DPA attack method for carrying out fitting by utilizing neural network, system and terminal
A neural network and prediction neural network technology, applied in the DPA attack method and system, terminal field, can solve the problems of insufficiency, limited application scenarios of high-order template attack, etc., to achieve the effect of improving attack efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0070] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
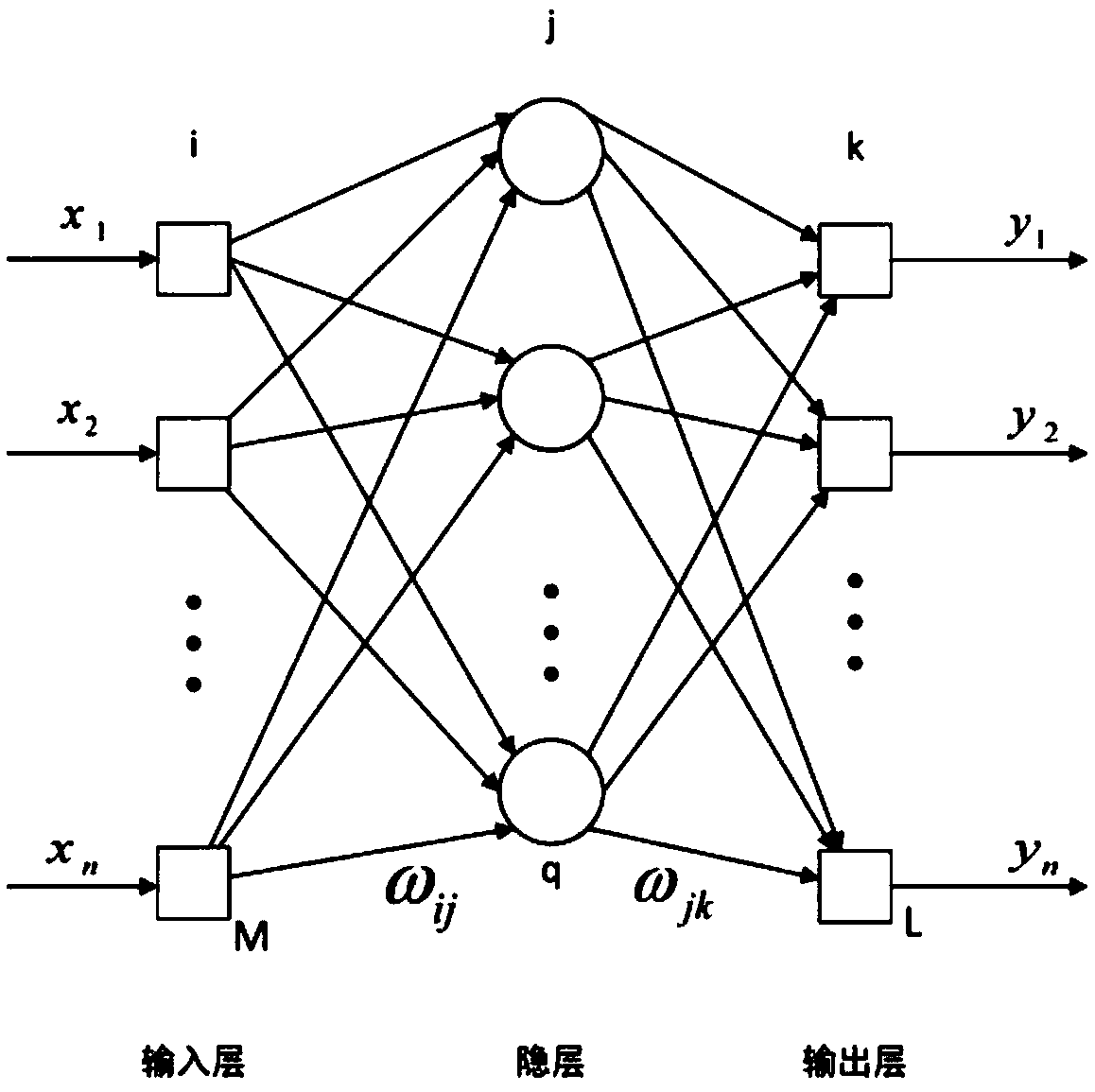
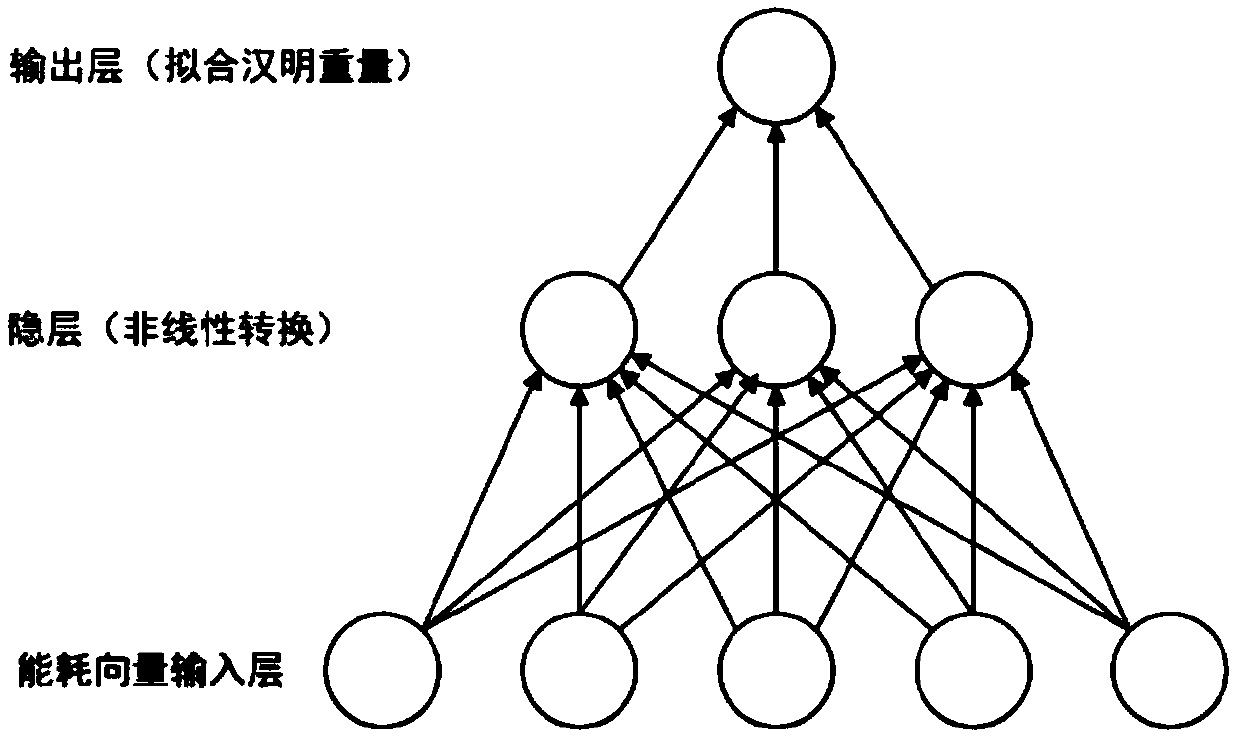
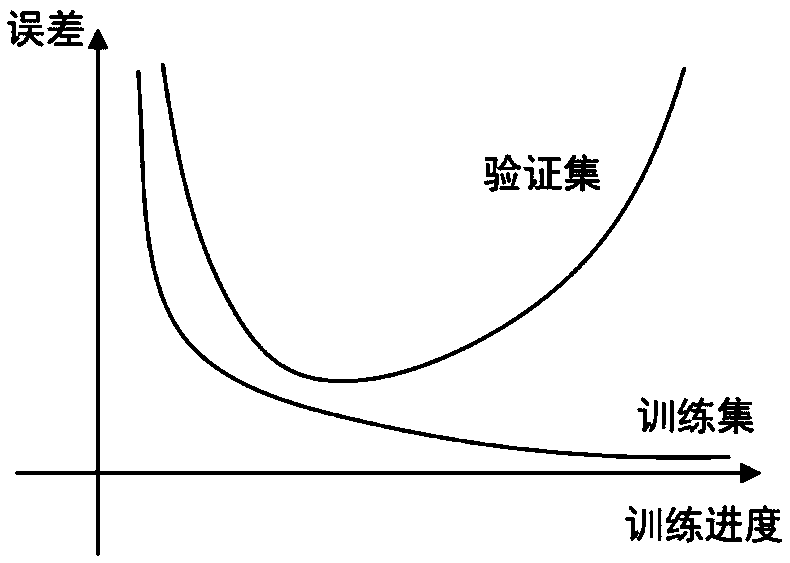
[0071] The invention adopts the neural network to establish the fitting model of the energy consumption and the unmasked intermediate combination value, and attacks based on the correlation coefficient between the fitted unmasked intermediate combination value and the guessed unmasked intermediate combination value.
[0072] This approach eliminates the requirement of having to know the mask during the learning phase, avoids the need for high-order DPA to cross-combine energy, reduces the attack conditions, and improves the attack efficiency. Experiments confirm the feasibility and efficiency of the attack algorithm.
[00...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More