Secure communication method for wireless sensor network
A wireless sensor and network security technology, applied in wireless communication, public key for secure communication, secure communication device, etc., can solve problems such as secret key escrow, achieve strong security, avoid delayed verification problems, and avoid replay attacks Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
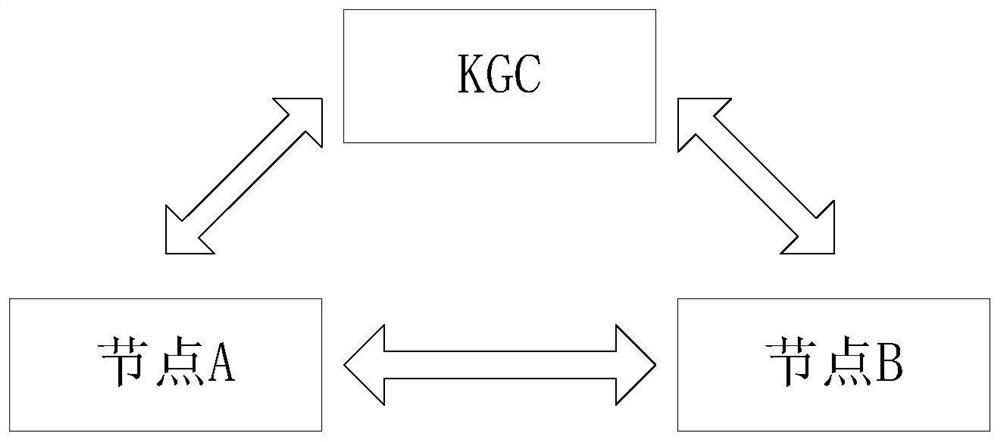
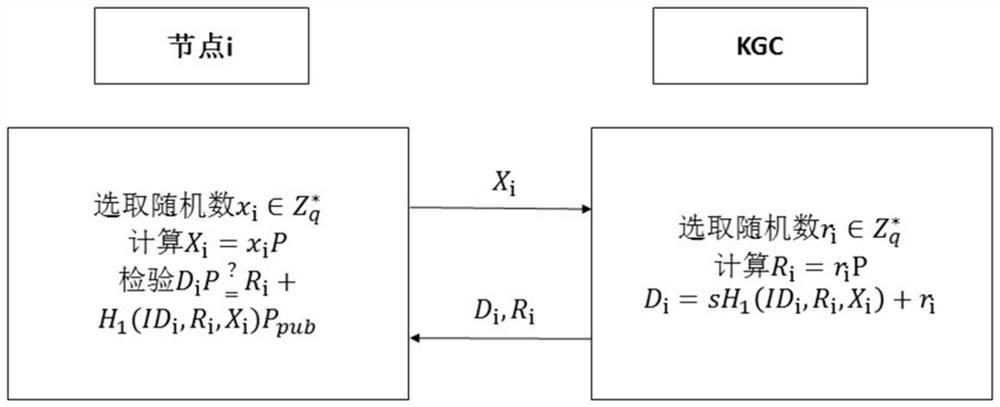
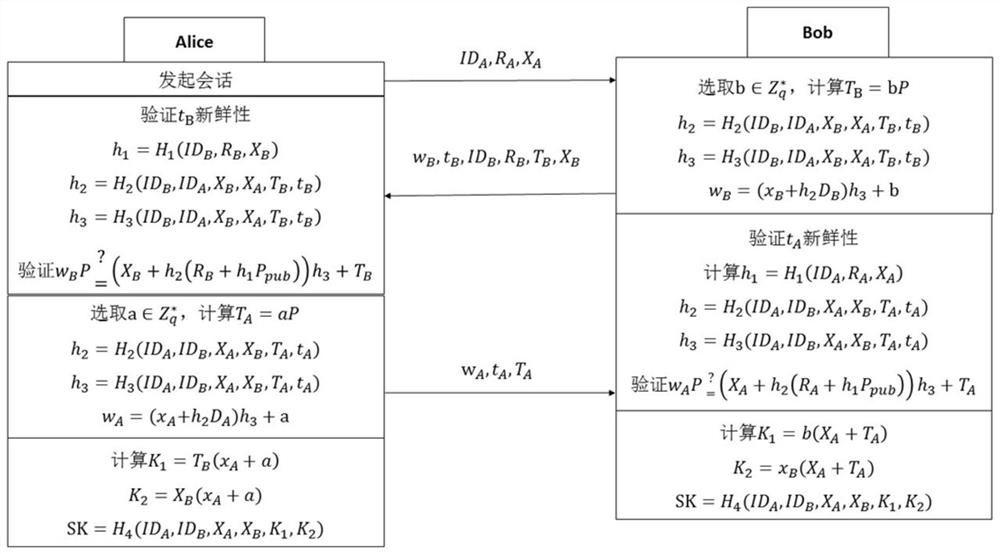
[0082] This embodiment proposes a method for secure communication in a wireless sensor network. The method in this embodiment is implemented based on a wireless sensor network system. The wireless sensor network system includes: KGC (Key Generation Center, secret key generation center), the trust center of the entire network , is used to establish the basis of the authentication system, and all nodes trust the signature of KGC. KGC creates a partial key for each node for identity authentication and key negotiation; nodes, participants in sessions in the network, and executive entities of the key negotiation scheme. When executing the negotiation plan, the process of generating signature and verifying signature will be executed separately. After the identity is confirmed, it will enter the generation stage of the session key. After the session key is generated, the node will use the session key to encrypt the message. The service object of KGC is as follows: figure 1 shown.
...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More