Data integrity verification method for shared outscored database
A technology for data integrity and integrity verification, applied in digital data protection, electronic digital data processing, special data processing applications, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
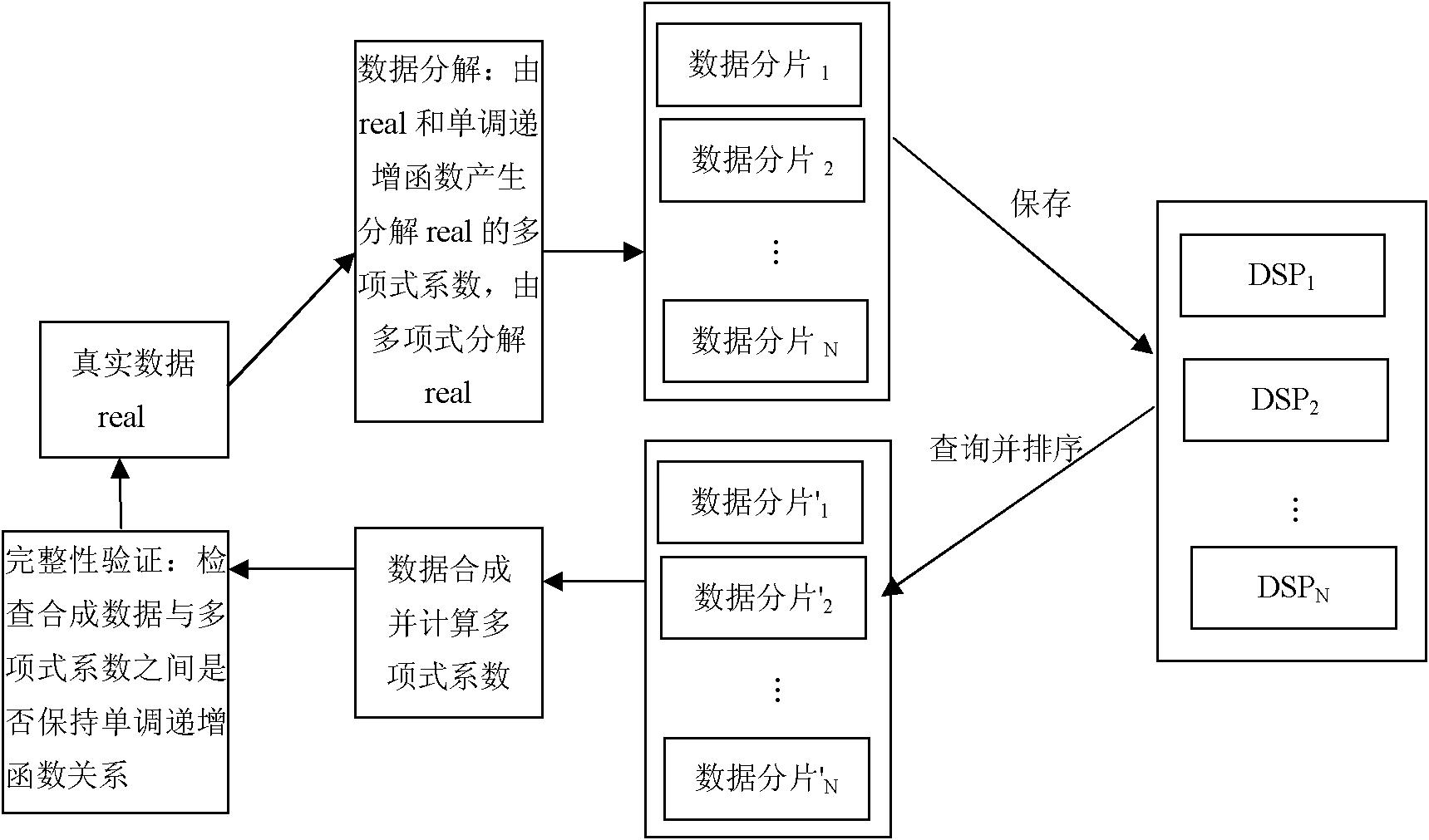
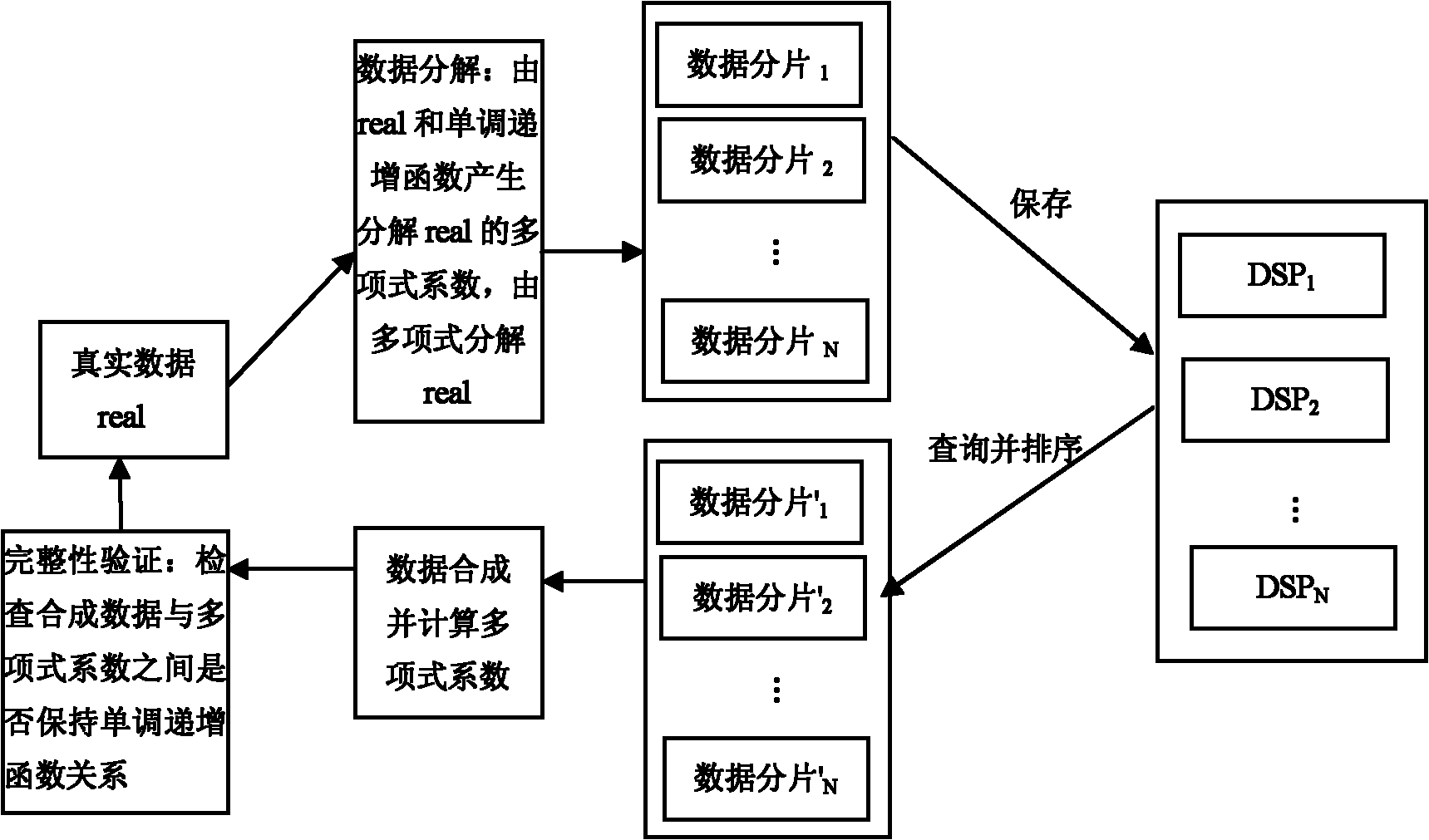
[0011] The present invention will be further described below with reference to the drawings and embodiments, but the embodiments should not be construed as limiting the present invention.
[0012] The invention is implemented in three steps:
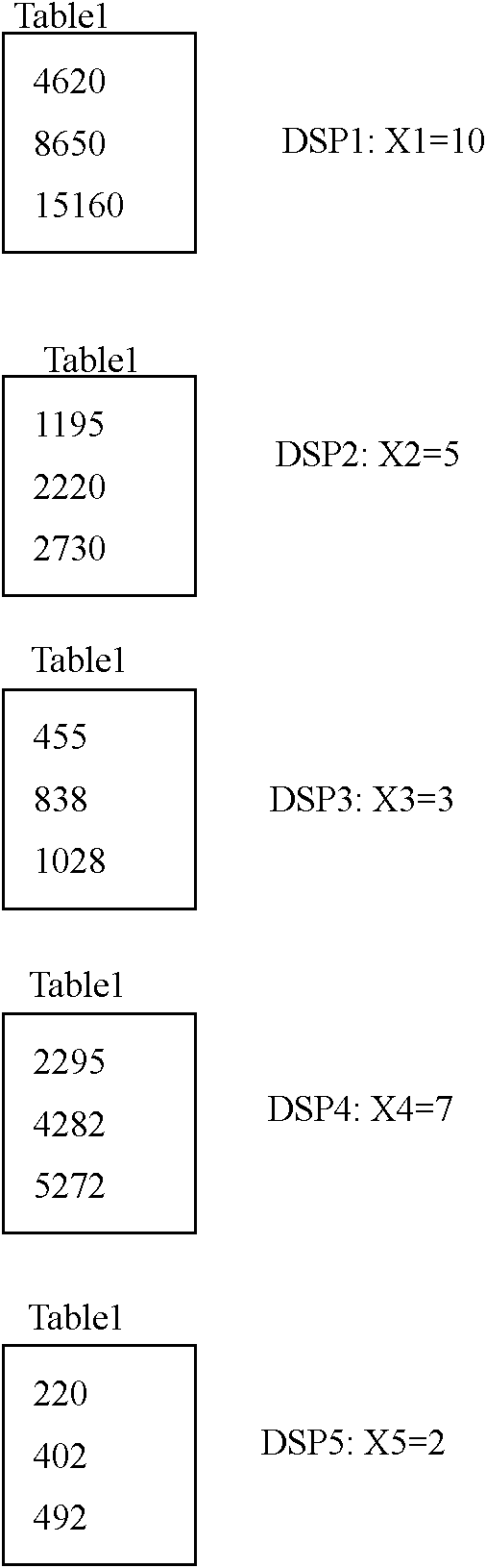
[0013] A basic table Tablel (coll int) is defined in the database, and a table with the same name is created in the database servers of N=5 database service providers to store the decomposed data fragments. Assuming that K=3 at this time, where (X1, X2, X3, X4, X5)=(10, 5, 3, 7, 2), that is, the 5 DSPs are numbered 10, 5, 3, 7, 2, respectively. The polynomial to decompose the original data is: a 1 x i 2 +a 2 x i +real(i=1,...,5), where real is the true value, x i The value is the number of the DSP server. a 1 The coefficient is generated using a monotonic increasing function f(x)=2x+5, a 2 The coefficients are generated with a monotonic increasing function g(x)=|_logx_|+6, and the variable x=real.
[0014] In the system operation stage, if th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More