Authentication key negotiation method and system against continuous leakage
An authentication key negotiation and verification key technology, which is applied in the public key, transmission system, digital transmission system and other directions of secure communication, can solve the problem that the opponent cannot obtain the secret value, and achieve the effect of high security and high efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0030] In order to facilitate those of ordinary skill in the art to understand and implement the present invention, the present invention will be further described in detail below in conjunction with the accompanying drawings and examples. It should be understood that the implementation examples described here are only used to illustrate and explain the present invention, and are not intended to limit this invention.
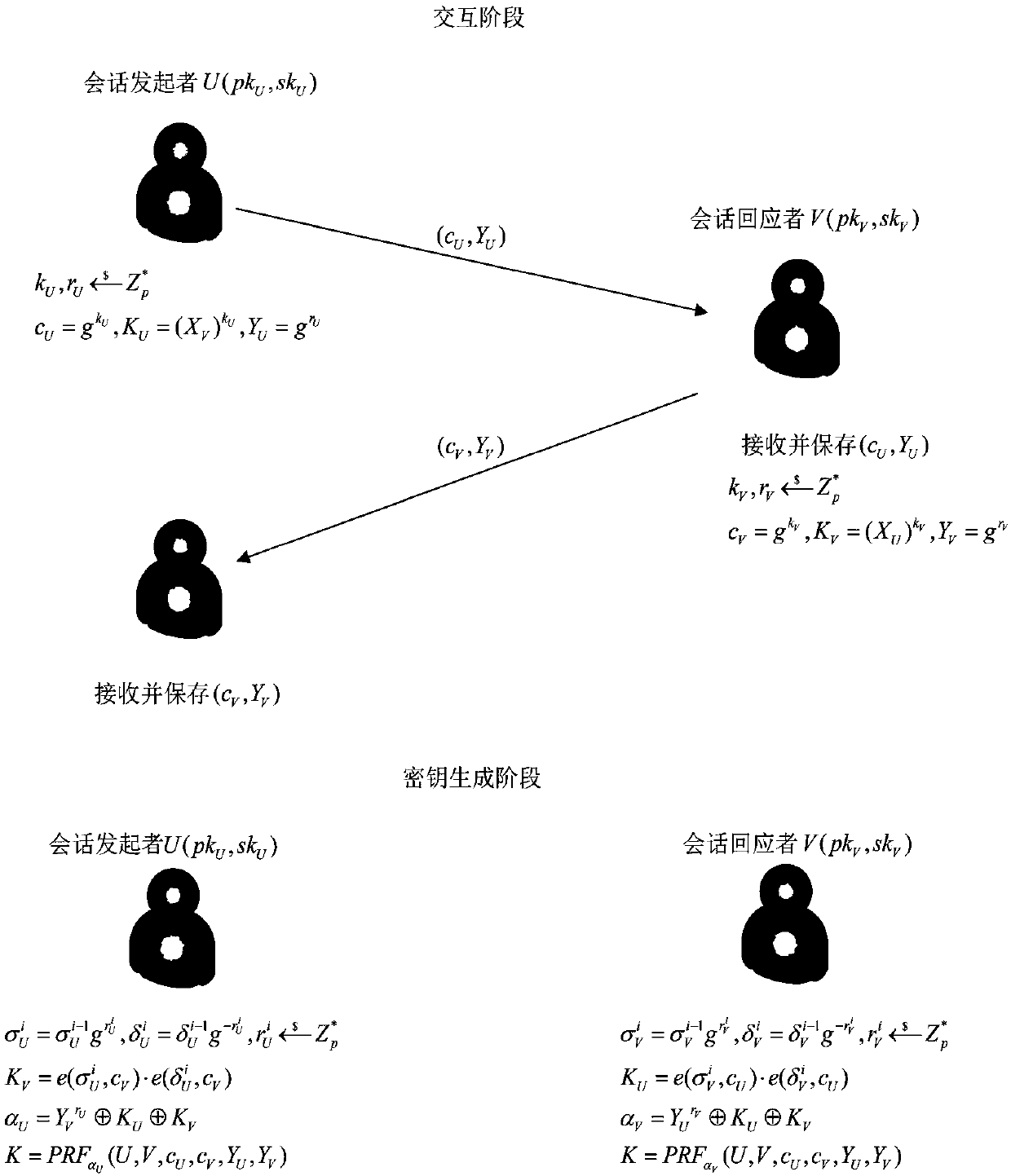
[0031] please see figure 1 , an authentication key agreement system against continuous leakage provided by the present invention, the system has two users in total, namely the session initiator U and the responder V, and each user has its own public-private key pair.
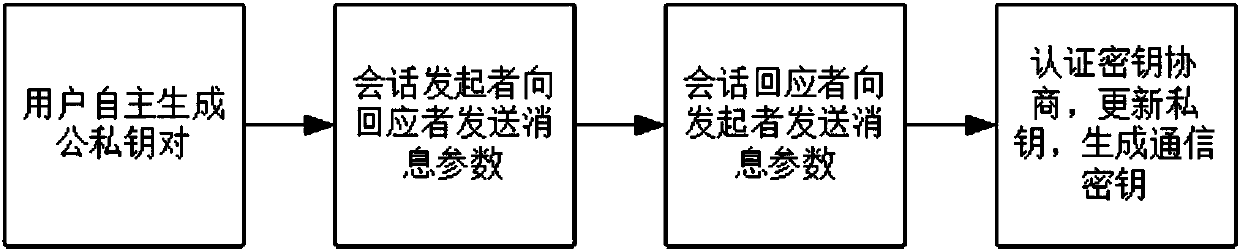
[0032] please see figure 2 , an authentication key agreement method against continuous leakage provided by the present invention, specifically comprising the following steps:
[0033] Step 1: The system is initialized, and the user independently generates a public-private key pair;
[0034] St...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More