Method and device for controlling process access to files
A control method and process technology, applied in the field of system security, can solve problems such as unrealization
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0048] While the invention may be embodied in various forms, some exemplary and non-limiting embodiments are shown in the drawings and will be described below, it should be understood that the disclosure is to be considered as exemplary and not It is intended that the invention be limited to the specific embodiments described.
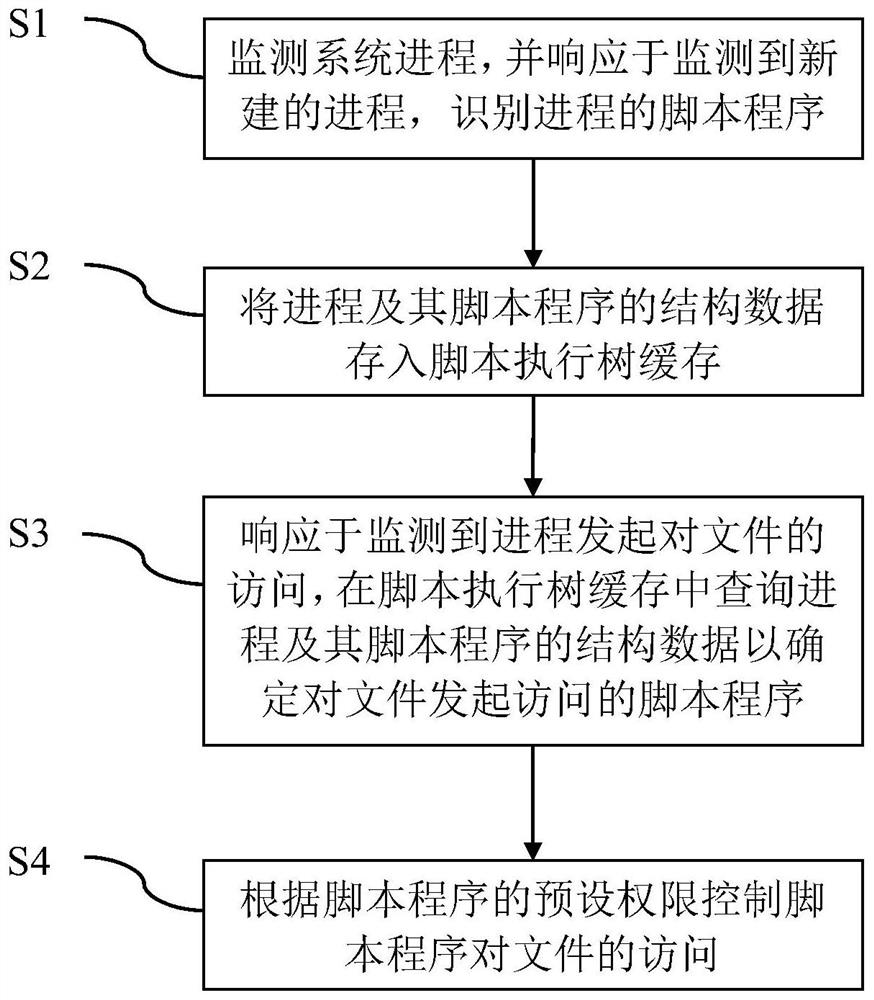
[0049] figure 1 A schematic block diagram of an embodiment of the method for controlling process access to files according to the present invention is shown. In the embodiment shown in the figure, the method at least includes the following steps:
[0050] S1: monitor the system process, and identify the script program of the process in response to the monitoring of a newly created process;
[0051] S2: Store the structural data of the process and its script program into the script execution tree cache;
[0052] S3: In response to detecting that the process initiates access to the file, query the structural data of the process and its script program ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More