Microprocessor and method for limiting access
A microprocessor and register technology, applied in the direction of preventing unauthorized use of memory, protection of internal/peripheral computer components, digital data authentication, etc., can solve problems such as command failure, inability to read/write special module registers, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
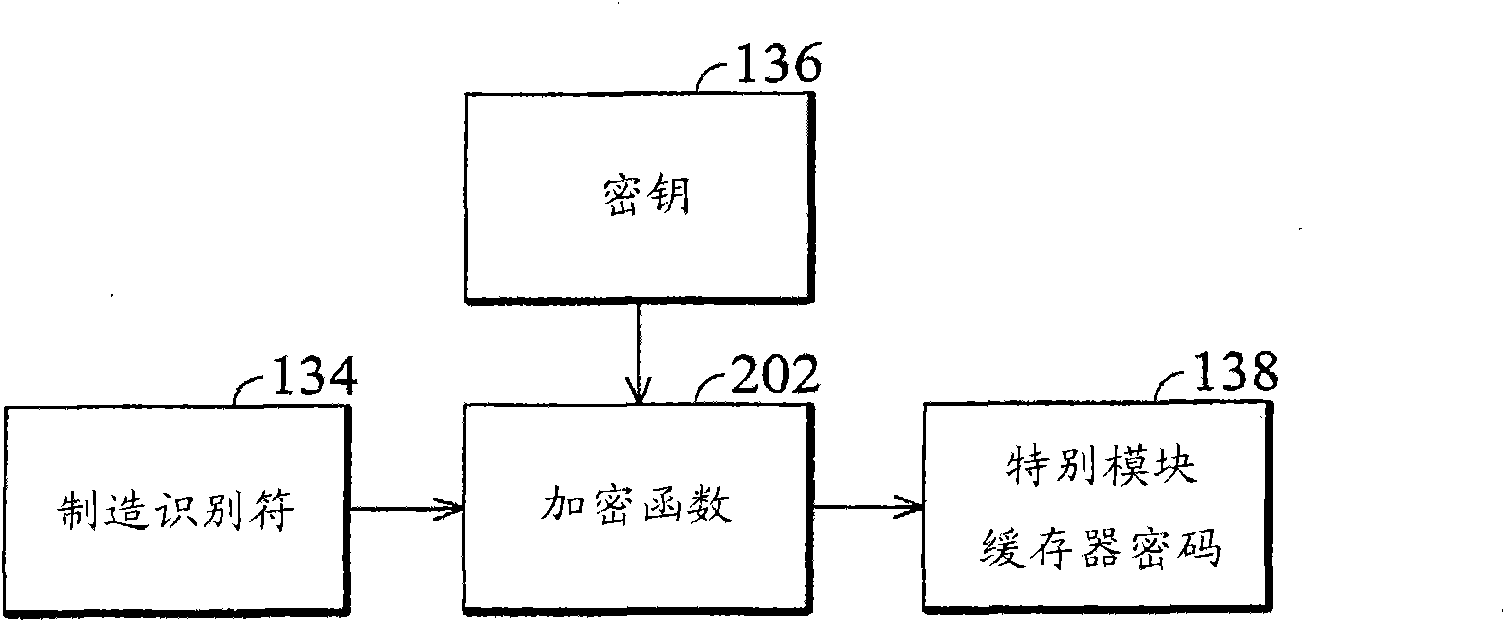
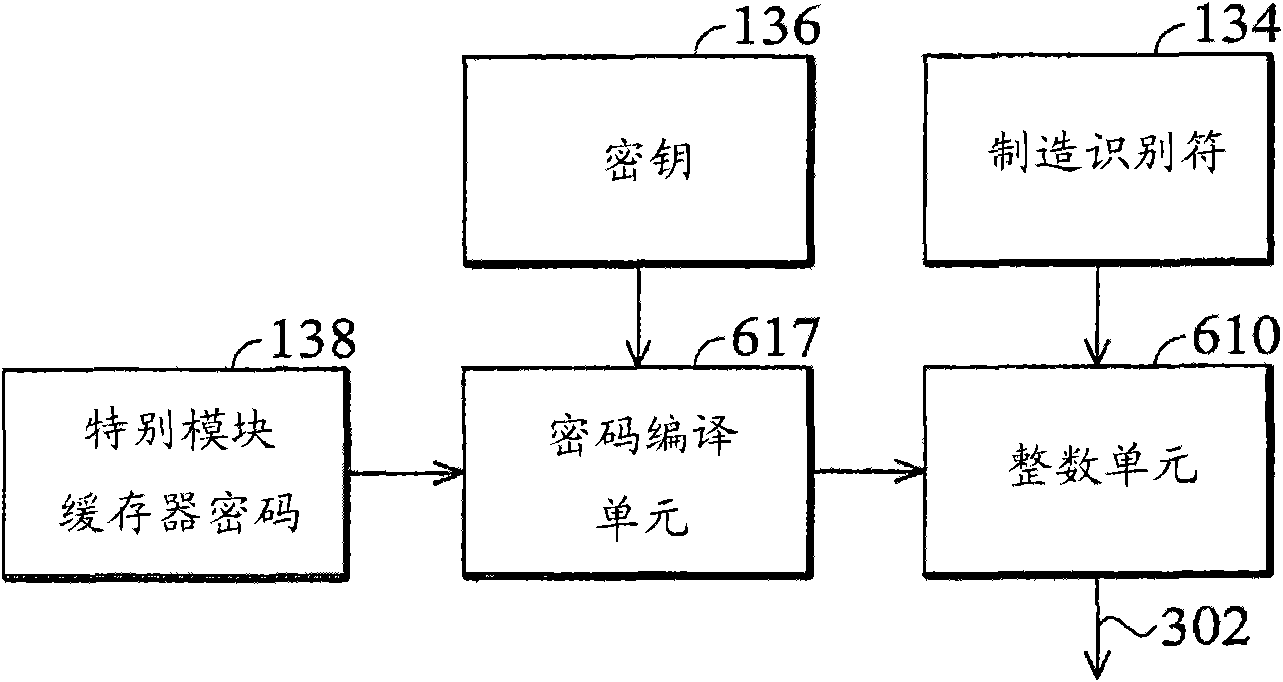
[0038] In order to solve the above-mentioned problems, embodiments of the present invention provide an access key method by having each processor have a different access key. Therefore, even if a specific processor's access key is disclosed, the potential risk will be limited to that specific processor.
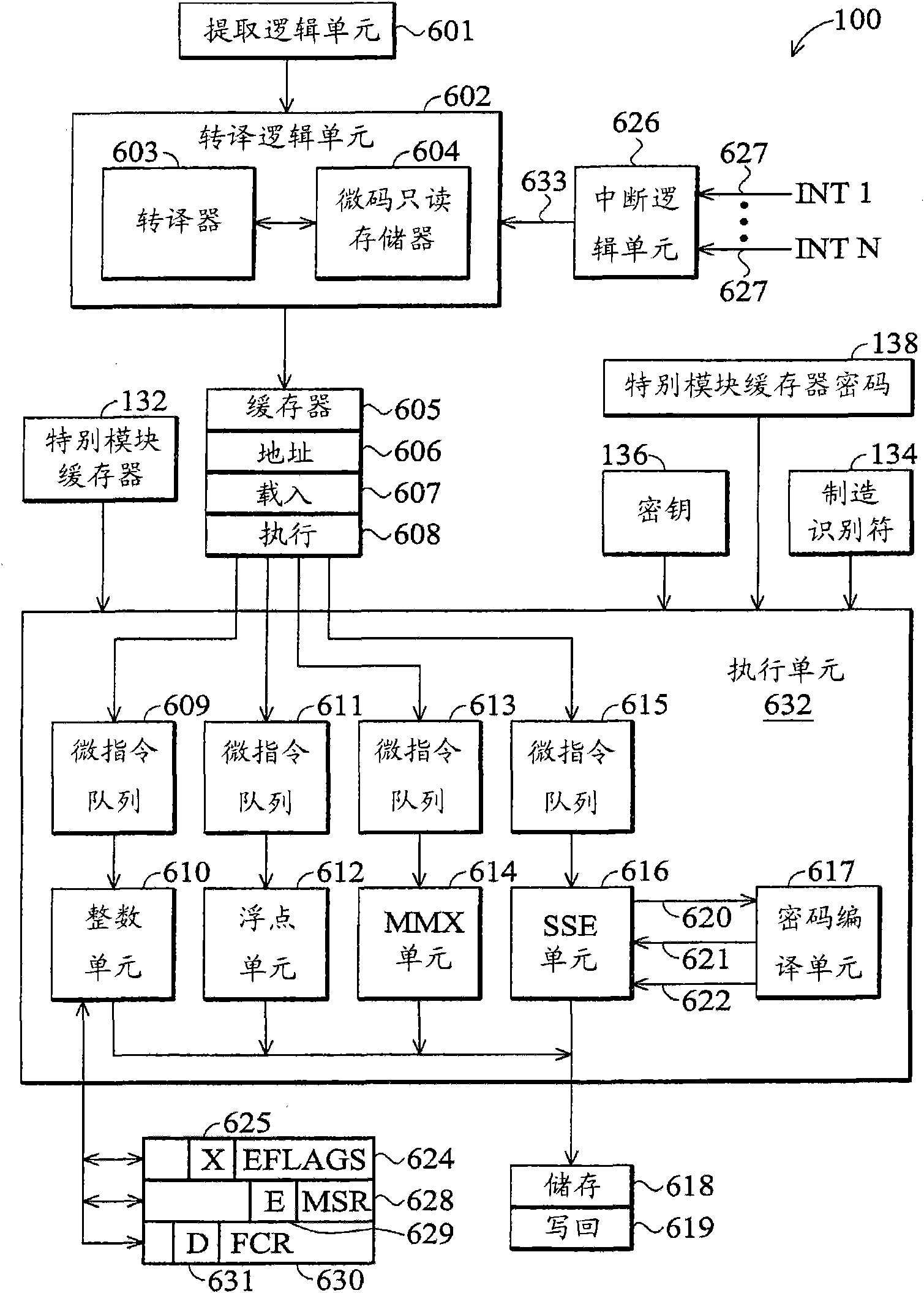
[0039] refer to figure 1 , figure 1 A microprocessor 100 according to an embodiment of the invention is shown. figure 1 The microprocessor 100 includes a plurality of MSRs (MSRs) 132 , a manufacturing identifier 134 , a key 136 and an MSR password 138 , all of which are received by an execution unit 632 .
[0040] Part of the module-specific registers 132 is protected by a password, while another part of the module-specific registers 132 is not protected by a password. In one embodiment, microcode read-only memory (ROM) 604 stores a list of password-protected module-specific registers 132, where the microcode considers when To execute the RDMSR / WRMSR instruction. In one ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More