A trajectory sensitive data protection method supporting personalized privacy
A sensitive data and trajectory technology, applied in digital data protection, electrical digital data processing, instruments, etc., can solve problems such as sensitive location leakage
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0043] In order to make the purpose, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments. The specific embodiments described here are only used to explain the present invention, not to limit the present invention.
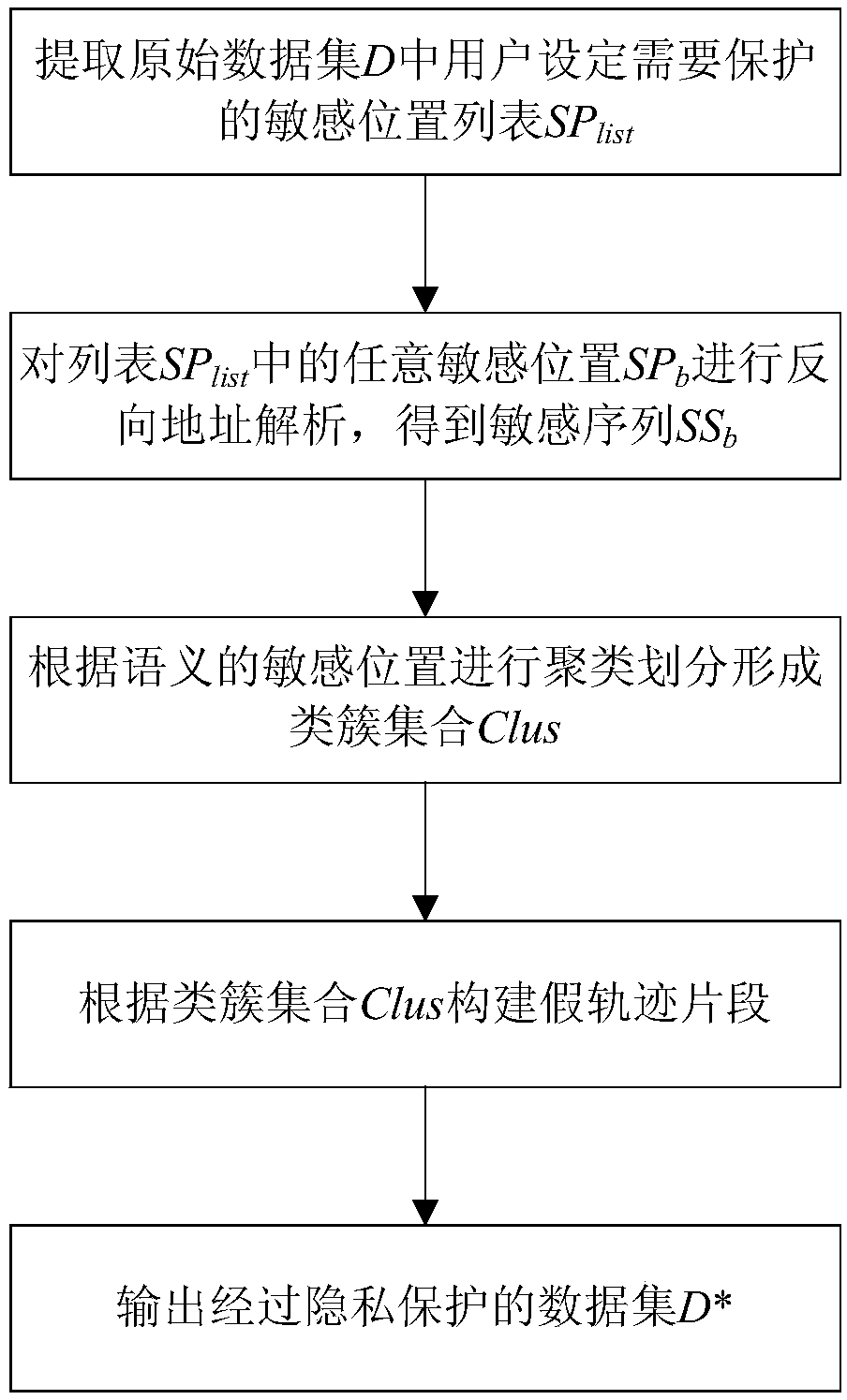
[0044] A trajectory-sensitive data protection method that supports personalized privacy, the process is as follows figure 1 As shown, the specific method is as follows:
[0045] Step 1: Extract the sensitive location list SP set by the user to be protected in the original data set D list .
