System, method and computer program product for authenticating a data agreement between network entities
A technology of computer programs and network entities, applied in digital transmission systems, transmission systems, user identity/authority verification, etc., can solve problems such as errors and difficult strings
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0025] Hereinafter, the present invention will be described more fully with reference to the accompanying drawings, in which preferred embodiments of the invention are shown. However, the invention may be embodied in many different forms and should not be construed as limited to the embodiments set forth herein; rather, these embodiments are provided so that this disclosure will be thorough and complete, and will convey knowledge to those skilled in the art. personnel to fully convey the scope of the invention. Like numbers refer to like elements throughout.
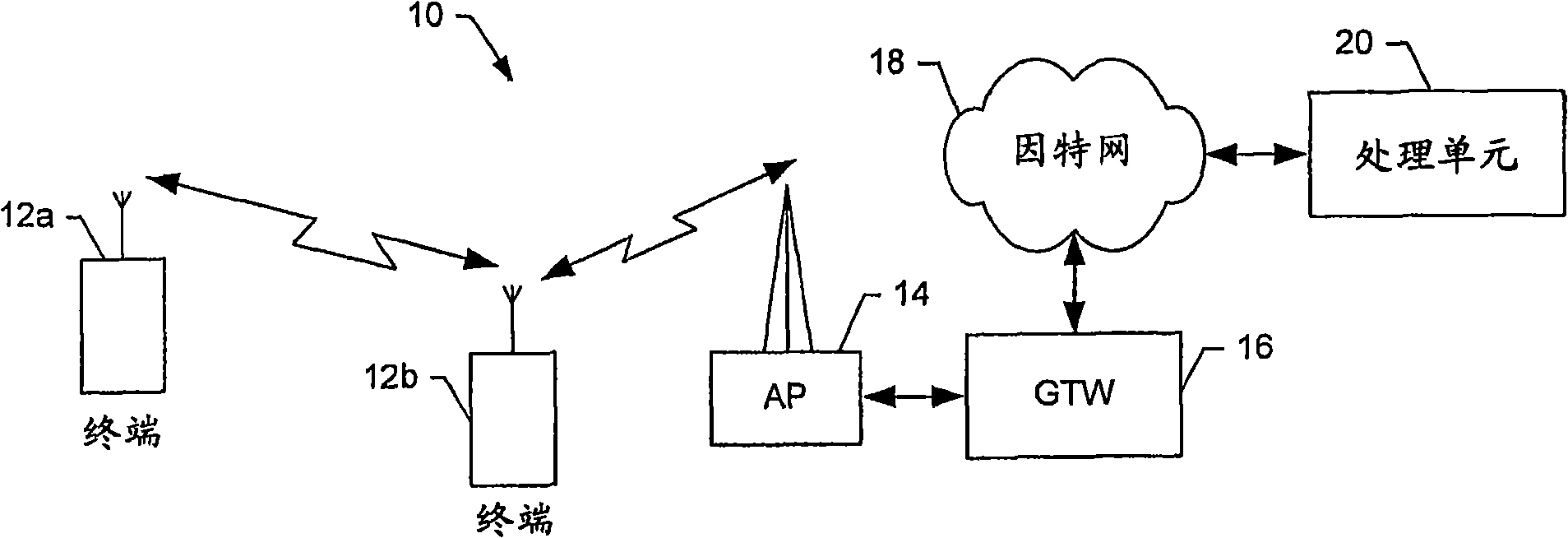
[0026] refer to figure 1 , which provides a description of one type of terminal and system that would benefit from the present invention. The systems, methods and computer program products of embodiments of the present invention will primarily be described in conjunction with mobile communication applications. It should be understood, however, that the systems, methods, and computer program products of embodiments of ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More