White list library file protection method based on trusted computing
A technology of trusted computing and library files, applied in computing, digital data protection, computer security devices, etc., can solve problems such as the inability to properly solve the problem of illegal acquisition of secrets, the inability to perform security functions normally, and the loss of the meaning of comparison. High security protection strength, real and effective protection, high security protection effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
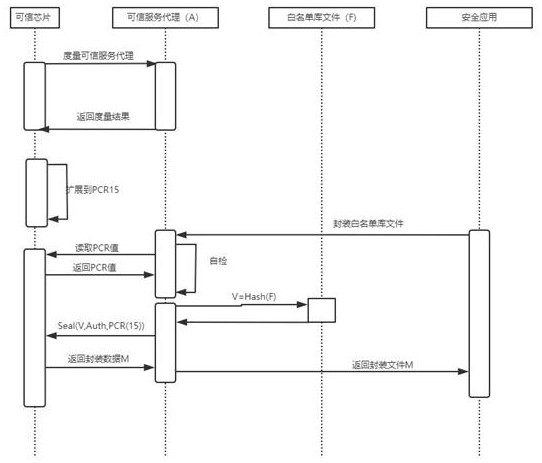
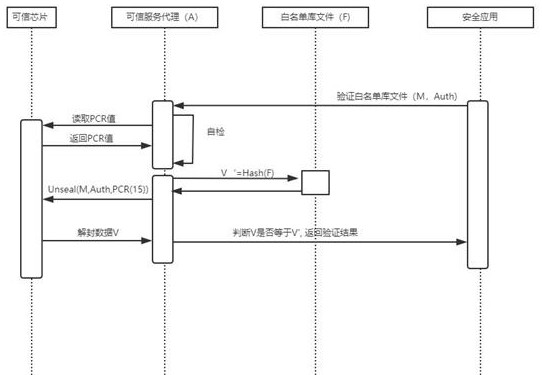
[0022] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
[0023] see Figure 1-2 , the present invention provides a technical solution: a whitelist library file protection method based on trusted computing, comprising the following steps:
[0024] The first step: the trusted service agent (A) joins in the startup trusted chain, and the measurement value of the trusted service agent (A) is extended to the platform configuration register (PCR) when the system starts;
[0025] Step 2: the security application sends a self-t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More