Network strategy verification system and method
A technology of network policy and verification method, applied in the direction of version control, software maintenance/management, creation/generation of source code, etc. The effect of saving development and technical iteration costs
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
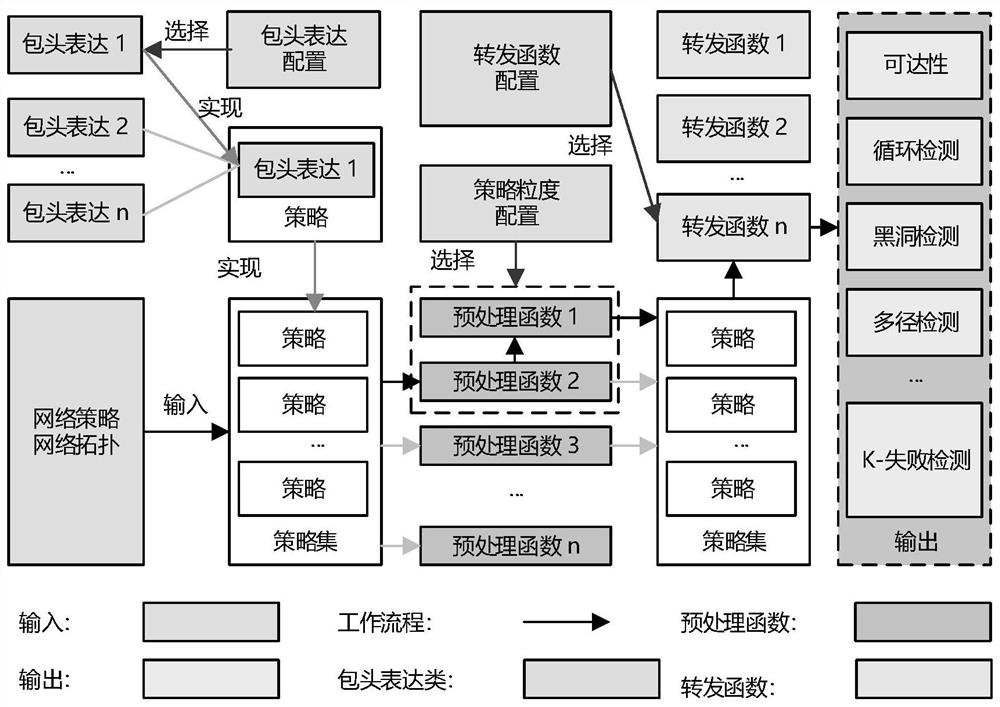
[0049] In order to make the purpose, technical solutions and advantages of the present invention clearer, the technical solutions in the present invention will be clearly and completely described below in conjunction with the accompanying drawings in the present invention. Obviously, the described embodiments are part of the embodiments of the present invention , but not all examples. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
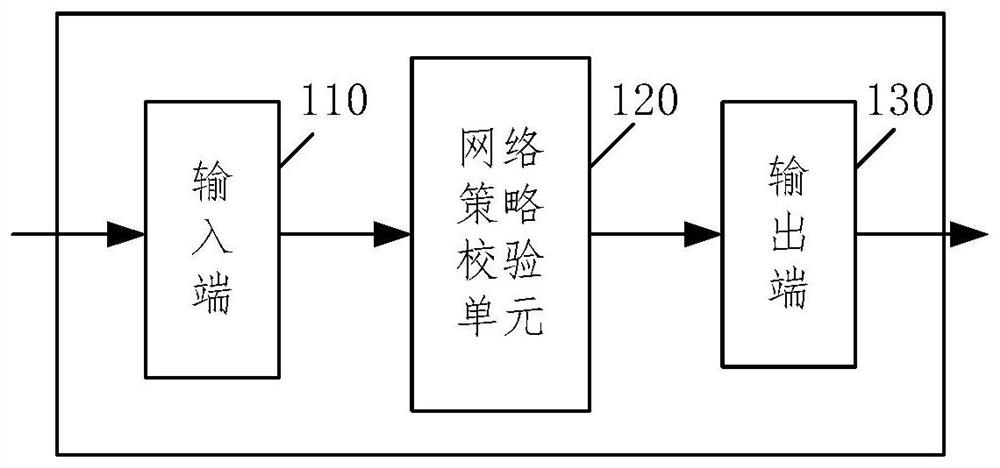
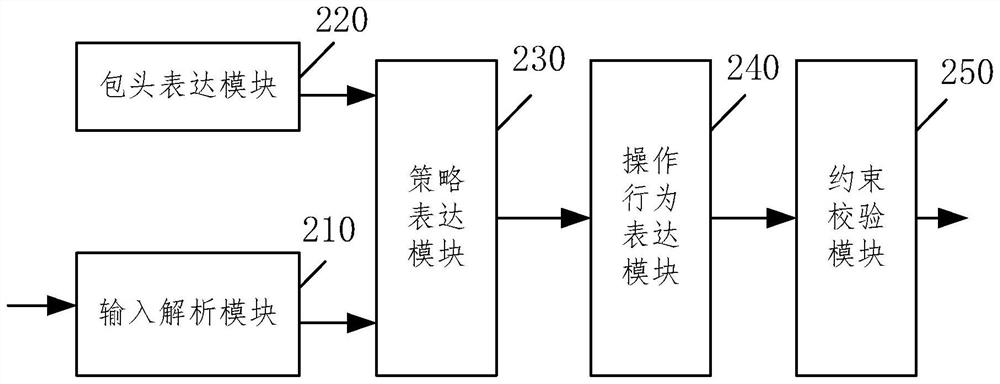
[0050] The purpose of the present invention is to reconstruct various network verification algorithms through modular program design based on the functional modularization of network policy verification technology, define a unified module interface and data structure, and realize flexible and expandable The general framework of network policy verification tools reduces the difficulty of using...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More