An access control method, device, equipment, and medium
A technology for access control and volume access, applied in the direction of instruments, input/output to record carriers, computing, etc., can solve problems such as disconnection of other volumes, data loss, and normal operation of business, and achieve the effect of avoiding data loss
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
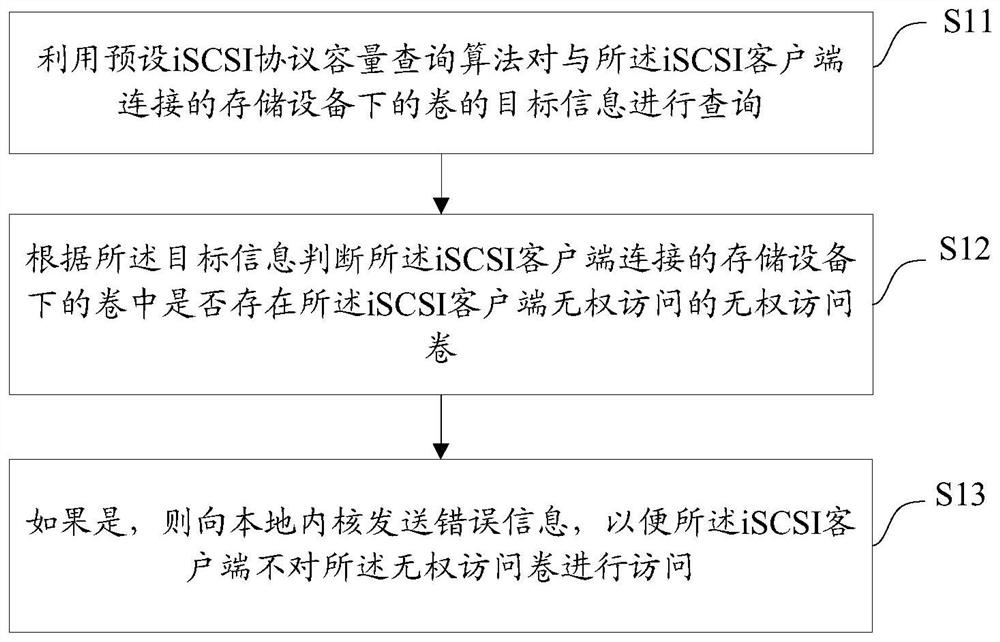
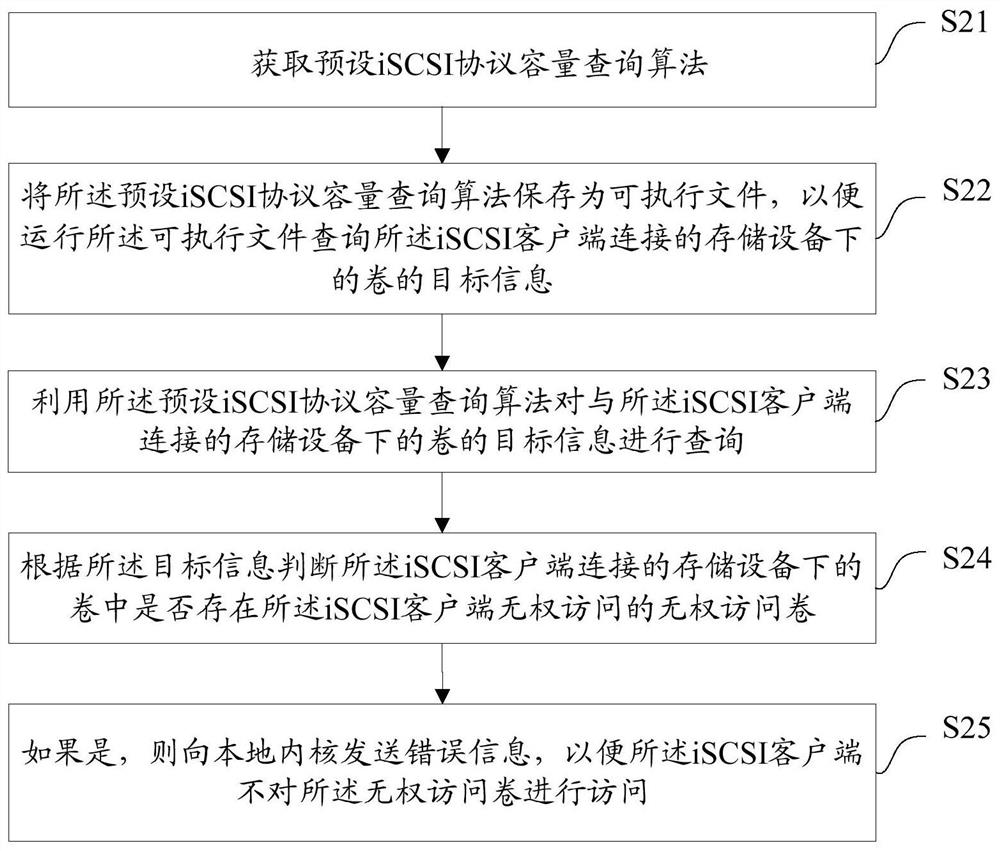
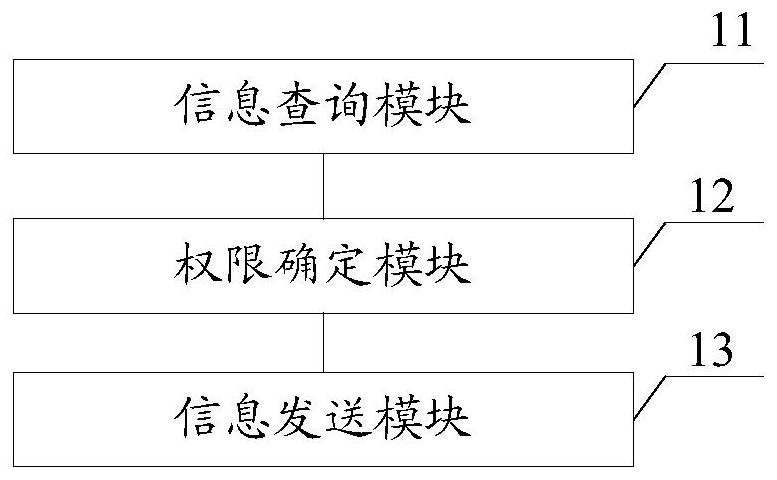
[0042] The technical solutions in the embodiments of the present application will be clearly and completely described below with reference to the drawings in the embodiments of the present application. Obviously, the described embodiments are only a part of the embodiments of the present application, rather than all the embodiments. Based on the embodiments in this application, all other embodiments obtained by those of ordinary skill in the art without creative efforts shall fall within the protection scope of this application.
[0043] At present, the access control authority of the volume connected to the storage device can only be judged when the client logs in. If you want to disconnect the access control authority of a client after the login is completed, you must log out / login again. Affects other volumes on the connected storage device, causing other volumes to be disconnected, affecting the normal operation of services and causing data loss. In view of this, the prese...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More