Identification authentication method and system
A technology for identity authentication and identity information, applied in the field of information security, can solve the problem of low security of identity authentication methods and achieve the effect of improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
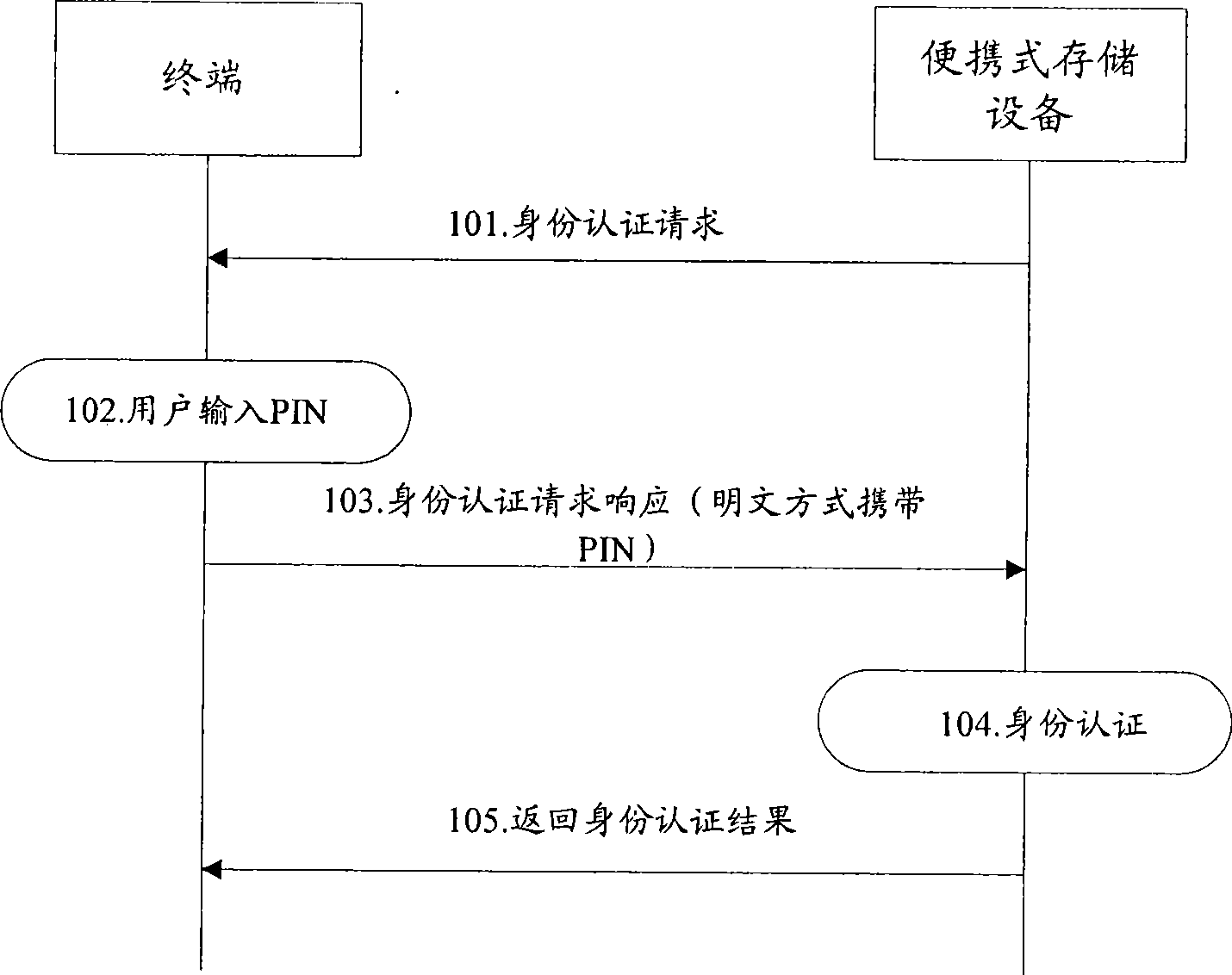
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
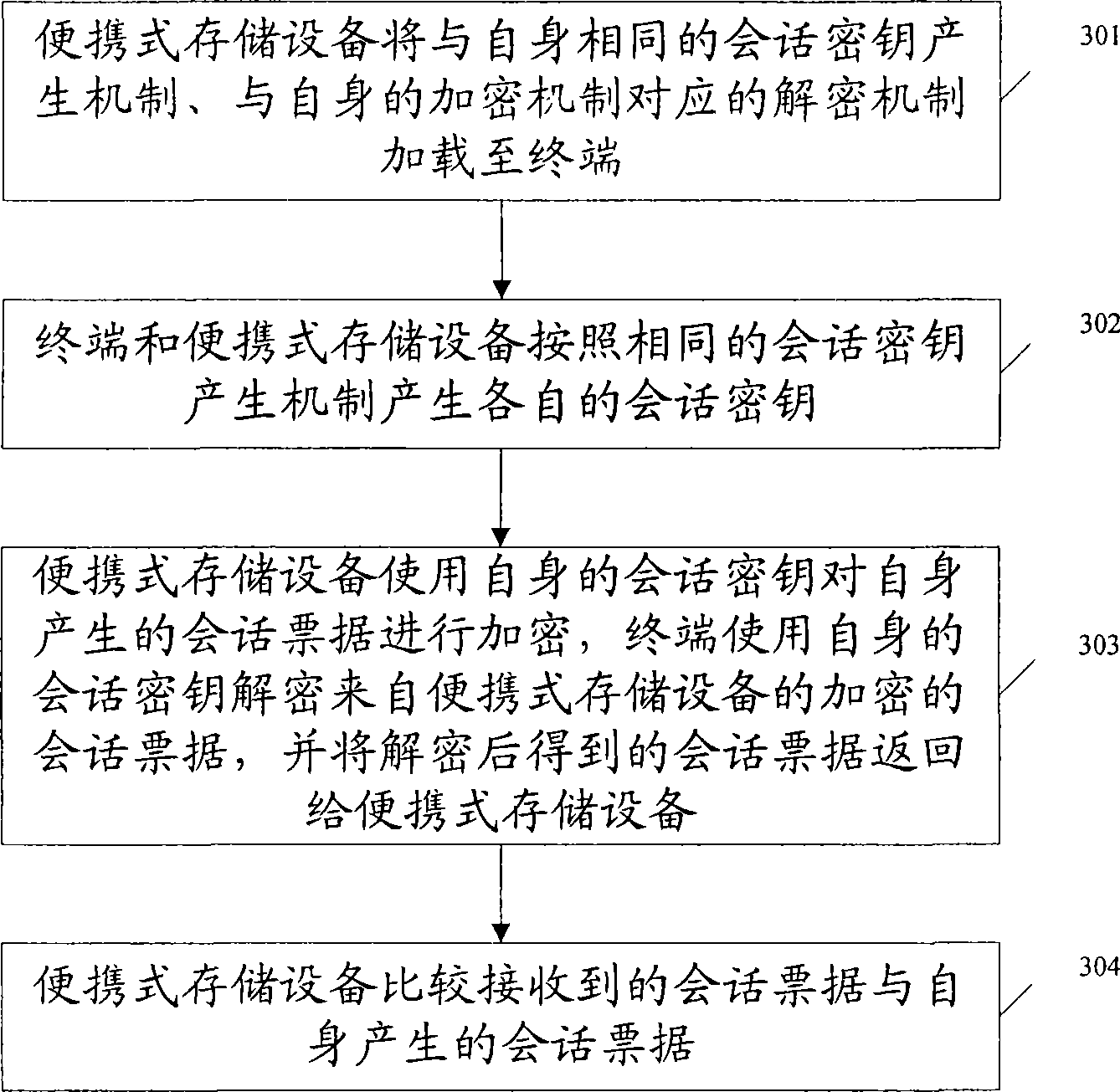
[0052] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below with reference to the accompanying drawings and examples.
