Image encryption method based on improved Logistic mapping
An encryption method and image technology, applied in the direction of secure communication, instruments, and digital transmission systems through chaotic signals, can solve the problems of not being well verified, random sequences not obeying uniform distribution, etc., and achieve key space increase, random Sexual Enhancement Effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
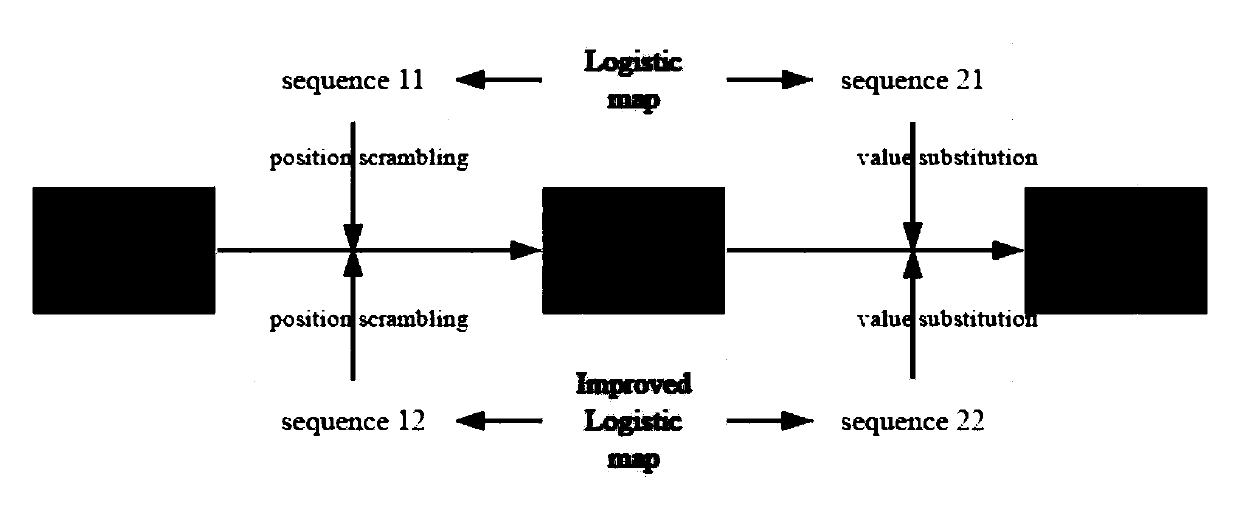
[0090] An image encryption method that simply scrambles image pixel positions and replaces pixel values. The encryption principle is as follows: figure 1 shown. The method consists of an encrypted part of the image and a decrypted part.
[0091] (1) The encrypted part of the image:
[0092] In the encryption process, the first pair of random sequences generated by the traditional Logistic mapping and the improved Logistic mapping are used to scramble the pixel positions of the image to be encrypted to realize the first encryption; then the second pair of random sequences generated by using the The pixel values of the image encrypted for the first time are subjected to XOR operation to realize the replacement of pixel values and obtain the final encrypted image.
[0093] (2) The decrypted part of the image:
[0094] In the decryption process, first use the second pair of random sequences to perform XOR operation with the encrypted image respectively to restore the initia...
Embodiment 2
[0097] Combine below figure 1 The design principle introduces the scheme in embodiment 1 in detail, see the following description for details:
[0098] In order to verify the validity and feasibility of the improved Logistic mapping scheme in detail, a simple image scrambling algorithm is designed combining the improved Logistic mapping scheme and the traditional Logistic mapping respectively. The block diagram of its encryption principle is as follows: figure 1 As shown, the encryption method consists of the encrypted part of the image and the decrypted part of the image. The specific implementation of these two parts will be described in detail below.
[0099] (1) The encrypted part of the image:
[0100] 1) First, the first pair of random sequences seq11 and seq12 generated by traditional Logistic mapping and improved Logistic mapping are used to scramble the pixel positions of image I to be encrypted respectively;
[0101]
[0102]
[0103] In the formula, seq11 ...
Embodiment 3
[0116] Below in conjunction with specific accompanying drawing, the scheme in embodiment 1 and 2 is carried out feasibility verification, see the following description for details:
[0117] The Lyapunov exponent distribution figure of the improved Logistic mapping proposed in traditional Logistic mapping and the present invention is as figure 2 (a) and figure 2 (b)-(d) shown.
[0118] image 3 (a) and image 3 (b) Distribution histograms of random sequences generated for traditional and improved logistic maps, respectively. Compared with the traditional Logistic mapping, the random sequence generated by the improved Logistic mapping satisfies the uniform distribution.
[0119] Adopt the first scheme among the present invention and the second scheme to original image (as Figure 4 (a) After encryption, the obtained encrypted image is as follows Figure 4 (b) and Figure 4 (c) shown.
[0120] Depend on Figure 5 (b) It can be seen that the second scheme is obviously str...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More