User information management method, device, server and storage medium
A technology of user information and management methods, applied in the fields of user information management methods, devices, servers, and storage media, can solve problems such as complicated operations and long time-consuming, and achieve the effect of simplifying the operation process and shortening the login time
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
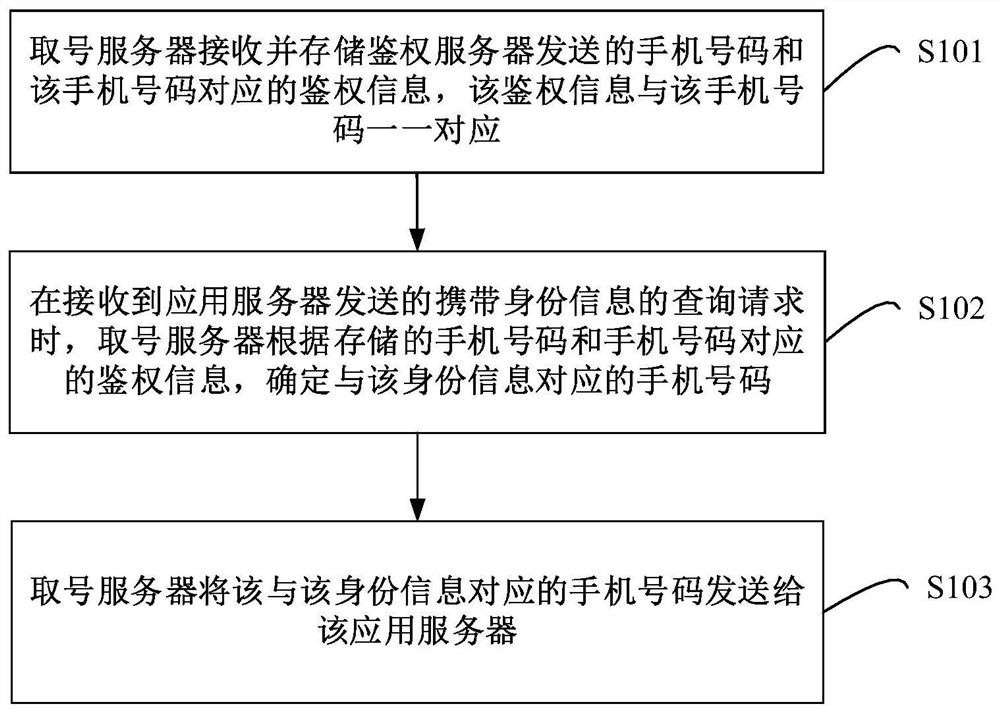
[0038] figure 1 It is a flow chart of the user information management method provided by Embodiment 1 of the present invention. The embodiment of the present invention provides a user information management method for the existing process of verifying the validity of a user's identity by verifying the validity of a mobile phone number through a mobile phone verification code, which is complicated to operate and takes a long time. Such as figure 1 The specific steps of the method are as follows:
[0039] Step S101, the number acquisition server receives and stores the mobile phone number sent by the authentication server and the authentication information corresponding to the mobile phone number, and the authentication information is in one-to-one correspondence with the mobile phone number.
[0040] Wherein, the number acquisition server is a server installed in the operator's headquarters, the authentication server is a server installed in each provincial department (or bra...
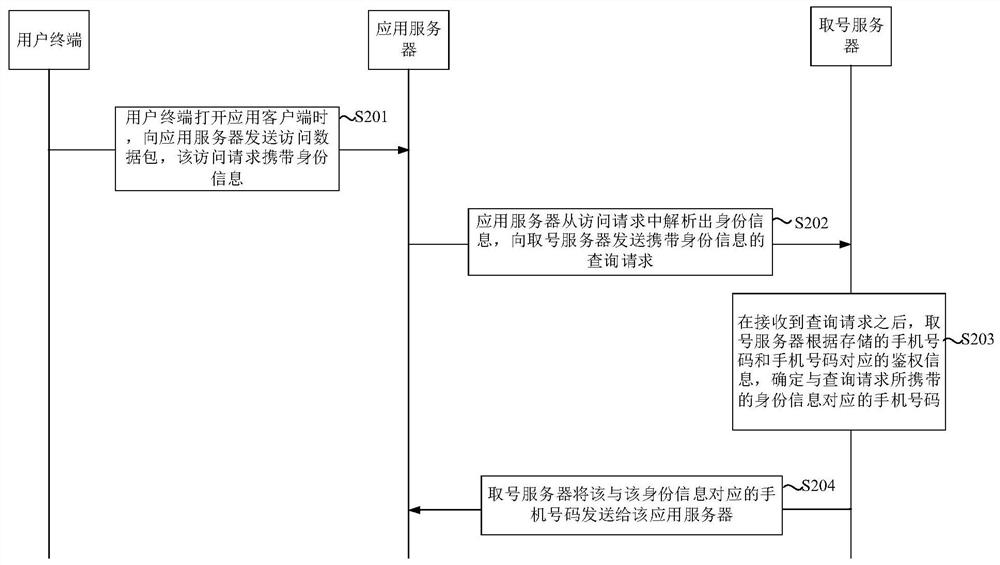
Embodiment 2
[0055] On the basis of the first embodiment above, in this embodiment, the authentication information corresponding to the mobile phone number includes the attribution region code of the mobile phone number and the private network IP in the mobile communication network, and the identity information is received by the application server. The private network IP and public network IP in the mobile communication network carried in the user terminal access request.
