Malicious URL detection method based on URL imaging technology
A detection method and malicious technology, applied in the field of URL recognition, to achieve good image representation, accurate recognition results, and accelerated gradient update
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0046] The specific embodiments of the present invention are described below so that those skilled in the art can understand the present invention, but it should be clear that the present invention is not limited to the scope of the specific embodiments. For those of ordinary skill in the art, as long as various changes Within the spirit and scope of the present invention defined and determined by the appended claims, these changes are obvious, and all inventions and creations using the concept of the present invention are included in the protection list.
[0047] Embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings.
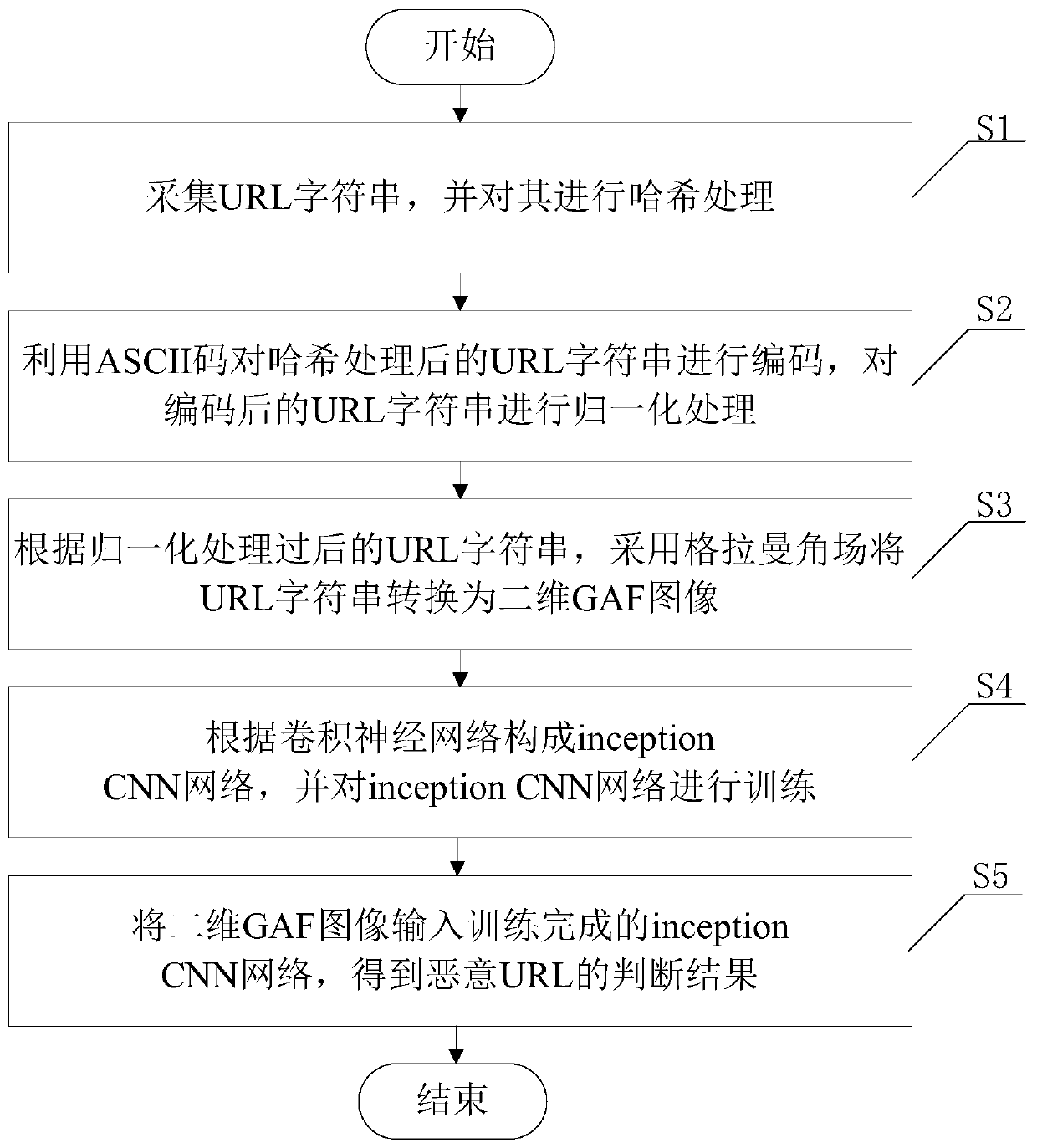
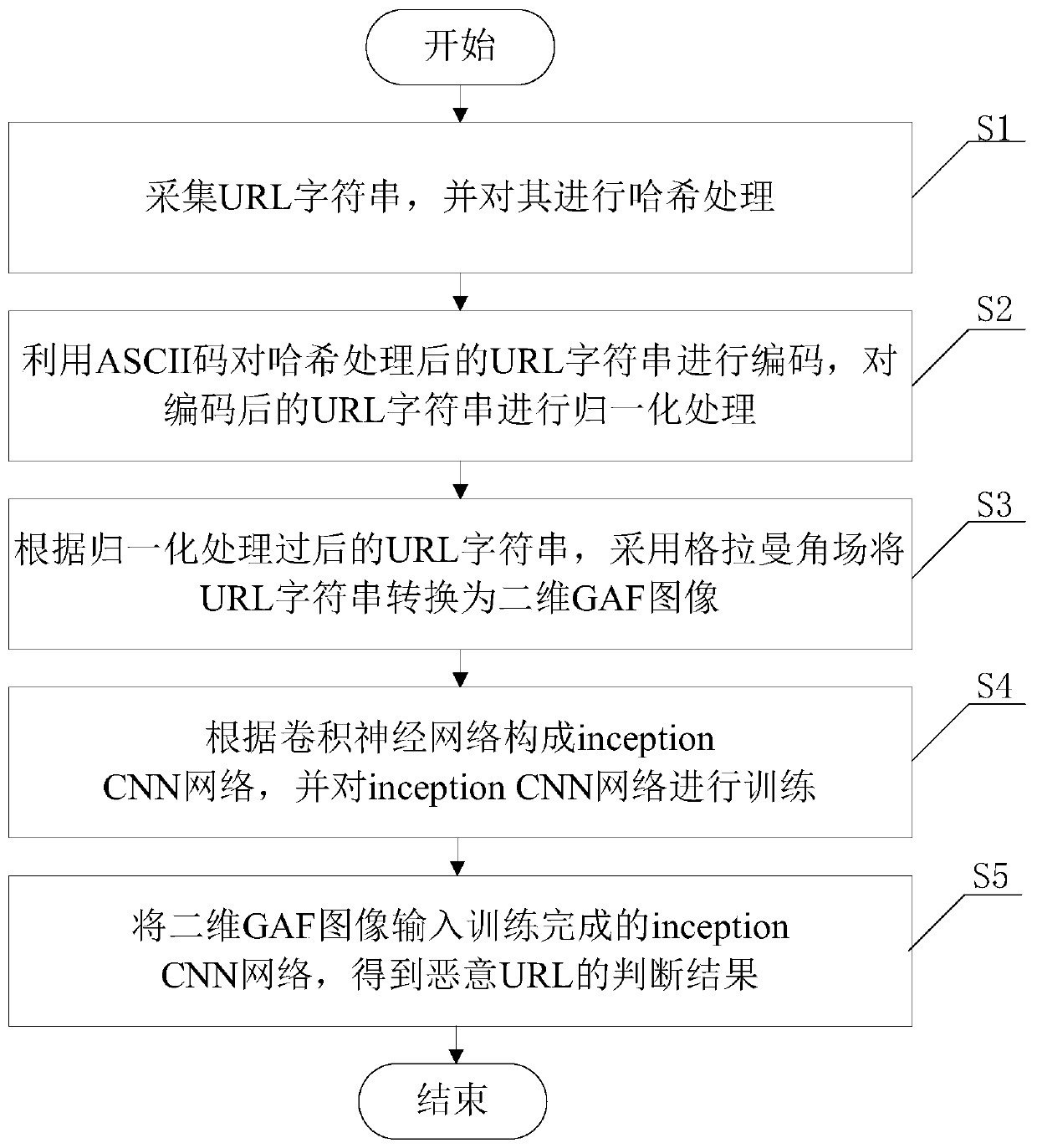
[0048] Such as figure 1 As shown, a malicious URL detection method based on URL imaging technology includes the following steps:
[0049] S1. Collecting URL strings and hashing them;
[0050]S2. Encode the hashed URL string by using the ASCII code, and normalize the encoded URL string;
[0051] S...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More