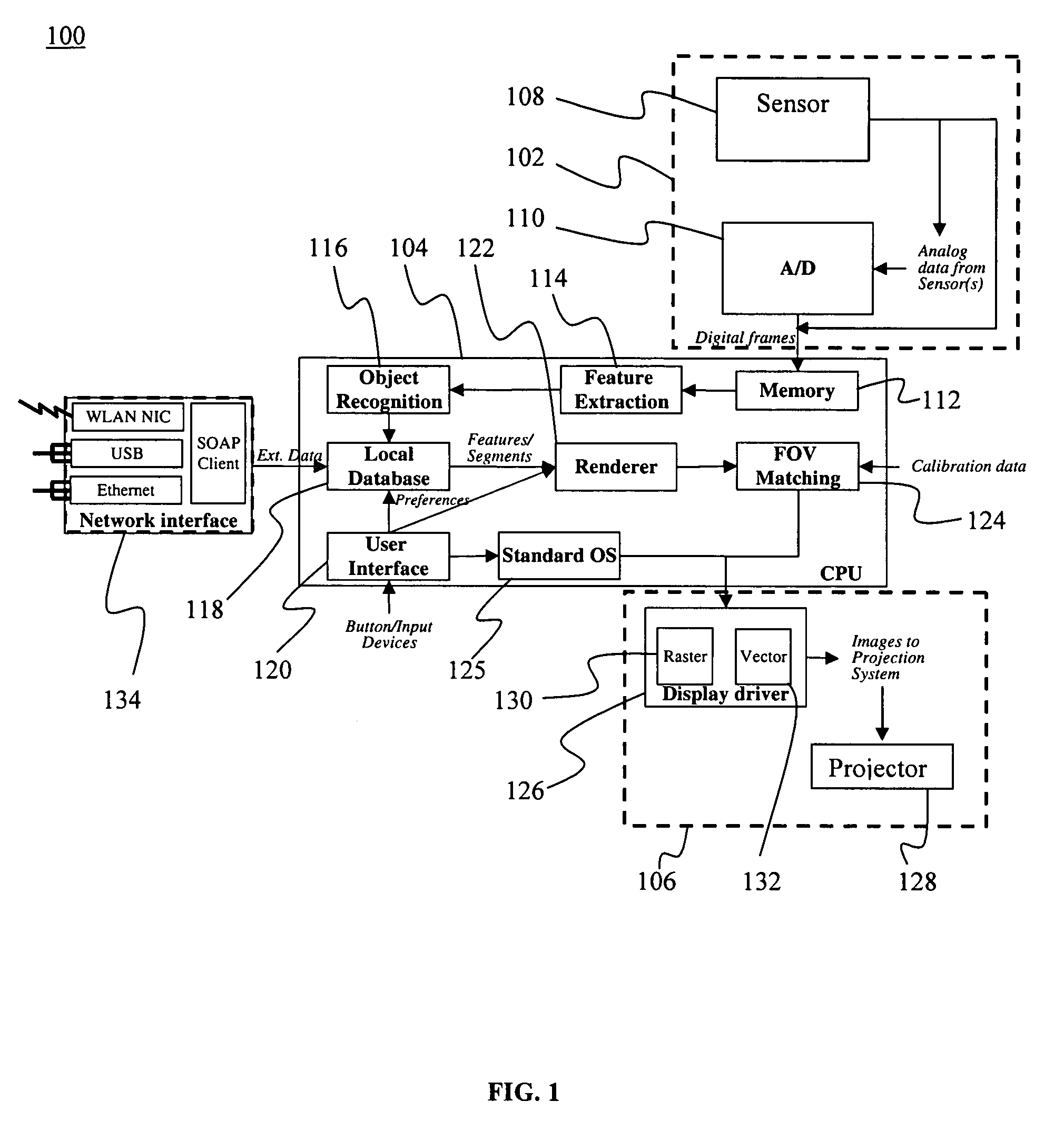
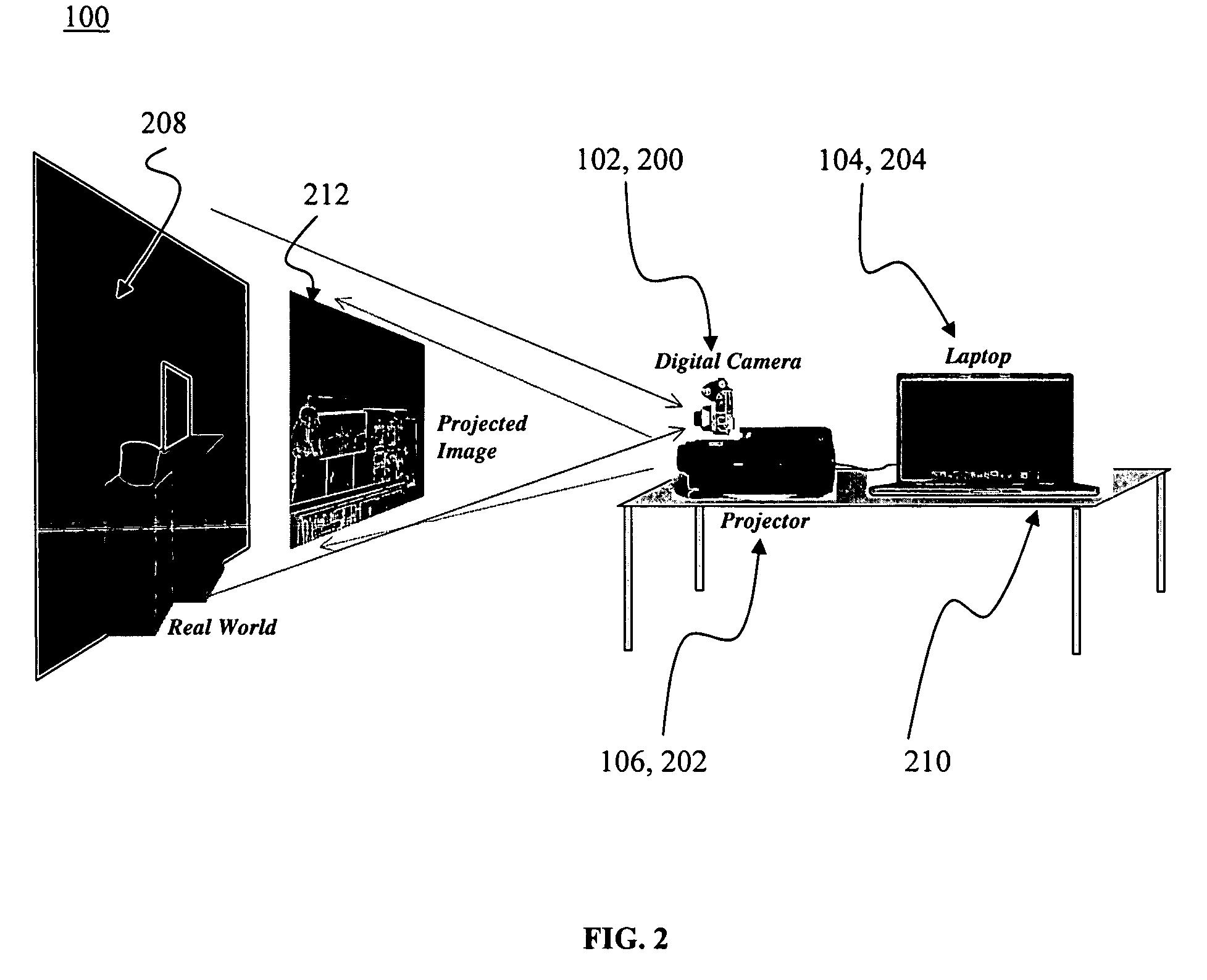
Enhanced perception lighting
InactiveUS7315241B1Facilitate cognitionImprove user perceptionElectrical apparatusElectric lighting sourcesDisplay deviceEffect light
The present invention relates to an enhanced perception lighting (EPL) system for providing enhanced perception of a user's physical environment. The EPL system comprises a sensor module for detecting and sampling a physical aspect from at least one point in a physical environment and for generating an observation signal based on the physical aspect; a processor module coupled with the sensor module for receiving the observation signal, processing the observation signal, and generating an output signal based on the observation signal; and a projection display module located proximate the sensor module and communicatively connected with the processor module for projecting a display onto the at least one point in the physical environment based upon the output signal. The system allows a user to gather information from the physical environment and project that information onto the physical environment to provide the user with an enhanced perception of the physical environment.
