A security verification method and router
A security verification and router technology, applied in the field of security verification methods and routers, can solve problems such as low security and achieve the effect of ensuring security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
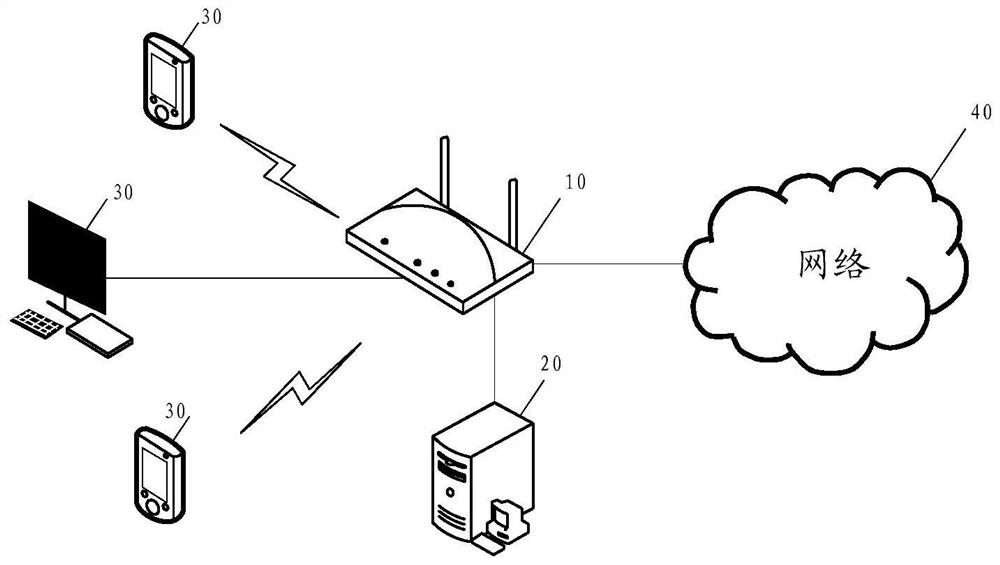
[0045] Image 6 A schematic flow diagram of a security verification method provided in the embodiment of this application, which is applied to such as figure 1 In the network communication system shown. The safety verification method specifically includes the following steps:
[0046] S601. The router obtains the first list.
[0047] Specifically, the transceiver module 11 of the router 10 acquires the first list.
[0048] The router 10 or the server 20 may randomly generate a preset number of first IP addresses according to user instructions or preset configurations, and establish correspondence between the preset number of first IP addresses and the preset number of user identifiers. By randomly generating the first IP address and establishing a corresponding relationship with the user ID, the IP addresses corresponding to the user ID in the first list used each time the security verification method is executed are different, avoiding fixed IP addresses and user IDs Risk...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More