A file encryption method based on Linux operating system with CPK authentication
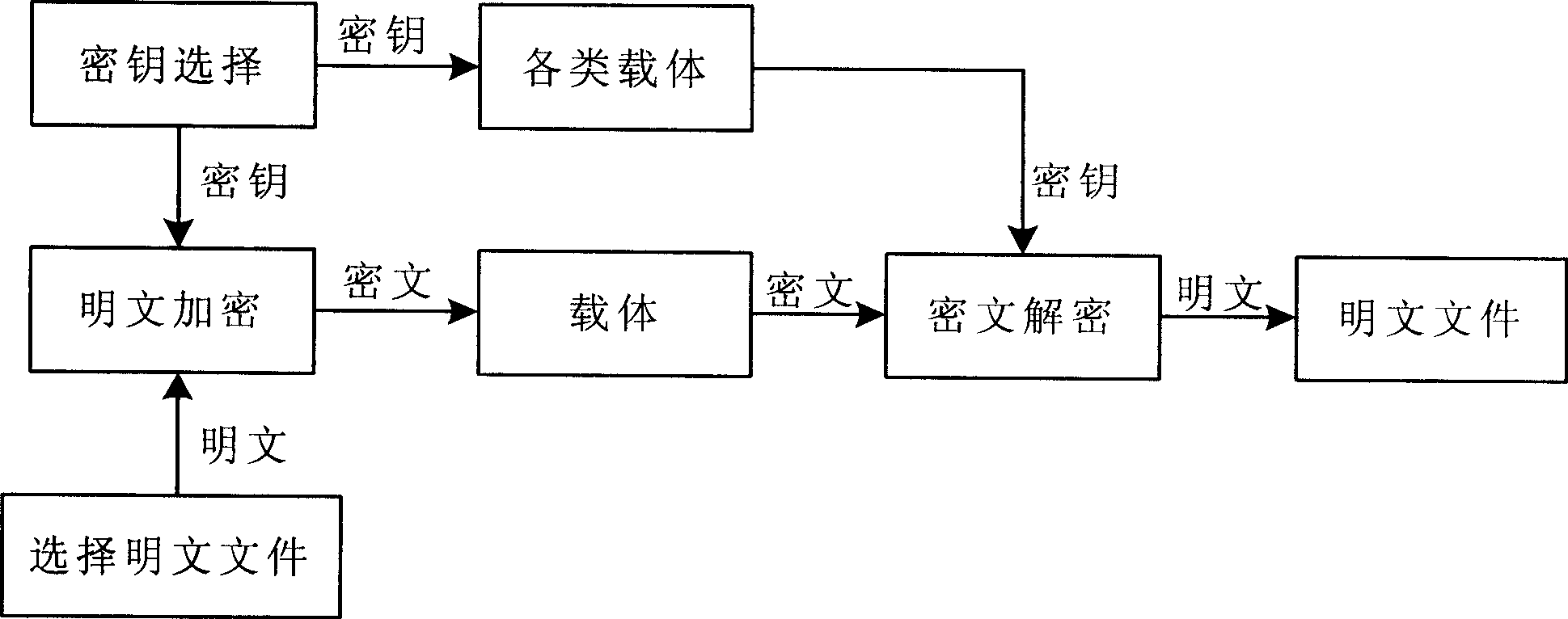
An operating system and file encryption technology, applied in the field of information security, can solve the problems of low encryption energy, slow authentication speed, easy to be deciphered, etc., to achieve the effect of fast authentication speed, ensure security, and solve the hidden danger of key security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
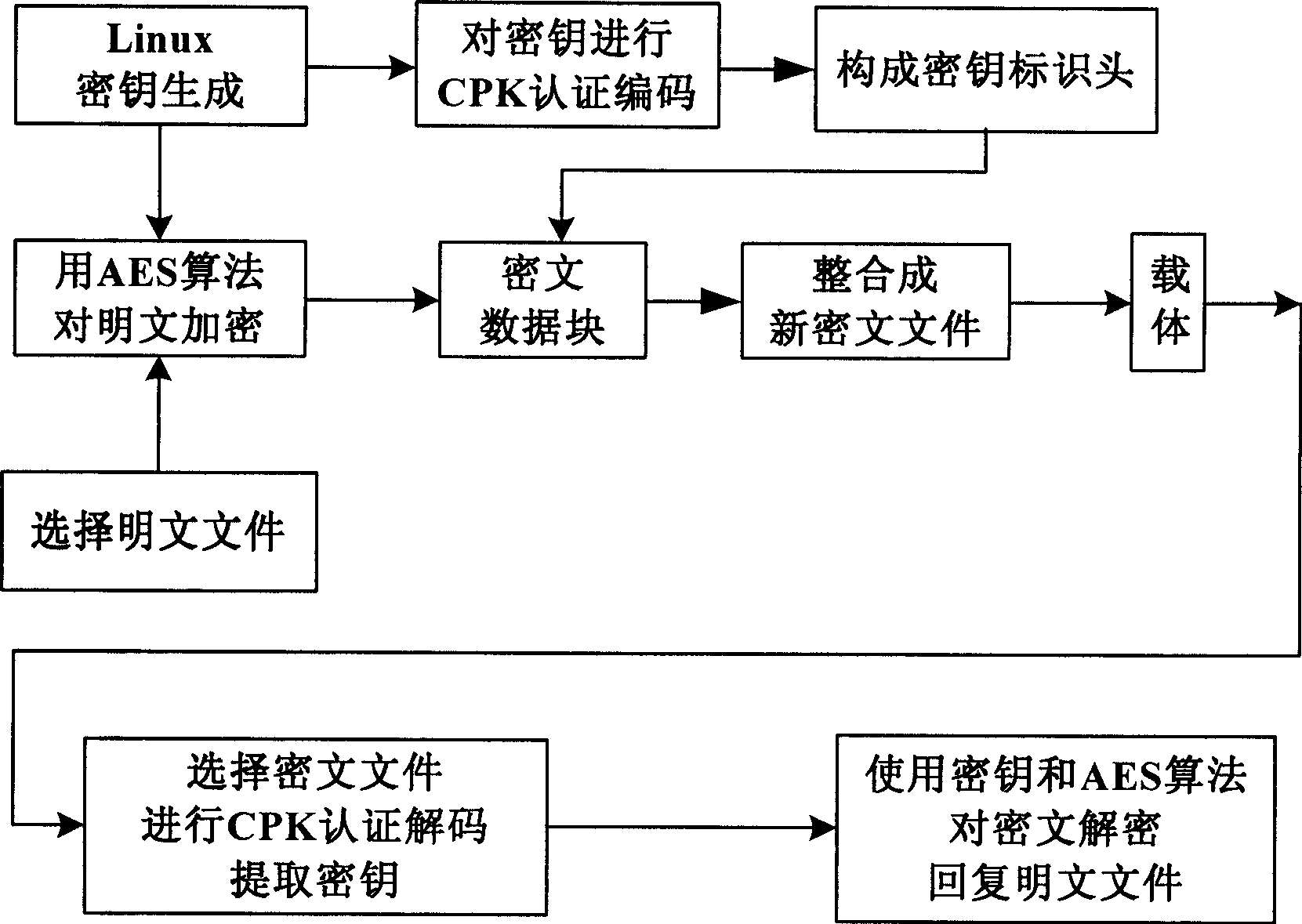