Owner:HRL LAB
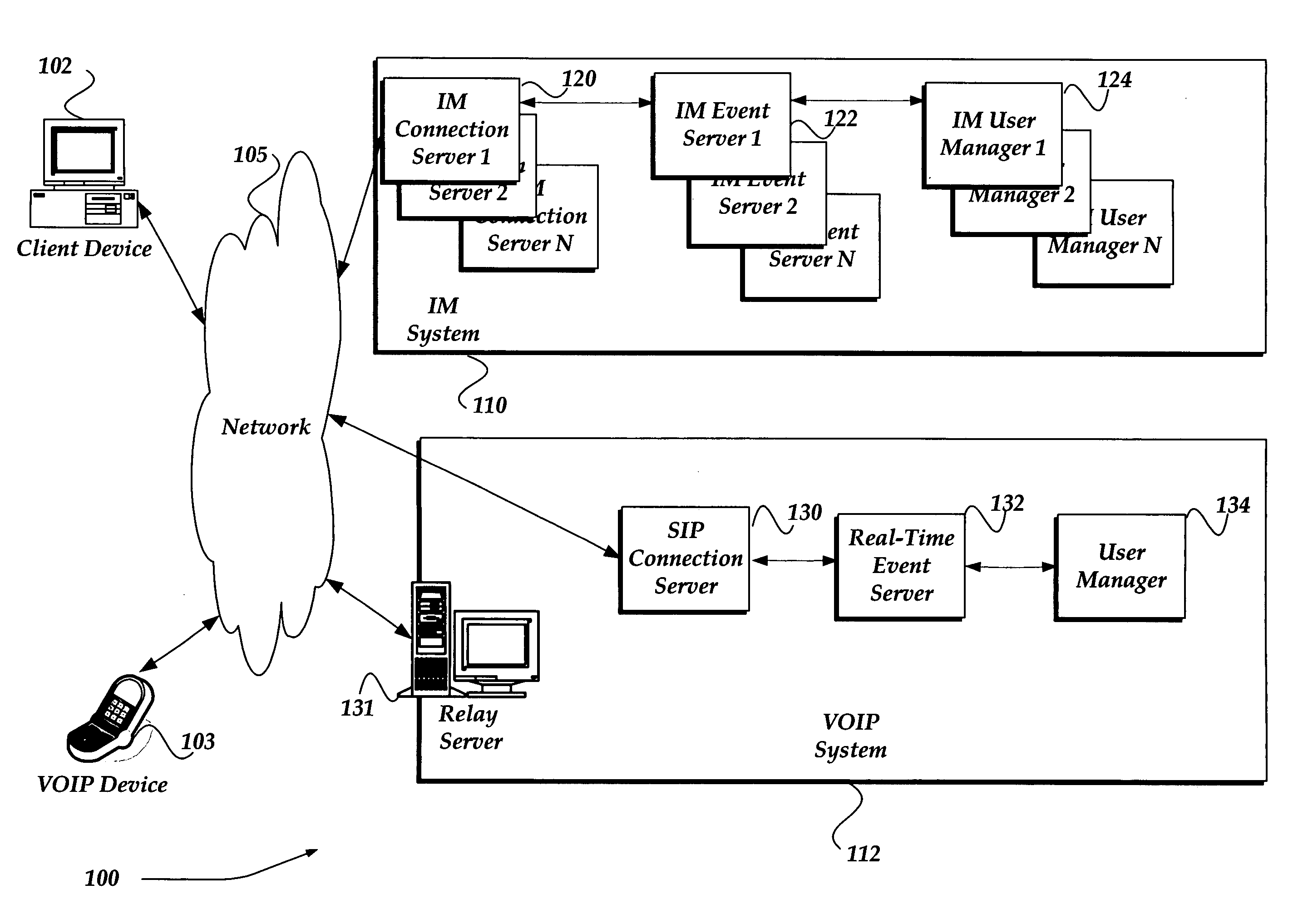
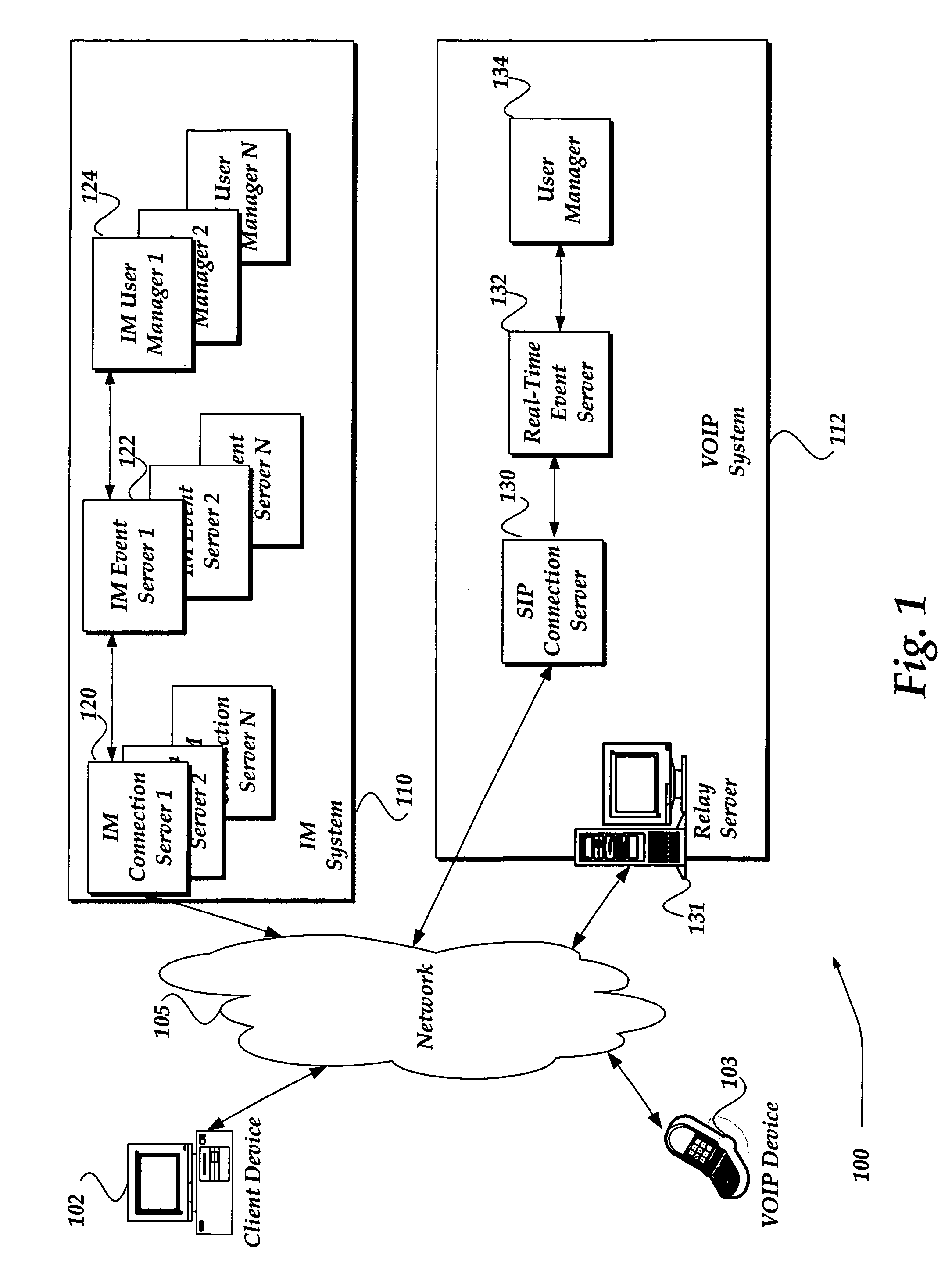
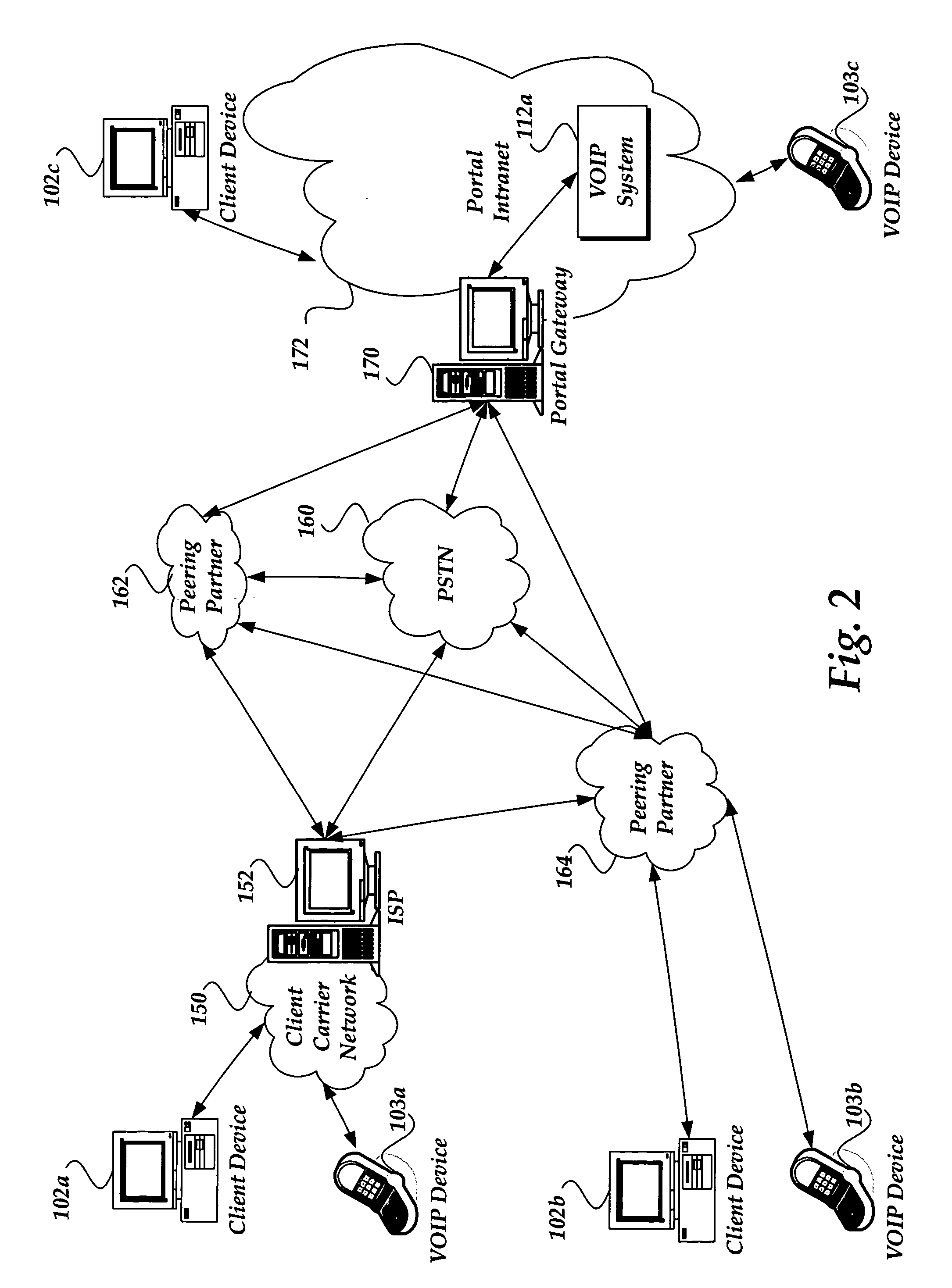
Selecting a network based on metrics for real time communication
A system, method, and apparatus are directed towards routing a Voice over IP (VOIP) messages over a network. The VOIP messages are sent by a source client device to a destination client device through a portal service that has access to multiple routing services such as peering partners, carriers, etc. A VOIP system of the portal service aggregates call quality data after each VOIP call over each routing service. The call quality data is analyzed to determine a perception factor for each routing service at various times of day, days of the week, day of the year, geographic areas, and the like. When a VOIP call is requested through the portal service, the VOIP system determines a current cost, a current quality of service, and the perception factor for each routing service. A weighting is applied to each criterion and a routing service is selected for routing the VOIP call.
