Host monitoring alarm processing method and device
A host and monitoring object technology, applied in the field of network security, can solve problems such as ensuring the security and disadvantages of the network system
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
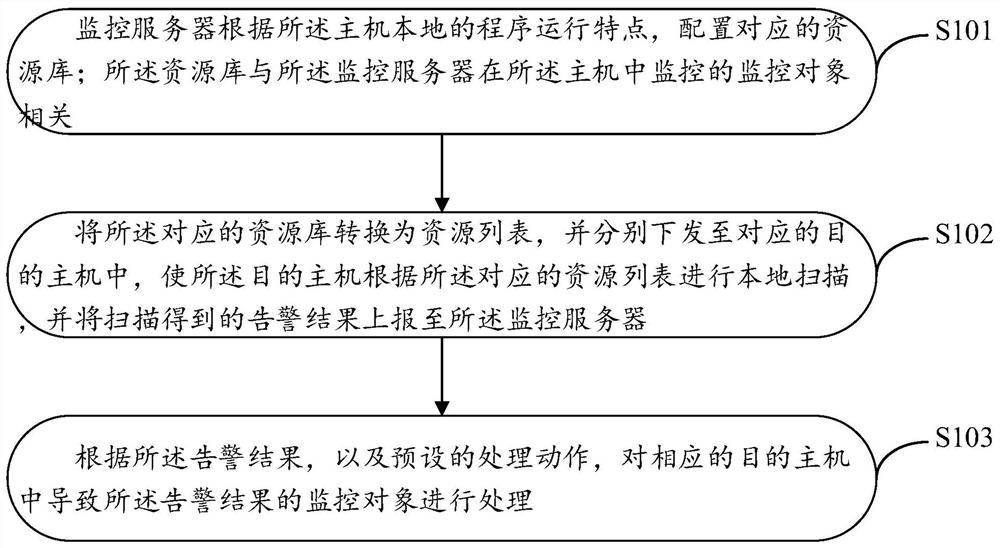
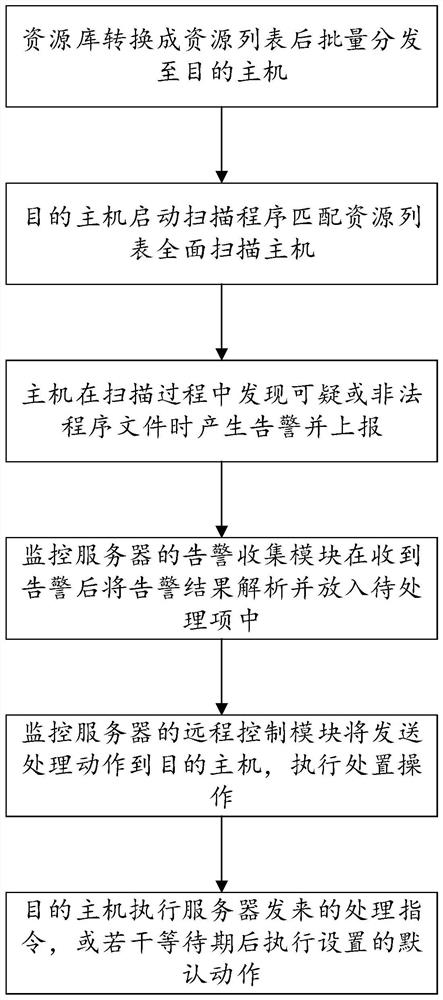
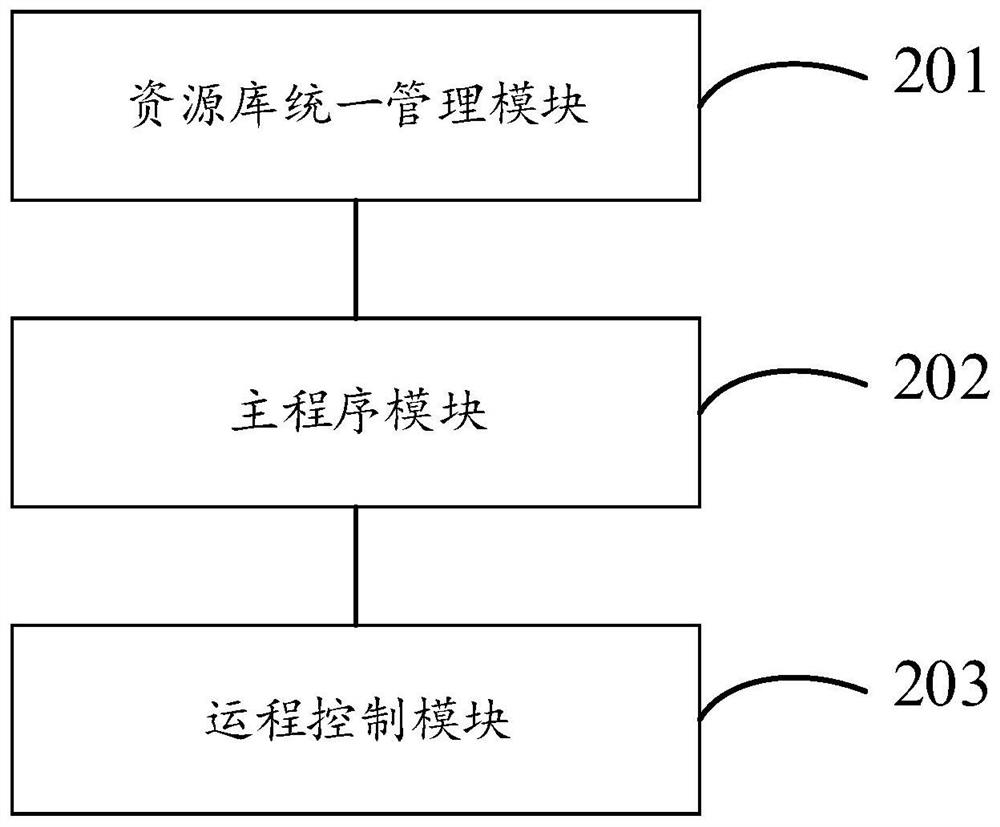
Method used
Image
Examples
Embodiment Construction
[0029] In order to make the purpose, technical solution and advantages of the present application clearer, the following will give a clear and complete description of the present application in conjunction with specific embodiments of the present application. Apparently, the described embodiments are only some of the embodiments of the present application, rather than all the embodiments. Based on the embodiments in this application, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the scope of protection of this application.
[0030] With the rapid development of the Internet, many companies are getting bigger and bigger, and more and more companies are also being established. During this process, the number of host servers used is increasing rapidly. At the same time, the complexity of the Internet environment has also made the issues of host security and network security increasingly prominent. In different pr...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More