Security policy configuration method and device, electronic equipment and storage medium
A security policy and configuration method technology, applied in the field of network security, can solve the problems of low security policy configuration efficiency, improve configuration efficiency and execution efficiency, reduce memory pressure, and improve security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
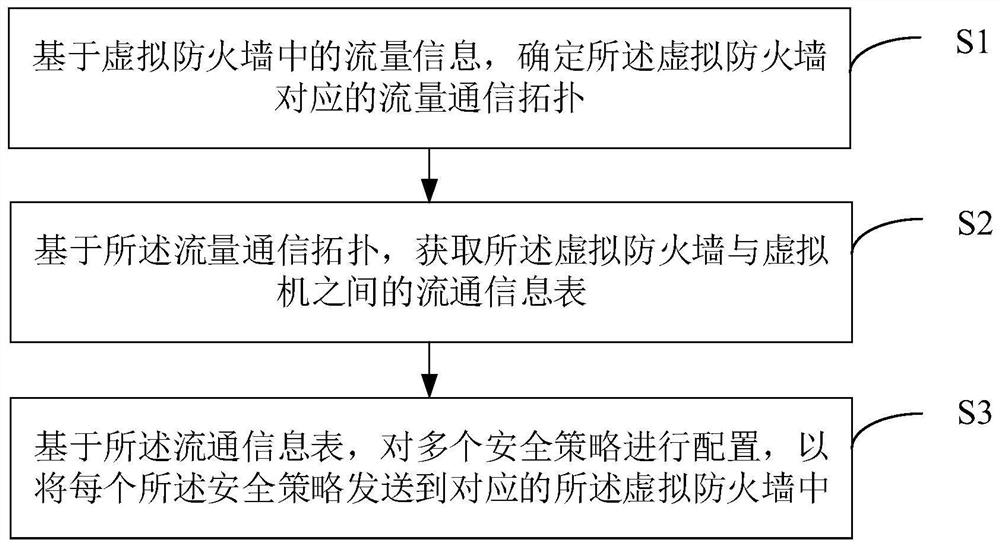
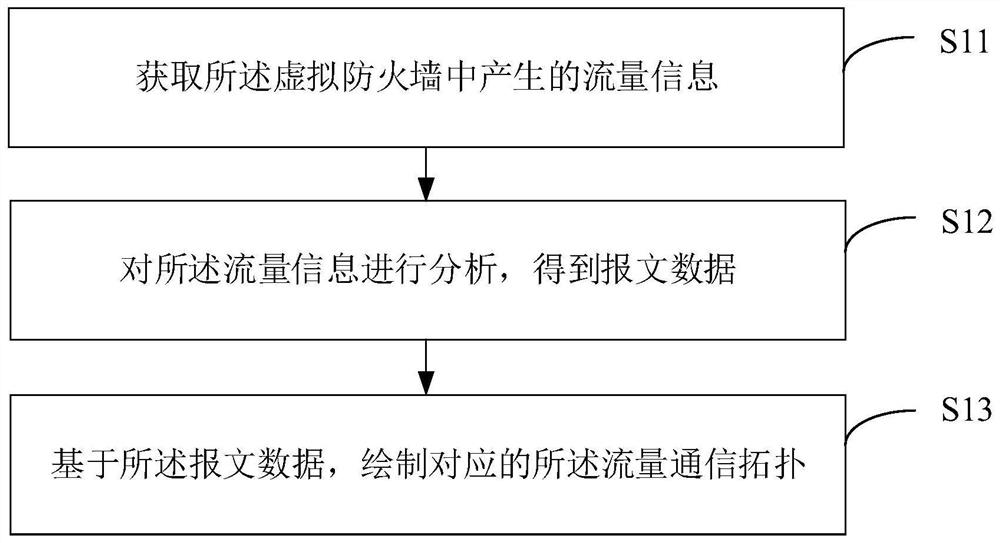
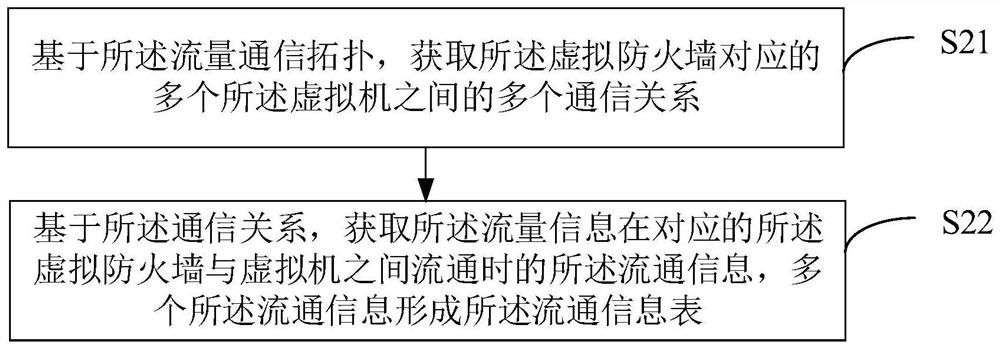
[0052] The following will clearly and completely describe the technical solutions in the embodiments of the present application with reference to the drawings in the embodiments of the present application. Apparently, the described embodiments are only some of the embodiments of the present application, but not all of them. Based on the embodiments of the embodiments of the present application, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the scope of protection of the embodiments of the present application.
[0053] When using VFW (Virtualization Security Firewall) for virtual security processing, virtual machines are usually allocated relatively fixed addresses or dynamically allocated in fixed address segments, and the static IP (Internet Protocol, Internet Protocol) of virtual machines is interconnected Protocol) or the virtual machine IP synchronized from the virtualization cloud platform is configured as...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More