Owner:R2 SOLUTIONS
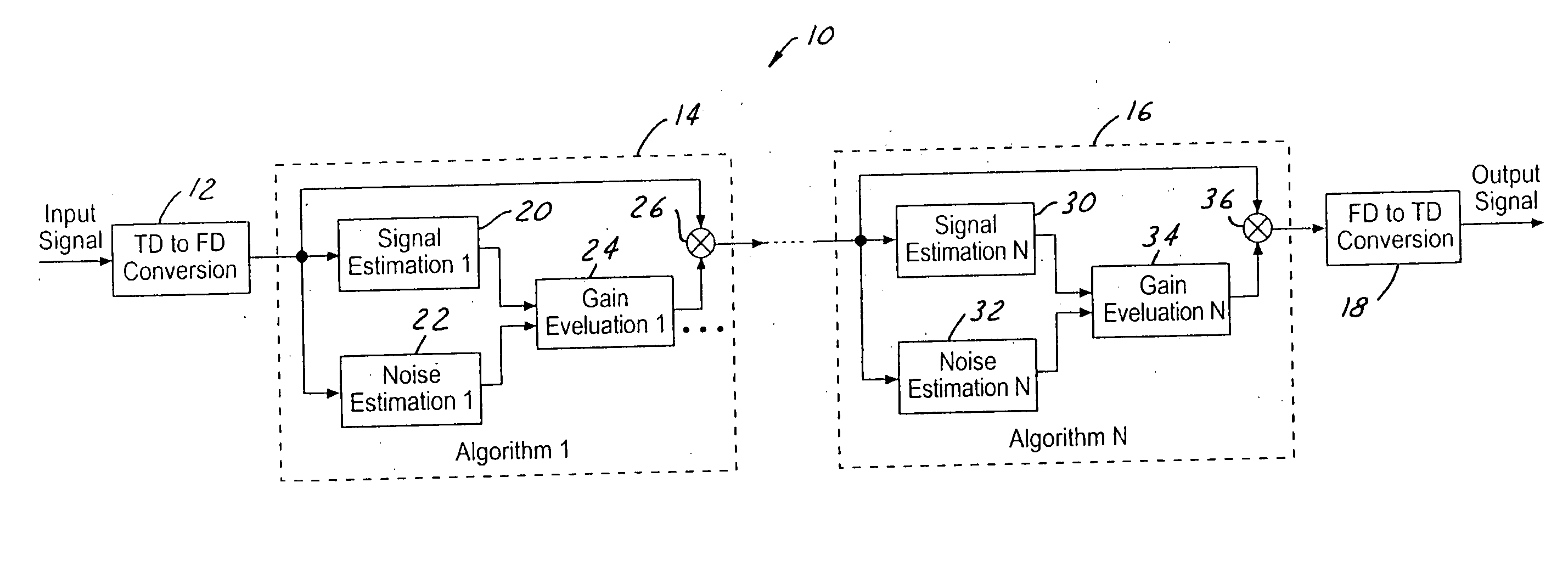
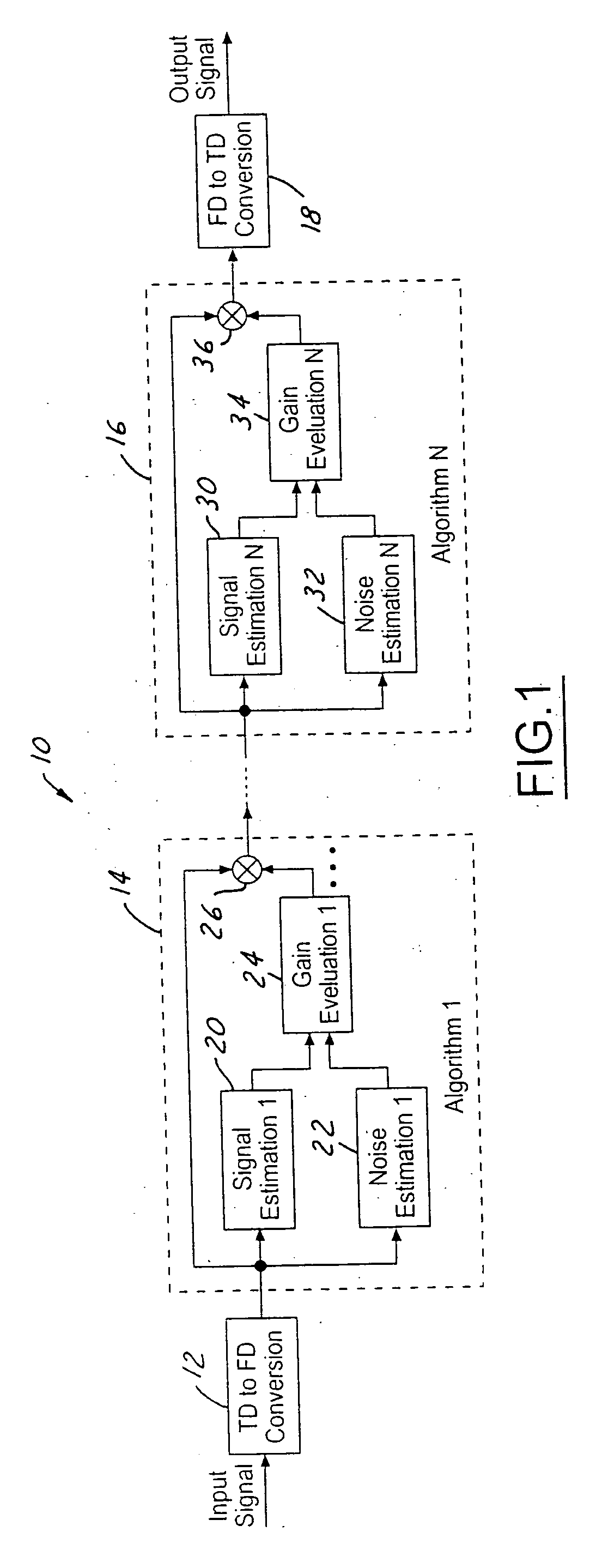
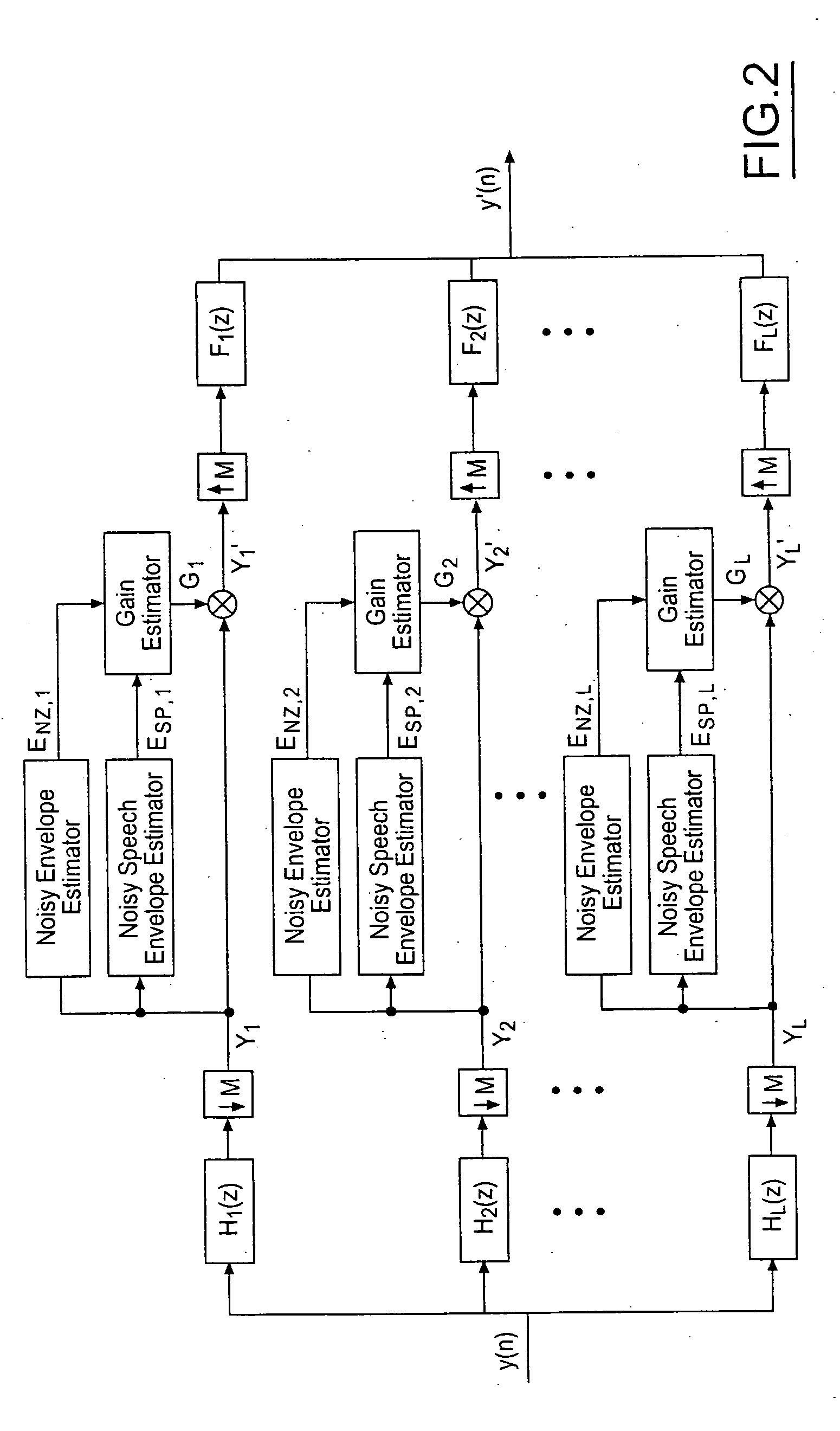
Method of cascading noise reduction algorithms to avoid speech distortion
ActiveUS20060074646A1Reduce generationImprove variationSpeech analysisAlgorithmNoise reduction algorithm
A method of reducing noise by cascading a plurality of noise reduction algorithms is provided. A sequence of noise reduction algorithms are applied to the noisy signal. The noise reduction algorithms are cascaded together, with the final noise reduction algorithm in the sequence providing the system output signal. The sequence of noise reduction algorithms includes a plurality of noise reduction algorithms that are sufficiently different from each other such that resulting distortions and artifacts are sufficiently different to result in reduced human perception of the artifact and distortion levels in the system output signal.
