High-confidentiality server anti-theft control and management system and method and medium
A server and confidential technology, which is applied in the direction of faulty hardware testing methods, faulty computer hardware detection, internal/peripheral computer component protection, etc., can solve data leakage, packet loss, enterprise-level server theft, etc., to achieve anti-theft leakage, The effect of preventing leakage
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
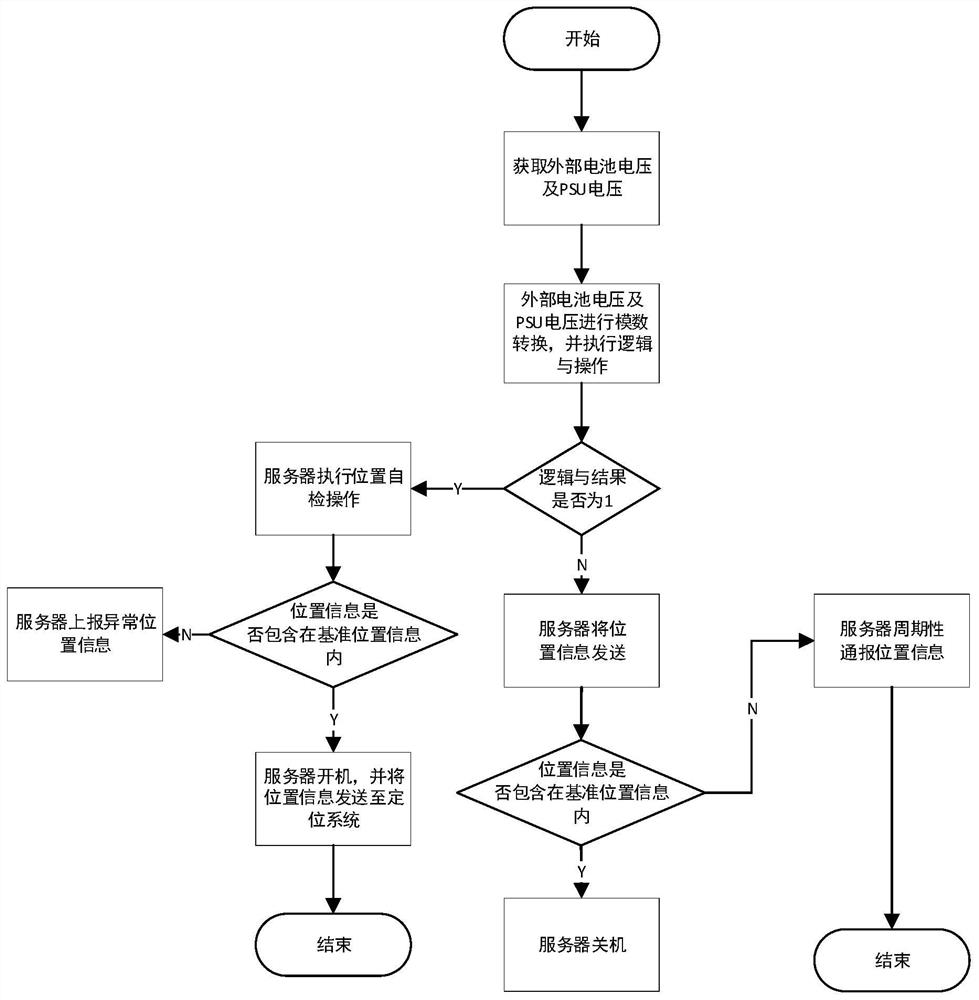
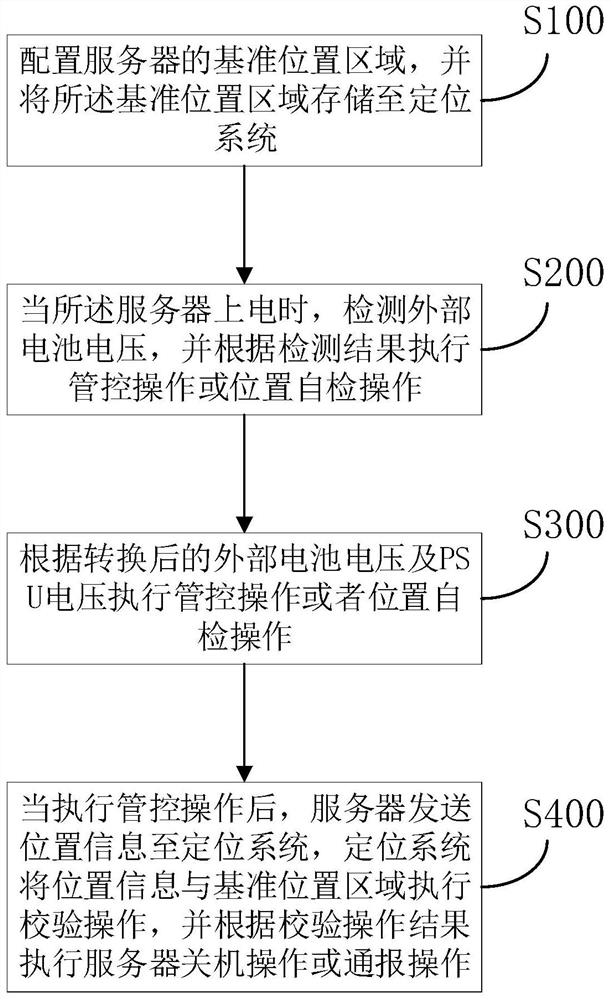
[0059] Embodiments of the present invention provide a high secret server anti-stealing control method, see figure 1 and figure 2 , Including the following steps:
[0060] S100, configure the reference location area of the server, and store the reference position area to the positioning system;
[0061] Step S100 specifically includes:
[0062] S101, configuring the reference location area:
[0063] The server referred to in the present invention may be a separate server, or a server cluster, when the server or server cluster implementation is initialized, the initialization state can make the server manufacturer for the first time, or the server cluster is migrated, first need Statistics of all servers of all servers in the server cluster, the statistical method in this embodiment is recorded the IP address and the physical address, with the IP address and the physical address as the center, and set the radius, the reference position area, the radius The setting can be divided a...
Embodiment 2
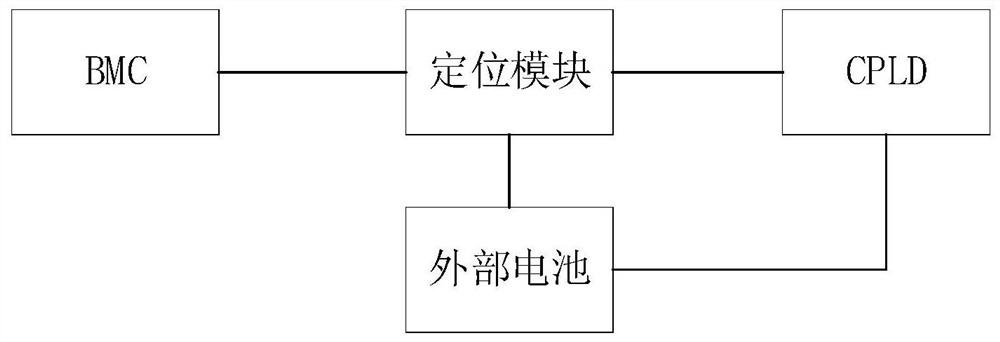
[0094] Embodiments of the present invention provide a high secret server anti-stealing control system, please refer to image 3 , Including: positioning module, CPLD, BMC, and external batteries;