[0056] In this embodiment, when a user accesses the mobile communication network through a user terminal, the user terminal sends an activation request message to the gateway node to request the use of the mobile communication network, so that the gateway node sends a charging request message to the charging server to enable Radius accounting function. The charging request message is used to request the charging server to charge the mobile phone number for using the mobile communication network resources, and the charg...
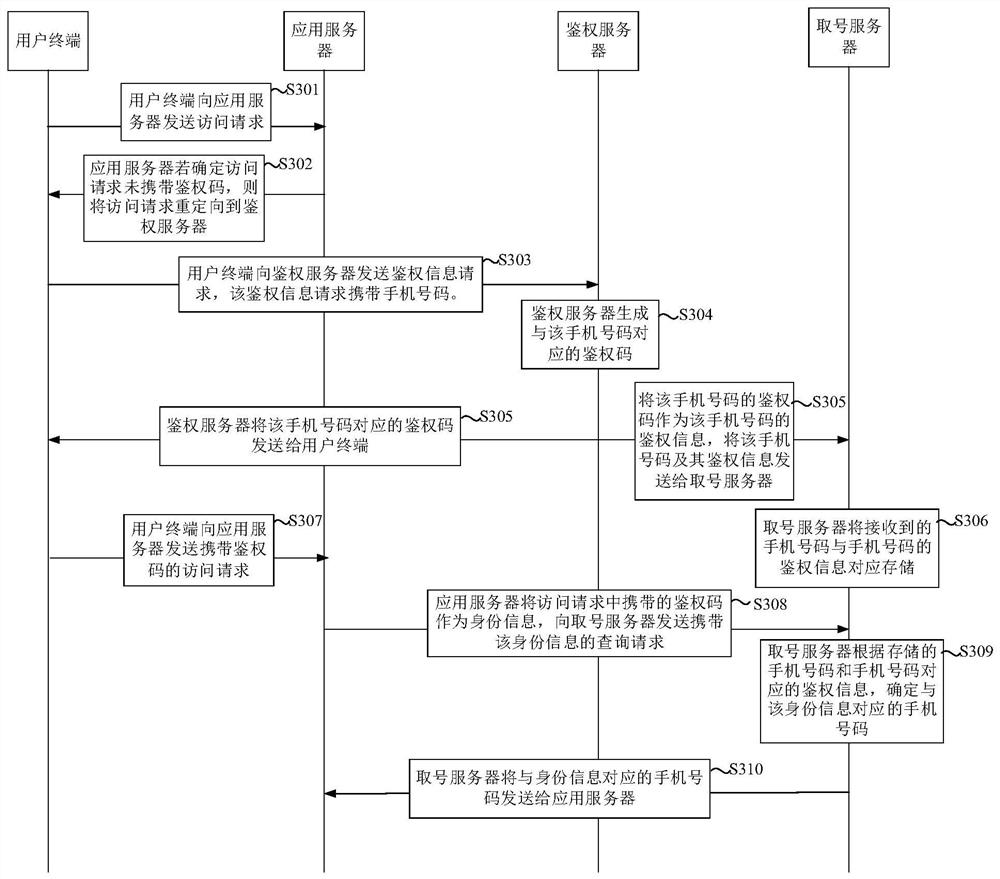
Embodiment 3
[0083] On the basis of the first embodiment above, in this embodiment, the authentication information corresponding to the mobile phone number is the authentication code of the mobile phone number generated by the authentication server, and the identity information is the user terminal access code received by the application server. The authentication code corresponding to the user terminal carried in the request.
[0084] In this embodiment, when the user opens the application client corresponding to the application server on the user terminal (the access traffic starts to be generated at this time), the user terminal sends an access request to the application server. When the application server receives the access request, if it determines that the access request does not carry the authentication code, it redirects the access request to the authentication server, so that the user terminal sends an authentication information request to the authentication server, and the authen...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More