Owner:CSR TECH INC
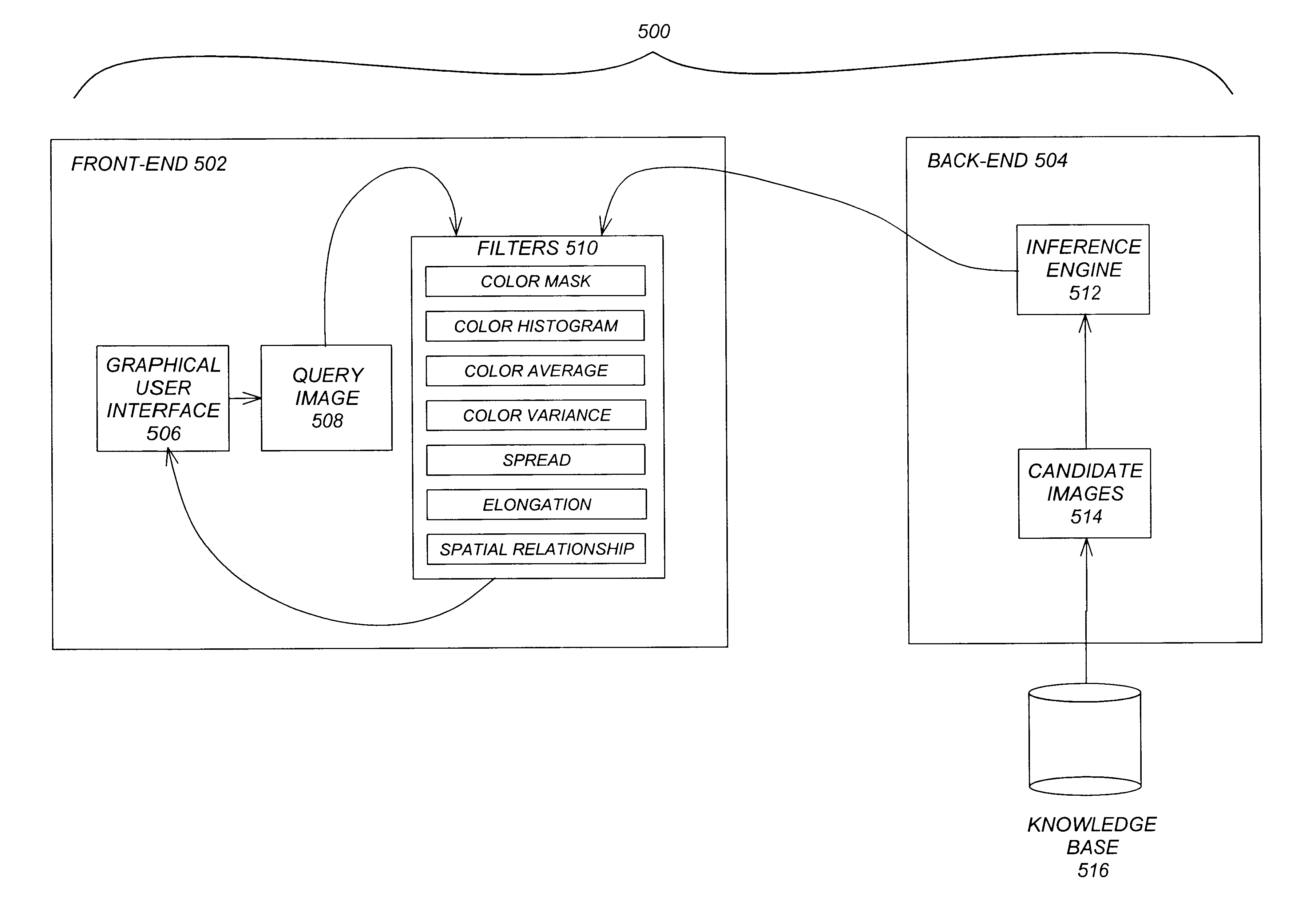
Perception-based image retrieval
InactiveUS6865302B2Data processing applicationsDigital data information retrievalAverage filterPattern perception
A content-based image retrieval (CBIR) system has a front-end that includes a pipeline of one or more dynamically-constructed filters for measuring perceptual similarities between a query image and one or more candidate images retrieved from a back-end comprised of a knowledge base accessed by an inference engine. The images include at least one color set having a set of properties including a number of pixels each having at least one color, a culture color associated with the color set, a mean and variance of the color set, a moment invariant, and a centroid. The filters analyze and compare the set of properties of the query image to the set of properties of the candidate images. Various filters are used, including: a Color Mask filter that identifies identical culture colors in the images, a Color Histogram filter that identifies a distribution of colors in the images, a Color Average filter that performs a similarity comparison on the average of the color sets of the images, a Color Variance filter that performs a similarity comparison on the variances of the color sets of the images, a Spread filter that identifies a spatial concentration of a color in the images, an Elongation filter that identifies a shape of a color in the images, and a Spatial Relationship filter that identifies a spatial relationship between the color sets in the images.
Owner:RGT UNIV OF CALIFORNIA
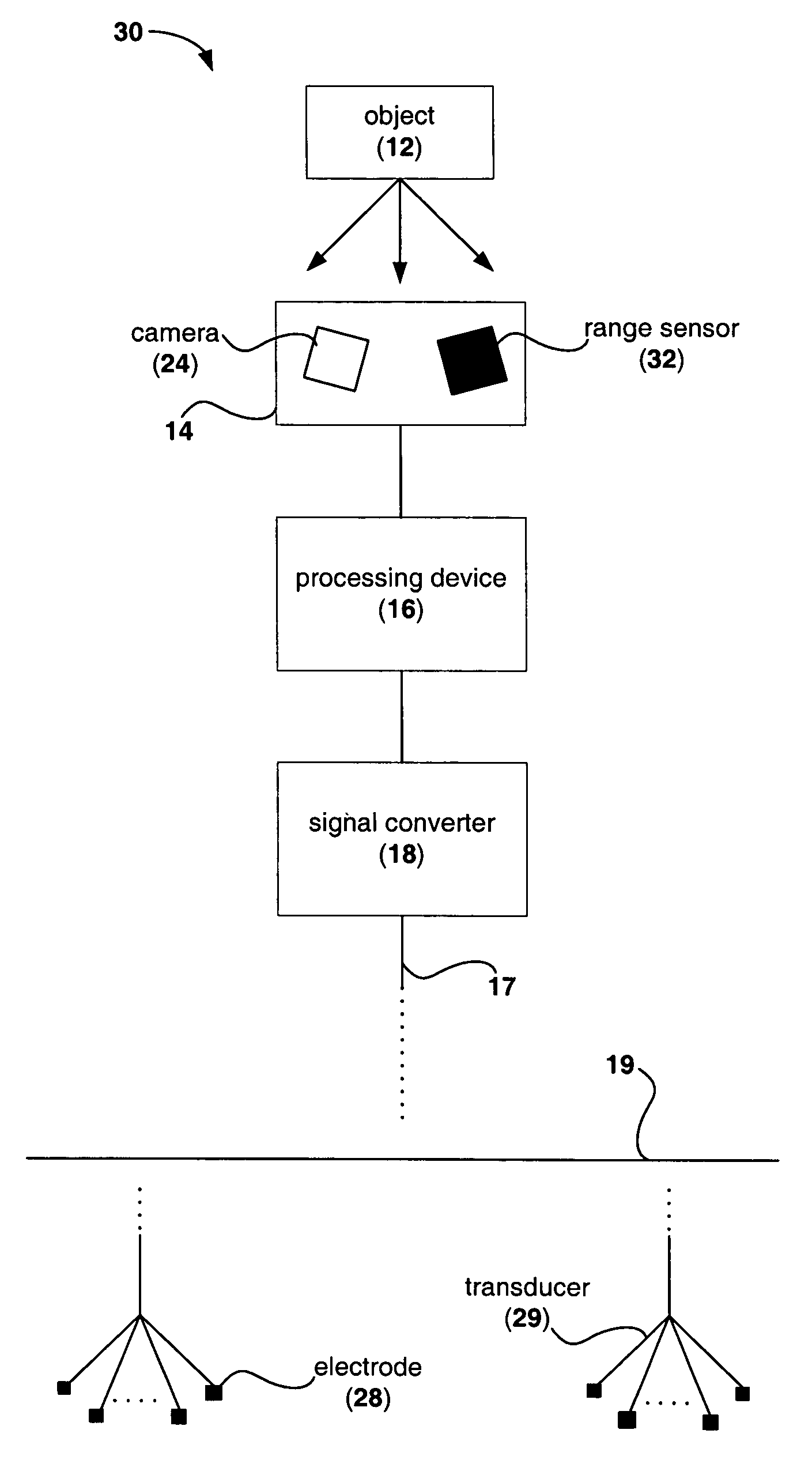
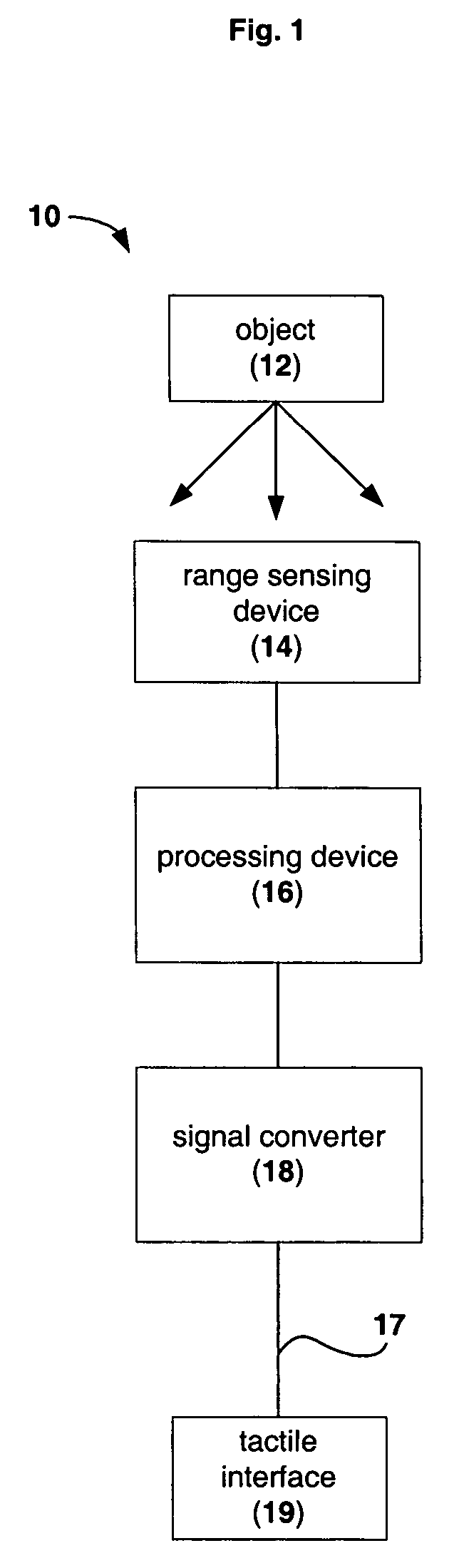
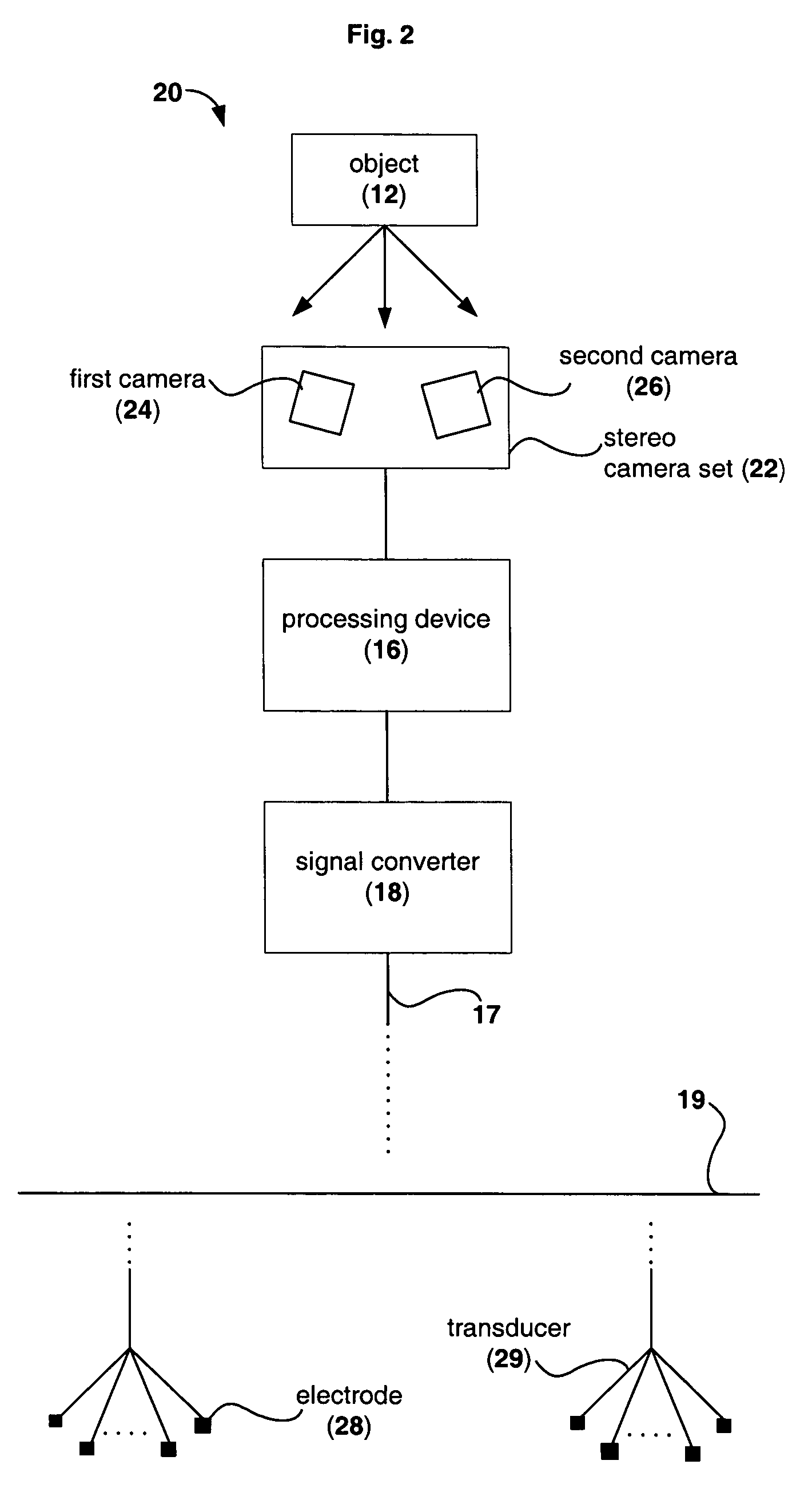
Device for providing perception of the physical environment
Owner:UNIV OF WOLLONGONG
