Malicious mining program active defense method and device
A technology of active defense and program, applied in the field of network security, can solve the problem of active defense against malicious mining programs, and achieve the effect of ensuring network security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
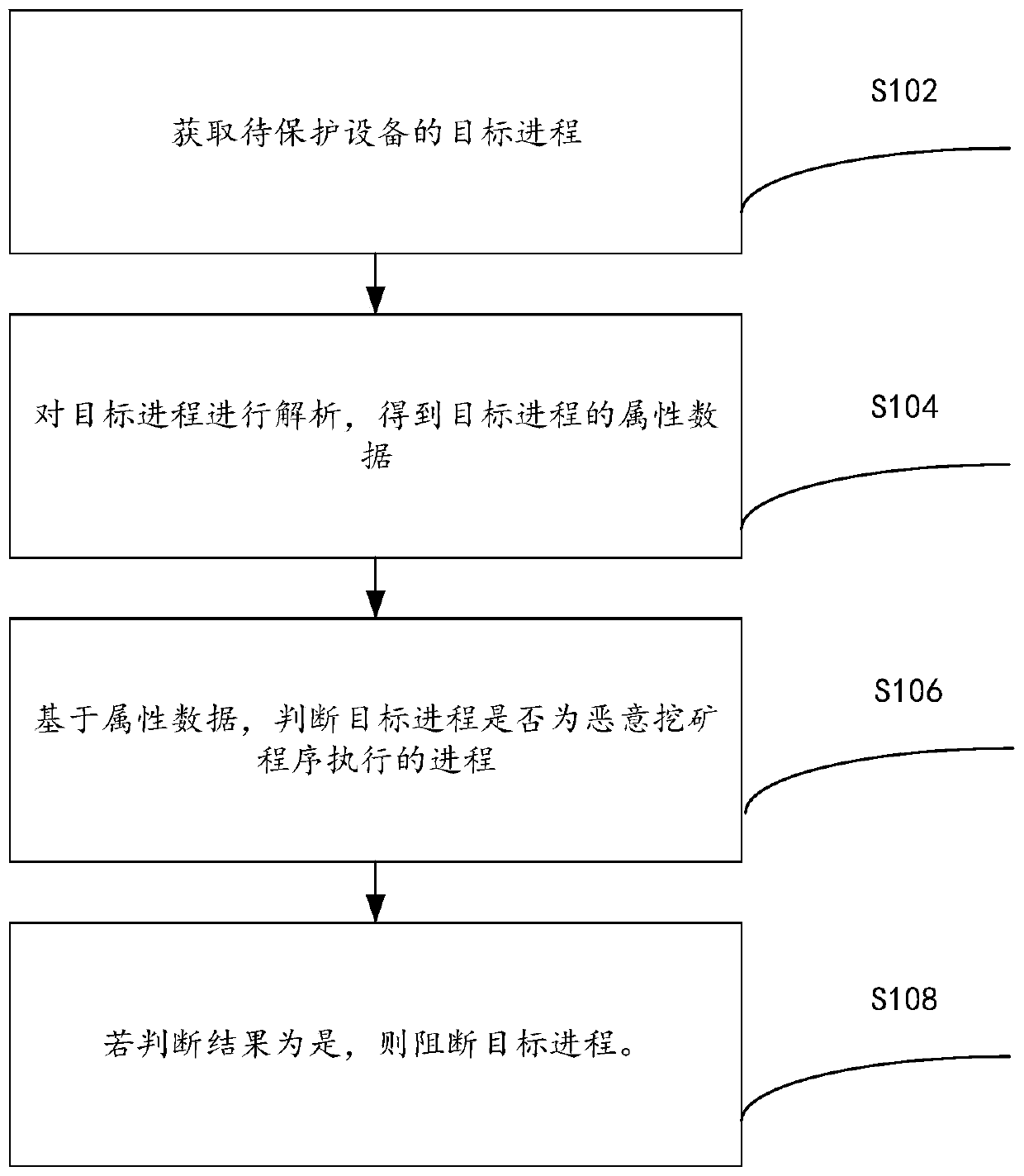
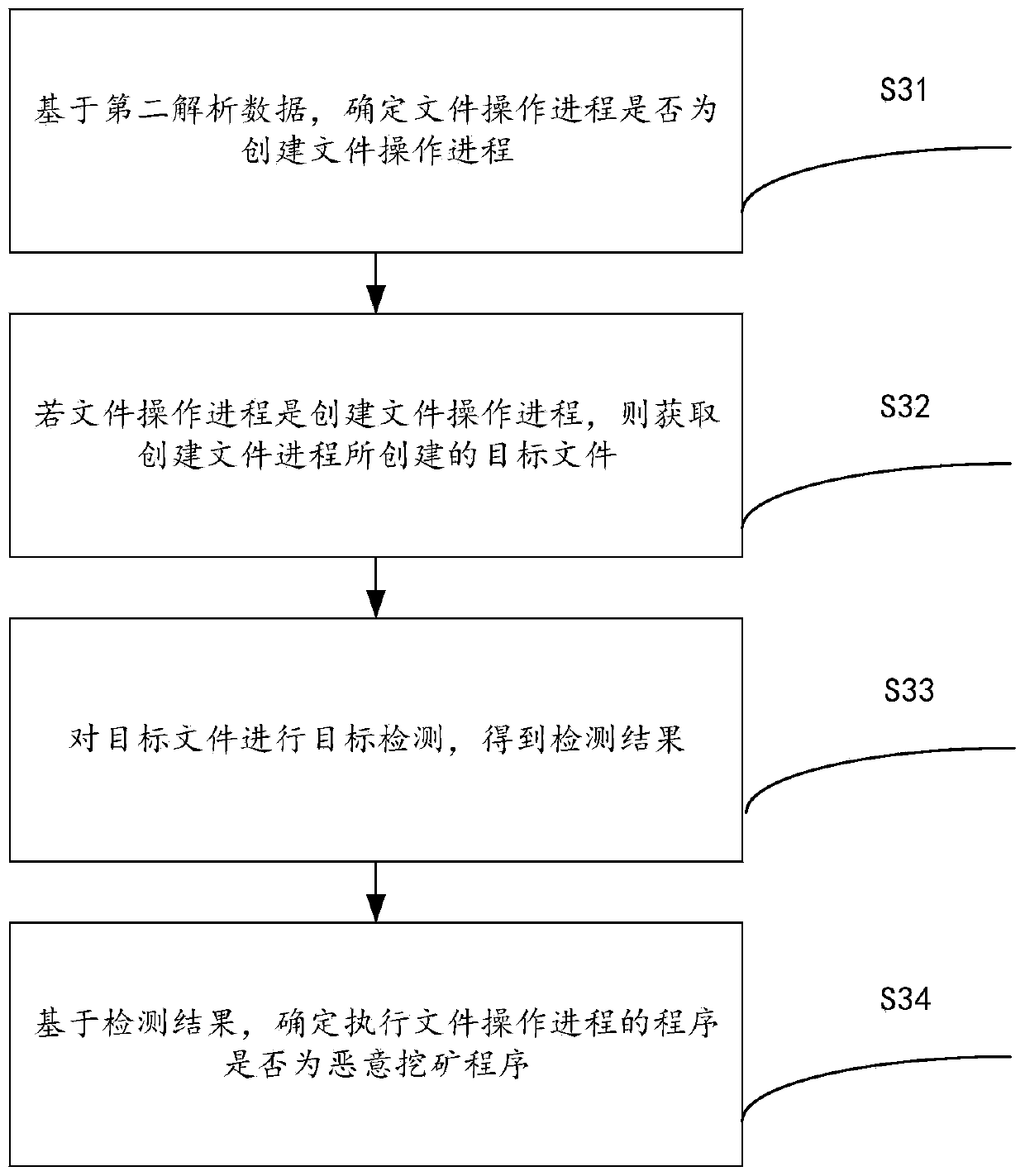
[0027] According to an embodiment of the present invention, an embodiment of a method for actively defending malicious mining programs is provided. It should be noted that the steps shown in the flow charts of the accompanying drawings can be executed in a computer system such as a set of computer-executable instructions , and, although a logical order is shown in the flowcharts, in some cases the steps shown or described may be performed in an order different from that shown or described herein.
[0028]Now that the digital currency market is booming, the prices of various virtual currencies continue to rise, and they are being targeted by many black production gangs. Black industry gangs invade victims' machines through illegal methods such as illegal intrusion and system loopholes, and maliciously deploy mining programs to make profits. Malicious mining programs will occupy valuable resources such as the hardware and network of the victim's machine, and some malicious minin...
