Security function service chain deployment method
A security function and service chain technology, applied in the field of security function service chain deployment, can solve the problem of not considering computing resources and storage resources, only considering bandwidth requirements, etc., to achieve the effect of low network cost
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0033]In order to make the purpose, content, and advantages of the present invention clearer, the specific implementation manners of the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments.
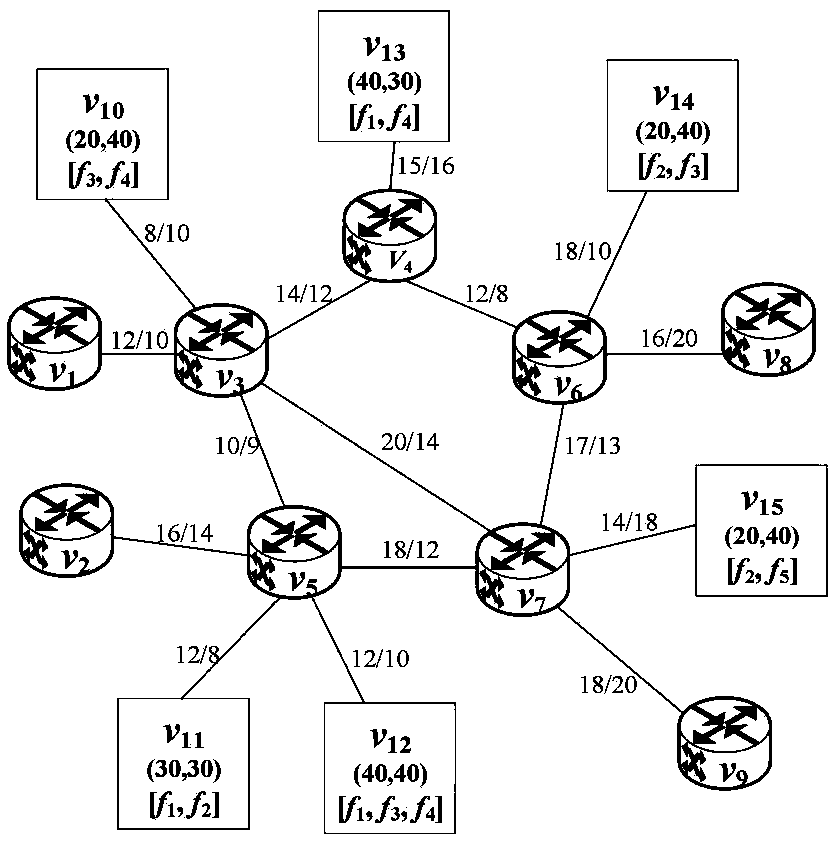
[0034] Unlike existing deployment methods that limit physical nodes to only provide a certain security function, the security function service chain deployment method proposed in the present invention considers the fact that physical nodes can provide multiple security functions, which is more in line with real applications Scenes. Such as image 3 The schematic diagram of the underlying network topology shown, the underlying network topology G S Contains a total of 15 physical nodes, that is, the physical node set V S ={v 1 ,v 2 ,v 3 ,v 4 ,v 5 ,v 6 ,v 7 ,v 8 ,v 9 ,v 10 ,v 11 ,v 12 ,v 13 ,v 14 ,v 15}. Among them, the set of forwarding nodes T S and the security function node set N S Respectively T S...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More