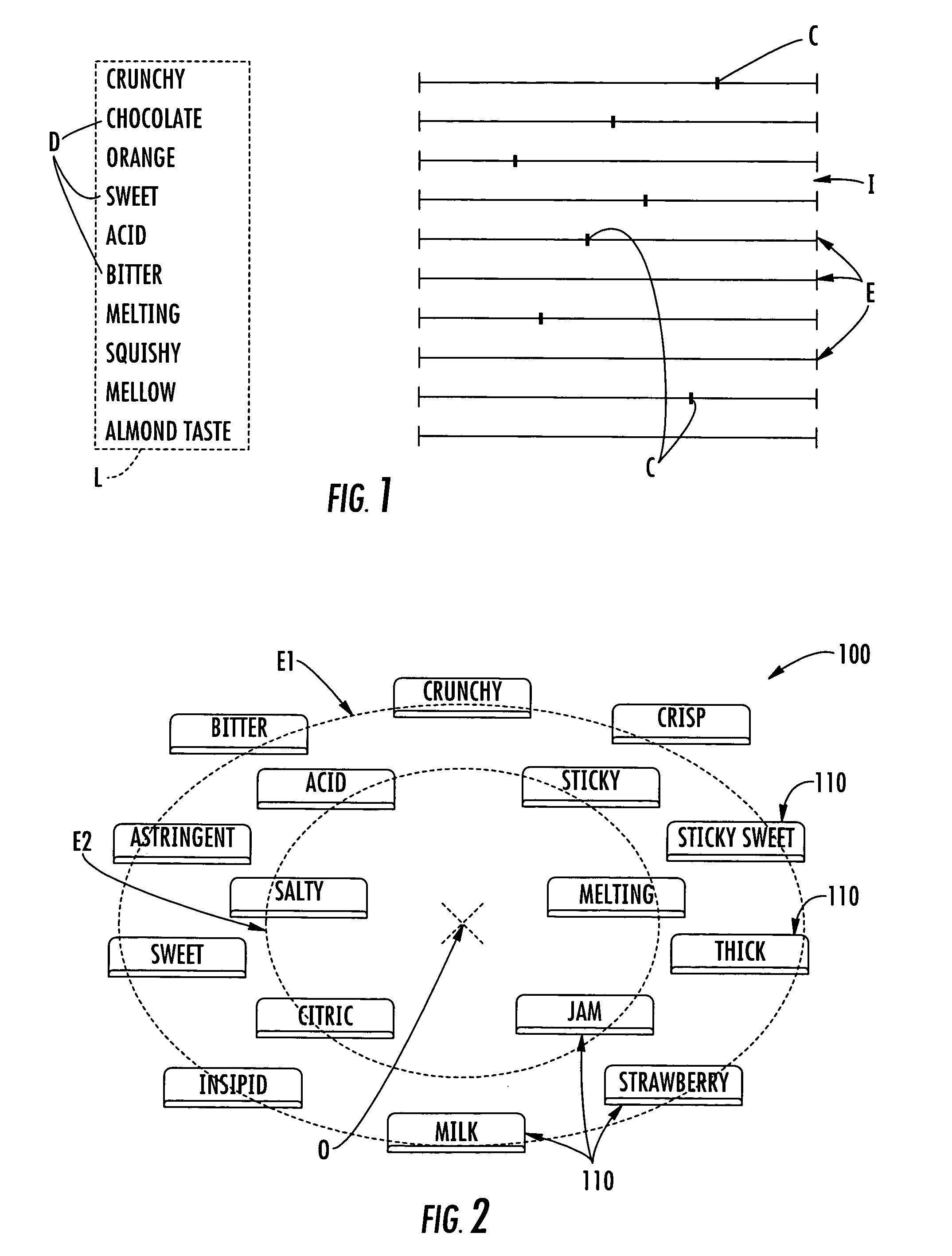
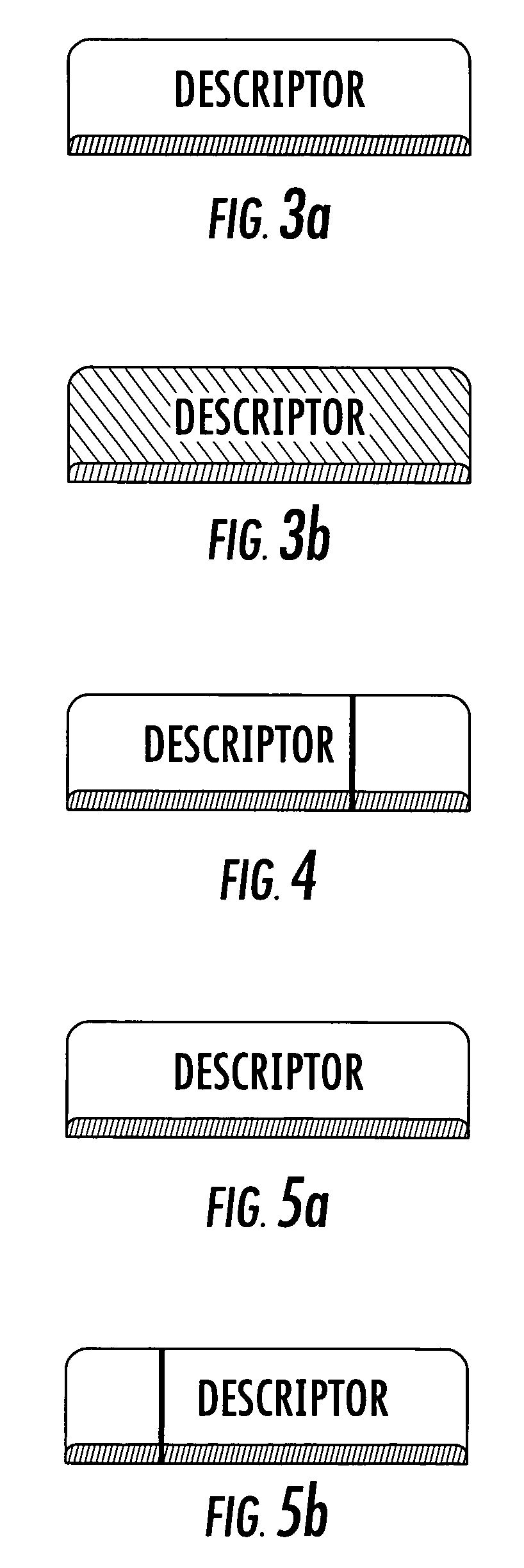
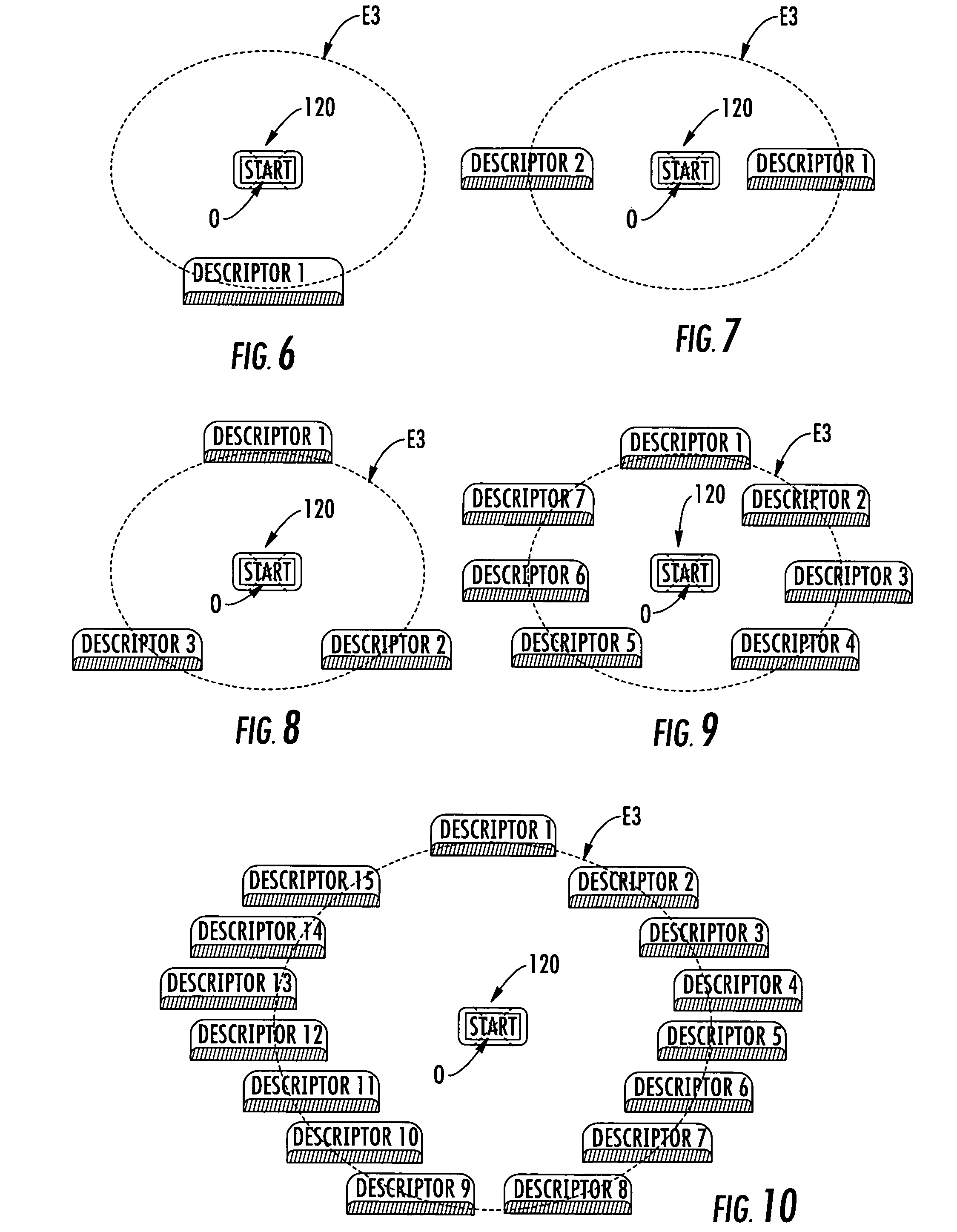
Method of analyzing industrial food products, cosmetics, and/or hygiene products, a measurement interface for implementing the method, and an electronic system for implementing the interface
InactiveUS7577530B2Easy to measureTesting beveragesTesting dairy productsElectronic systemsPattern perception
The invention seeks to improve the taking of physical measurements on an industrial product represented by organoleptic perceptions, the method providing a measurement interface that submits descriptors in a relative arrangement such that testers are not influenced by the order in which they appear, regardless of the descriptor and regardless of the field of the descriptor. For this purpose, the invention provides a method of analyzing industrial products in order to characterize them, in order to distinguish between them, and / or in order to modify them so as to improve them, by analyzing the responses of a panel of testers in application of certain descriptors. The method comprises steps consisting in selecting descriptors that are a priori pertinent for determining the organoleptic characteristics of the products; selecting a response mode; providing all of the descriptors simultaneously to the panel of testers on a single occasion and for a determined duration in a measurement interface presenting a center and an input zone for each descriptor, the input zones being distributed uniformly over at least a section of at least one conic about the center of the interface; collecting the responses from each tester as a function of the selected response mode; recording the responses; and analyzing the responses using at least one statistical method.
