Key management method and device
A key management and key technology, applied to secure communication devices and key distribution, can solve problems such as user inconvenience and user asset security risks, and achieve the effect of ensuring asset security and eliminating the risk of key leakage or loss.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
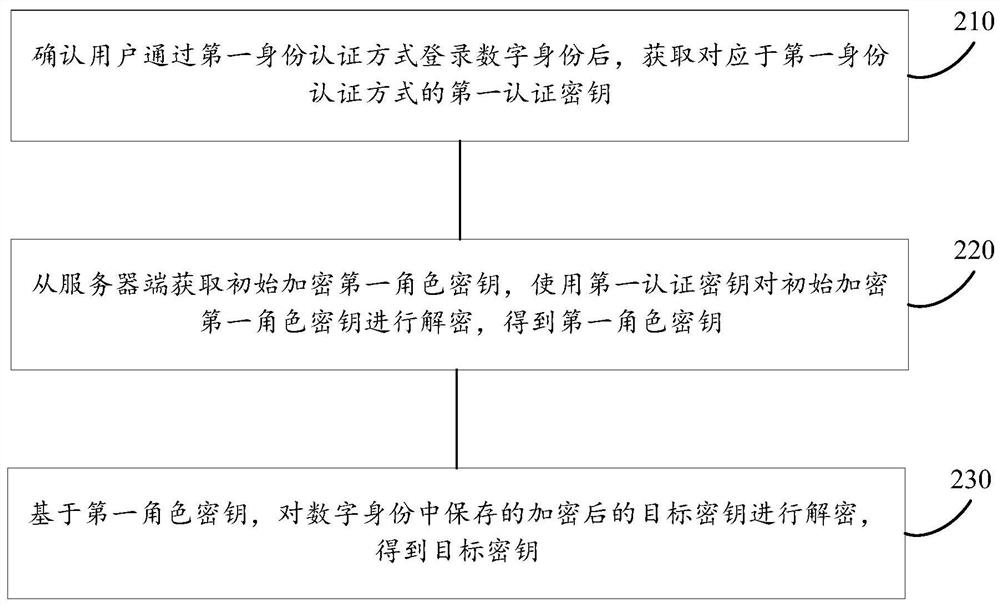
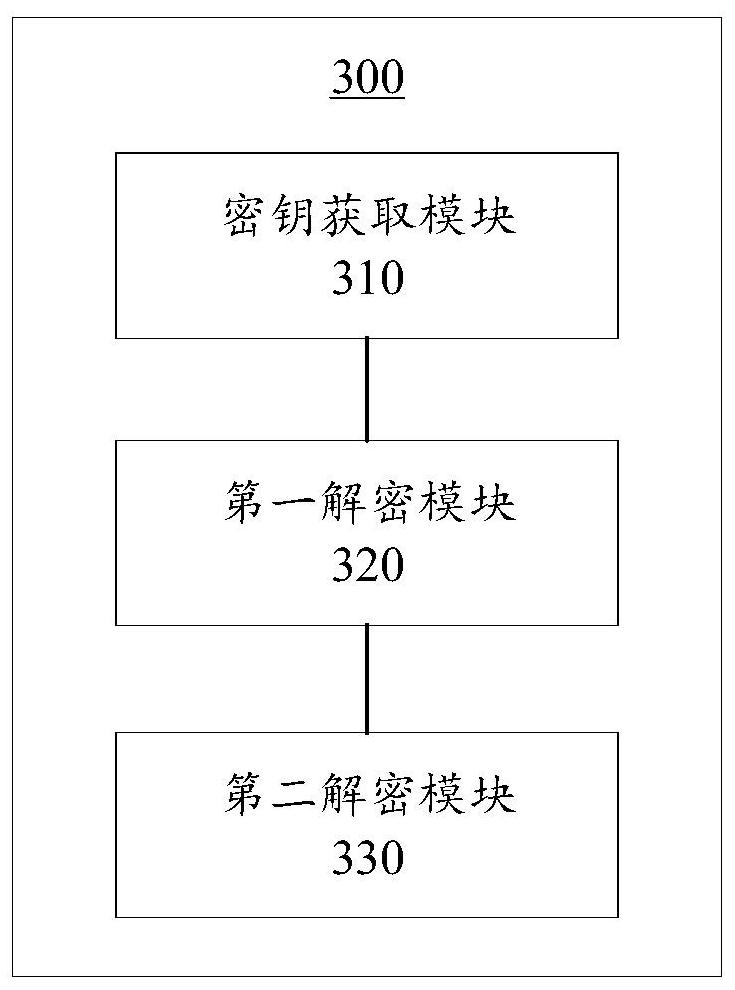
[0016] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some of the embodiments of the present invention, not all of them. All other embodiments obtained by persons of ordinary skill in the art based on the embodiments of the present invention belong to the protection scope of the present invention.
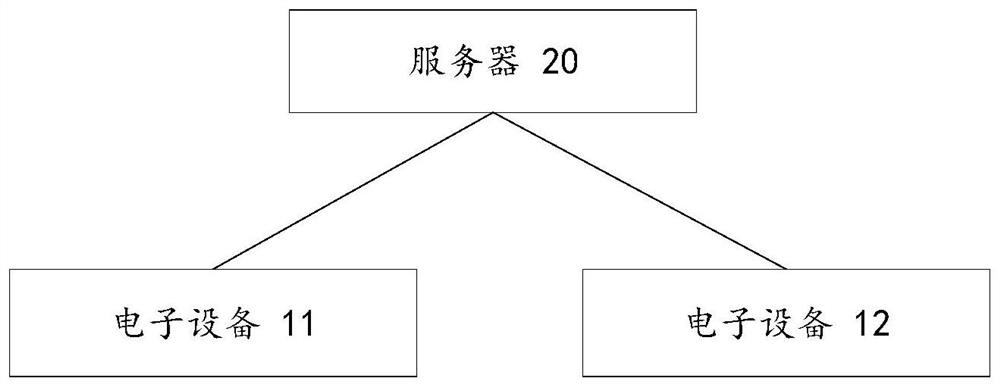
[0017] Application overview
[0018] As mentioned earlier, in the current environment where the Internet is rapidly developing and popularizing, users need to manage their own assets through various account passwords or keys. However, there are so many products and platforms that make people dizzy, the account passwords that are not commonly used are easy to forget, and the keys are long and difficult to remember, making them very difficult to manage.
[0019] In view of the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More