Image Authentication Method Based on Phase Recovery and Elliptic Curve Digital Signature Algorithm
An elliptic curve and digital signature technology, applied in the field of information security, can solve problems such as optical information security system collisions, and achieve the effects of improving security, avoiding collision problems, and avoiding trusteeship problems
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
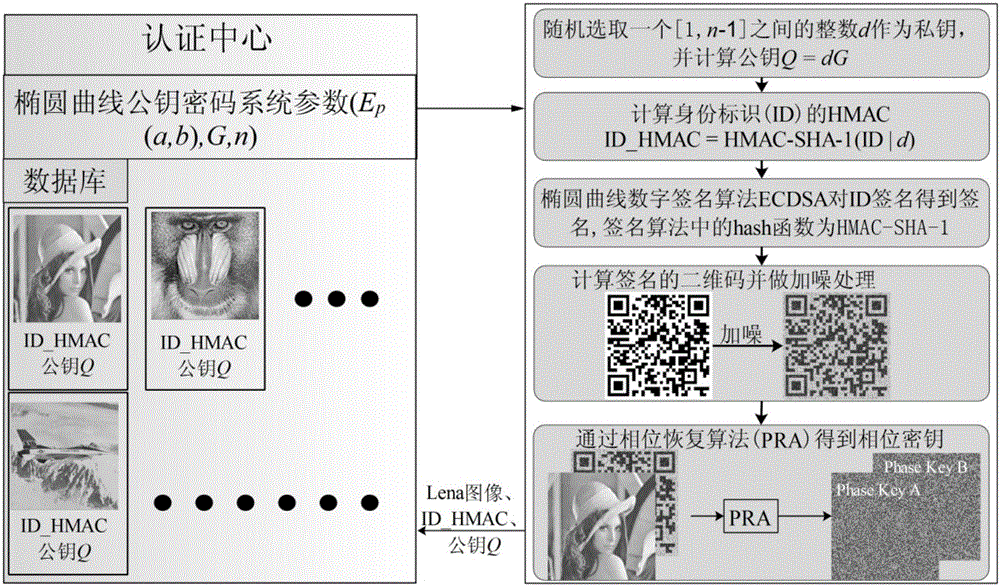
[0032] figure 1 The flow of authentication information generation in the present invention is given (only the authentication information generation flow of a single user is displayed, other users can generate authentication information according to the same flow), the authentication information generation process is as follows:
[0033] (1) The certification center generates and announces the parameters of the elliptic curve public key cryptosystem (E p (a,b),G,n):p is the specified finite field Z p A large prime number of , a and b are the elliptic curve y 2 ≡x 3 Coefficient of +ax+b(modp), G is the base point of the cyclic subgroup of points on the elliptic curve, and n is the order of the point G. In this embodiment, the secp160r1 elliptic curve on the prime number field recommended by StandardsforEfficientCryptography (SEC) and some simple parameters are selected. The parameters are:
[0034] Elliptic curve equation y 2 ≡x 3 +ax+b(modp)
[0035] p=FFFFFFFFFFFFFFFFF...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More