Owner:DANONE
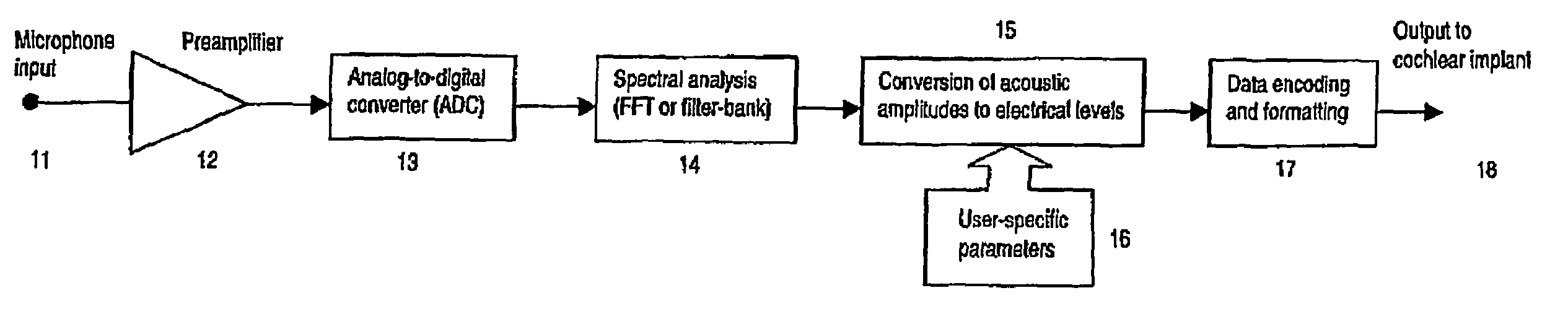
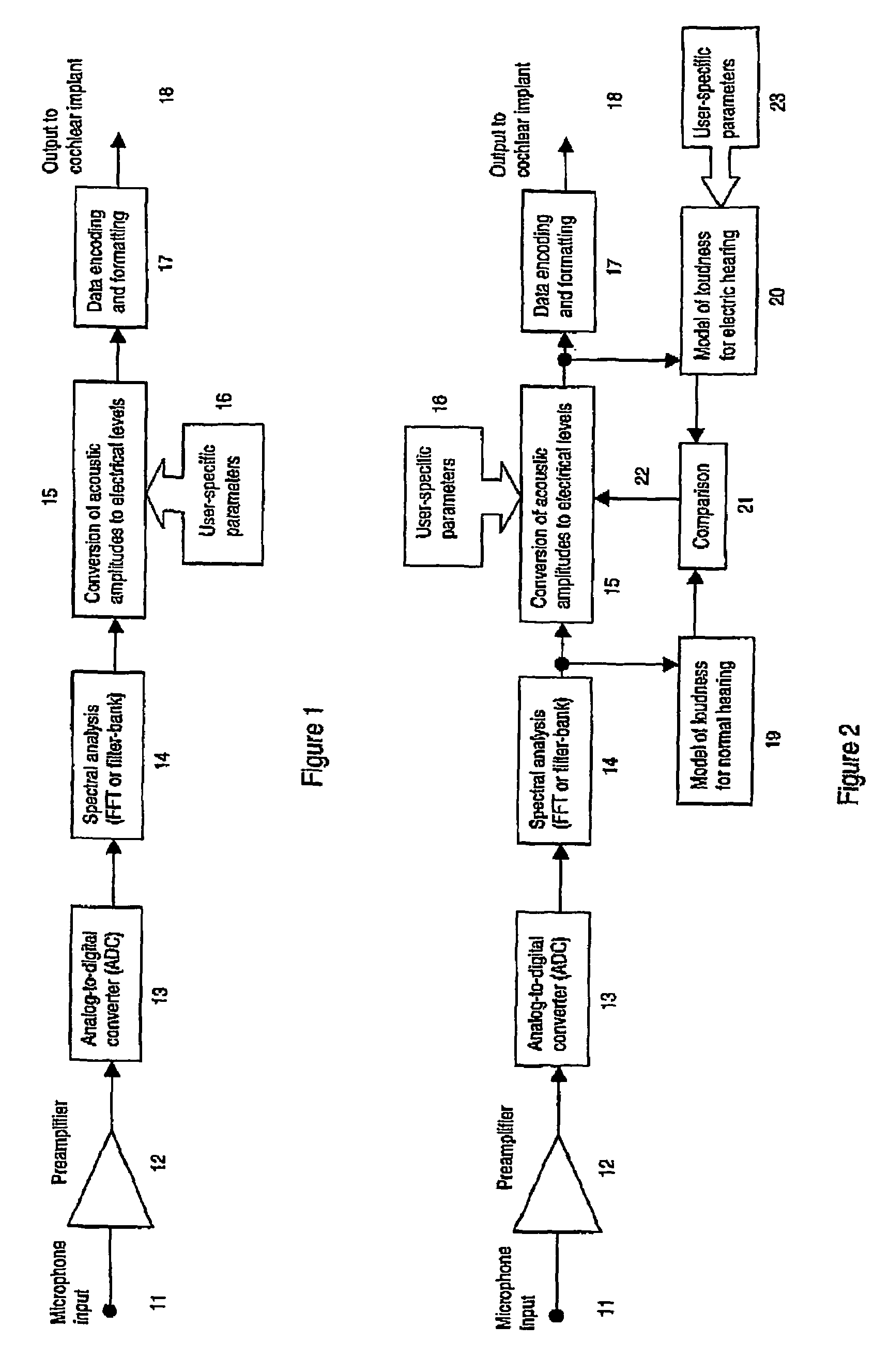
Sound-processing strategy for cochlear implants
InactiveUS7171272B2Reduce the impactImprove speech clarityElectrotherapySpeech analysisCochlear implantationProsthesis
A sound processing method for auditory prostheses, such as cochlear implants, which is adapted to improve the perception of loudness by users, and to improve speech perception. The overall contribution of stimuli to simulated loudness is compared with an estimate of acoustic loudness for a normally hearing listener based on the input sound signal. A weighting is applied to the filter channels to emphasize those frequencies which are most important to speech perception for normal hearing listeners when selecting channels as a basis for stimulation.
