Safety data transmission
A technology for secure data and security equipment, applied in the field of secure data transmission, which can solve the problems of weak protection and easy to be cracked.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
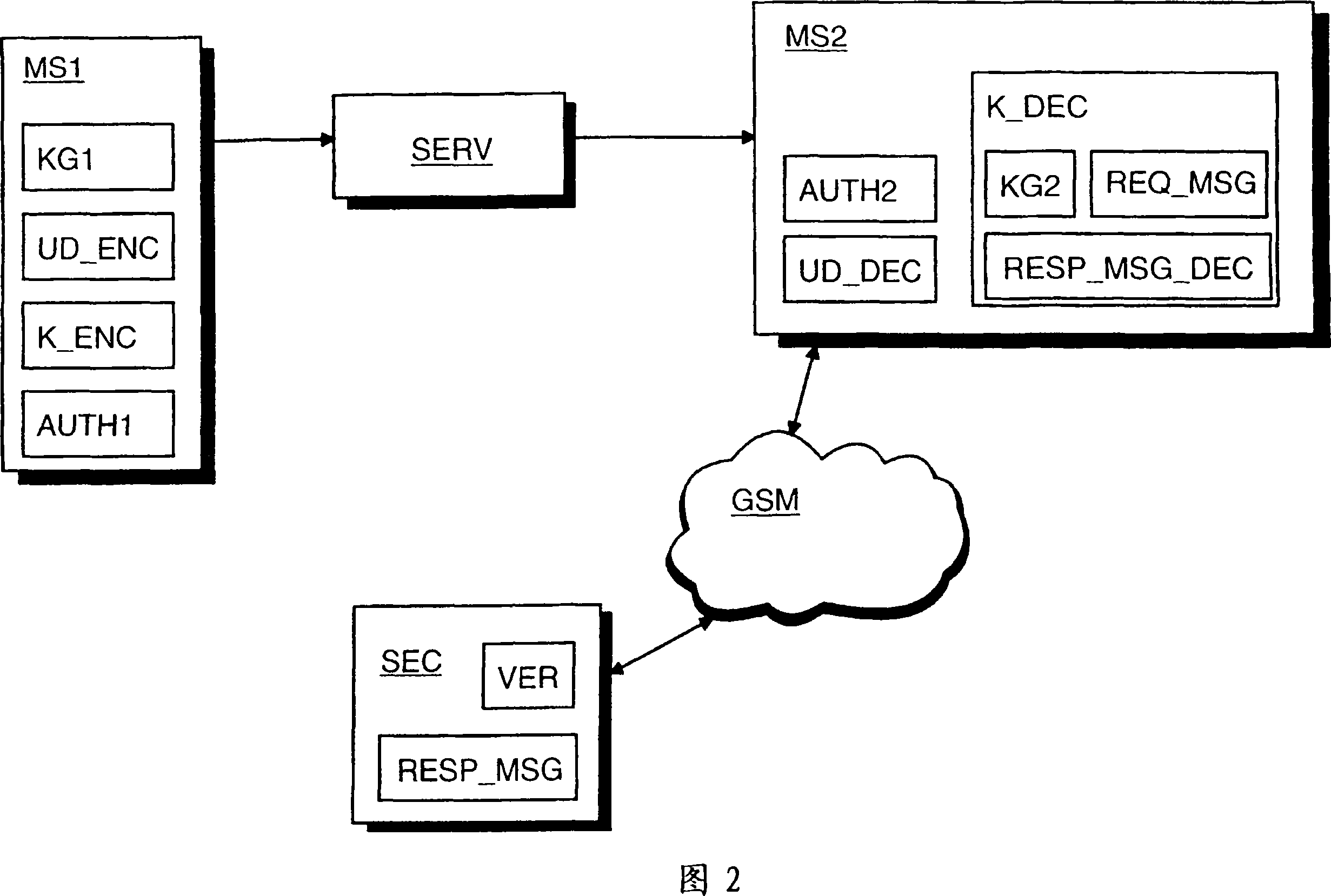
[0023] Embodiments of the invention will now be described in detail, examples of which are illustrated in the accompanying drawings.
