Malicious PDF document detection method based on TF-IDF algorithm and SVDD algorithm
A TF-IDF and detection method technology, applied in the field of malicious PDF document detection, can solve the problem that PDF documents are easily infected by JavaScript code, and achieve the effect of avoiding serious harm and efficient analysis and detection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
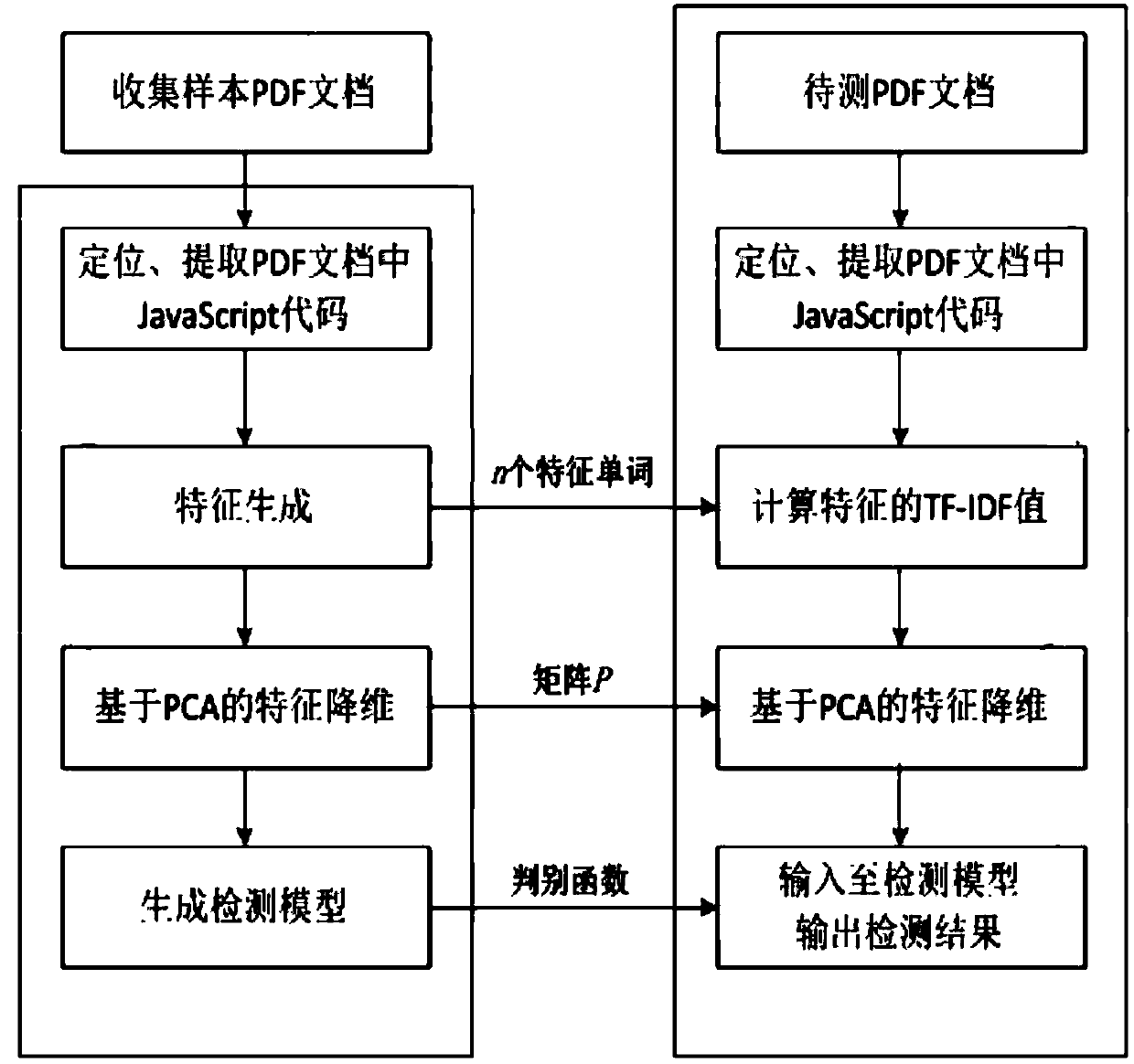
[0054] A malicious PDF document detection method based on TF-IDF algorithm and SVDD algorithm, comprising the following steps:
[0055] Step 1: Collect a certain number of malicious PDF documents and normal PDF documents as sample sets;
[0056] Step 2: Generate a detection model that can detect malicious PDF documents;
[0057] Step 3: Detect the PDF document to be tested, take the PDF document to be tested as input, and judge whether the PDF document to be tested is a malicious PDF document through the discriminant function of the detection model.
