Memory data encryption method and device and memory data decryption method and device
A technology of memory data and encryption method, which is applied in the fields of digital data protection, electrical digital data processing, computer security devices, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
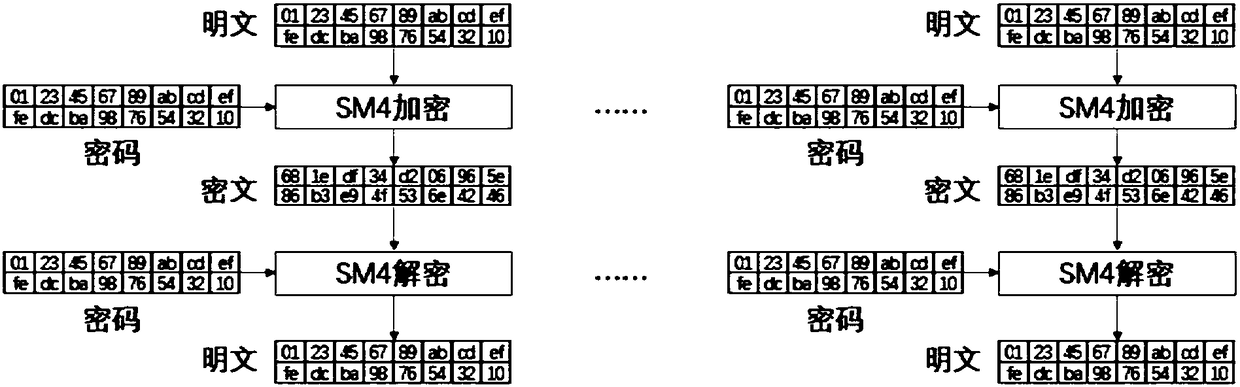
[0026] In order to express the technical solutions and advantages of the embodiments of the present invention more clearly, the technical solutions of the present invention will be further described in detail below with reference to the drawings and embodiments.
[0027] image 3 It is a flow chart of the memory data encryption method of the present invention. Such as image 3 As shown, the first embodiment of the present invention proposes a memory data encryption method, comprising the following steps:
[0028] In step S301, the plaintext of the memory data is obtained, and the address information of the data is obtained.
[0029] Specifically, first read the data of the physical memory address, obtain the plaintext of the memory data, and obtain address information for reading and writing the physical memory.
[0030] Step S302, using an encryption algorithm to encrypt the plaintext for the first time to obtain a primary ciphertext.
[0031] Specifically, the processor ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More