Owner:UNIVERSITY OF MELBOURNE
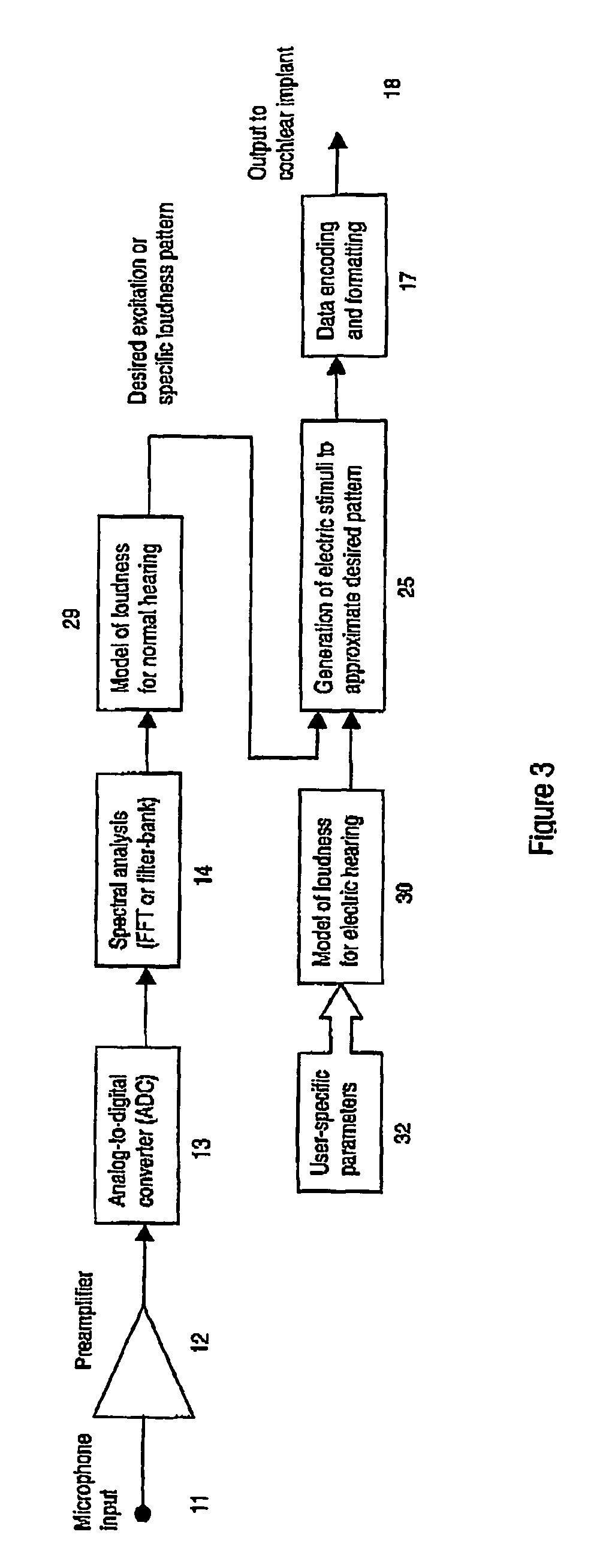
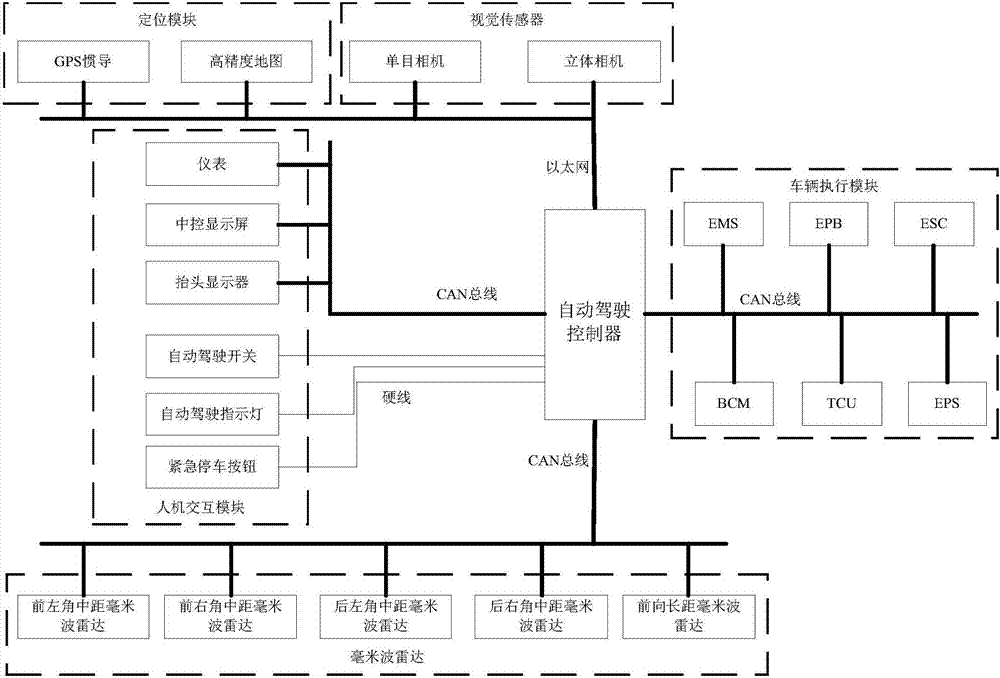
Automatic driving system based on highway
InactiveCN107031600ALow costEasy to integrateExternal condition input parametersStereo cameraPattern perception
The invention relates to the technical field of automatic driving, in particular to an automatic driving system based on a highway. The automatic driving system comprises a sensor, a positioning module, a man-machine interaction module, an automatic driving controller and a vehicle executing module. A traditional laser radar is replaced with a monocular camera, a stereo camera, a forward-direction long distance millimeter microwave radar and four-corner middle distance millimeter microwave radars which are arranged behind an inside-vehicle rearview mirror, at the center of a vehicle front bumper and on the two sides of the front bumper and a rear front bumper correspondingly. Multiple kinds of information in traffic sign road information and obstruction information are collected separately. The whole automatic driving system of perception fusion, path planning, decision planning, controlling and the like is integrated into an embedded type controller to achieve automatic driving. Compared with a traditional automatic driving system adopting the laser radar, the cost is low, and integration is easy. Perception precision is improved greatly, the system is high in integration level and small in size, the size of the automatic driving system is reduced greatly, the power consumption of the system is lowered, and mass production is easy.
Owner:DONGFENG MOTOR CORP HUBEI
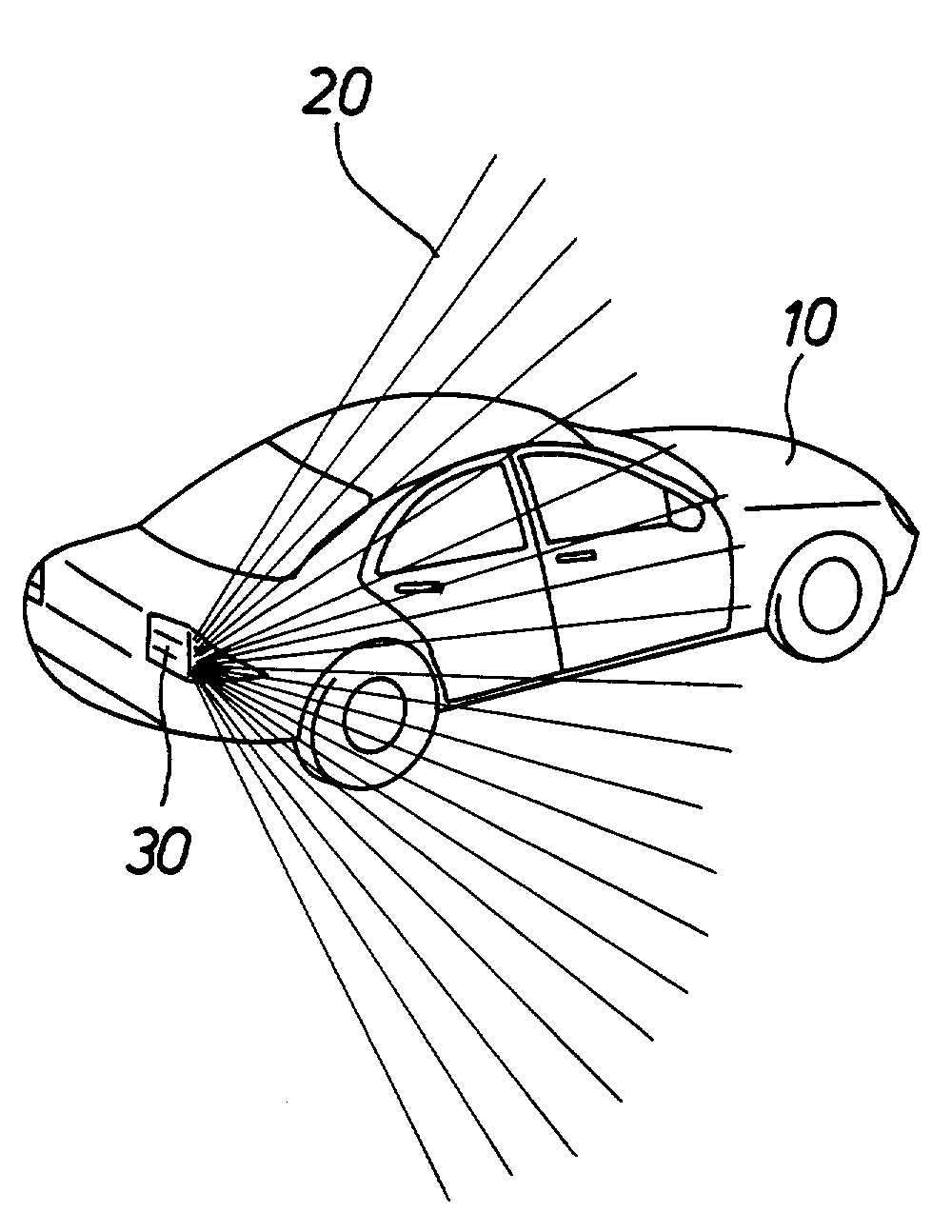
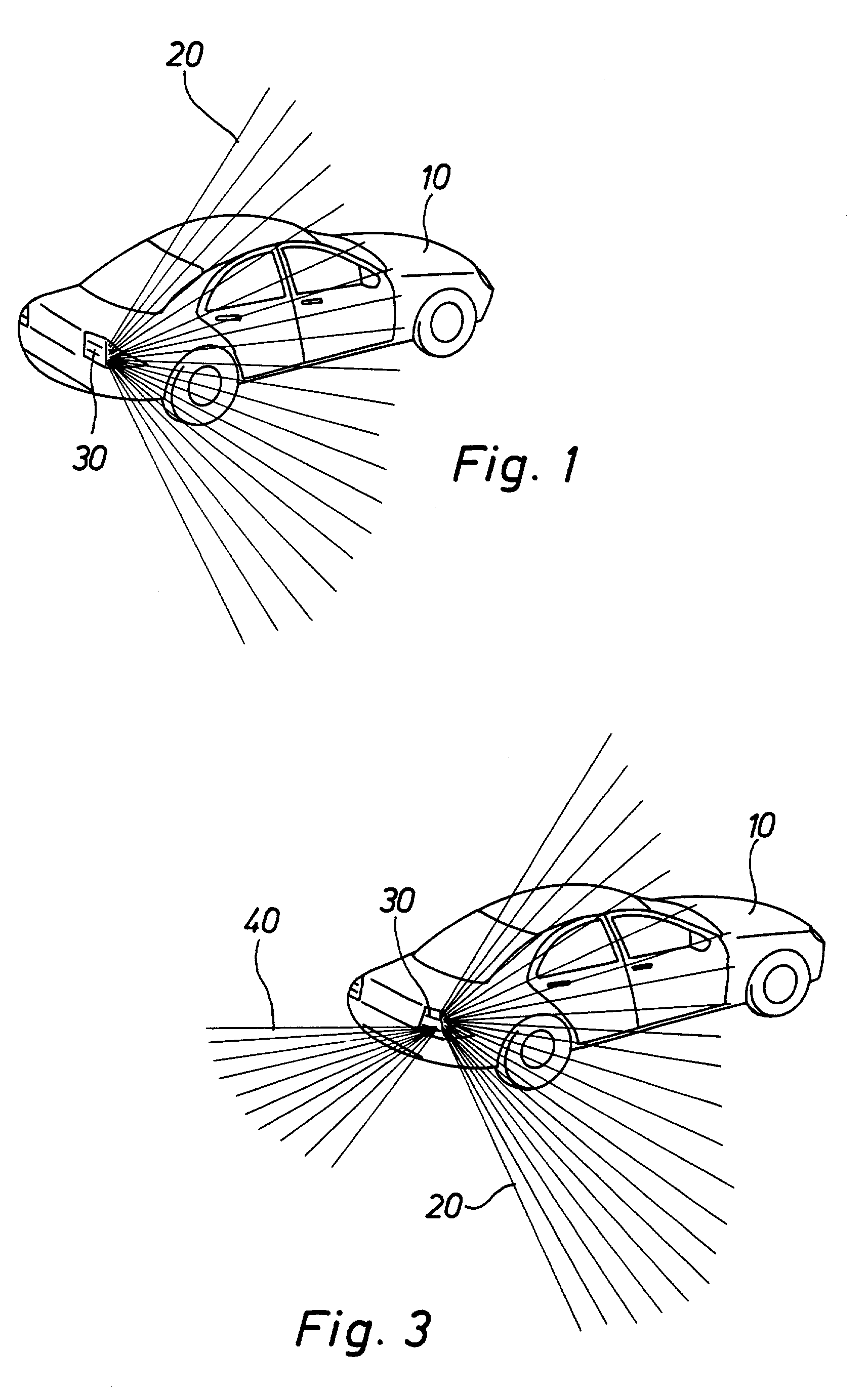
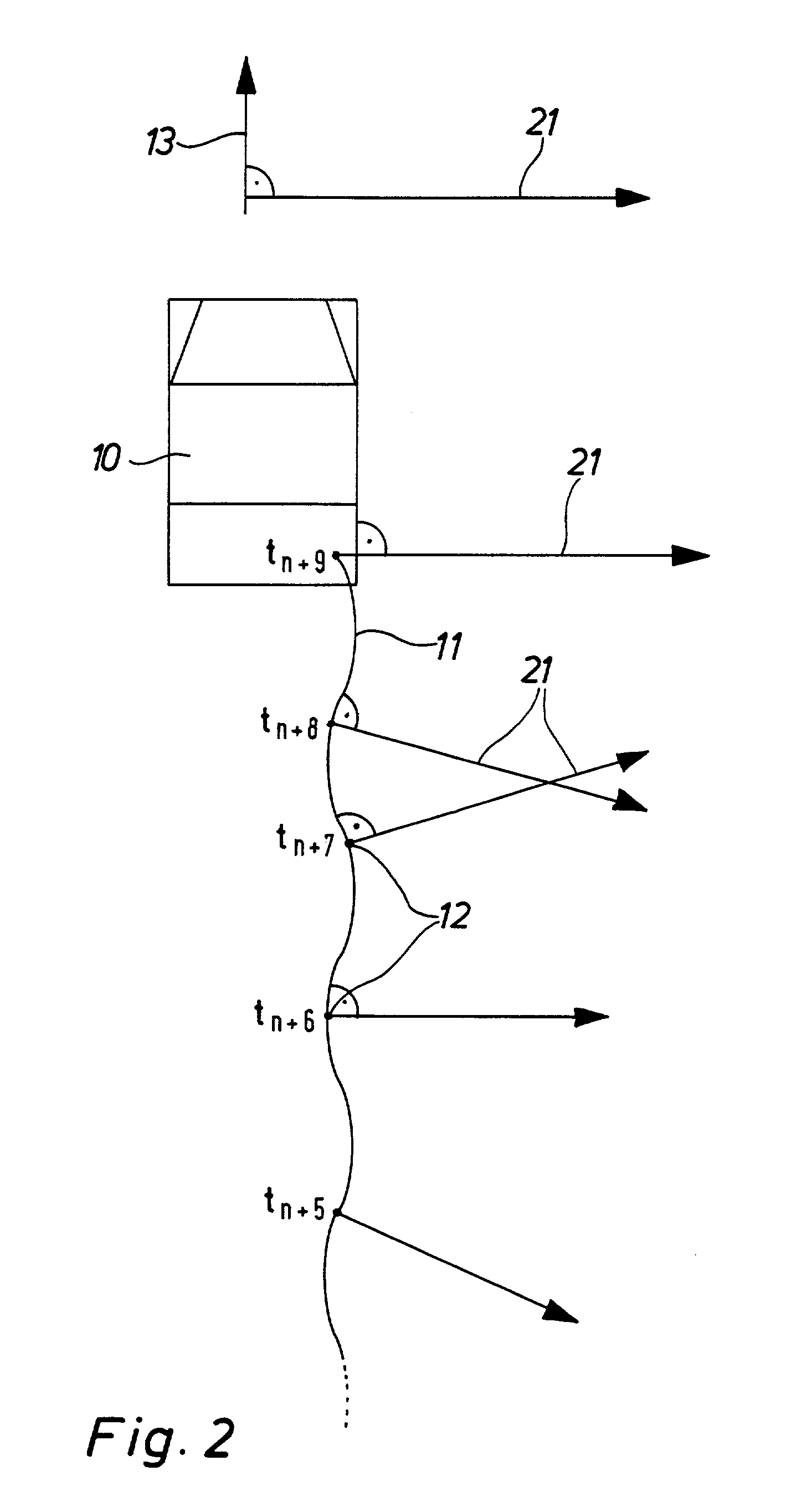
Three-dimensional perception of environment
InactiveUS7230640B2Character and pattern recognitionColor television detailsMobile vehicleImage resolution
