A service calling monitoring method and system in a virtual environment
A virtualization environment and service invocation technology, which is applied in the field of service invocation monitoring in a virtualization environment, can solve the problem that auxiliary modules are no longer trustworthy, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0043] In order to make the above objects, features and advantages of the present invention more comprehensible, the present invention will be further described below through specific embodiments and accompanying drawings.
[0044] This embodiment is an example of a cryptographic operation service call monitoring system in a cloud environment.
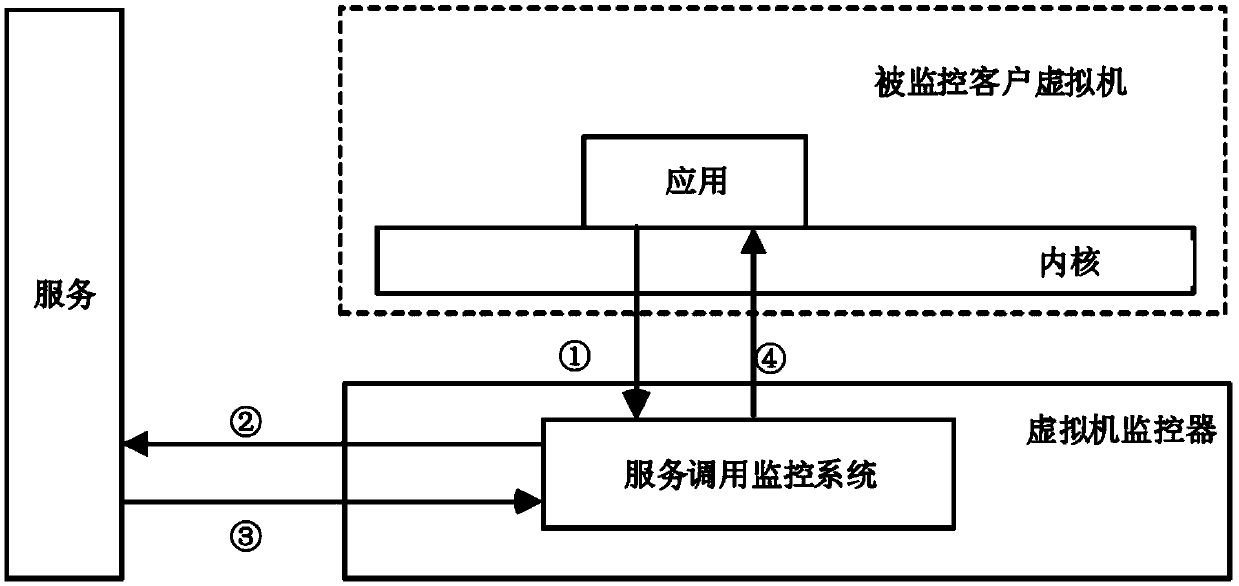
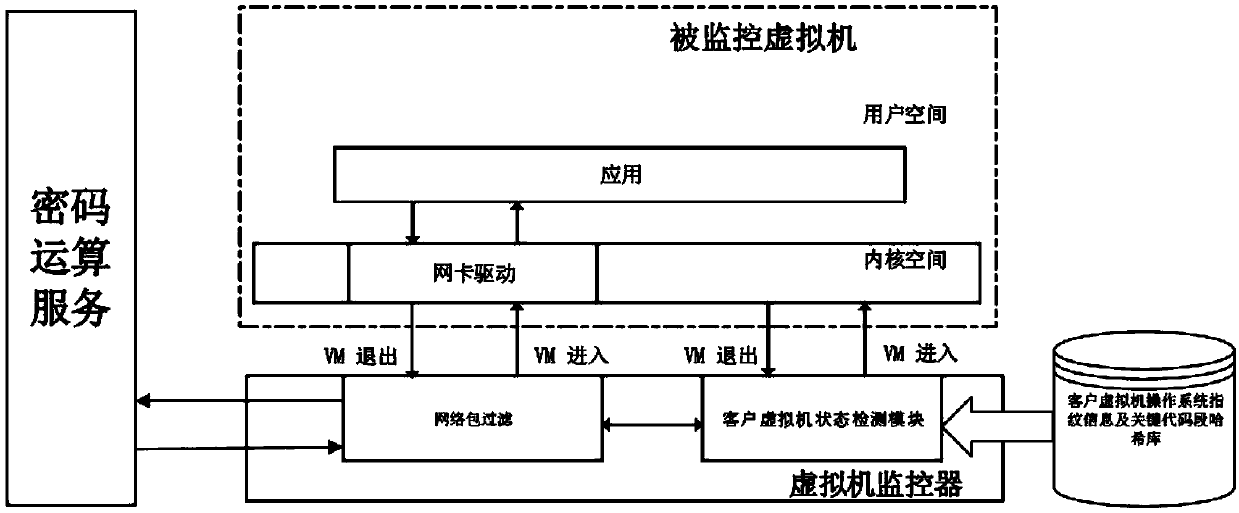
[0045] figure 2 It is a schematic diagram of using the method of the present invention to provide a cryptographic operation service invoking a monitoring service in a virtualized environment. The user subscribes to the key management service (KMS) provided by the cloud service provider, and the KMS service provides services through https. The KMS service is responsible for managing the user's key and providing cryptographic computing services.
[0046] The service call monitoring system in this embodiment is implemented on the QEMU-KVM virtualization platform, and the host computer uses an Intel CPU chip. The detection part of the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More