Method for identity identification according to characteristics of user keystroke
An identity authentication and user technology, applied in user identity/authority verification, electrical components, transmission systems, etc., to achieve the effect of reducing the possibility and improving system security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
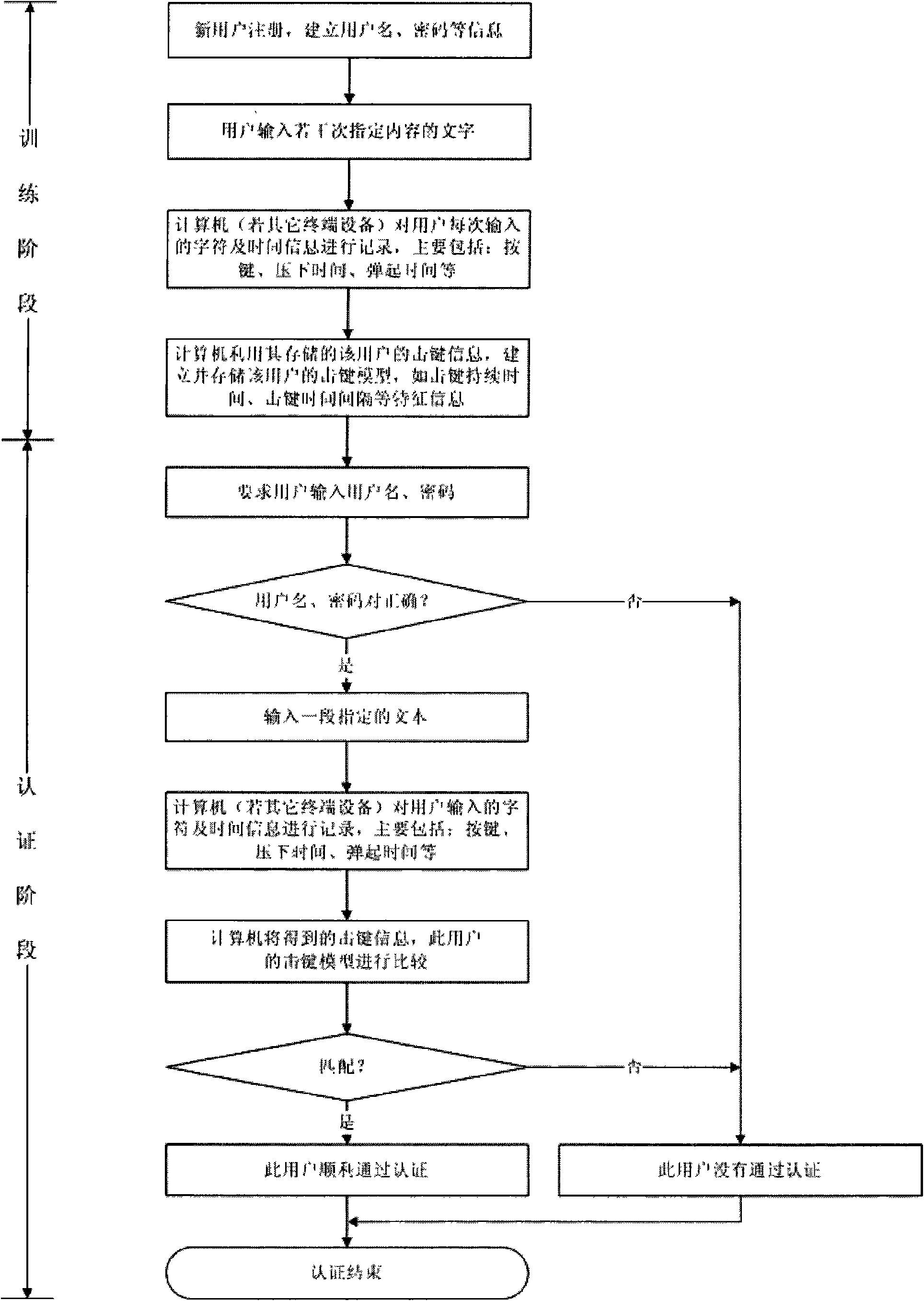
[0024] The method proposed by the invention mainly improves and strengthens the traditional user name / password pair authentication method. The implementation of the method proposed by the present invention will be described in detail below.
[0025] The implementation of the method proposed by the present invention mainly includes three aspects: keystroke information collection, training stage and authentication stage.
[0026] The keystroke information collection includes not only the keystroke information collection during the training phase when the user inputs specified text several times, but also the keystroke information collection during the authentication phase when the user is required to input the specified text.
[0027] The training stage mainly refers to requiring the user to input the specified text several times, and in this process, the keystroke model of the user is established by processing the collected keystroke information. In fact, the keystroke models ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More