Data processing method and device, electronic equipment and computer storage medium
A data processing and data backup technology, applied in the computer field, can solve the problems of large user business intrusion, affecting user use, and the database cannot provide data writing services, so as to minimize user business impact, ensure database backup, and ensure global consistency. sexual effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
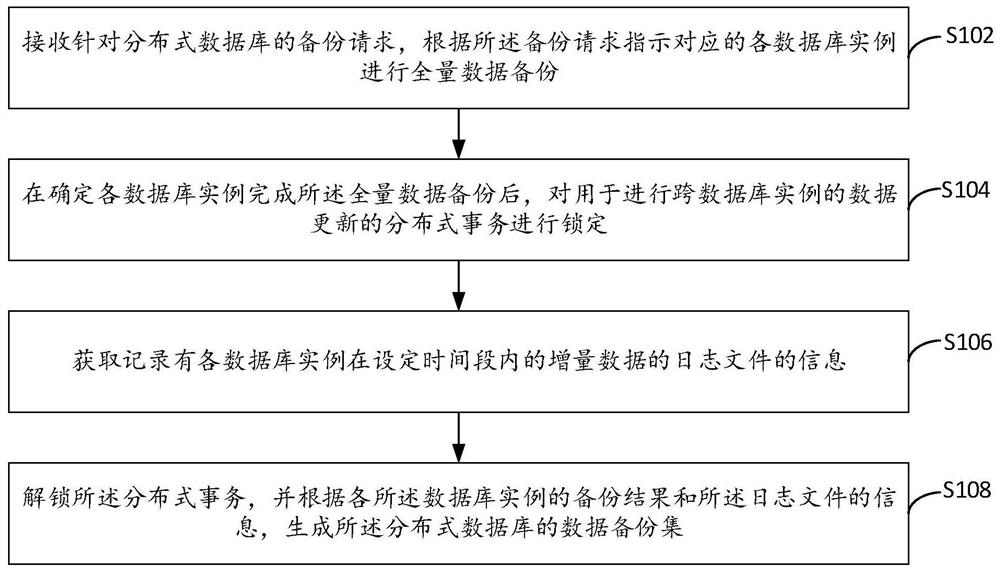
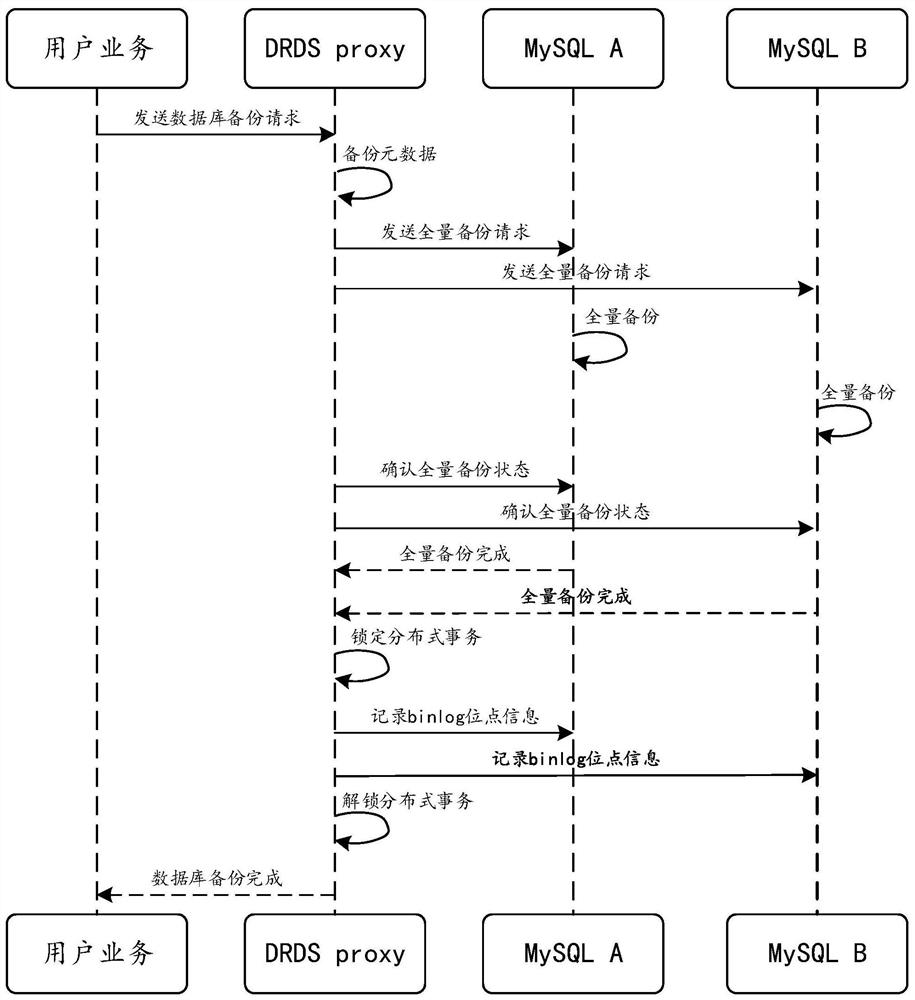
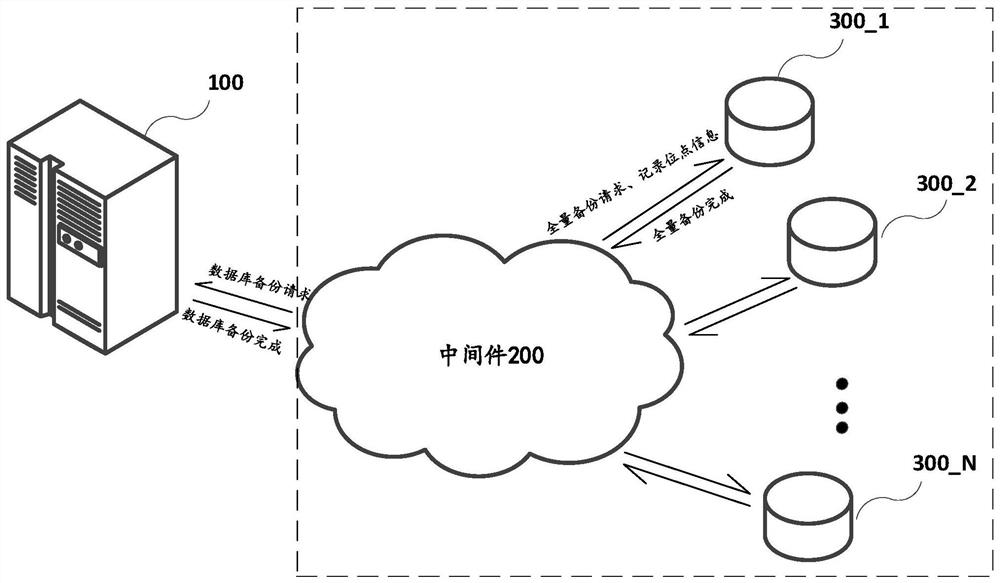
[0034] refer to figure 1 , shows a flowchart of steps of a data processing method according to Embodiment 1 of the present invention.
[0035] The data processing method of the present embodiment includes the following steps:
[0036] Step S102: Receive a backup request for the distributed database, and instruct each corresponding database instance to perform full data backup according to the backup request.
[0037] In this embodiment, the distributed database can adopt database sub-table technology (such as MySQL Sharding). This kind of distributed database can split a data table with a large amount of data into multiple sub-tables, and these sub-table Distributed across multiple database instances (such as MySQL instances). In this way, the sub-tables in each MySQL instance only contain part of the data in the data table, so that the data storage and computing pressure is distributed among multiple MySQL instances to solve the problem of single-machine performance bottlen...
Embodiment 2
[0058] refer to image 3 , shows a flowchart of steps of a data processing method according to Embodiment 2 of the present invention.
[0059] The data processing method of this embodiment includes the aforementioned steps S102 to S108.