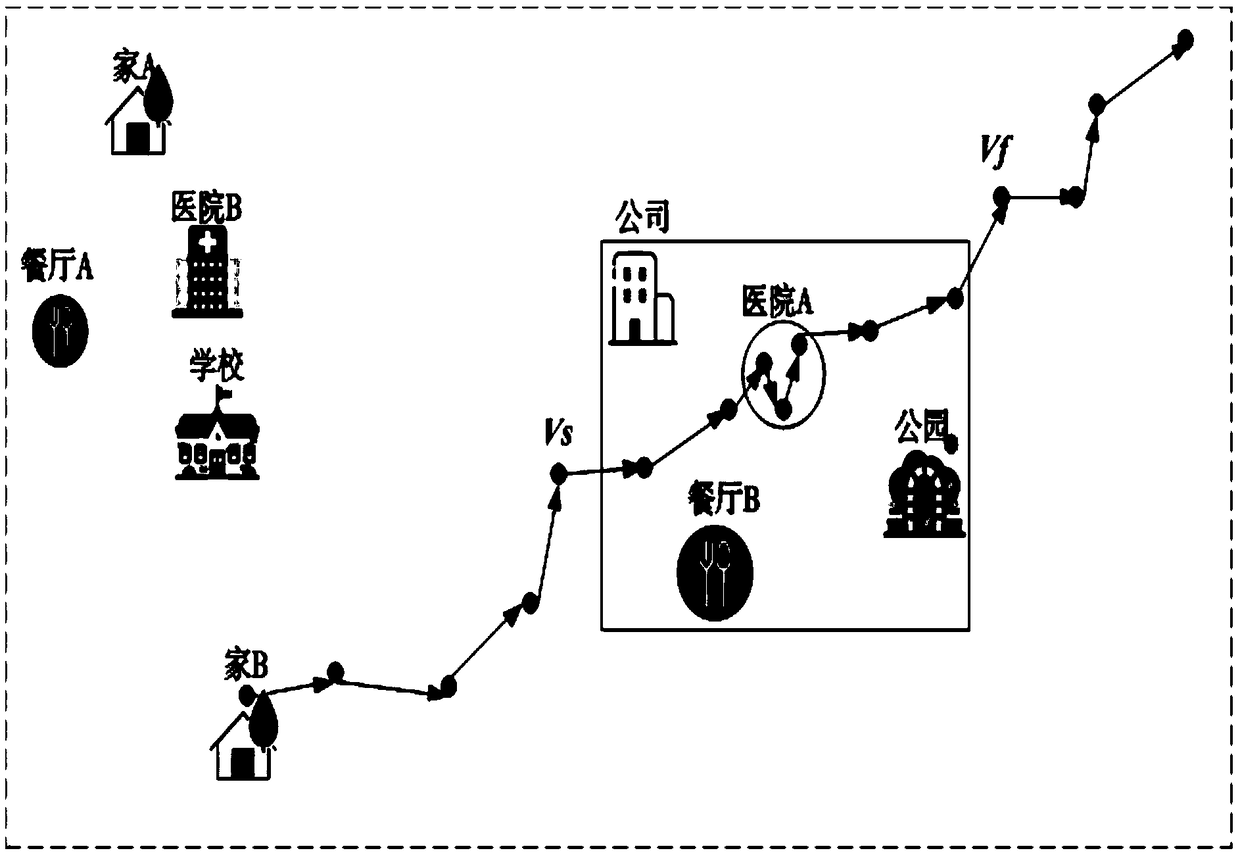
[0046] In this example, 182 volunteers collected by GeoLife of Microsoft Asia Research Institute from April 2007 to August 2012 have a total of 17,621 trajectories, and the total length of trajectories is 1,292,951 kilometers. The trajectories in the original data set are screened, and only BJ is selected. Trajectory data with...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More