Embodiment 2
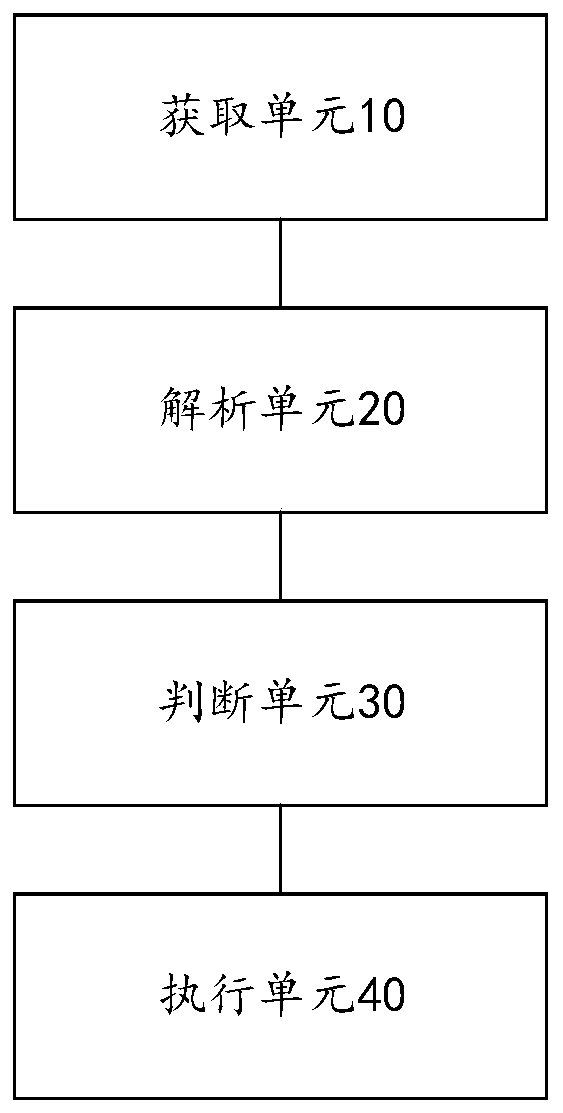
[0086] The present invention also provides an active defense device for malicious mining programs, which is used to implement the active defense method for malicious mining programs provided by the above-mentioned content of the embodiments of the present invention. The following is the malicious mining program provided by the embodiments of the present invention Specific introduction of the device for program active defense.
[0087] Such as image 3 As shown, the above-mentioned active defense device for malicious mining programs includes: an acquisition unit 10 , an analysis unit 20 , a judgment unit 30 and an execution unit 40 .
[0088] The obtaining unit 10 is used to obtain the target process of the device to be protected;
[0089] The parsing unit 20 is configured to parse the target process to obtain attribute data of the target process;
[0090] The judging unit 30 is configured to judge whether the target process is a process executed by a malicious mining program...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More