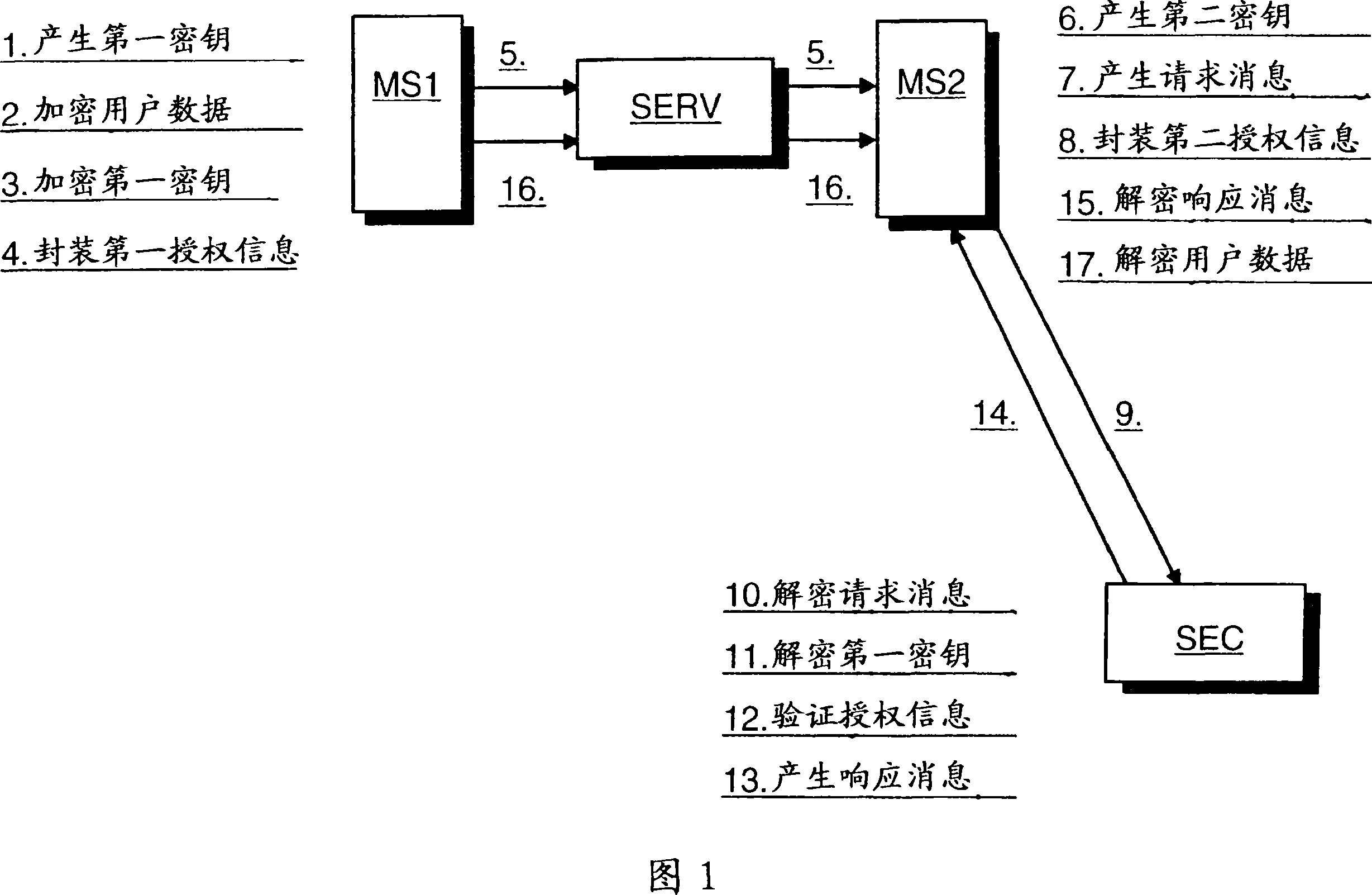
[0024] Figure 1 illustrates an exemplary embodiment of the method of the present invention. In step 1, a random first symmetric key is generated at the first wireless communication device. Then, the user data of the first wireless communication device is encrypted at the first wireless communication device with the generated first symmetric key (step 2). User data can be encrypted eg as one data block, or can be encrypted on a "file-by-file" basis.
[0025] In step 3, the generated first symmetric key is encrypted at the first wireless communication device with a third party's public key. The public key may have been obtained beforehand and embedded in the first wireless communication device in an integrity-protected manner such that an attacker cannot change or replace the public key. Alternatively, the public key can be introduced external...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More