A vehicle-useful, high-resolution 3D-detection of the environment of a street vehicle with environment scanning sensors is not possible today. Depending on application the first commercially available vehicle integrated systems may be a comprise between resolution of the sensors and size of the sampled area. With the inventive two dimensional distance resolution sensor device it becomes possible, in contrast to those which are known, to produce a system which, installed in a street vehicle, detects and preferably processes complex dynamics scenarios such for example street traffic, from the prospective of the active dynamic moving vehicle. Therein a three dimensional image of the environment is produced using a distance sensor, which produces a two dimensional distance profile (depth profile), and on the other hand, using a data processing and a storage unit, which process and store sequential distance profiles and sequence a series of distance profiles into the three dimensional image of the environment.
Owner:DAIMLER AG
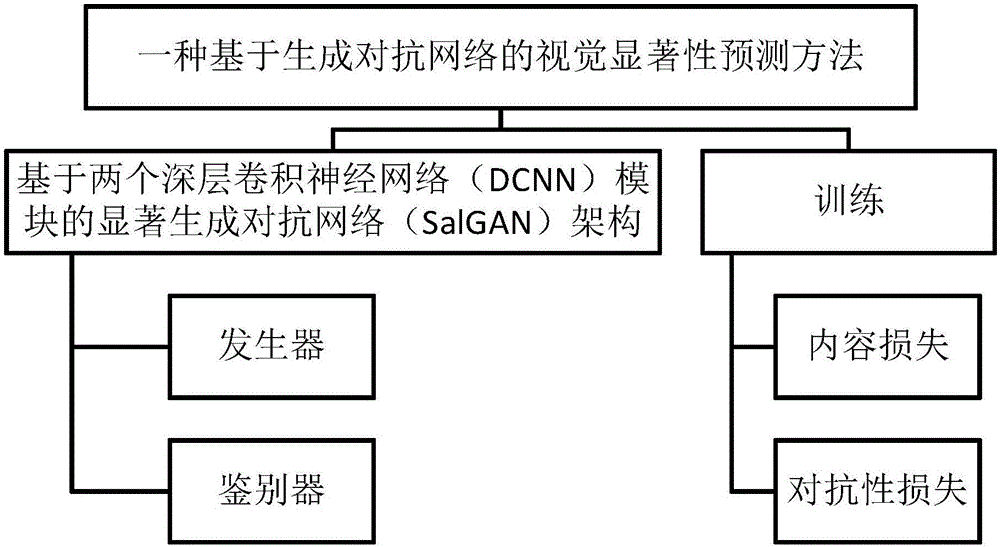
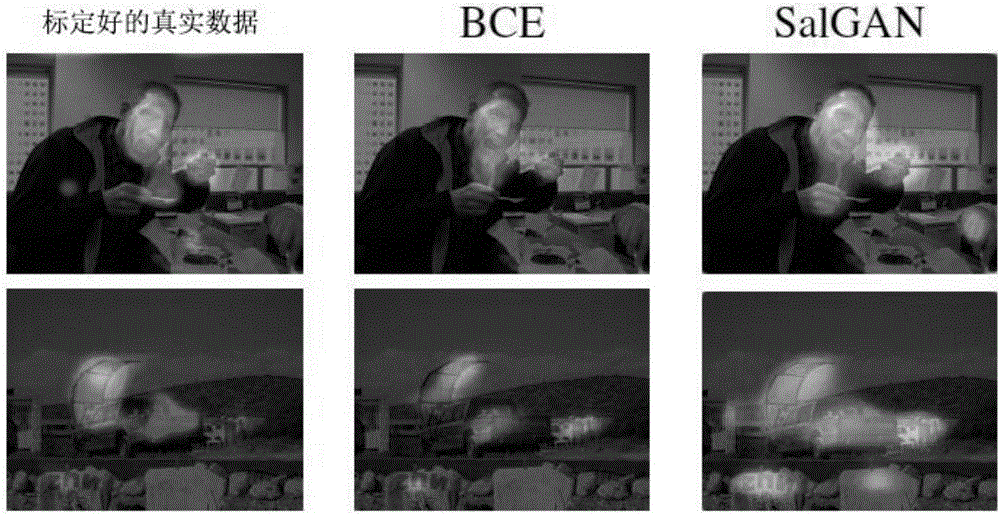
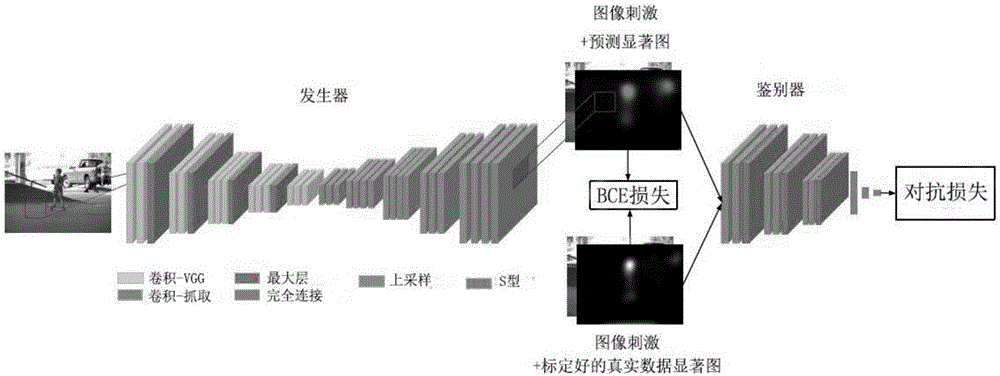
Visual significance prediction method based on generative adversarial network
InactiveCN106845471ACharacter and pattern recognitionNeural learning methodsDiscriminatorVisual saliency
The invention provides a visual significance prediction method based on a generative adversarial network. which mainly comprises the steps of constructing a saliency generative adversarial network (SalGAN) based on two deep convolutional neural network (DCNN) modules, and training. Specifically, the method comprises the steps of constructing the saliency generative adversarial network (SalGAN) based on two deep convolutional neural network (DCNN) modules, wherein the saliency generative adversarial network comprises a generator and a discriminator, and the generator and the discriminator are combined for predicating a visual saliency graph of a preset input image; and training filter weight in the SalGAN through perception loss which is caused by combining content loss and adversarial loss. A loss function in the method is combination of error from the discriminator and cross entropy relative to calibrated true data, thereby improving stability and convergence rate in adversarial training. Compared with further training of individual cross entropy, adversarial training improves performance so that higher speed and higher efficiency are realized.
Owner:SHENZHEN WEITESHI TECH