Computer interface security device for preventing data from being stolen
A security device and computer technology, applied in the protection of internal/peripheral computer components, etc., can solve the problems of data theft, data theft and leakage, and normal data export by users, so as to improve security and secure data security protection. stable effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
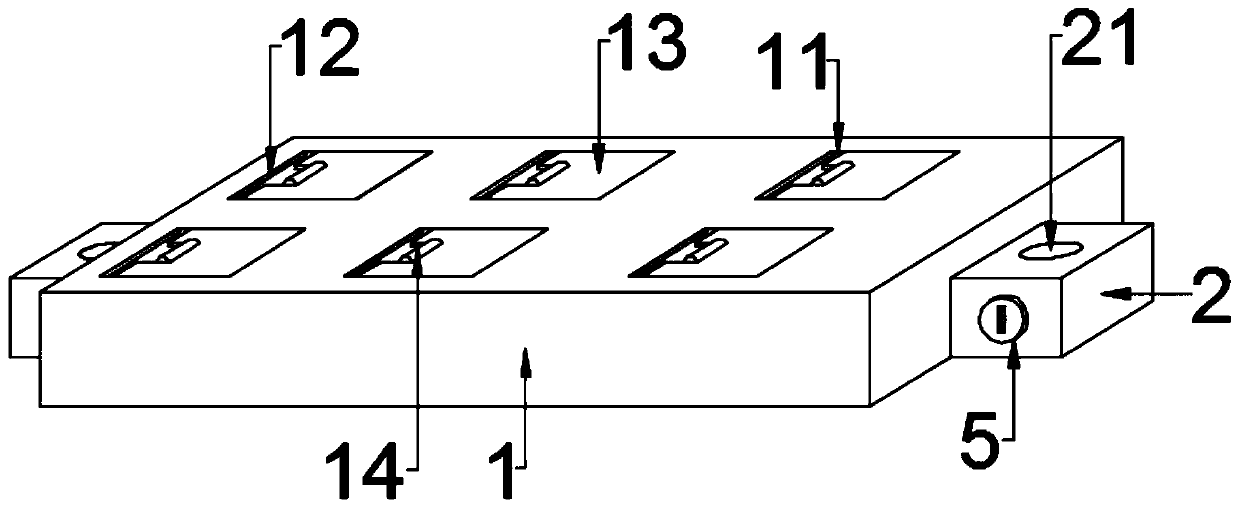
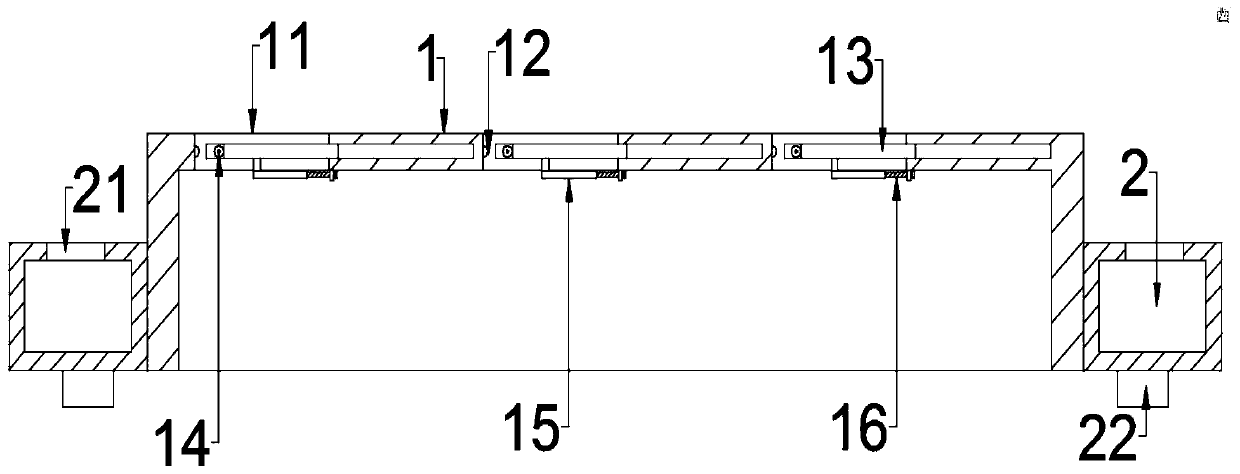
[0023] see Figures 1 to 2 , in the embodiment of the present invention, a computer interface security device for preventing data from being stolen includes a casing 1 and a limit pad 2, and the casing 1 is provided with a plurality of sets of wire holes for cables to pass through. 11. The wire setting hole 11 is provided with a movement restriction structure, and the movement restriction structure is controlled to move by the adjustment structure located on the lower side of the cover shell 1, and the limit pads 2 are symmetrically and fixedly arranged on both sides of the cover shell 1. , and the lower end of the limiting pad 2 is fixedly connected with a positioning protrusion 22 .
