Authentication device in communication system
A communication system and authentication technology, applied in the field of communication, can solve the problems of user interference, attack user key security threats, etc., and achieve the effect of good compatibility, maintenance of authority and security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
no. 1 example
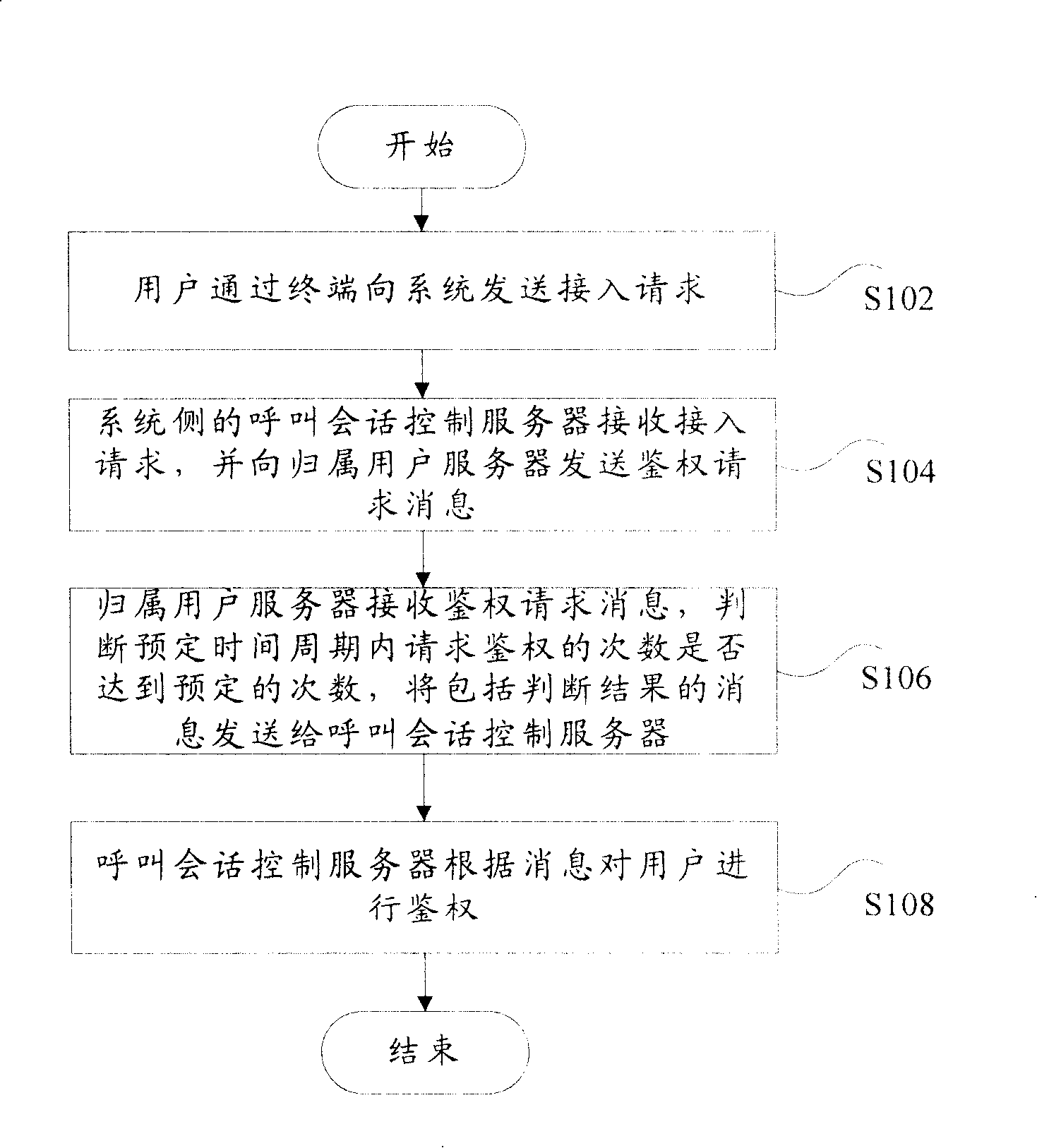
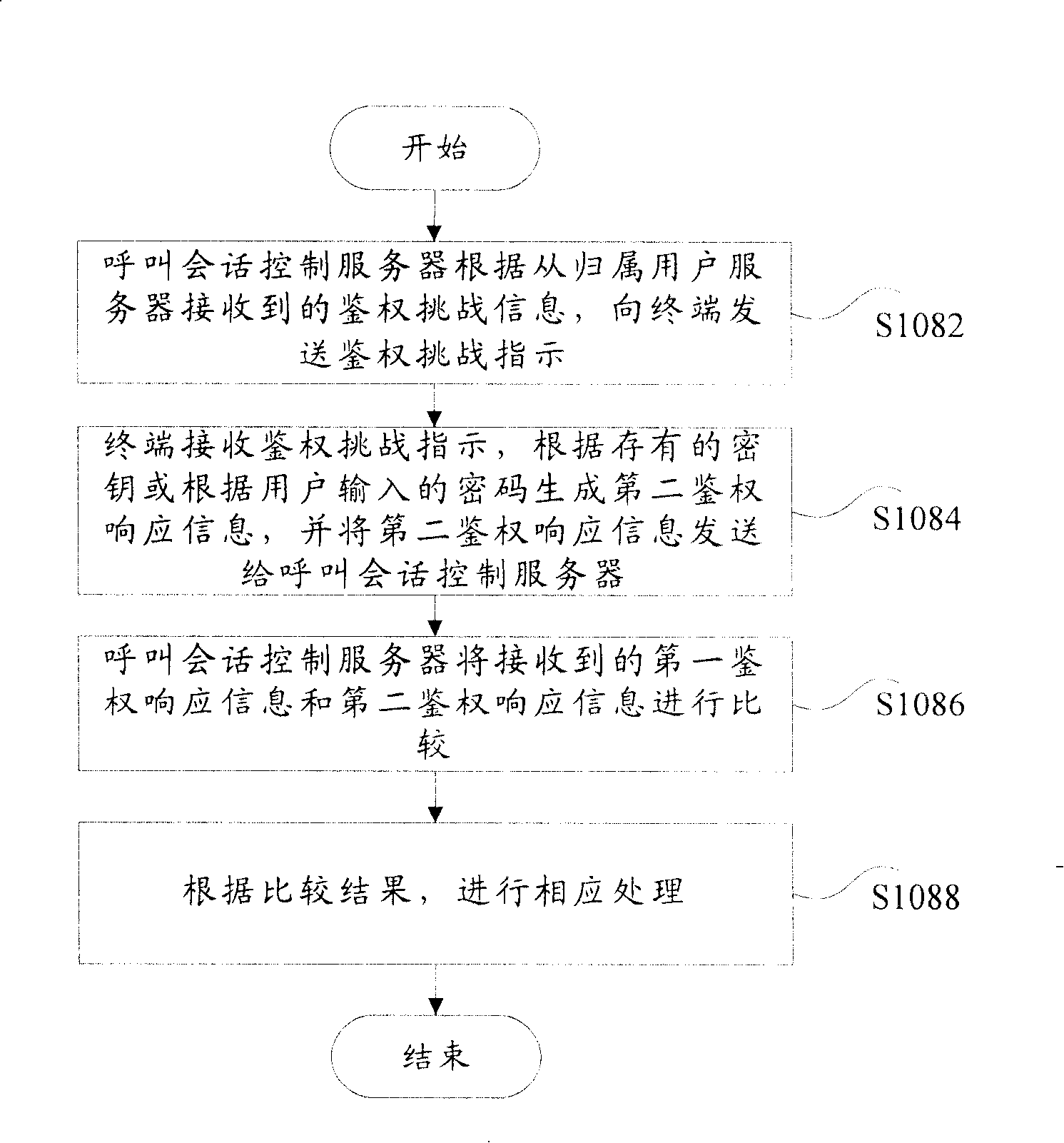
[0026] First, refer to figure 1 and figure 2 A first embodiment of the present invention is described. figure 1 is a flow chart of the communication system authentication method according to the first embodiment of the present invention, figure 2 is a detailed flow chart of the communication system authentication method according to the first embodiment of the present invention.
[0027] Such as figure 1 As shown, the communication system authentication method according to the first embodiment of the present invention includes the following steps: step S102, the user sends an access request to the system through the terminal; step S104, the call session control server on the system side receives the access request, and sends the The home subscriber server sends an authentication request message; Step S106, the home subscriber server receives the authentication request message, judges whether the number of requests for authentication in a predetermined time period reaches ...