[0060] Wherein, the step S104 includes the following sub-steps:
[0061] Sub-step S1041: After determining that each database instance completes the full data backup, determine whether all the distributed transactions that are being executed across database instances are committed.
[0062] Since the submission of distributed transactions may cause the global consistency of data cannot be guaranteed, in order to avoid this problem, after confirming that each database instance has completed the full data backup and before locking the distributed transactions, determine whether all the distributed transactions in execution Commit complete.
[0063] It should be noted that the completion of submission in this embodiment can be either a formal...
Embodiment 3
[0072] refer to Figure 4 , shows a flowchart of steps of a data processing method according to Embodiment 3 of the present invention.
[0073] The data processing method of this embodiment includes the aforementioned steps S102 to S108.
[0074] The step S104 can be realized by the method in the foregoing embodiment 1 or embodiment 2, or by other methods.
[0075] In this embodiment, the step S108 includes the following sub-steps:
[0076] Sub-step S1081: Generate an unlock instruction that allows the distributed transaction to be committed, to indicate to unlock the distributed transaction.
[0077] In order to minimize the intrusion to the user's business, after obtaining the information of the log file, an unlock command that allows distributed transaction submission is generated, so that the user business can normally submit the distributed transaction.
[0078] Those skilled in the art may use any appropriate method to generate the unlock instruction as required, whic...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap