6LoWPAN network intrusion detection method based on improved KNN
A technology of network intrusion detection and intrusion detection, applied in network topology, short-distance communication services, security devices, etc., can solve problems such as wrong prediction, resource consumption, ICMP abuse, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
[0308] Attack result: Assume that the attack achieves that node 10 is captured. That is, node 10 is a puppet network element.
[0309] Intrusion Detection Implementation:
[0310] 1) constructing a network element state data table;
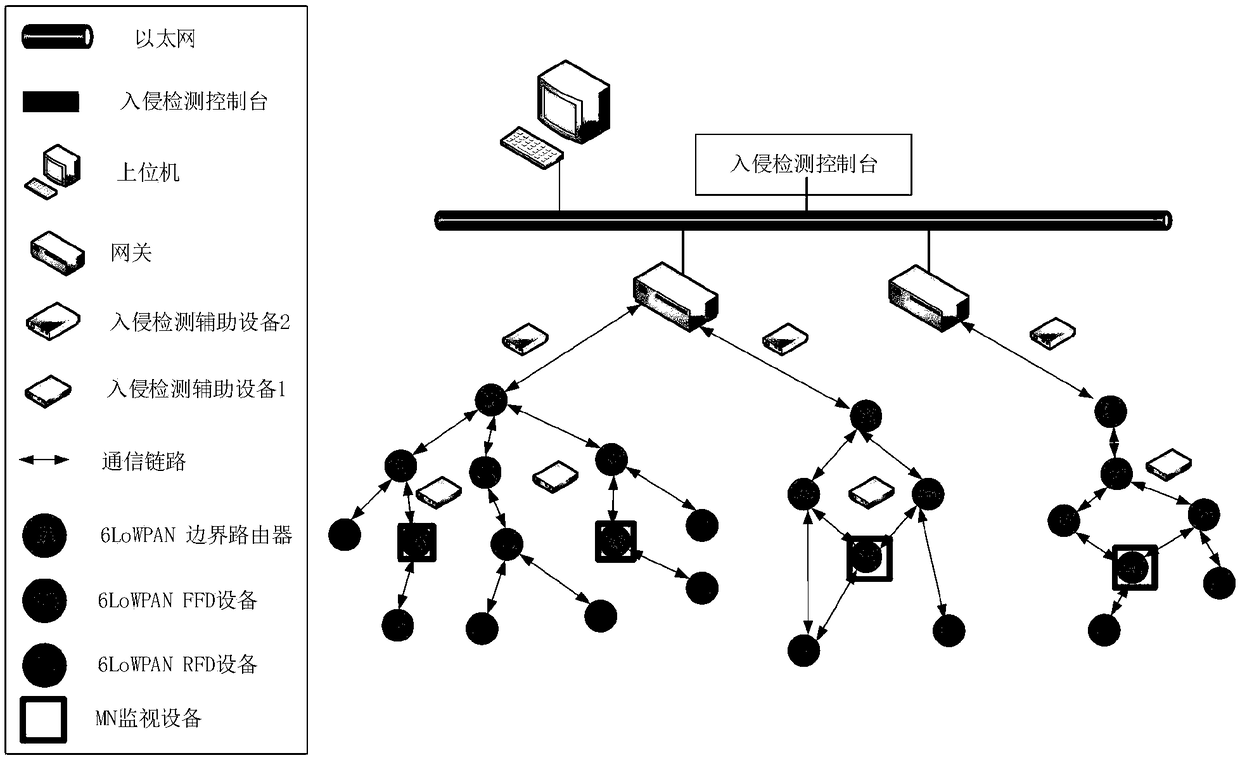
[0311] There are a total of 12 network elements in the network. Among them is a 6R network element.
[0312] Therefore, the amount of network element status data is taken as 20.
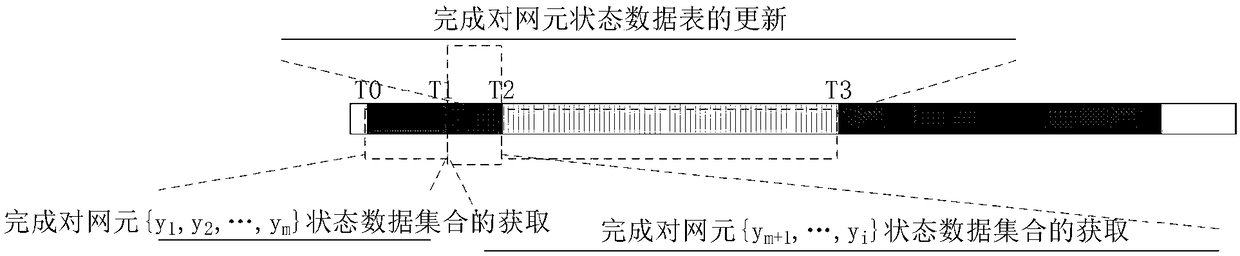
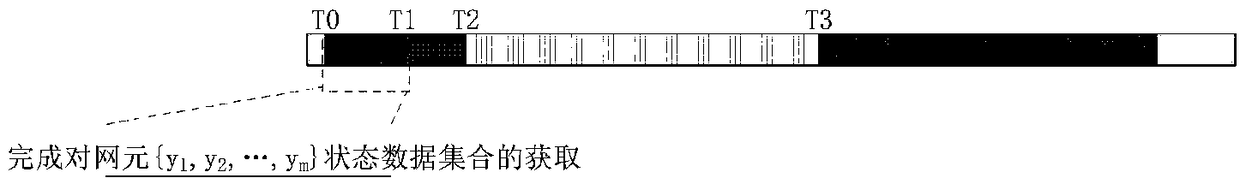
[0313] The network starts from running T 0 →T 1 , T 1 →T 2 Each network element captures data and forms a network element status data table on the console for the first time.
[0314] The algorithm for forming the network element status data table for the first time is as follows:
[0315]
[0316]
[0317] 2) Detection process: construct feature space and establish normal contour.
[0318]
[0319] Intrusion detection results:
[0320] It is easy to see that the parameter k=1 / 12*20≈2
[0321] The intrusion detection process calculates that the data ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More