no. 2 example
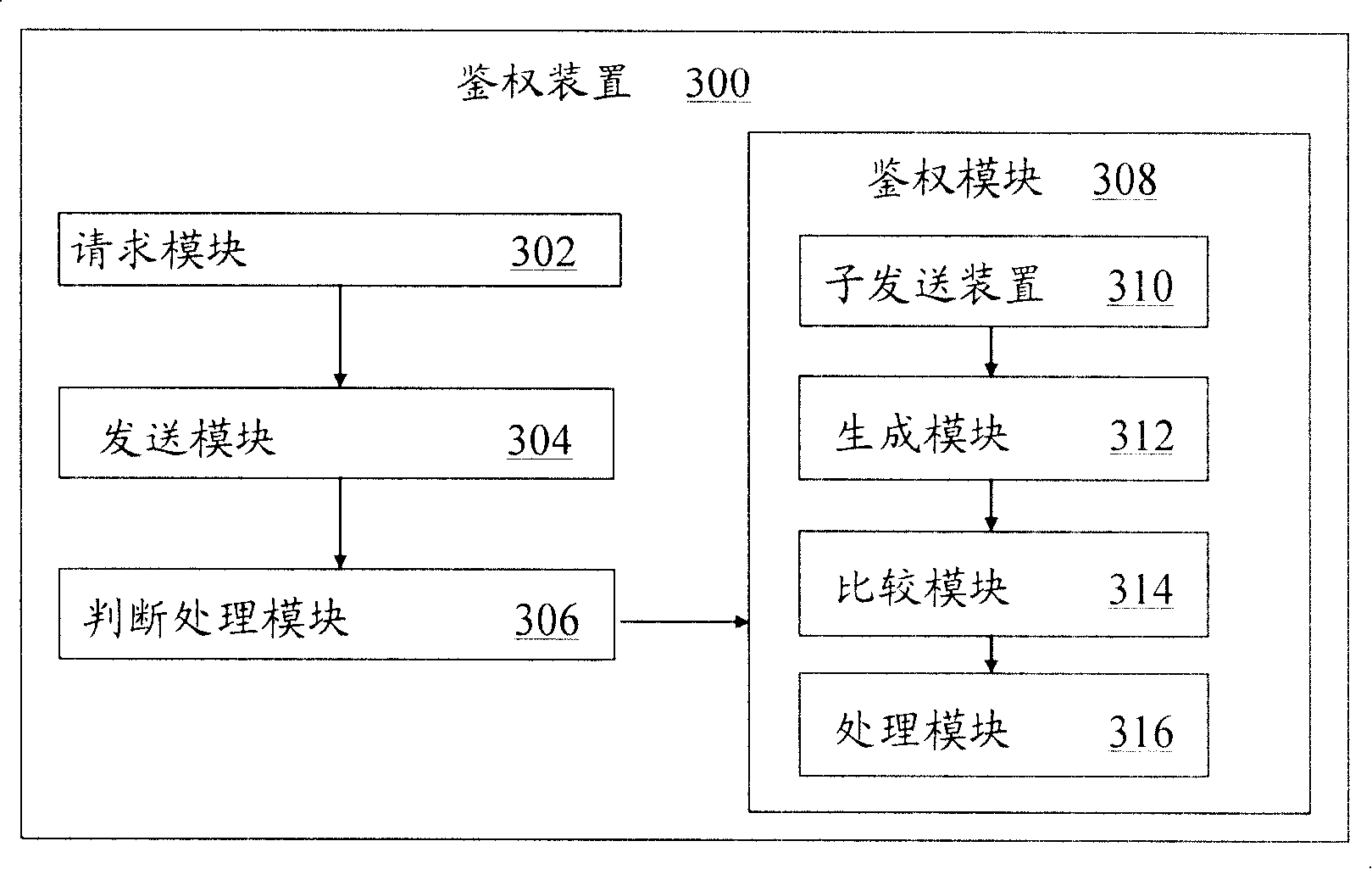
[0036] The following will refer to image 3 A second embodiment of the present invention is described. image 3 is a block diagram showing the configuration of the authentication device 300 in the communication system according to the second embodiment of the present invention.
[0037] Such as image 3As shown, the authentication device 300 in the communication system according to the second embodiment of the present invention includes: a request module 302, which is used to enable the user to send an access request to the system through a terminal; a sending module 304, which is used to make the call session on the system side The control server receives the access request, and sends an authentication request message to the home user server; the judging processing module 306 is used to make the home user server receive the authentication request message, and judge whether the number of requests for authentication within a predetermined time period reaches a predetermined nu...
no. 3 example
[0045] The following will refer to Figure 4 , Figure 5 , Figure 6 ,and Figure 7 A third embodiment of the present invention is described. Figure 4 is a block diagram of a system configuration example applying the present invention, Figure 5 yes Figure 4 The flow chart of normal user registration in the system shown, Figure 6 yes Figure 4 Flowchart of malicious registration of illegal users in the system shown, Figure 7 is in image 3 A flowchart of the implementation of the present invention in the system shown.
[0046] The following describes the embodiments of the present invention by taking the IMS system as an example.
[0047] Such as Figure 4 As shown, the mobile or fixed terminal UE 11 accesses the IMS (IP Mutimedia Subsystem) network, and is required to be authenticated during the registration (Register) process;
[0048] The access proxy server P-CSCF 12 implements the user agent function, and processes or forwards received requests and services...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More