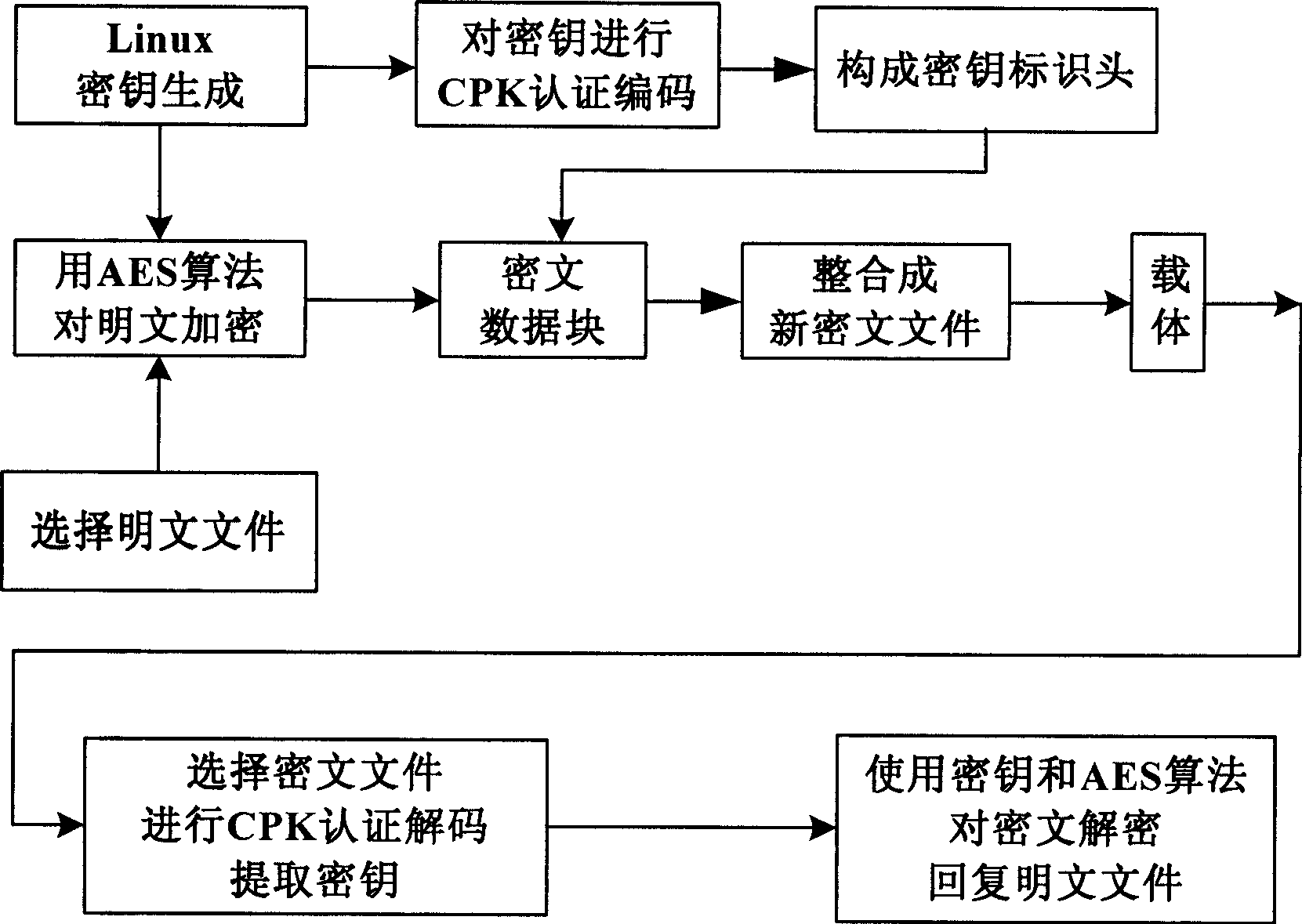
[0023] see figure 2 , this method consists of the following steps:
[0024] 1), the Linux operating system selects the plaintext file that needs to be encrypted according to the needs of the user,
[0025] 2), after the file is selected, the Linux operating system will generate a set of random key data;
[0026] 3), the Linux operating system uses the key data and the AES algorithm to encrypt the selected plaintext file to generate ciphertext data;
[0027] 4), the Linux operating system carries out CPK authentication encoding to the key data in addition, and constitutes a file identification header;
[0028] 5), then the file identification header and the ciphertext data are integrated into a new ciphertext file by the Linux operating system;
[0029] 6), the Linux operating system stores the above-mentioned ciphertext file in a carrier again;
[0030] 7), when using this file, after the Linux operating system extracts the ciphertext file in the carrier, carry out CPK au...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More