Database data encryption and decryption method and device, computer equipment and storage medium
An encrypted storage and database technology, applied in the field of information security, can solve the problems of low key distribution efficiency and poor security, and achieve the effect of improving product development and maintenance efficiency, and improving key security and security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
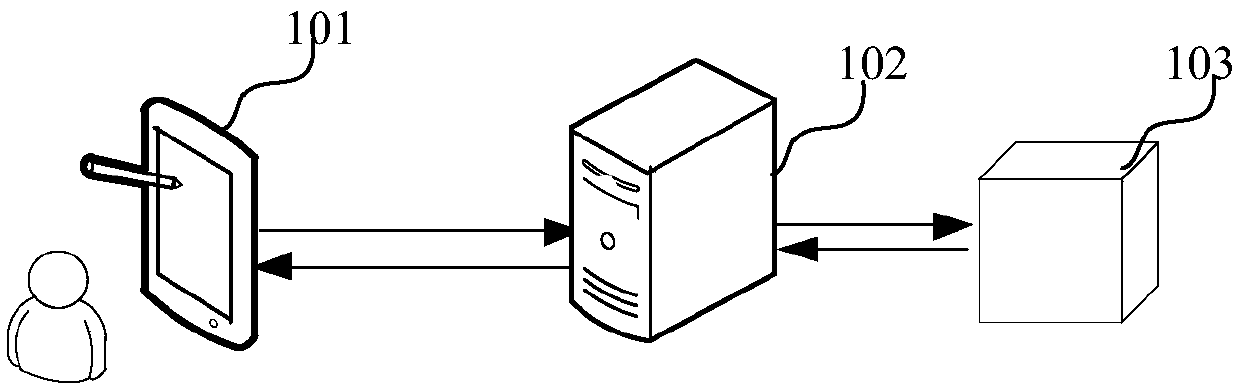
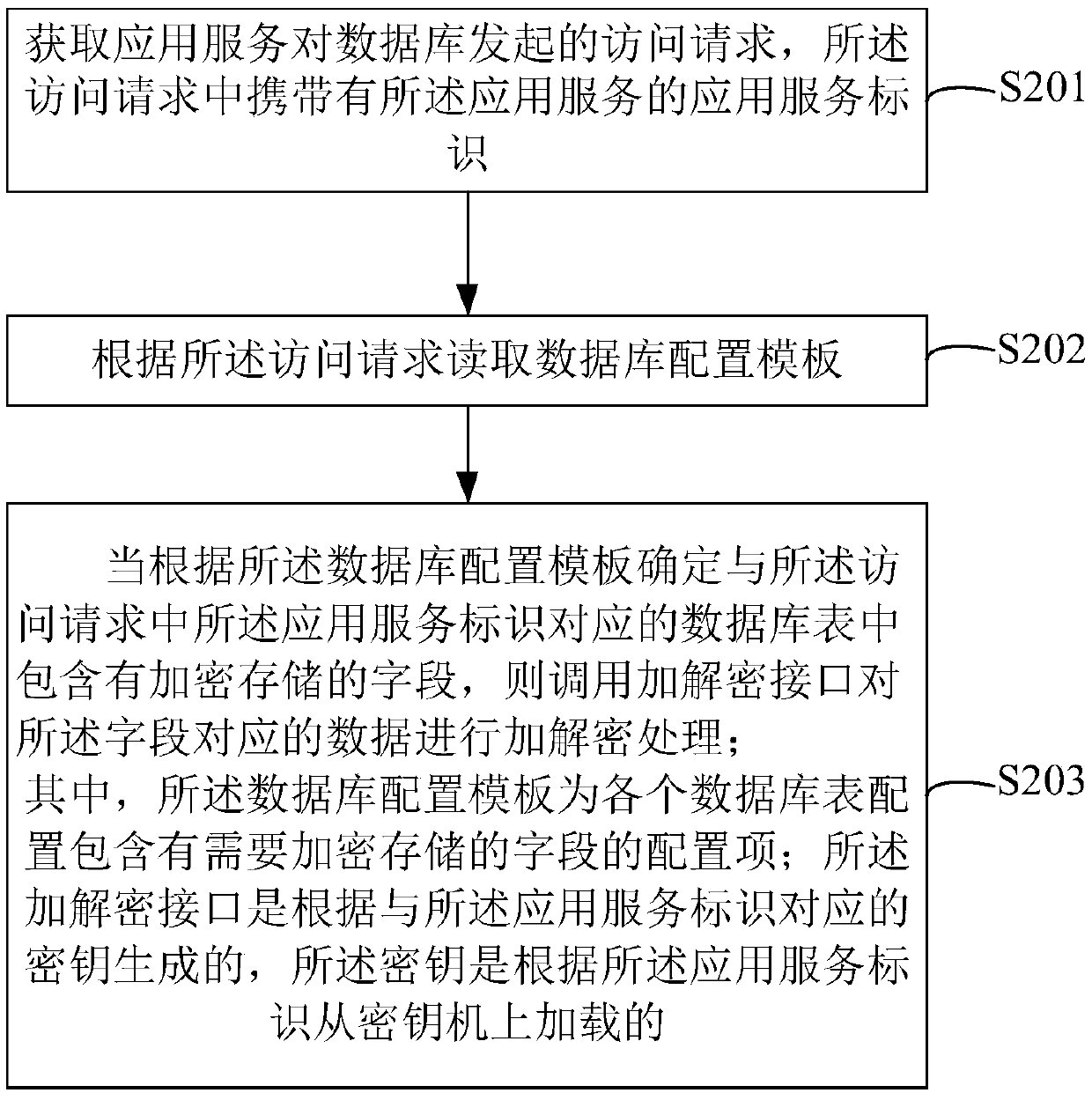
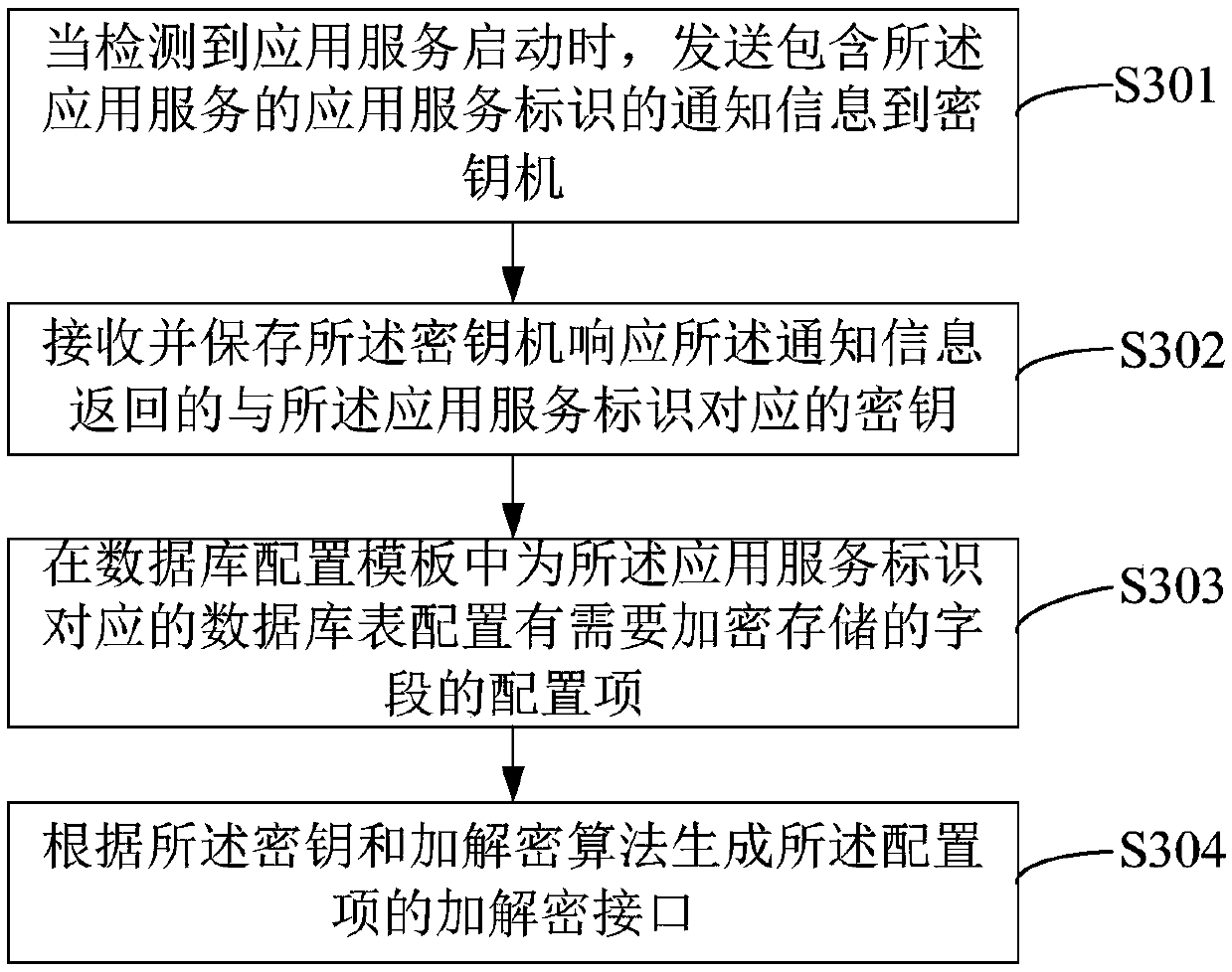
[0055] In order to make the purpose, technical solution and advantages of the present application clearer, the present application will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present application, and are not intended to limit the present application.
[0056]The current method of encrypting sensitive data is usually to first save the key locally on the server. If it is a distributed service, you need to save the key on multiple servers, and then read the key locally from the server to perform encryption operations. In addition, when the application service accesses the database, the usual practice is to directly solidify the encryption and decryption operations for sensitive data in the business code, which will lead to too tight coupling between the business function module and the encryption and decryption function modu...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More