Information synchronization management method and device, computer system and readable storage medium
A technology of information synchronization and management methods, which is applied in the field of big data data processing, can solve problems such as the difficulty of smooth operation of authentication servers, and achieve the effect of eliminating the risk of information tampering and ensuring smoothness
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
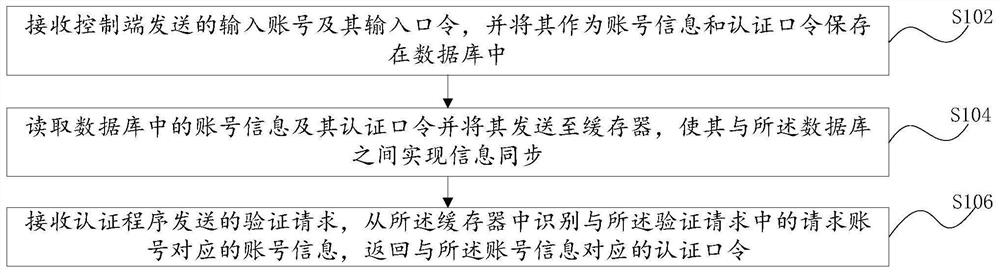
[0039] see figure 1 , an information synchronization management method of this embodiment, applied to an authentication server with an authentication program, including:
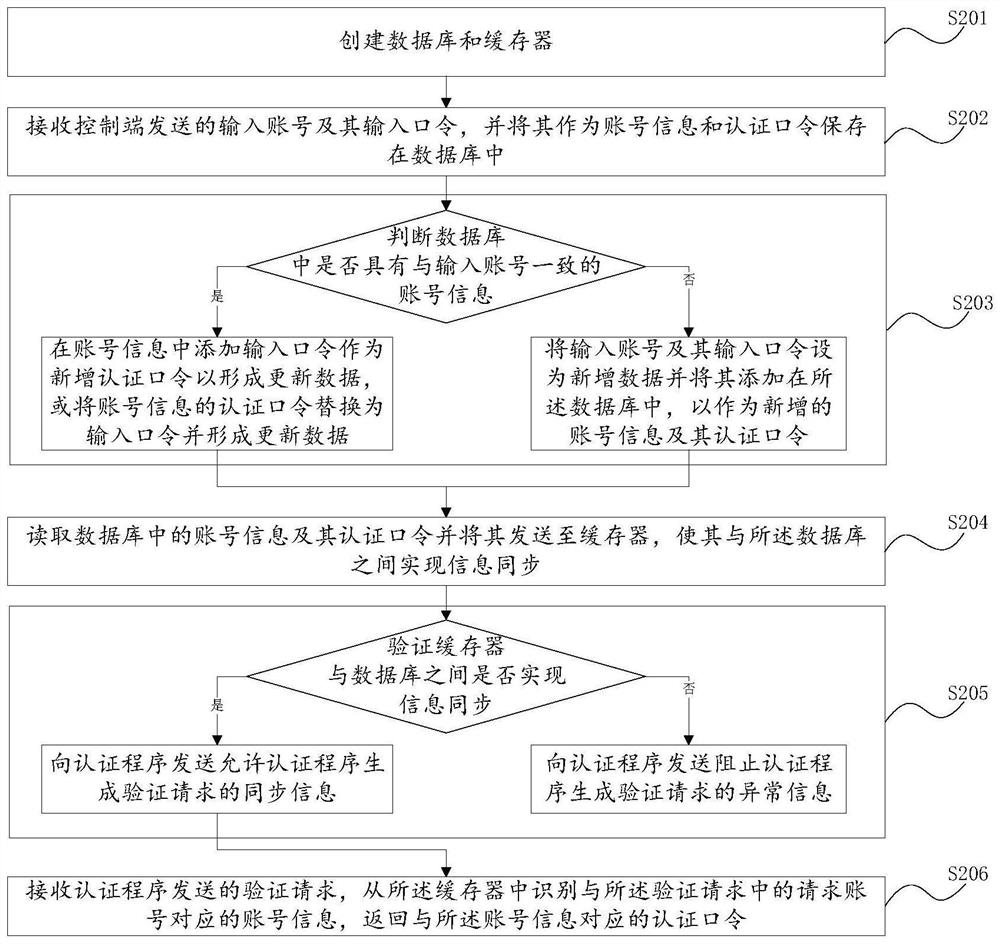
[0040] S102: Receive the input account number and input password sent by the control terminal, and store them in the database as account information and authentication password;
[0041] S104: Read the account information and its authentication password in the database and send it to the cache, so as to realize information synchronization with the database;
[0042] S106: Receive a verification request sent by the verification program, identify account information corresponding to the requested account in the verification request from the cache, and return an authentication password corresponding to the account information.
