Creation method of end-to-end secure link and system
A technology of secure connection and establishment method, which is applied in the field of establishment method and system of end-to-end secure connection, can solve problems such as complex distribution and update process, unsuitable establishment of end-to-end secure connection of local area network, complex topology of wired local area network, etc. Achieving flexibility in the build and update process
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0041] The node N (Node) in the present invention refers to a user terminal STA (STation) and a switching device SW (SWitch) in a wired LAN. Physical layer devices such as hubs in the LAN are not treated as nodes.
[0042] In the network, all switching devices and user terminals have established secure connections with the core switching devices in the network through pre-distribution or other security mechanisms, that is, they already have shared keys. The establishment mechanism of the assumed key is not limited or defined in the present invention. The core switching device in the present invention is generally the switching device closest to the gateway in the local area network, which can be specified or configured by the network administrator, and is not limited or defined in the present invention.
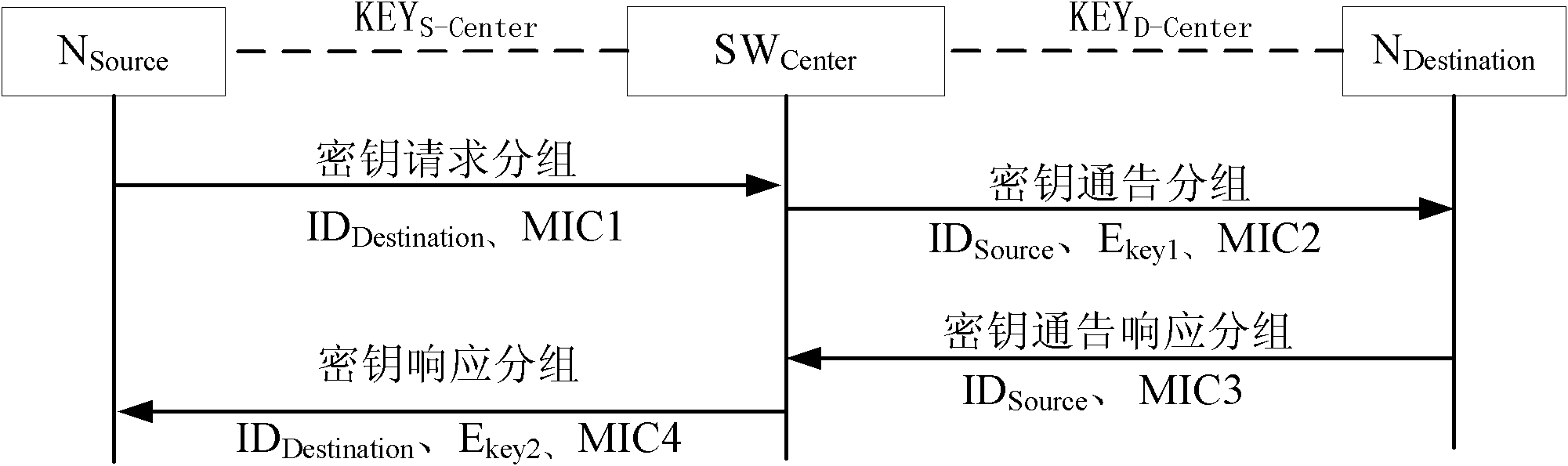
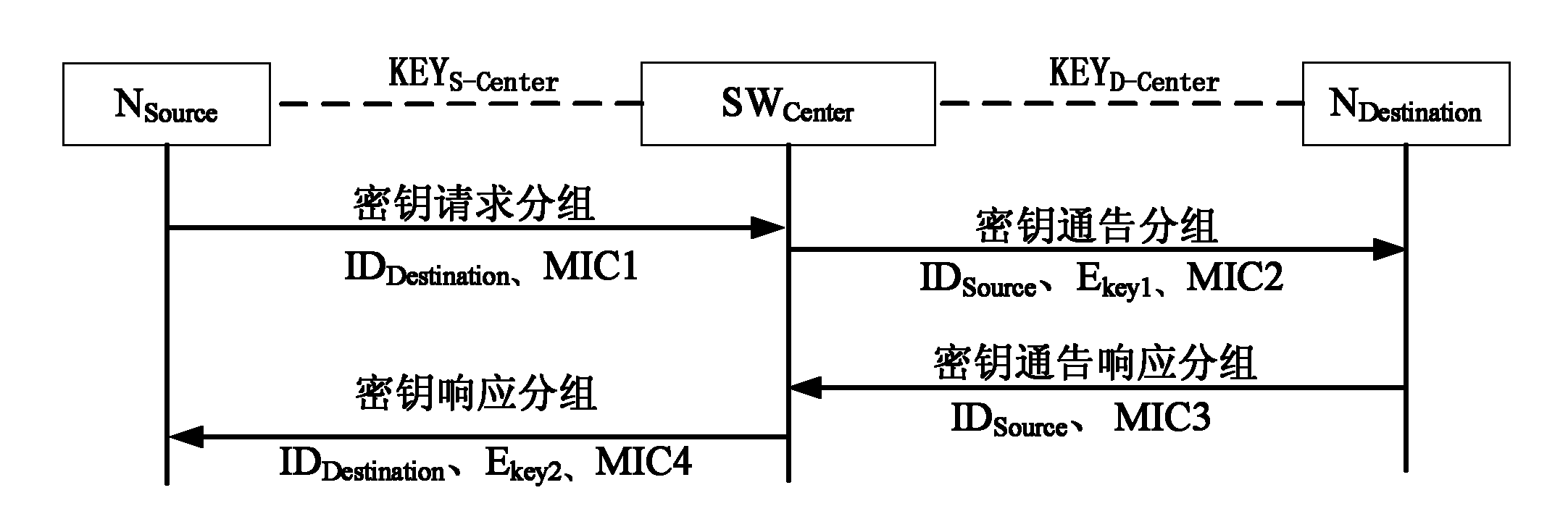
[0043] to send source node N Source with destination node N Destination As an example to illustrate the establishment of a secure connection between SW Center It is the c...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More