Image encryption method based on 3D scrambling model and chaos
An encryption method and scrambling technology, applied in computer security devices, instruments, computing and other directions, can solve the problems of weak security and low encryption efficiency, and achieve the effect of protecting security, improving security and improving encryption effect.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] The implementation process of the present invention will be further described in detail below in conjunction with specific drawings and examples.
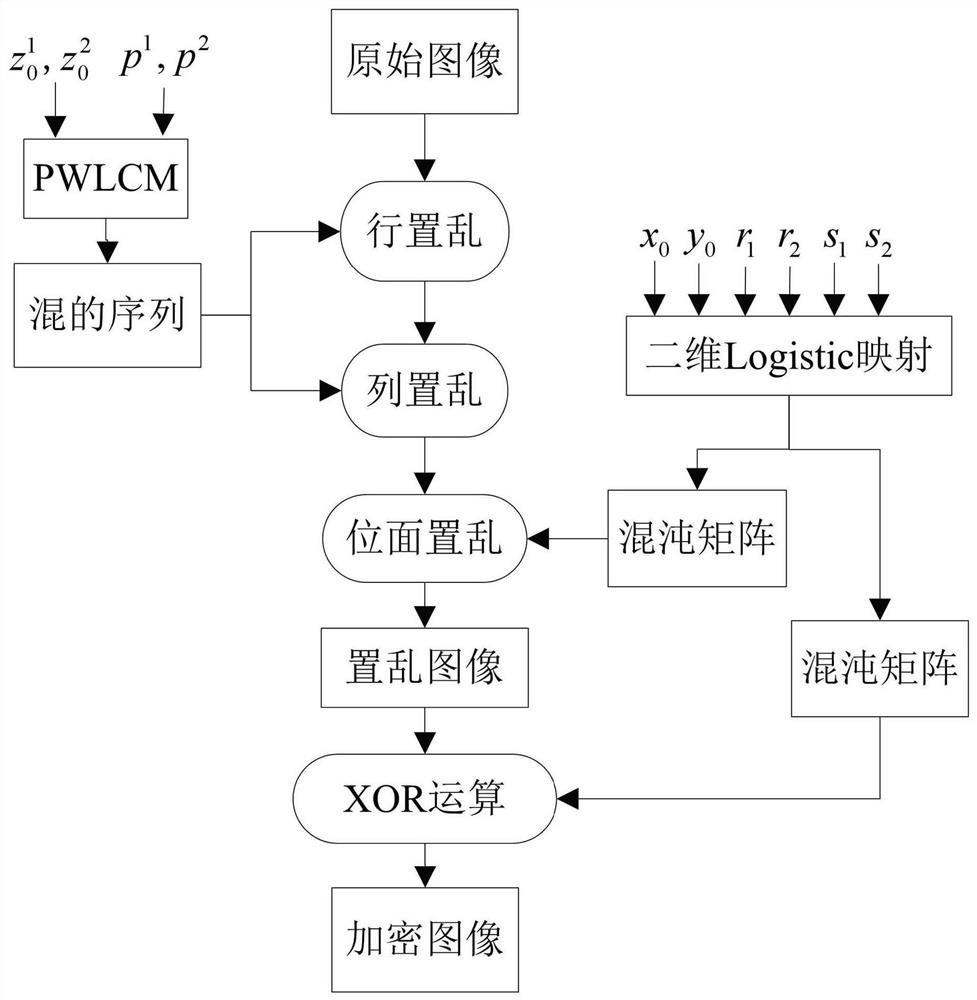
[0035] figure 1 is the encryption flowchart of this method.
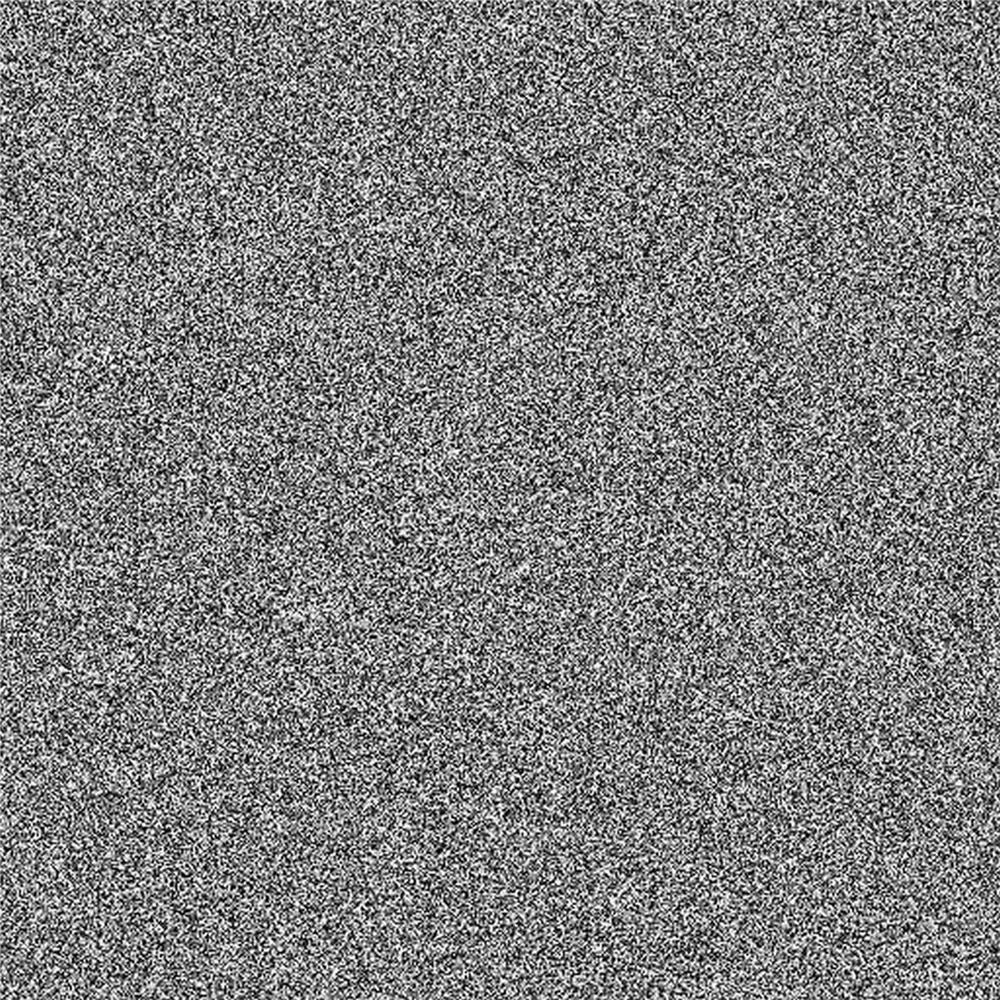
[0036] The programming software used is Matlab R2016a, select figure 2 is the original image, its size is 512×512. Using this method, the detailed process of Alice encrypting the original image is described as follows.
[0037] Step 1: chaotic sequence generation: Let the original image be I ; Select the initial value of PWLCM z 0 1 =0.203921568627451 and parameters p 1 =0.190196078431373, Alice iterates the map 512 times to obtain a chaotic sequence Z 1 ={ z i 1} 512 ;Use formula (1) to calculate R 1 ={ r i 1} 512 ; similarly, she utilizes the initial value of PWLCM z 0 2 =0.239215686274514 and parameters p 2 =0.378431372549021, iterate the map 512 times, and get another chaotic sequence Z 2 ={ z i 2} 512 ;Use formula (2) to calculat...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More