Active defense method and system for exclusive storage space
A storage space and active defense technology, applied in the field of information security, can solve problems such as insufficient data protection and ineffective protection, and achieve reliable security and prevent counterfeiting and tampering
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0052] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the drawings in the embodiments of the present invention. Obviously, the described embodiments are part of the embodiments of the present invention, not all of them. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts shall fall within the protection scope of the present invention.
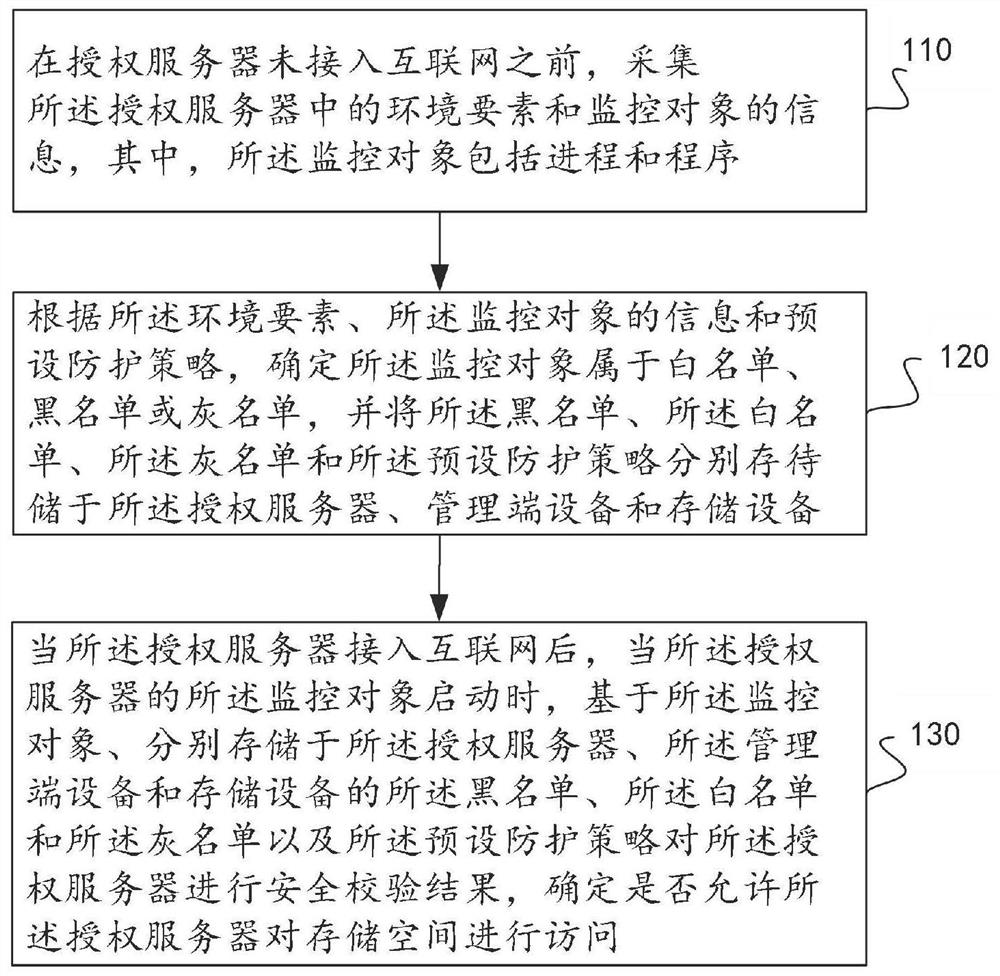
[0053] Such as figure 1 As shown, a dedicated storage space active defense method includes:
[0054] 110. Before the authorization server is connected to the Internet, collect information about environmental elements and monitoring objects in the authorization server, where the monitoring objects include processes and programs.
[0055] 120. Determine that the monitored object belongs to a whitelist, blacklist, or graylist according to the environmental e...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap