System and method for realizing network access authentication, transmission encryption and UTM
A technology of network access and network transmission, which is applied in the field of network access authentication, transmission encryption, and UTM systems. It can solve the problems of poor overall network performance, poor compatibility, and seamless integration, so as to reduce networking costs and improve Overall network performance, enhanced linkage effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
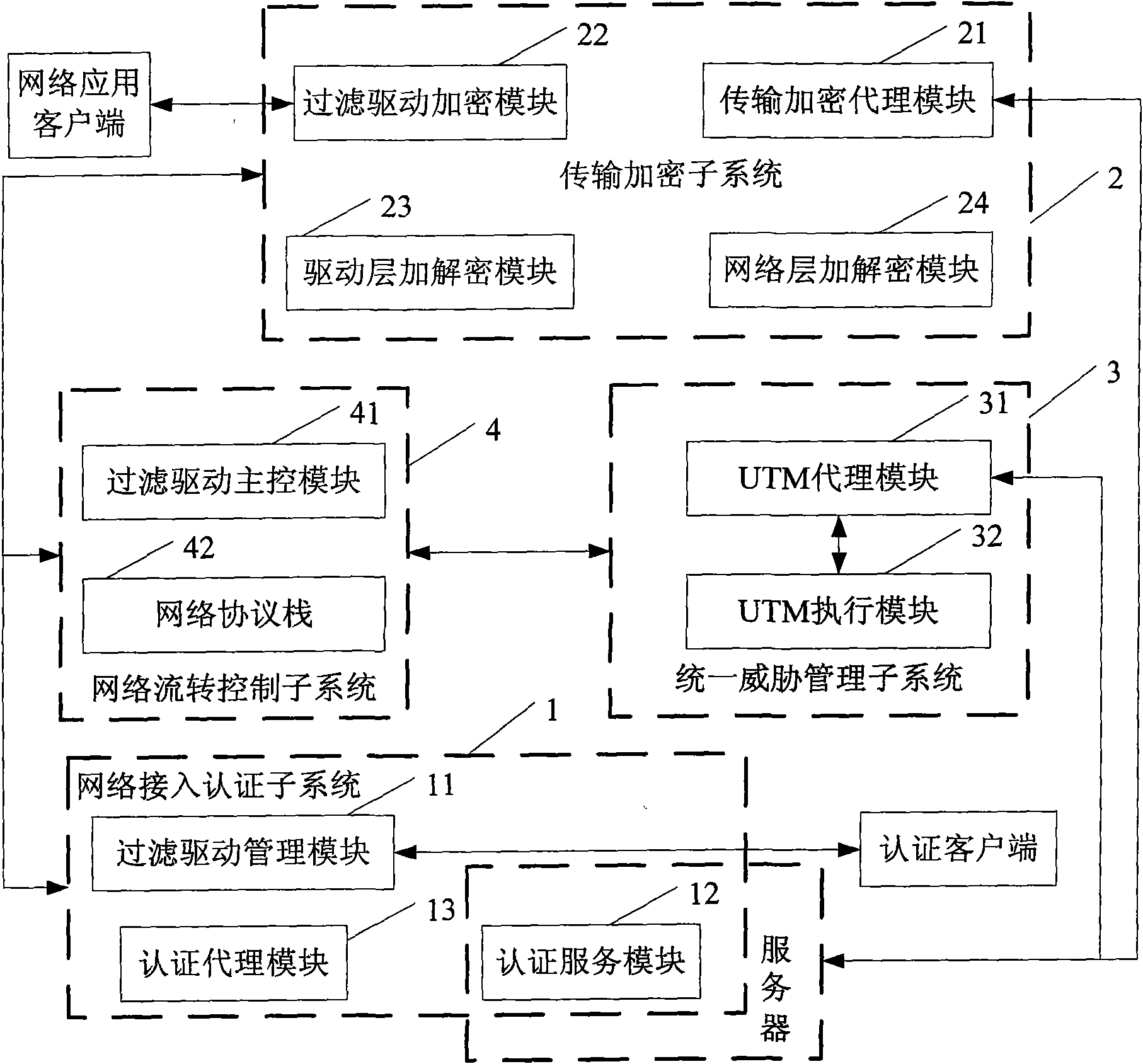
[0021] Refer below figure 1 Describe in detail an embodiment of a system for realizing network access authentication, transmission encryption, and UTM provided by the present invention; as shown in the figure, this embodiment mainly includes:
[0022] The network access authentication subsystem 1 is configured to perform access authentication on users accessing the network according to a preset authentication method;
[0023] The network transmission encryption subsystem 2 is used to encrypt / decrypt the network data packets that need to be encrypted / decrypted in the network transmission link according to the preset key;
[0024] The unified threat management subsystem 3 is used to perform unified threat management on network data packets according to preset management strategies;
[0025] The network flow control subsystem 4 is connected with the above-mentioned subsystems, and is used to intercept network data packets at the bottom layer of the network driver of the controll...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More