Cryptographic protocol verification method
A cryptographic protocol and verification method technology, applied in transmission systems, electrical components, etc., can solve problems such as incorrect proof results, inaccurate target models, and difficulties
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0109] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0110] Aiming at the problems existing in the prior art, the present invention provides a cryptographic protocol verification method. The present invention will be described in detail below in conjunction with the accompanying drawings.
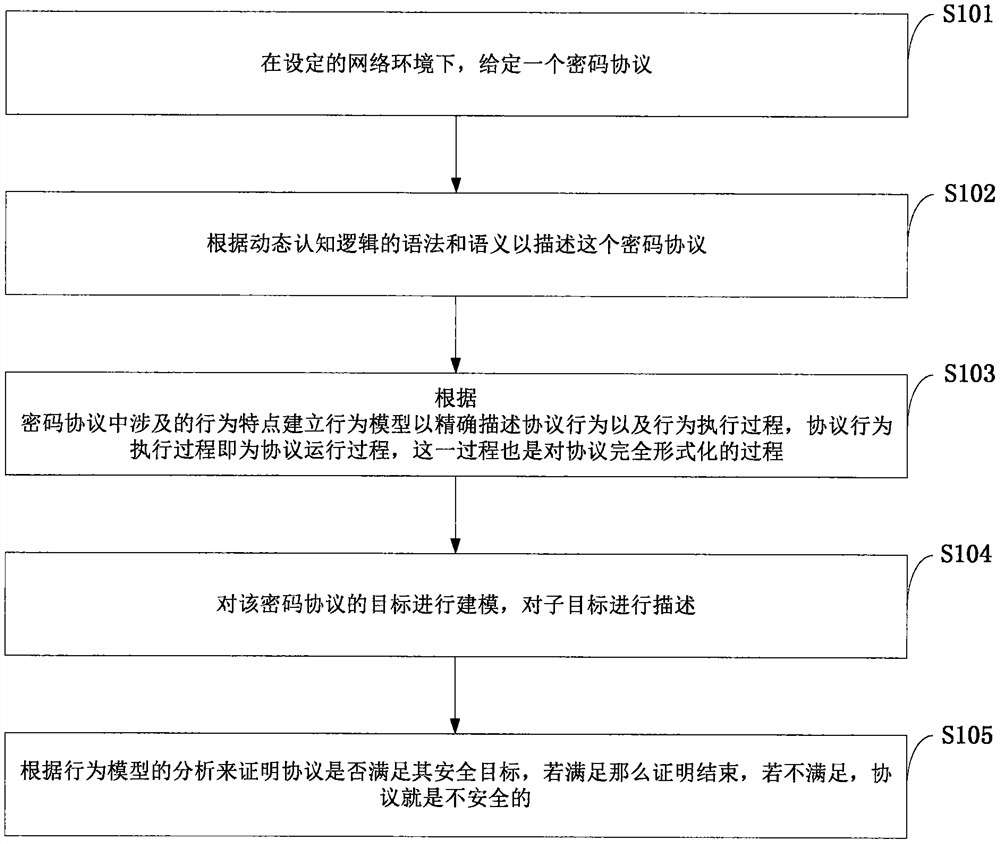
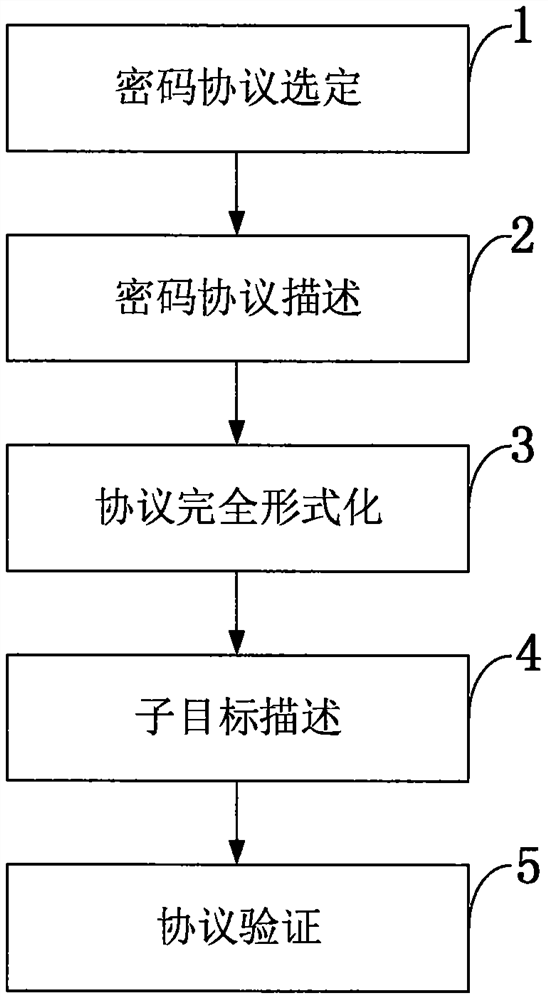
[0111] like figure 1 As shown, the cryptographic protocol verification method provided by the present invention comprises the following steps:
[0112] S101: Under the set network environment, a cryptographic protocol is given;
[0113] S102: Describe the cryptographic protocol according to the syntax and semantics of dynamic cognitive logic;
[0114] S103: Establish a behavior model a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More