A role-based method of authorizing permissions for form operations
A technology of operation authority and role, which is applied in the direction of instruments, digital data authentication, data processing applications, etc., can solve problems such as complex time-consuming, incapable of batch authorization, loss of system users, etc., to improve work efficiency, improve enterprise management system, The effect of saving working time
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 4
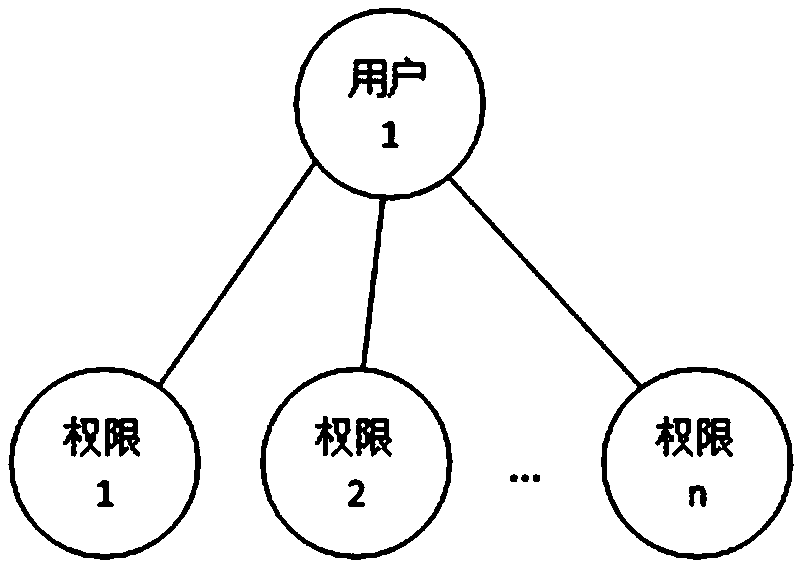
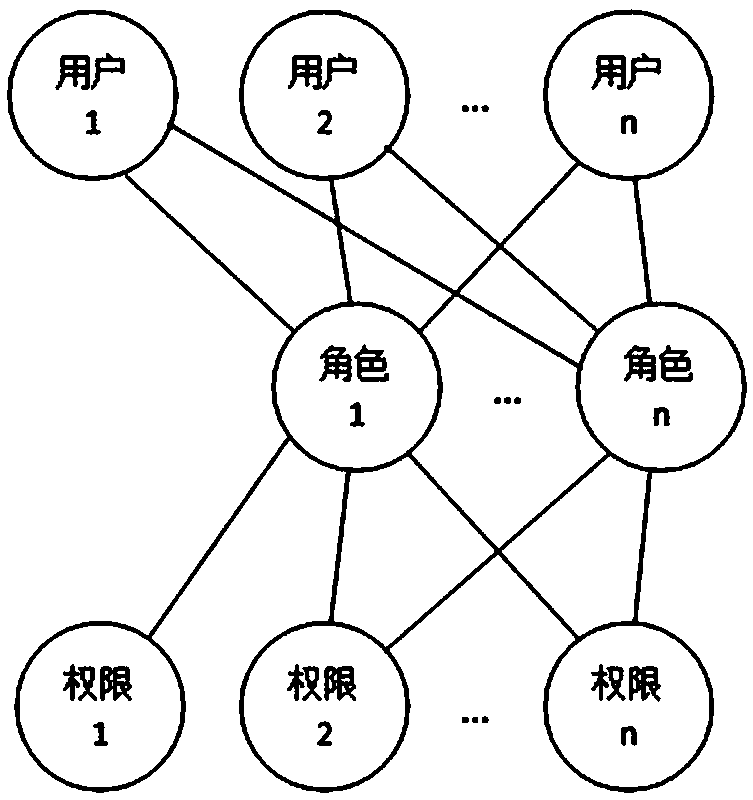
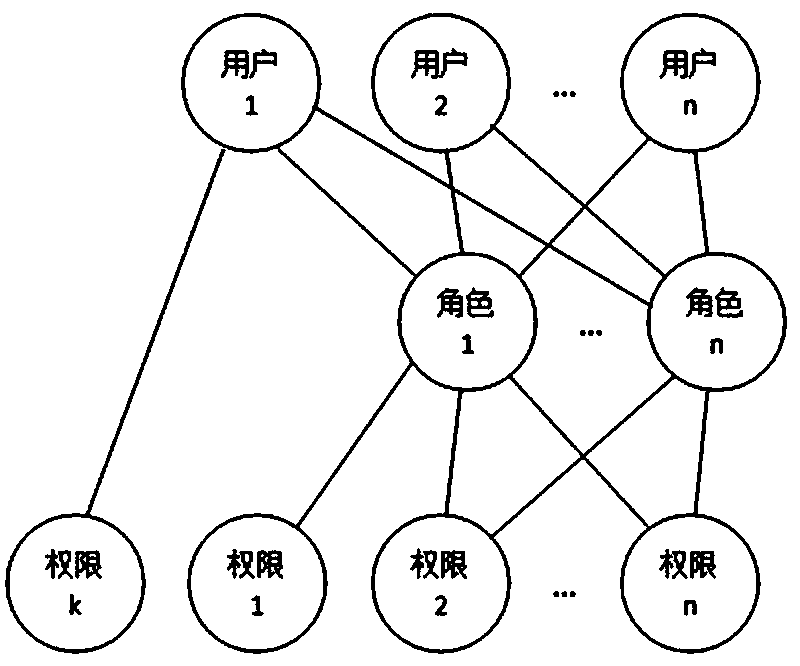
[0046] [Example 4] Role-based form operation authority authorization method, including selecting authorized roles: selecting one or more roles as authorized roles, each role is an independent individual, not a group / class, and one role at the same time Only a unique user can be associated, and a user is associated with one or more roles; select form: select one or more forms, when the selected authorized role is one and the selected form is one, it will display the authorized role pair. The current operation permission status of the selected form, the previously selected and saved form operation permission in the selected form of the authorized role is automatically selected; when there are two or more of the authorized role and the selected form, it will display Form operation authority, the form operation authority is not selected; authorize the form (selected form) operation authority to the authorized role: display all the operation authority of the form, select an existing...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More