A Digest Authentication Method for Non-Access Stratum in Trunking Communication System
A cluster communication and non-access layer technology, applied in the field of communication, can solve the problems of large security risks in the cluster communication system
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
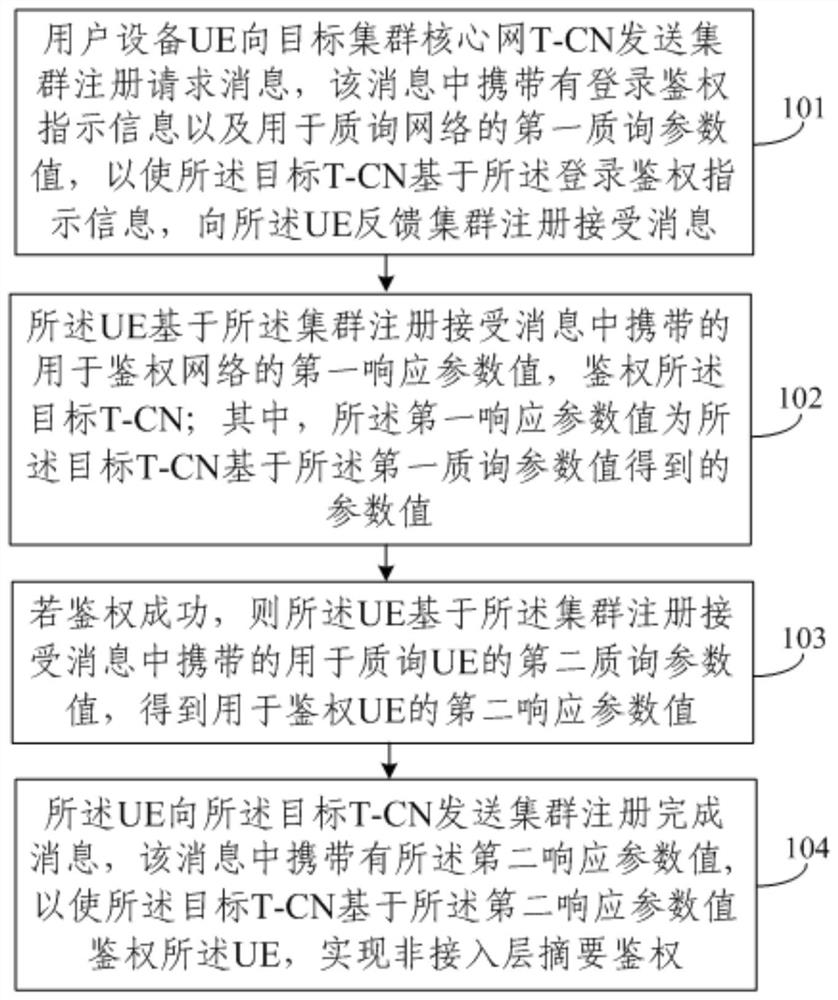
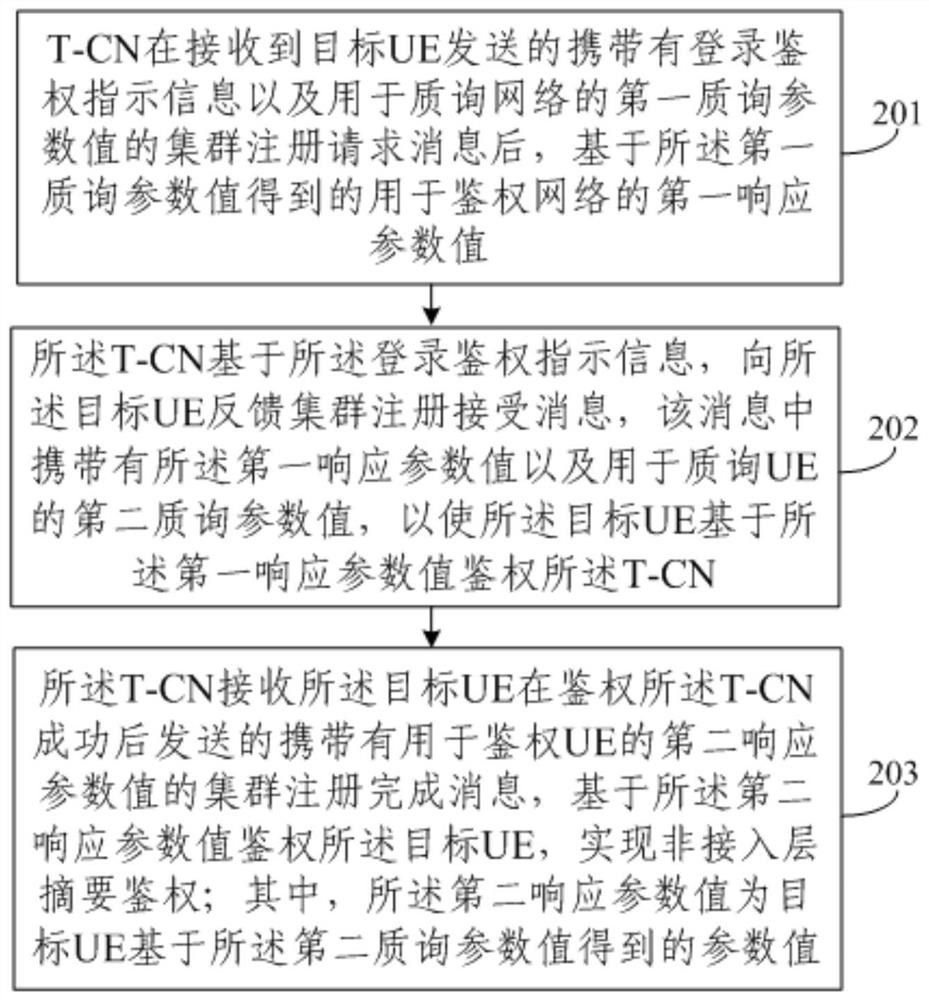
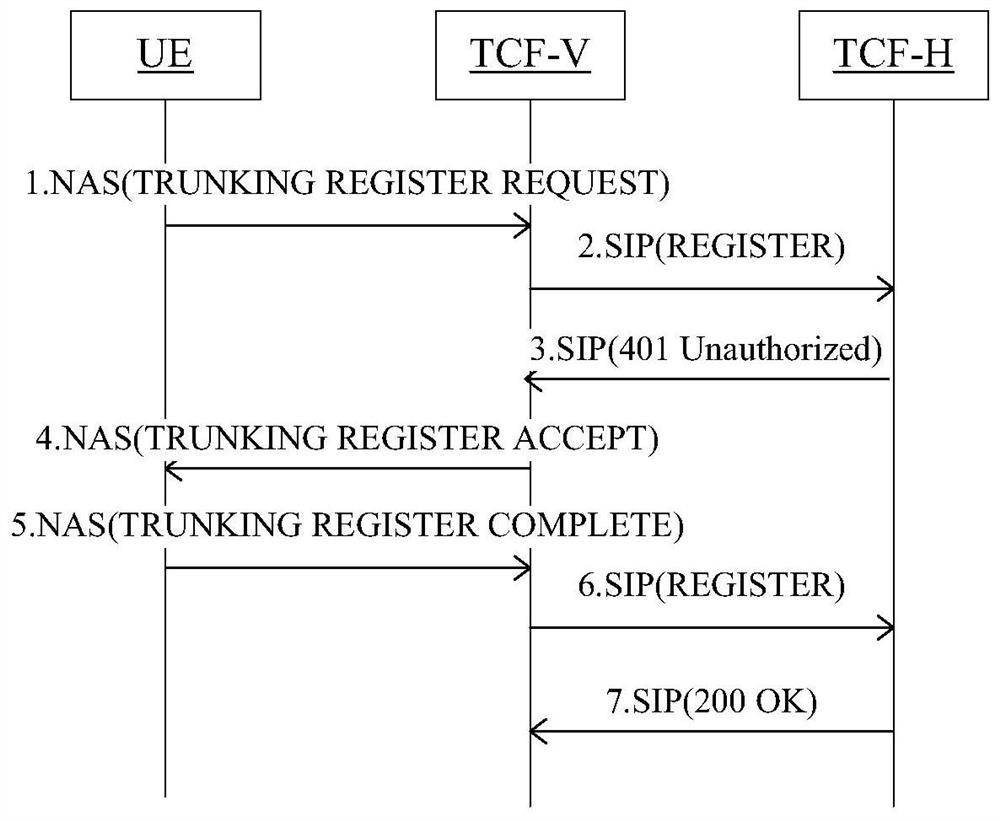
Method used
Image
Examples
Embodiment Construction
[0024] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention clearer, the technical solutions in the embodiments of the present invention will be clearly described below in conjunction with the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are the Some, but not all, embodiments are invented.
[0025] It should be noted that in this article, the words "first", "second", "third", and "fourth" are only used to distinguish the same names, not to imply the relationship between these names or order.
[0026] Each embodiment of the present invention follows the following premises and descriptions 1-4:
[0027] 1. After the user equipment (User Equipment, UE) (also referred to as user terminal) attaches to the LTE access network, the non-access stratum (Non-Access Stratum, NAS) signaling is all transmitted over the air interface in an encrypted manner. The authentication ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More