[0058] The detection model for generating detectable malicious PDF documents described in step 2 also includes the following steps:
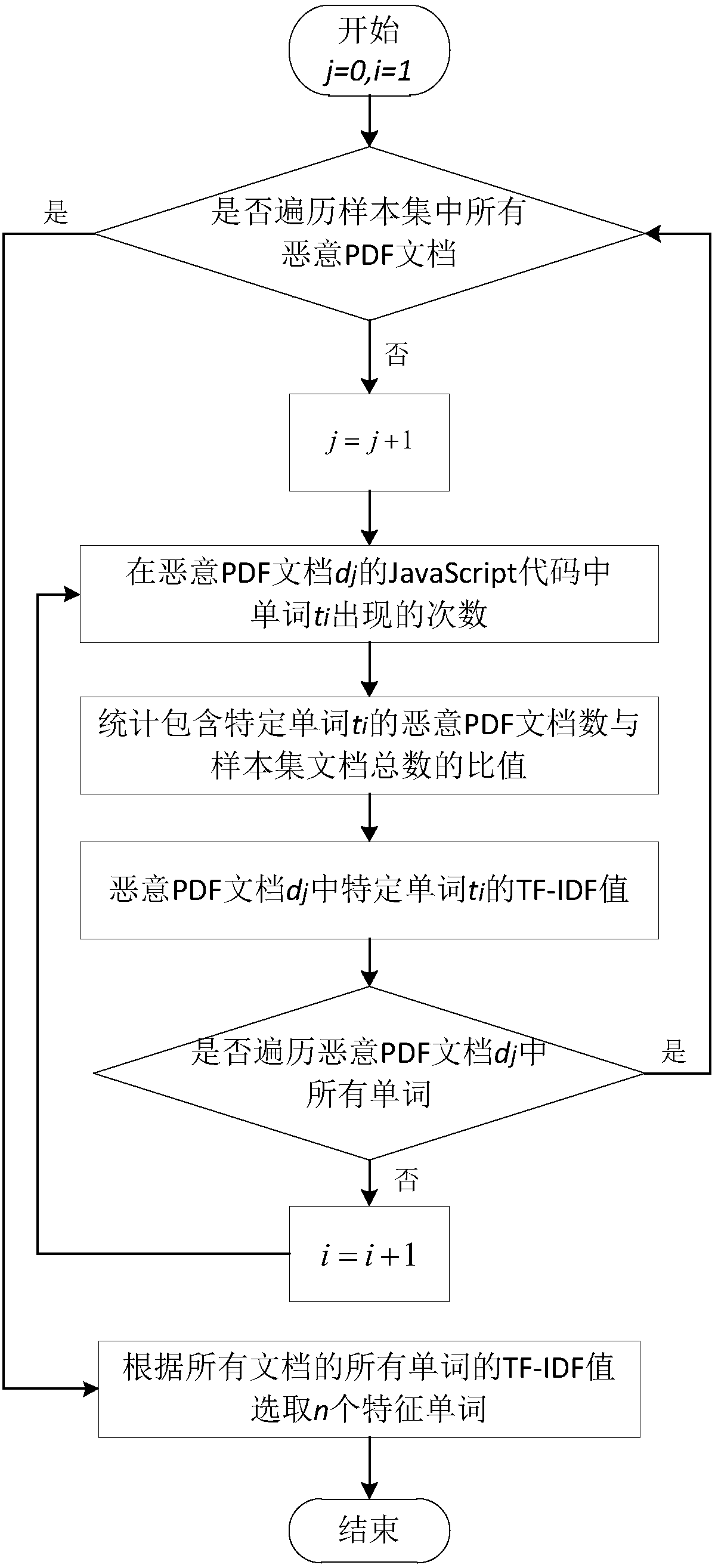
[0059] Step 2.1: Locate and extract the suspicious JavaScript code contained in the malicious PDF document in the sample set;
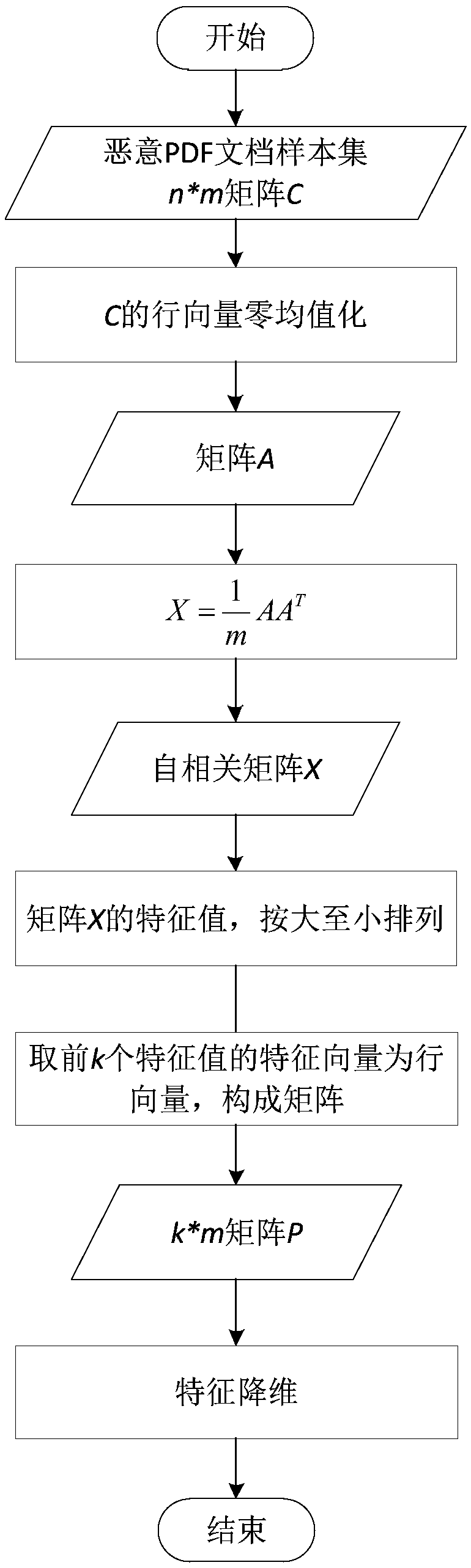
[0060] Step 2.2: Use the TF-IDF algorithm to generate malicious PDF document features, obtain a series of feature words, and count the TF-IDF values of the feature wor...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More