Information hiding method based on big data search and function transformation and robot system
A technology of information hiding and big data, applied in the field of information, can solve the problems of information hiding, such as limited data volume and easy cracking, and achieve the effect of low computing overhead, high security, and guaranteed security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
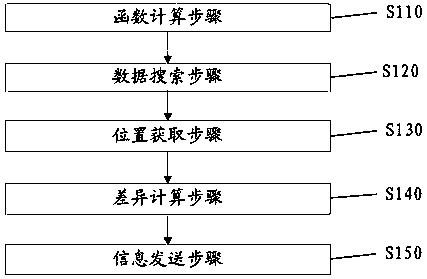
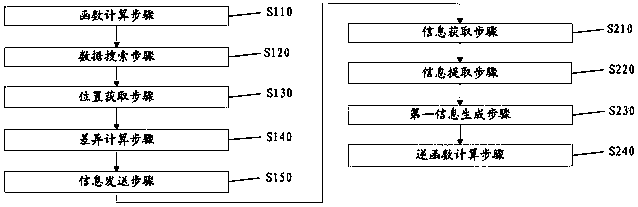
[0078] Embodiment 1 provides an information hiding method, such as figure 1 As shown, the method includes step S110 to step S150.
[0079] Function calculation step S110: Input the secret information x to be hidden into the reversible function f for calculation to obtain the first information y. Secret information refers to information to be hidden, which can be text, passwords, images, graphics or sounds, and so on. Preferably, the reversible function is y=f(x), and the inverse function of the reversible function is x=f -1 (y). The reversible function is, for example, y=5x^3+300, and the inverse function of the reversible function is, for example, x=((y-300) / 5)^(1 / 3). Beneficial effects: the secret information is transformed into the first information through the reversible function, so that even if the first information is deciphered, the secret information cannot be recovered, further improving the security and difficulty of deciphering the secret information. Generally...
Embodiment 2
[0085] Embodiment 2 provides a preferred information hiding method. According to the information hiding method described in Embodiment 1, combined with big data, the function calculation step S110 specifically includes step S111; the data search step S120 specifically includes step S121; the location acquisition step S130 specifically includes Including step S131, the difference calculation step S140 specifically includes step S141.
[0086] Multi-function calculation step S111: Divide the secret information x into multiple parts of secret information x1, x2, ..., xm (m is the number of divisions), input the reversible function f for calculation, and obtain a plurality of first information y1, y2, ..., ym. Preferably, the secret information x is divided into m parts with equal length as a character string, and becomes x1, x2, . . . , xm. Preferably, record the sequence numbers of each part of the secret information after segmentation, and add the sequence numbers to the heade...
Embodiment 3
[0091] Embodiment 3 provides a preferred information hiding method. According to the information hiding method described in Embodiment 2, the reversible functions are different reversible functions.
[0092] The multi-function calculation step S111 is specifically: divide the secret information into multiple parts of secret information x1, x2, ..., xm, respectively input multiple reversible functions f1, f2, ..., fm for calculation, and obtain multiple first - Information y1, y2, . . . , ym. Preferably, y1=f1(x1), y2=f2(x2), . . . ym=fm(xm).
[0093] The main beneficial effects of Embodiment 3: different first information converted from different parts of the secret information are converted using different reversible functions, so that even if some of the reversible functions are deciphered, all the first information cannot be recovered, and thus cannot The secret information is recovered, further improving the security and difficulty of deciphering the secret information. ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More