[0043]In order to solve the problems in the background technology, by saving the account information and its authentication password in the database, once the authenticator (such as: t...
Embodiment 2
[0046] This embodiment is a specific application scenario of the first embodiment above. Through this embodiment, the method provided by the present invention can be described more clearly and specifically.
[0047] In the following, the method provided in this embodiment will be specifically described by taking, as an example, the information synchronization of the buffer and the database and the identification of the returned authentication password in a service authentication server running an information synchronization management method and an authentication program. . It should be noted that this embodiment is only exemplary, and does not limit the protection scope of the embodiment of the present invention.
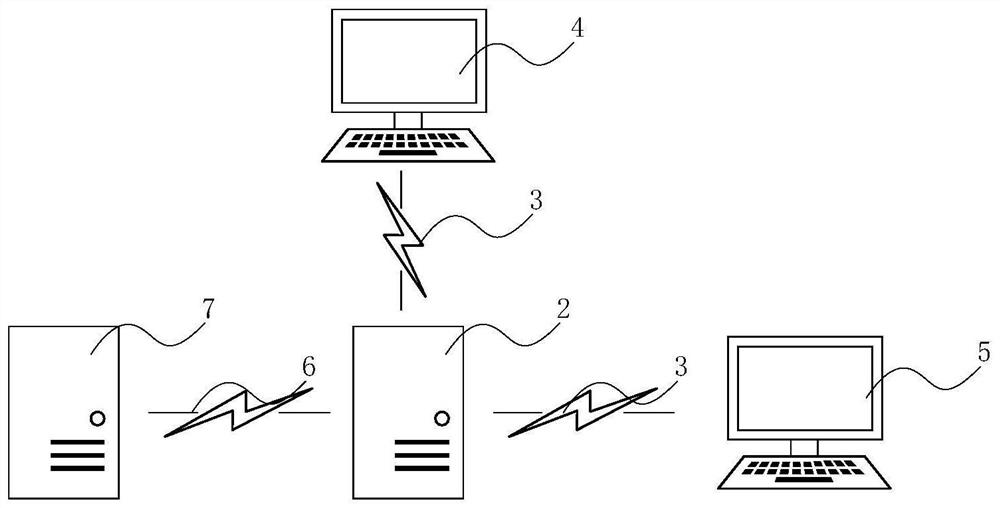
[0048] figure 2 A schematic diagram of an environment application of the information synchronization management method according to Embodiment 2 of the present application is schematically shown.
[0049] In an exemplary embodiment, the authentication server 2 w...
Embodiment 3
[0091] see Figure 4 , an information synchronization management device 1 of this embodiment is applied in an authentication server with an authentication program, including:
[0092] The input module 12 is used to receive the input account number and the input password thereof sent by the control terminal, and store it in a preset database as account information and authentication password;
[0093] Synchronization module 14, is used for reading the account information and its authentication password in the database and sending it to the cache memory, so that it realizes information synchronization with the database;
[0094] The output module 16 is configured to receive the verification request sent by the verification program, identify the account information corresponding to the requested account in the verification request from the cache, and return the verification password corresponding to the account information.
[0095] Optionally, the information synchronization ma...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More