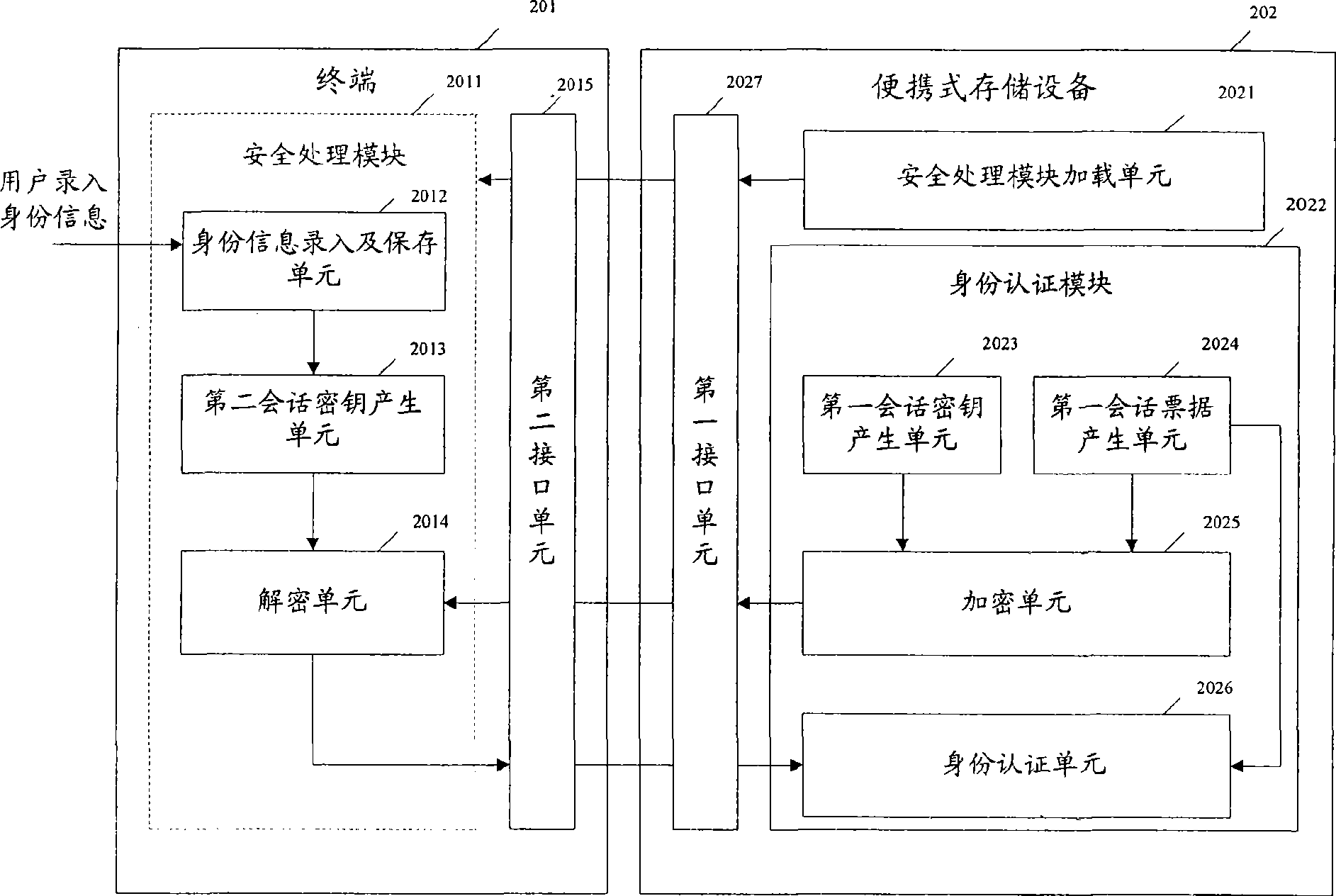
[0053] figure 2 A structural diagram of an identity authentication system provided by the present invention, such as figure 2 As shown, the identity authentication system includes: a terminal 201 and a portable storage device 202 .
[0054] The terminal 201 includes at least: a security processing module 2011 and a second interface unit 2015; the portable storage device 202 includes at least: a security processing module loading unit 2021, an identity authentication module 2022, and a first interface unit 2027.
[0055] The security processing module loading unit 2021 loads the security processing module 2011 to the terminal 201 through the first interface unit 2027 and the second interface unit 2015. The security processing module 2011 carries the sam...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More