Authentication system for networked computer applications
A computer system, computer technology, used in computer parts, record carriers used by machines, computing, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
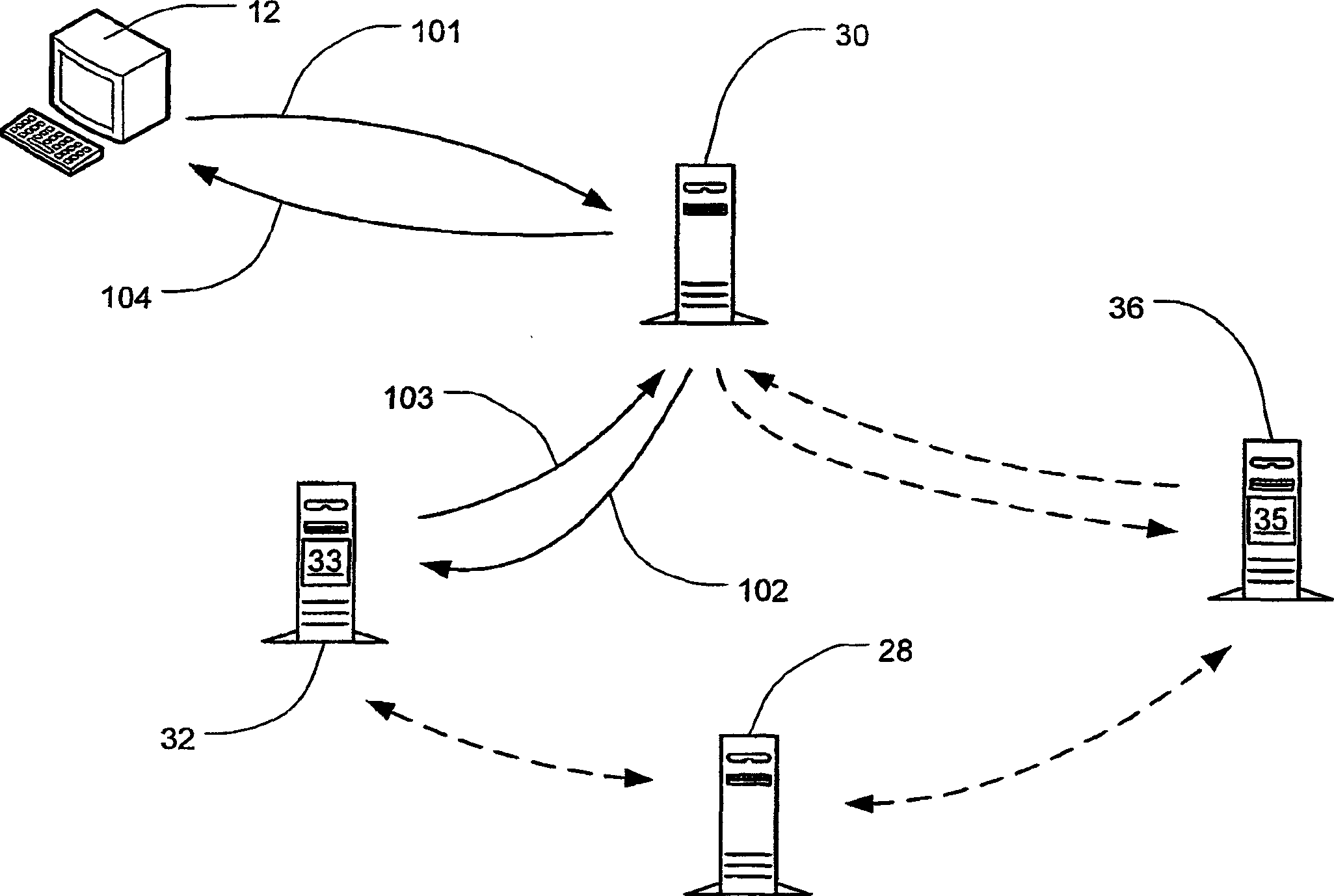
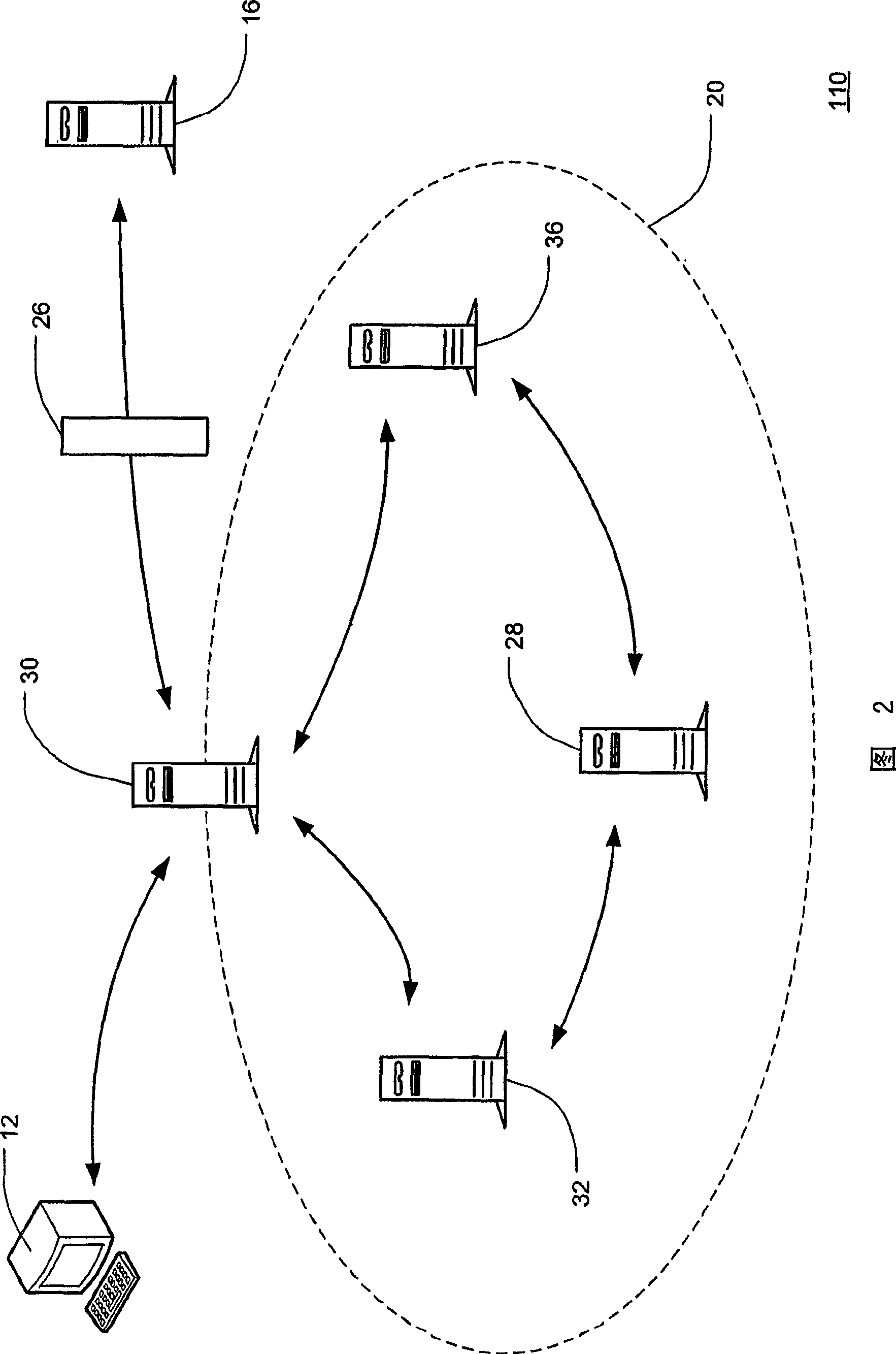
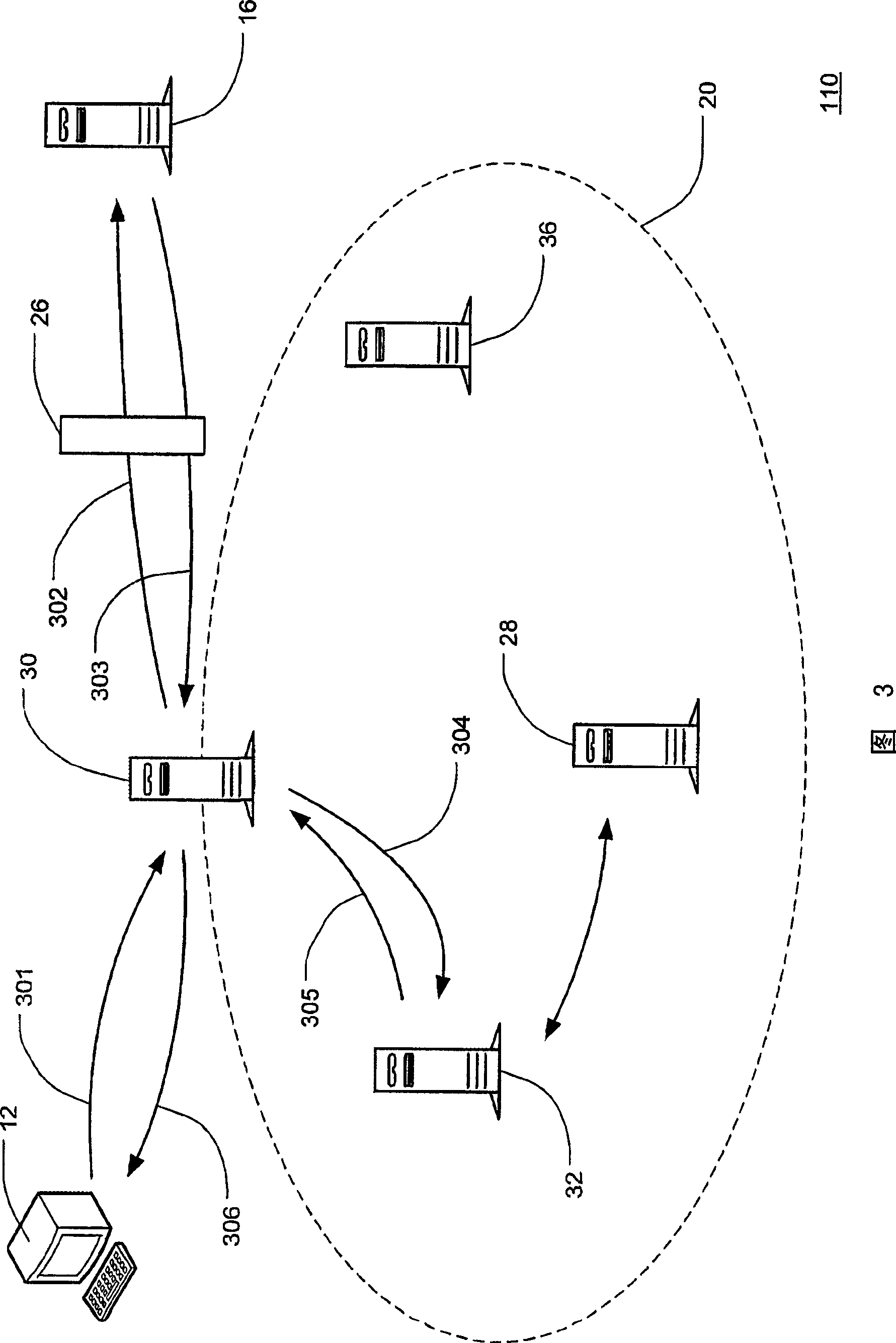
Image
Examples
Embodiment Construction
[0026] The following descriptions of embodiments of the invention are merely exemplary in nature and are not intended to limit the invention and its application or uses. The present invention has a wide range of potential applications and uses, and it is foreseeable that it can be applied to a wide range of entities for securing and limiting access to applications and information in networked computer systems. For example, it is envisioned that the authentication system and method for networked computer applications can be advantageously utilized by any bank that provides online banking, investment and / or mortgage services. It is further envisioned that the system and method used in the present invention will also advantageously enable retail businesses providing online retail services to authenticate users. Furthermore, the systems and methods used in the present invention benefit any entity that maintains secure applications and information accessed by third-party computers ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More