[0024] The specific position and quantity of the wire setting hole 11 can be selected according to different objects, which is very simple and easy to operate in the production and processing of this product in the field. The inner side of the opening of the wire setting hole 11 is horizontally...
Embodiment 2
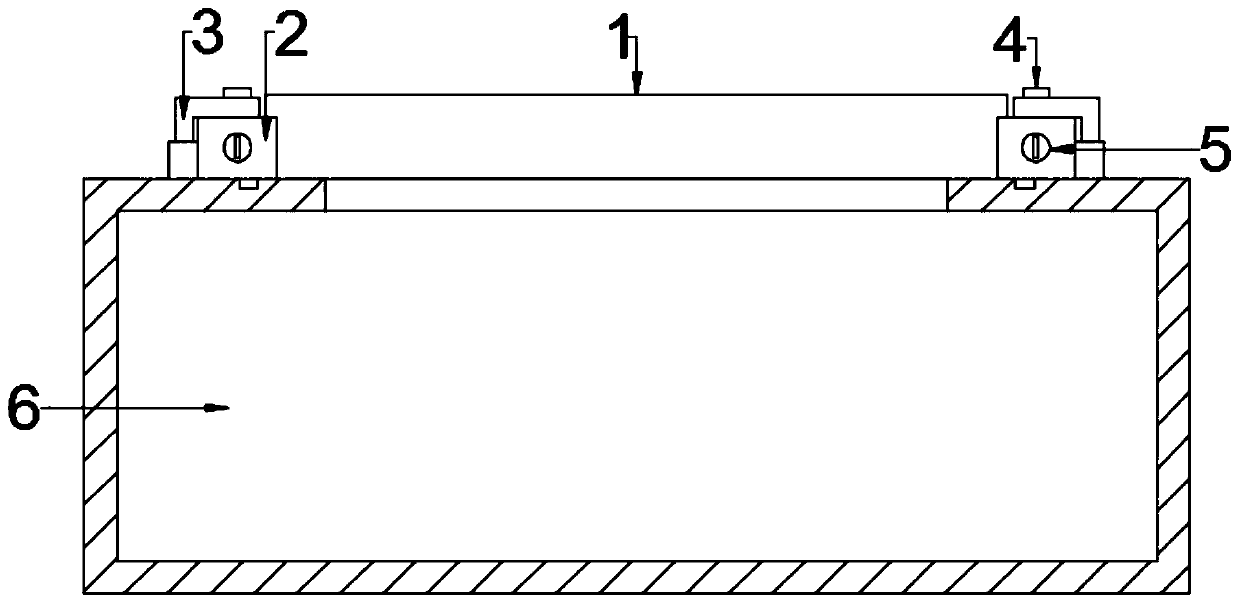
[0028] see Figures 3 to 5 , in the embodiment of the present invention, a computer interface security device for preventing data theft, on the basis of Embodiment 1, the casing 1 is movably assembled and arranged on the upper end of the main chassis 6 through the positioning protrusion 22, and the casing 1 and the data interface on the main box 6 are arranged opposite to each other, and the main box 6 is also connected with a limit clip 3 that is movably matched with the limit pad 2, and the limit clip 3 includes fixed on the main box 6. The bearing sleeve on the upper end and the "L"-shaped clip connected to the upper end of the bearing sleeve, one end of the "L"-shaped clip is connected with the bearing sleeve in rotation, and the other end is bent and movably attached to the upper end of the limit pad 2, so The upper end of the "L"-shaped clip in the limit clip 3 is provided with a positioning pin 4 that is slidably adapted to the positioning hole 21. Limit pin 5.
[002...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More