[0095] The positioning modules are connected to external batteries, CPLD, and BMC, and CPLDs are connected to external batteries;
[0096] The positioning module includes a crystal unit, an RF unit, a VCC interface, an I2C interface, and a power supply unit.
[0097] The I2C interface of the positioning module is connected to the I2C interface of the BMC;
[0098] BMC sends information to server managers over the network interface;
[0099] External batteries are connected to the VCC interface of the positioning module;
[0100] External batteries are connected to the CPLD GPIO interface;
[0101] The RF unit is used to obtain location information;
[0102] The crystal unit is used to provide a clock for the positioning module;
[0103] The positioning module is used to store the referen...
Embodiment 3
[0107] The present invention also provides a computer readable storage medium that stores a computer program that performs as the method is performed when executed by the processor.
[0108] Finally, it will be noted that one of ordinary skill in the art will appreciate that all or part of the flow in the above-described embodiment, can be stored by a computer program to direct the related hardware, and the program of monitoring software can be stored in a computer. In the storage medium, the program may include the flow of an embodiment of each method as described above. Wherein, the storage medium of the program can be a disk, an optical disk, a read-only storage memory (ROM), or a random storage memory (RAM), and the like. Embodiments of the above computer program can achieve the same or similar effects as the corresponding foregoing any method embodiments.
[0109] Further, the method disclosed in accordance with an embodiment of the present invention may also be implemented a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com